Abstract
This thesis presents a mural broadcast authentication protocol (MBAP) for wireless sensor networks based on Fourier series according to the issues of the main broadcast authentication protocol µTESLA being limited in authentication delay, more initial parameters, limited time, large key chain, and network congestion. Firstly, achieving the forward authentication work for common sensor nodes to base station is based on the characteristic of continuous-integrability function
1. Introduction
In wireless sensor networks (WSN), in order to save the network bandwidth and the communication time, the base station and the cluster heads generally send messages to the common sensor nodes by broadcasting. And broadcast communication plays a very important role in WSN, and its security has a direct impact on the security of the entire network [1–5]. Therefore, it must be able to authenticate the source, the accuracy, and the integrity of the broadcast packets when the receiving nodes get the broadcast packets; it is also known as broadcast authentication.
The broadcast authentication includes two parts: entity authentication and source attestation. Entity authentication is the process for confirming the identity of the sending nodes based on some authentication protocol, which insures the security for network access. And source attestation is mainly to ensure the integrity of the messages and prevent unauthorized nodes sending, forging, and tampering messages. These two parts’ authentication can be achieved by the generation and verification of message authentication code (MAC). If the broadcast authentication takes the symmetric encryption mechanism, each captured node can modify or forge the messages and threaten the whole network security. So, it is necessary to use asymmetric encryption technique for broadcast authentication.
There are many efficient broadcast protocols that have been proposed, such as broadcast transmission capacity (BTC) of heterogeneous wireless ad hoc networks with secrecy outage constraints [6], a qos-based broadcast protocol (QBBP) for multihop cognitive radio ad hoc networks under blind information [7], and a reliable and total order tree-based (RTOT) broadcast in wireless sensor network [8]. But it is hard to design broadcast authentication protocols for WSN because of the limitations of WSN. There are two kinds of WSN broadcast authentication protocols: one is the signature authentication [9–11], but it is hard to be applied because of the disadvantage of using public key cryptography and large cost, and the other one is the message authentication code (MAC) [12–15], such as the μTESLA which is proposed as the broadcast authentication protocol by Perrig based on the security protocols for sensor networks in [15], which realizes the asymmetry of broadcast authentication by using the symmetric encryption mechanism, and including three key parts: key establishment, disclosing authentication key, and authenticating broadcast data. In addition, multilevel LTESLA, a broadcast authentication system for distributed sensor networks, is proposed in [16], which divides authentication into multiple levels, where the high level key chain authenticates the low level key chain, and the low layer key chain authenticates the broadcast data packets, but it is suitable for the single base station network.
This thesis presents a mutual broadcast authentication protocol (MBAP) for wireless sensor networks based on Fourier series according to the problems of the main broadcast authentication protocol μTESLA being limited in authentication delay, more initial parameters, limited time, large key chain, and network congestion. And the mutual authentication between nodes and base station is achieved according to the characteristic of continuous-integrability function
The paper is organized as follows. In Section 2, we analyze the related work, such as μTESLA protocol principle and its issues. In Section 3, we discuss the specific principle of MBAP, including network model assumptions, Fourier series’ characteristics analysis and MBAP authentication principle. Section 4 analyzes the security of MBAP compared with MBAP. And summary is made in Section 5.
2. Related Work
2.1. μTESLA Protocol
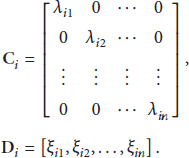
In μTESLA, the asymmetric characteristic of broadcast authentication is realized by using the symmetric encryption mechanism on condition of the loose time synchronization of sending nodes and receiving nodes. The key points of μTESLA protocol are using hash key chain and publishing key delayed, as showed in Figure 1, a one-way function key chain is established by the sending node, where the length of key chain is
μTESLA protocol.
To avoid the additional communication cost, the published key is sent to the receiving nodes by being attached with the data packet. If there is no data packet on some time slice, the key attached with the data packet will not be published, and this key can be calculated by the next keys in one-way function
2.2. μTESLA Protocol Issues
2.2.1. Computation Cost
The μTESLA protocol has higher authentication efficiency in the case of sending data packets frequently, but it has a very low sending frequency in some applications, such as fire alarm and other event-driven applications, where the transmission interval of the adjacent data packets may be far greater than the time slice D of μTESLA and causes lots of keys not to be used for the data packets authentication, and the distance between adjacent keys on the key chain is also increased and causes a large computation cost and authentication delay.
Increasing D can alleviate this problem, but it also causes a lot of authentication delay, and the receiving nodes also need more memory space for buffering packets.
2.2.2. Delay
In μTESLA, the time interval of sending message
2.2.3. Problem of Initialization Parameters
The most important problem of μTESLA is the distribution of initialization parameters. Each sending node has an independent authentication key chain for encrypting its own data packets, and each receiving node makes authentication for
2.2.4. Authentication Aging Problem
There are some applications that require real-time authentication for broadcasting, such as real-time audio frequency, video stream, and alarm information. Obviously, μTESLA is not suitable for high ageing applications because of the authentication delay.
2.2.5. Fixed Key Chain Length
In μTESLA, the authentication key of each time slice is predistributed upon network initialization. On the one hand, if the work time is too long, it means that the length of key chain is too large, which will cause a large computation cost and storage cost. On the other hand, if the work time is too short, it cannot meet the requirement of frequent data exchange and long-term work.
Therefore, in order to meet the characteristics of lower delay, better aging, less key storage, computing fast, and better flexibility for the general broadcast authentication in WSN, this paper introduces the mathematical theory of Fourier series, which simplifies the practical issues based on characteristic of Fourier series coefficients and makes a simple and efficient broadcast authentication.
3. MBAP
3.1. Network Model Assumptions
In WSN, either the base station or the sensor node is the broadcaster (as shown in Figure 2).
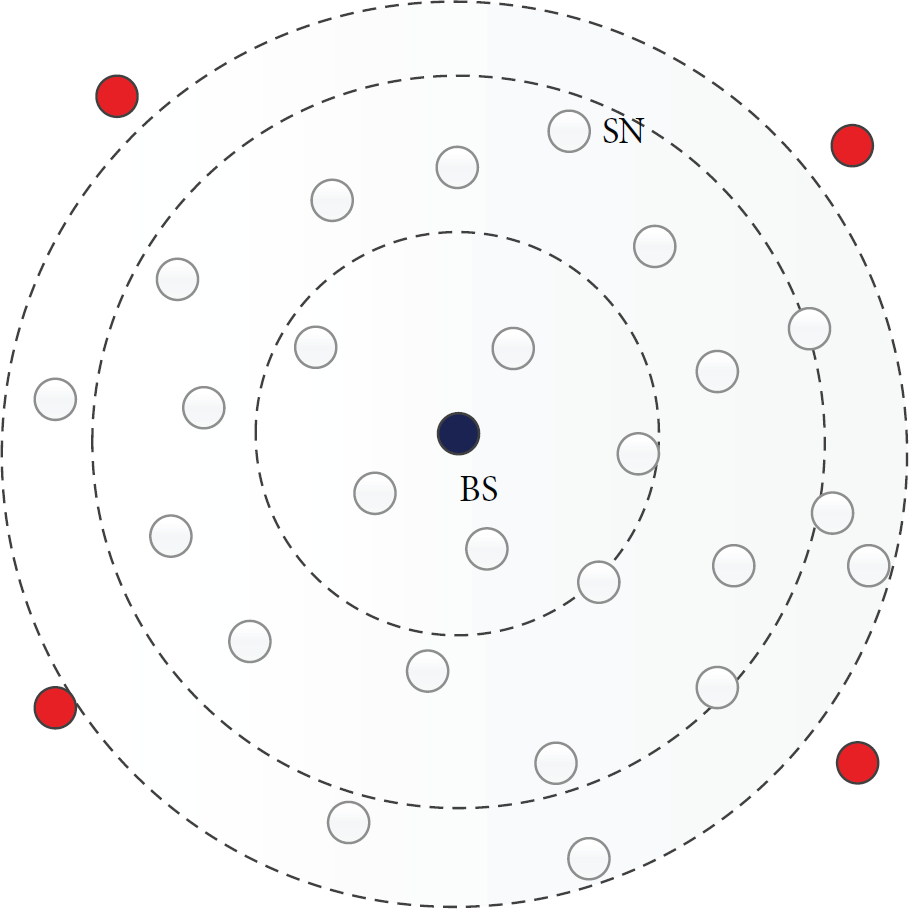
Broadcasting communication in centralized network.
According to the topology of the network, it can broadcast directly when the base station is the broadcaster which can send the information to the prerecipient without intermediate nodes or can send the information to the prerecipient layer by layer, such that the base station will send the information to each cluster head first of all, and the cluster head will send the information to each common sensor node after authentication.
When the sensor nodes are the broadcasters, they can only send the information to their neighbor nodes directly without intermediate nodes.
In order to facilitate the description of MBAP, the network is assumed as follows:
Assume that the network is isomorphic and static and each of the sensor nodes has been uniformly deployed in the target area and has same configuration in software and hardware and will not move any more once they are deployed, where the network size is N, including 2 types of nodes, base station (BS) and sensor node (SN), as shown in Figure 2. Assume that base station (BS) is equipped with abundant software and hardware resources and can cover the entire network deployment area by means of a high power radio signal, and it is responsible for storing the basic information of all the nodes in network and has the ability to detect compromised or captured nodes. Common sensor node is responsible for collecting environmental data. The ability to process data of sensor node is limited by storage space, energy reserves, and communication distance. Since the communication radius of the common sensor node is limited, the communication between nodes which are not in the communication radius should be transferred by neighbor node.
The main symbols in the text are shown as follows:
K: authentication key, D: time slice length, P: plaintext,
3.2. Analyzing Characteristics of Fourier Series
Definition 1.
If the function
And claim that formula (1) is the Fourier series determined by
3.2.1. Orthogonal Analysis of Trigonometric Function
Assume that c is a real number and
And it is easy to prove with product and difference
3.2.2. Fourier Series Coefficient Analysis
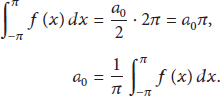
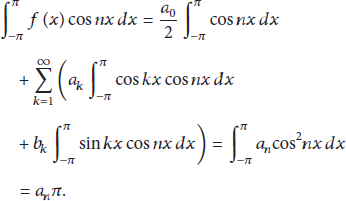
Deduction 1.
Assume that function
Then
Proof.
Assume that
Set that n is a positive integer and multiplying by both sides with
Therefore
Similarly
Thus Deduction 1 is proved.
3.3. MBAP Authentication Principle
We assume that
Step 1 (establishing authentication key). The base station divides the communication time into equal time slices, where the length of each time slice is D, and each time slice is assigned a key in order. Set
It is obvious that the keys for each time slice are different based on Deduction 1, and
It is showed in (12) that the authentication key
Step 2 (building broadcast authentication information). We assume that
Then there are base station broadcasts
Step 3 (application verification). The common sensor node gets the authentication information
If the common sensor node has received the authentication information
Conversely, if
Step 4 (entity authentication). Because
If
Conversely, if
Step 5 (source attestation). After the completion of entity authentication, it is necessary to determine whether the plaintext message
It is showed in (16) that the calculation of
And if
Conversely, if
The forward authentication work for common sensor nodes to base station is completed from now on, and the forward flow chart of MBAP protocol is showed in Figure 3.

Forward flow chart of MBAP protocol.
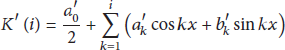
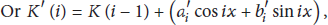
Step 6 (reverse authentication)
Deduction 2.
In order to detect the security of
Proof.
Assume that
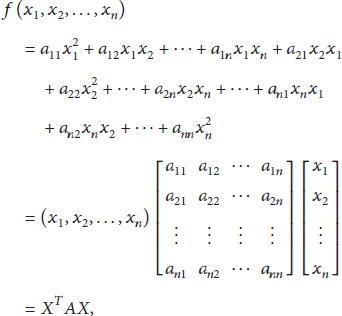
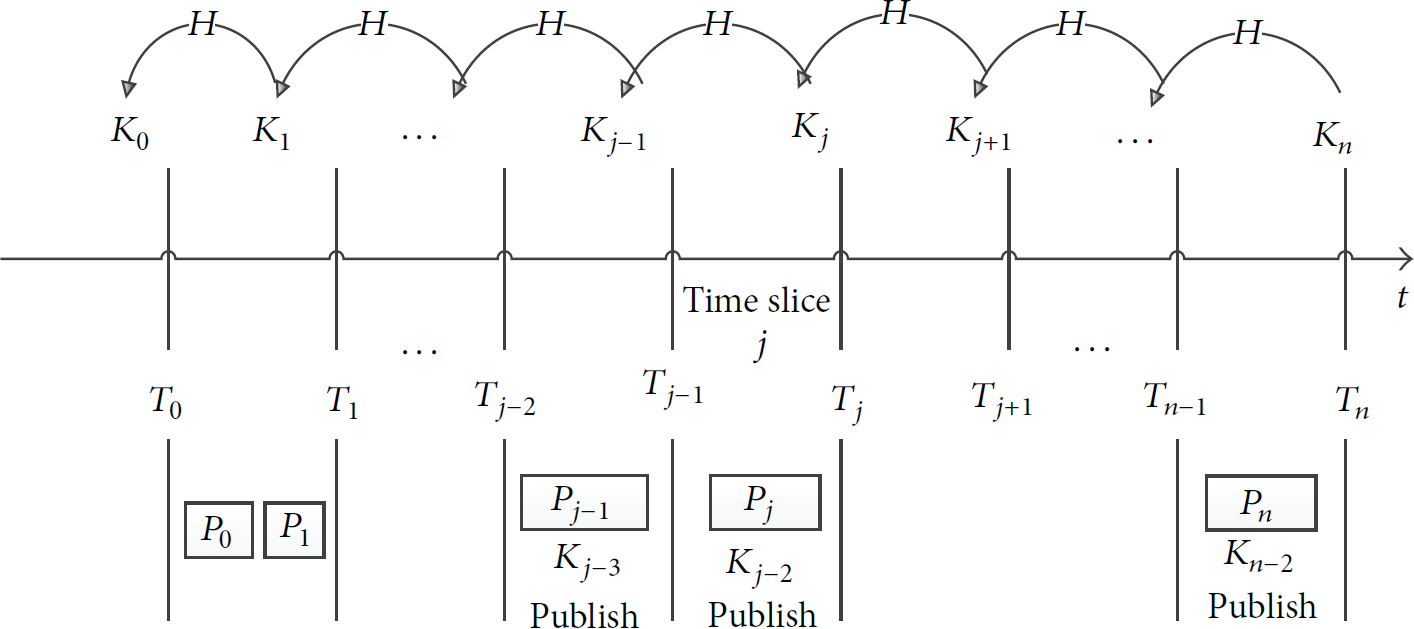
A key management scheme based on quadratic for WSN is proposed in [17] by the author Xiaogang Wang, where, assuming
We can assume that node
Based on [17], we can get that the eigenvalues
Therefore, a mutual broadcasting authentication work is achieved by now and Deduction 2 is proved.
Step 7 (update
And the updating for
4. Security Analysis
Because of the limited resource in WSN, it should meet 3 basic requirements for designing efficient broadcast authentication protocol: Firstly, insure the lower computation and communication cost. Secondly, the base station can make authentication randomly. Thirdly, the sensor nodes can make a real-time authentication. In this paper, the TWBAP protocol has some own security features besides the above the 3 conditions.
4.1. Anticapture
In MBAP, we know that

Anticapture performance of MBAP.
In addition to this, we assume that the size of the network in WSN is N, and if
4.2. Low Cost
In this paper, the computation cost and communication cost of MBAP protocol are relatively low, which can meet the requirements of low cost. Firstly, the broadcast authentication information
4.3. Instant Authentication
In MBAP, we can make authentication immediately based on the characteristics of Fourier series coefficients when the authentication information
4.4. Delay
In μTESLA, we know that the time interval of sending message
In MBAP, the authentication information
We know that authentication delay includes the transmission cost and the computation cost, where the transmission cost is the necessary cost which cannot be avoided. For μTESLA, the authentication delay should also include delay time δ.
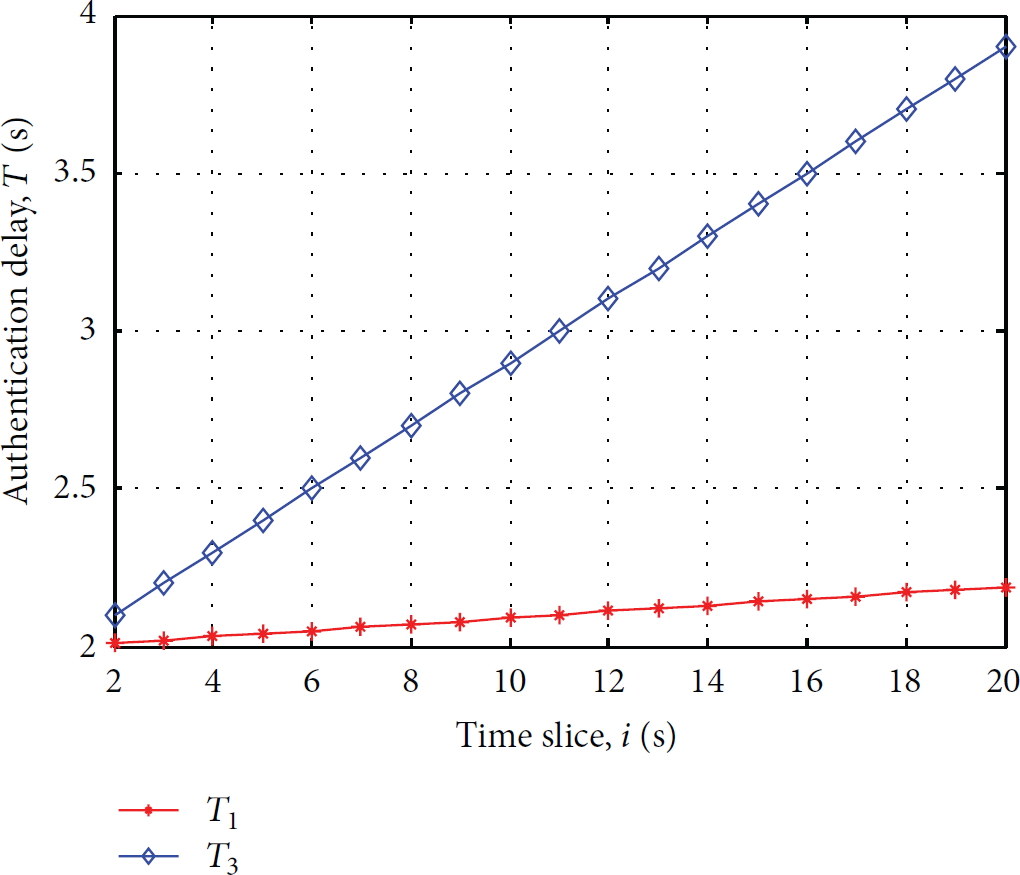
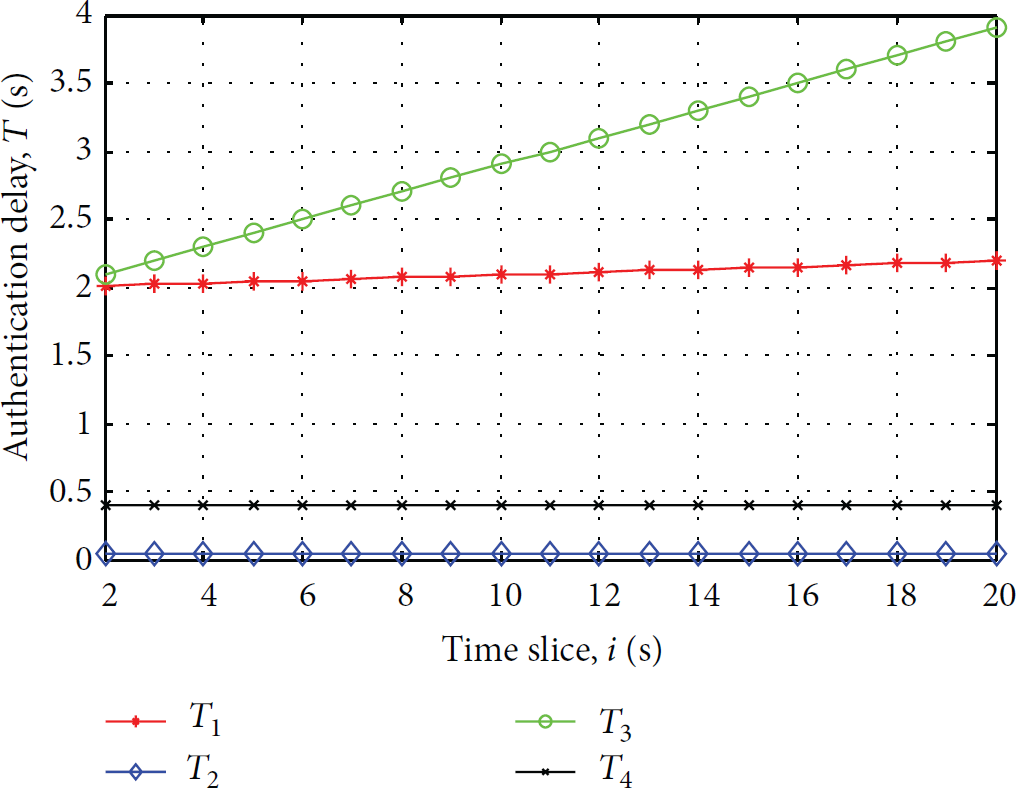
In order to analyze the delay problems between MBAP and μTESLA by simulation, we assume that T is the authentication delay and D is the length of time slice, which can be set to 1 in here, and assume delay time
In μTESLA,
In MBAP,
And the authentication cost of

T changes.
It shows the cost changes of once authentication calculation on different time slices in Figure 5, but there will be amounts of authentication calculation happening on each time slice actually, which can cause some time delay for each authentication calculation. So, the authentication delay is increased with the time changes. For this reason, we assume that there will be n times authentication calculation happening on each time slice, and we assume that
Similarly, we assume that
For ease of calculating, we assume
T changes of μTESLA protocol.

T changes of MBAP protocol.
T changes between two protocols.
It is indicated in Figures 6 and 7 that the authentication delays of these two protocols are all increased with the time changes, but the authentication delays of μTESLA are increased much faster with the authentication calculation increasing, while the authentication delay of MBAP is changed stably.
It is indicated in Figure 8 that there will be some messages abandoned on some slices with the authentication delay increasing in μTESLA; it is one of the issues in μTESLA analyzed in Section 2.
4.5. Initialization Parameter
In MBAP, the only predistributed initialization parameter is
While in μTESLA the initialization parameters are
4.6. Length of the Key Chain
In μTESLA, when the sensor nodes receive the published key
In MBAP, the authentication key
5. Summary
This thesis presents a mutual broadcast authentication protocol (MBAP) for wireless sensor networks based on Fourier series according to the problems of the main broadcasting authentication protocol μTESLA being limited in authentication delay, more initial parameters, limited time, large key chain, and network congestion. And the mutual authentication between nodes and base station is achieved according to the characteristic of continuous-integrability function
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work is funded by the National Nature Science Foundation of China (no. 61473050), National Science and Technology Planning of China (2011BAJ03B13-2), and National Basic Research Program of China (2013CB328903).