Abstract
The unique characteristics of wireless sensor networks make them susceptible to the attacks. The secure scheme is considered in designing the routing protocol and algorithm. The cryptography and authentication secure technology can defend the external attacks but have no way to protect the network when the internal attacks occur. However, the trust management scheme with attack-resistance and robustness can efficiently detect the internal attack. On the condition of defending the attacks, it is also an issue that the trust management scheme aids routing algorithm to improve the security and performance. In this paper, we proposed a Trusted Tree-based trust management for secure routing in wireless sensor networks. The common attacks are firstly analyzed. And then the dynamic time window is designed in the distributed trust model with the detection of direct trust and indirect trust. Based on the trusted nodes, Trusted Tree is constructed. And the path quality of nodes in Trusted Tree is used as the gradient for routing. Finally, we add Trusted Tree-based trust management into the QoS based routing protocol and algorithm. Experimental results show that the QoS based routing algorithm with Trusted Tree has better performance and security.
1. Introduction
Wireless sensor networks are the most important elements in Internet of Things [1–4] and playing more and more key role in a wide range of application domains, such as habitat monitoring, disaster prevention, automation control, and infrastructural security [5–7]. These network nodes are equipped with the sensor and collect the data from the monitored environments.
Since the communication range and computing ability of node are limited, the ad hoc routing protocol is used in wireless sensor networks [8, 9]. The traditional network protocol is not suitable for wireless sensor networks, and their security protocol can not be directly used to defend against the attacks in wireless sensor networks [10–12]. Many routing protocols and algorithms are designed for the efficient transmission of data in wireless sensor networks. The network threat is considered, such as flooding attack and eavesdropping attack. These attacks are divided into two types: internal attacks and external attacks [13, 14]. The cryptography and authentication are usually applied to the routing protocols to defend the external attacks, because the malicious nodes have no right to access the network. When the nodes are compromised and launch the internal attacks, the secure techniques with cryptography and authentication fail to protect the network security. For the internal attacks, the trust management is the effective method. The trust management can identify the malicious node by monitoring and evaluating their behavior. However, the trust management is also vulnerable to the attack, and some intelligent behavior can trick the trust management schemes, such as on-off attack and bad-mouthing attack. Therefore, robustness issue is also considered in the trust management scheme. The distributed trust mode with direct trust and indirect trust is used to enhance the robustness in the trust management.
The trust management scheme is usually seen as the service for the network routing protocol and algorithm. The trust evaluation in the trust management does not only detect the trust value of the nodes; but it is also one of the metrics in the routing algorithm. By accumulating the trust value in the routing path to evaluate the security of routing path, the secure route can be reasonably established. Therefore, based on distributed trust mode, how to design an efficient trust management scheme is a critical issue in enhancing the performance of secure routing.
In this paper, we propose a Trusted Tree-based trust management scheme for routing in wireless sensor networks, which can implement the routing security and improve network performance. The attacks are firstly analyzed. And then the trust computing model and Trusted Tree are established and maintained. Furthermore, our scheme is applied to the QoS based secure routing protocols and algorithms and guides the process of the routing establishment. The major contributions of this paper are threefold which are listed as follows.
Dynamic time window: the fixed size of sliding time window is changed into the dynamic size, so as to detect the malicious nodes with the low proportional bad behavior. Trusted Tree: based on the computed trust value of node, the Trusted Tree is established. The secure key of node is generated. The topology path quality in Trusted Tree is used as the gradient to guide the routing building. Aiding Routing: the QoS based routing protocol using Trusted Tree is implemented. The simulation results show that the QoS based routing protocol with Trust Tree can not only efficiently detect and exclude the malicious nodes, but also significantly enhance the network performance.
The remainder of this paper is organized as follows: Section 2 discusses the related works. The attacks, computing of trust value, and Trusted Tree are proposed in Section 3. The simulation results are presented in Section 4, and Section 5 concludes the paper.
2. Related Work
The trust management can ensure the security of data transmission in wireless sensor networks [15]. The trust management model in secure routing protocol and algorithms can be divided into the two classes: centralized trust model and distributed trust mode [16, 17].
2.1. Centralized Trust Model
The trust value of nodes is computed by the particular trusted centre or base station. CENTER [18] is a centralized trust based efficient routing protocol for wireless sensor networks. The base station is used to observe the behavior information from the nodes and deduce the global network view. The nodes’ trust value and the best routes are calculated for excluding the malicious nodes. Improving on the previous CENTER, CENTERA [19] includes an appropriate authentication scheme, and the base station gathers minimal neighbor trust information from the nodes. Although the base station can calculate and evaluate the trust value of the nodes by the global view of the network, the accuracy of trust metrics about the distributed nodes needs to be improved.
TCFL [20] uses the nodes’ trust value to select the routing path with highest trust value. The fuzzy logical deduction is used to quantize the uncertain and imprecise data. The proper transmitting path can be established from the source to the destination. However, the high energy is consumed in the TCFL.
2.2. Distributed Trust Model
The sensor nodes calculate the trust value by themselves. TQOS [21] obtains the secure routing by combining the trustworthiness of the nodes and the QoS of the link along a route. Based on the trustworthiness-based QoS metrics, the secure routing is discovered and set up. The trust value of nodes is gained by computing the ratio of the number of messages verified and received, but this simple statistics model is vulnerable to attack. ReTrust [22] is an attack-resistant and lightweight trust management approach. The sliding time window is used to calculate the trust value of nodes. ReTrust is a typical instance that uses direct trust and indirect trust. But this fixed size of sliding time window makes it difficult to detect the malicious nodes with low proportional behavior.
FTPR [23] proposes a fuzzy-based trust prediction model for routing. Based on the historical behavior and the fluctuations in trust value over a period of time, FTPR operates the trust prediction model to predict the future behavior of the neighbor nodes. However, the wireless link is unstable, and then the link temporary errors can result in the fluctuation of the trust value. For FTPR, it is difficult to discriminate them.
PLUS [24] uses the personal reference information and recommendation information to build the reasonable trust relationship among the sensor nodes. The personal reference value is gained based on the ratio of correct packets, and the recommendation value is computed by the neighbor nodes’ trust value. The trust value of suspect node is decided by the integrity check of the packet. Consequently, the suspect node may get unfair penalty and be regarded as the malicious node. In [25], considering the vulnerability of trust establishment to different attacks and the unique features of sensor nodes, a lightweight and robust trust establishment scheme is proposed. The trust value of the nodes is computed based on the rate of misbehavior. Although the frequency of misbehavior is used to check the on-off attack, this method fails to detect the attack with the low percentage of bad behavior.
Another interesting distributed trust model is proposed in ATSR [26]. ATSR also implements the trust mode by the direct and indirect trust information and adopts the location-based approach to reduce the routing protocol storage and cost. However, ATSR needs to rely on the location information. GTMS [27] is a group-based trust management scheme for clustered wireless sensor networks. GTMS has three levels: the node level, the cluster head level, and the base station level. Although the timing window mechanism is used to calculate the trust value of the node, GTMS is designed for the clustered network.
The cryptography and authentication technology are also used in the centralized and distributed trust model [28, 29]. In centralized trust model, CENTERA uses RC5 and PBC. In distributed trust model, TQOS contains authentication between two nodes.
By analyzing the above instances of trust management mode, it is found that the centralized trust mode has high energy consumption and low accuracy. The distributed trust mode is used in the massive routing protocol and much more suitable for wireless sensor networks.
3. Trusted Tree-Based Trust Management
In this section, the threats are firstly analyzed, and then the computing method of trust value and Trust Tree are designed. At last, the Trust Tree-based trust management is added into the QoS based routing protocol.
3.1. Threats Analysis
Two types of attacks could occur in wireless sensor networks. The first type is the external attack. Wireless sensor networks are generally deployed in the unattended environment. The malicious nodes make it easy to launch the external attacks, such as denial of service (DoS) attack, sniffing attack, and replay attack [30]. DoS attacker can flood the massive hello message or redundant information. The normal and legitimate communication between nodes is disrupted. Although the sniffing attacker has no key materials about communication, it can passively eavesdrop on the transmitted data between legitimate nodes. The replay attacker can simply retransmit the earlier packets to the neighbor nodes, since it can receive the packets by wireless link. These external attacks can be defended by some cryptographic algorithms and authentication mechanisms.
However, the cryptography and authentication fail to defend the internal attacks. When the node is compromised to be the malicious node, it is changed to be the internal attacker. The second type is the internal attacks that the compromised nodes launch. These malicious nodes can participate in the routing or collude with other malicious nodes. Wireless sensor networks are more vulnerable to the internal attacks as compared to the external attacks. There are usually some internal attacks including Blackhole, Greyhole, Sinkhole, and Wormhole [31]. The Blackhole attacker drops all the messages when it receives them from the neighborhood nodes. The Greyhole attacker forwards a part of the received message or discards parts of them. The Sinkhole attacker likes the Blackhole attacker, but it deceives the nodes in its near area and disguises itself as the Sink node and then attracts all the data from this area. The two malicious nodes tunnel the messages and replay them from one part of network to another part. This attack is called Wormhole attack. The trust mechanism is a widely used technology in aiding the nodes to deal with the uncertainties and malfunctions of the internal attacker nodes. By observing the behavior of the nodes in the network for a certain period, the normal node calculates the trust value and then justifies if the observed node is trusted.
Although the trust based security mechanism can continuously monitor nodes’ behavior to detect the malicious and compromised nodes, the trust mechanism itself is also easy to be attacked. Before the malicious and misbehaved nodes are not detected, they launch some attacks on the trust management system in the network, such as on-off attack and bad-mouthing attack. In the on-off attack, the malicious nodes avoid being found by alternatively good and bad behavior, hoping that they remain in the trusted nodes set. The bad-mouthing attacker forges the recommendation of nodes, in which they frame up the recommendation of normal nodes and boost the trust recommendation of malicious nodes. They impair the trust management system by this kind of different behavior. These malicious nodes trick and attack the trust management system by the intelligent misbehavior. When the proportion of malicious behavior is lower, the detection of malicious nodes is more difficult to achieve. The current trust mechanisms have seldom effective methods to detect the low proportional malicious behavior. In this paper, the dynamic sliding window is used to solve this issue.
3.2. Computing of Trust Value
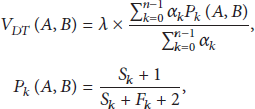
By observing the weight of neighborhood nodes’ misbehavior, the node usually computes their trust value. The sliding time window is used to estimate the trust value of nodes. The time window

Sliding time window.
Based on the observed information in the time window, the direct trust value is estimated. The direct trust value of node B for node A is denoted by
The direct trust value is computed by the observed number of misbehavior. Since the on-off attacker behaves well and badly alternatively to get the high trust value, calculating the period of misbehavior is adopted to detect the on-off attack. Based on the units in sliding time window, the time interval of good and bad behavior is estimated. When the proportion of misbehavior is higher, the smaller size of sliding time window can detect the misbehavior. However, when the proportion of misbehavior is lower, the size of sliding time window needs to be enlarged to cover the enough observed behavior. The current sliding time window adopts the fixed size that is previously set, before the nodes are deployed. If the fixed size is larger, it is a waste of storage resource. On the other hand, if the fixed size is smaller, it is not effective for detecting the low proportion of misbehavior. Therefore, in this paper, the sliding time window is changed into a kind of dynamic sliding time window. When the trust evaluation value is lower than the trust threshold of behavior, this window unit is considered as an on attacking unit and is temporarily stored in time window by prolonging the size of sliding time window. The fourth on window unit is reserved, as shown in Figure 2(a).

Size of dynamic time window.
In sliding time window, node A observes the behavior of node B and finds that
Node A normally sets a reasonable and secure value low bang
Recommendation consistency is used to estimate the recommendation trust. The outlier detection scheme is a tool for detecting recommendation consistency. After receiving the recommendations from the neighboring nodes, node A firstly computes the mean
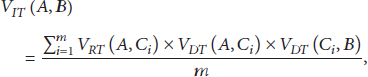
The indirect trust is calculated by employing trust chain, on the condition of legitimate recommendation trust. Node
The trust value of node B for node A is obtained according to the direct and indirect trust value:
The computing process of node trust value is detailed as follows.
Node A firstly broadcasts the Trust Computing Request (TCR) message to the neighbor nodes in the communication range. The TCR message contains the following fields:
Upon receiving the TCR message, the neighbor node
After node A receives the recommendations, it can compute the trust value of node B and decide if node B is reserved in its trusted neighbors set.
3.3. Model of Trusted Tree
Each node sends or forwards the data to the Sink in wireless sensor networks. The communication link is wireless channel, which is easily influenced by the environment. The quality of wireless link is usually measured by the number of data packets transmitted successfully [32–34]. The wireless link is a bidirection channel with ACK message. By using EWMA method, the nodes set time interval to compute the success probability of packet acceptance in the wireless link. The ETX is used to calculate the link quality.
According to the accumulation process of path quality, the network topology can form a tree, and the root is Sink, as shown in Figure 3. To some extent, the path quality in this tree reflects the distance to the Sink, which is seen as the gradient information for routing.

Trusted Tree.
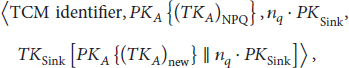
3.4. Establishment of Trusted Tree
Since the bilinear pairing technology has been implemented on the sensor node platform, identity-based cryptography is used in wireless sensor networks [35]. The public key is derived based on the public information, such as the ID of node. The steps of key distribution and authentication between nodes are decreased. The complexity of computing and communication load is effectively controlled. In recent years, there have been many solutions put in wireless sensor networks, such as TinyTate [36], TinyPBC [37], and TinyParing [38]. Based on cryptography technology and trust management, Trusted Tree is constructed.
3.4.1. Key Predeployment
The data is forwarded to the Sink in wireless sensor networks. It is assumed that the Sink is secure and trusted, which is equipped with trusted computing module. Therefore, the Sink is trustworthy and unassailable and is seen as the trusted authority. All of the key materials are stored in the Sink. However, the normal nodes are not tamper-resistant and can be compromised easily. The key and data of node can be extracted, because the hardware of node is cost constraint.
Before the network nodes are deployed, the initial key and the necessary part of key materials are stored in the normal nodes. The five steps are listed as follows:
Each node A has a unique, integer-valued ID, denoted by Choose the hash function Choose the hash function Set the path quality of node A to the initial value Store the relative parameter
Since the Discrete Logarithm Problem is too difficult to be solved, it is infeasible to deduce k from the ID and public key. In other words, although some nodes are captured and compromised, and relative key materials are extracted from them, the adversaries have no way to compute the critical key of other nodes.
3.4.2. Authentication between Neighborhood Nodes
The neighborhood authentication is the foundation of the data transmission between neighborhood nodes. When the legitimate node only forwards/receives data to/from the authenticated nodes, the bogus message is not injected into the network, and the secure data is not swindled by the external attackers. The detailed procedure of neighborhood authentication is the following.
Before the node communicates with the neighbor, the nodes should firstly perform the mutual authentication. Node A broadcasts the neighborhood authentication (NAU) message, which includes message identifier,
Node B responds to this message, when it is within the transmission range of node A. Node B firstly calculates the shared key
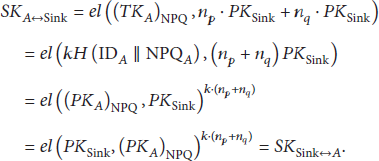
Based on the bilinearity and symmetry of
By the three-way handshaking above, node A can construct the set of its certificated neighborhood nodes, and the shared keys between them are generated at the same time.
3.4.3. Construction Procedure
The Sink is secure and not compromised in wireless sensor networks; otherwise it is difficult to set up the trust management mechanism and secure protocol. Since the path quality of Sink is 0, each node can find a path to the Sink, by the relaying of other nodes. In the construction procedure, the Sink firstly establishes the one-hop trusted path with the neighboring nodes, and then other nodes are added into the Trusted Tree by the nodes that have joined the Trusted Tree. The detailed procedure of construction is represented as follows.
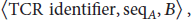
The Sink periodically broadcasts the Trusted Tree (TTR) message, which contains the message identifier, a sequence number
Node A receives the messages from the certificated neighboring nodes. If the current path quality of neighboring node is not the initial value
If the trust value of parent node B is larger than the trusted threshold, node A sets up the Joining Tree (JTR) message by using
Node A sends the JTR message to the parent node B. Node A encrypts the JTR message by using the shared key with node B. If node B is not directly communicated with the Sink, it needs to forward JTR message to the relaying node D, and then node D forwards it to the Sink. In the forwarding process, the trust value of relaying nodes is added into the JTR message. Figure 4 shows the JTR message delivering.

Message delivering.
After the Sink receives the JTR message from node A, the Sink stores the path quality of node A and calculates the new private key according to
Once node A receives the TCO message, it also computes the shared key as follows:
After the shared key is set up and node A has joined the Trusted Tree, node A updates the information with its neighborhood nodes. And the neighbors, which are not added into the Trusted Tree, join the Trusted Tree by node A. In the processing of establishing the Trusted Tree, the Sink stores the secure information of nodes in network.
These neighborhood authentication messages and Trusted Tree construction messages can be piggybacked in the routing protocol messages. So the communication overhead is further reduced.
3.5. Routing Algorithm
In the design of trust based routing, two aspects need to be considered. The first aspect implies checking the trust value of the nodes and path. Only the nodes and path, whose trust value is larger than the set trusted threshold, are placed into the candidate set of the routing decision. The second aspect tries to include the trust value metric and some kind of routing metric, such as hop counts and QoS parameter. In other words, on the basis of trusted nodes, the secure routing with QoS support is built. The routing decision is based on the combination value of the two metrics.
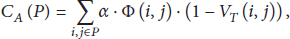
The Trusted Tree-based trust management scheme can be applied in many routing protocols and algorithms. Taking the QoS based routing protocol as example, we add Trusted Tree-based trust management scheme into the TQOS, which implements TQOS using Trusted Tree (TT). Since both the trust and QoS requirement are considered, the cost that combines the trust and QoS requirement is designed as follows:
In order to implement the minimum
In the process of secure routing establishment, source node A broadcasts the route discovery packet (
(a) Algorithm for secure route establishment
(1) Process Initialization; (2) Source node broadcasts RDP to its neighborhood nodes; (3) (4) (5) Receiving Node adds its own information and rebroadcasts RDP; (6) (7) Receiving Node drops RDP; (8) (9) (10) By using (17), the Sink computes the cost for the current route of the RDP; (11) Store the current RDP and its cost into (12) (13) By using (19), select the one with the least cost; (14) Sends the REP back to the Source Node over the selected route; (15) (16) Source node receives the REP; (17) (18) Secure route is established, and start data transmission; (19) (20) End Process
(b) Algorithm for secure route maintenance
(1) Process Initialization; (2) (3) Generates the RER, and broadcasts the RER; (4) (5) Deletes the route, and invokes Algorithm 1(a); (6) (7) Deletes the route; (8) (9) (10) (11) (12) Deletes the route; (13) (14) Broadcast the RER; (15) (16) Establish the new route by using Algorithm 1(a); (17) End Process
The nodes on the Trusted Tree monitor and observe the behavior of neighbor nodes. When the trust value of observed node is lower than the trust threshold, the route error (RER) message is generated to notify other nodes to change the route.
For example, node E is compromised. When the malicious behavior of node E is detected by node D, it broadcasts
4. Performance Evaluation
All of the simulation experiments are run in the TOSSIM simulator [39]. TOSSIM inherits the implementation and design of TinyOS, which provides the tool to generate network topology and uses CPM algorithm to simulate noise. The scenario that is used in our experiments consists of a 100 m × 100 m square area. The Sink is placed at the edge of the experiment area. The nodes are uniformly randomly distributed, where the average node density is about 2 to 6 nodes in each 20 m × 20 m square subarea. And the distance between any two nodes is more than 7 meters. The ID of node is orderly numbered by their distance to the Sink from near to far. Among the total number of the nodes in the experiment, 10 percent nodes are selected as the malicious nodes. Other normal nodes generate the sensed data packets by the period of random time interval. Each node can have the difference task for monitoring the environment. The period of sensing data or event driven time is also different. The nodes send a packet at the random time interval, which is randomly set from 5 to 15 seconds. The simulation experiments are run for 6000 seconds. The main experimental parameters are listed in Table 1.
Simulation settings.

We implement and compare TQOS, TQOS using ReTrust, and TQOS using TT (Trusted Tree). After the malicious and normal nodes are selected, each test is executed about 5 times, and then their average value is calculated.
4.1. The Security and Performance of Trusted Routing
The trust management scheme is the effective method to defend the attacks in the network routing. In the tampering attack, the malicious node forwards the messages in the routing path, after receiving and tampering the messages. So the trust management scheme needs to cooperate with the cryptographic technique to detect the malicious nodes. And then the trust management scheme recalculates the trust value of the nodes and path for the routing algorithm.
As shown in Figure 5, the average delivery ratio of the packet decreases significantly when the malicious nodes launch the attack, while the average delivery ratio increases after the malicious nodes are detected out. At the initial stage of network running, the average delivery ratio is close to 1. Since the tampered messages are dropped, the packet loss ratio increases and the average delivery ration suffers the degradation. Compared with TQOS, the TQOS using ReTrust and TQOS using TT can earlier detect the malicious nodes, because the direct trust and indirect trust are used in them. TQOS has only direct trust by observing the neighbor nodes, so the detection efficiency of TQOS is lower than them. However, the trust value node and path are computed in dynamic time window of TQOS using TT, and the path quality gradient of Trusted Tree can speed up the building process of secure routing path. Therefore, the average delivery ratio in the new path of TQOS using TT increases more than the TQOS using ReTrust.

Average delivery ratio under tampering attack.
Figure 6 represents the average transmission latency of the 30 normal nodes, which are randomly selected among the source nodes. The transmission time of packet is the base for the data transmission. The statistics of latency is based on the transmission time of packet. According to the transmission time of each packet from the source node to the destination node, the latency is counted and calculated on the Sink. Based on the link quality of Trusted Tree and the routing discovery, the TQOS using TT can get higher performance and has the lower transmission delay. TQOS using ReTrust has more stable routing path than the TQOS. Since the direct trust and indirect trust are used, the trust value of path is faster calculated for the routing. So the performance is enhanced.

End-to-end delay under tampering attack.
In the TQOS using TT, the routing path is built on the Trusted Tree. The next hop node is the trusted neighbor node, which is from the authenticated neighbor nodes set. And the neighbor nodes, which take lower path quality as routing gradient, forward the routing discovery packet for route establishment. The massive flooding of routing message is avoided. So TQOS using TT has the lower route load as shown in Figure 7. Due to the large number of broadcast and rebroadcast packets sent and forwarded, TQOS has much higher cost. Based on the scheme of TQOS, the direct trust and indirect trust communication of TQOS using ReTrust result in more load.
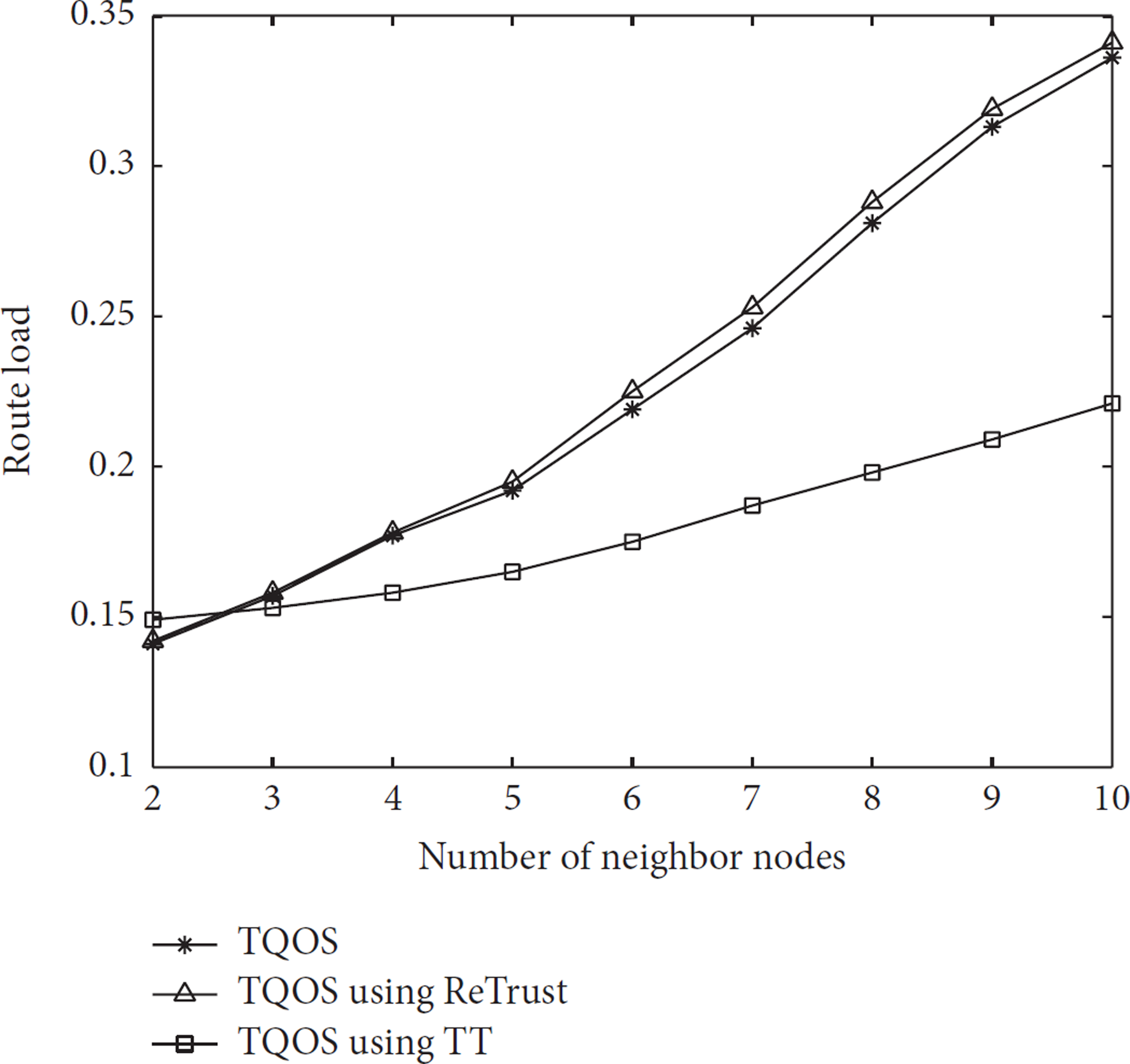
Route load.
4.2. Detecting Malicious Behavior
The malicious node can continue to change between the good and bad behavior, so as to achieve the purpose of damaging the network and avoid being detected. Firstly, we execute the simulation, in which the malicious nodes launch the on-off attack with dropping 50% of packets. The attack effect is shown in Figure 8. Compared with the tampering attack, the average delivery ratio decreases gently in the presence of the on-off attacking, but many packets are dropped. This is because the malicious nodes are difficult to be detected. The message authentication mechanism in TQOS is modified and replaced by the direct trust computing. The average delivery ratio is lower when only direct trust is used. But the malicious nodes are earlier detected out in the TQOS using ReTrust and TQOS using TT. And TQOS using TT has higher delivery ratio than TQOS using ReTrust, because of the dynamic time window and Trusted Tree.

Average delivery ratio under on-off attack.
In the presence of on-off attack, the average transmission latency of the 30 normal nodes is shown in Figure 9. The transmission latency of data packet is computed. In TQOS, the instability of the trust value results in the fluctuation of the delay. TQOS using ReTrust can alleviate the instability of the trust value. By the dynamic time window and Trusted Tree, TQOS using TT can quicker find out the malicious node and enhance performance on the latency.

End-to-end delay under on-off attack.
When the malicious nodes launch the on-off attack with dropping 10% of packets, the attack effect is shown in Figure 10. TQOS and TQOS using ReTrust are difficult to detect out the attack. However, TQOS using TT can prolong the size of dynamic sliding window to find out the malicious nodes and raise the average delivery ratio.

The effect of lower probability on-off attack.
When the bad-mouthing attack is launched, the malicious nodes detection performance is shown in Figure 11. Let D denote the set of malicious nodes that are detected out. M represents the set of malicious nodes. The malicious nodes detection performance is defined as
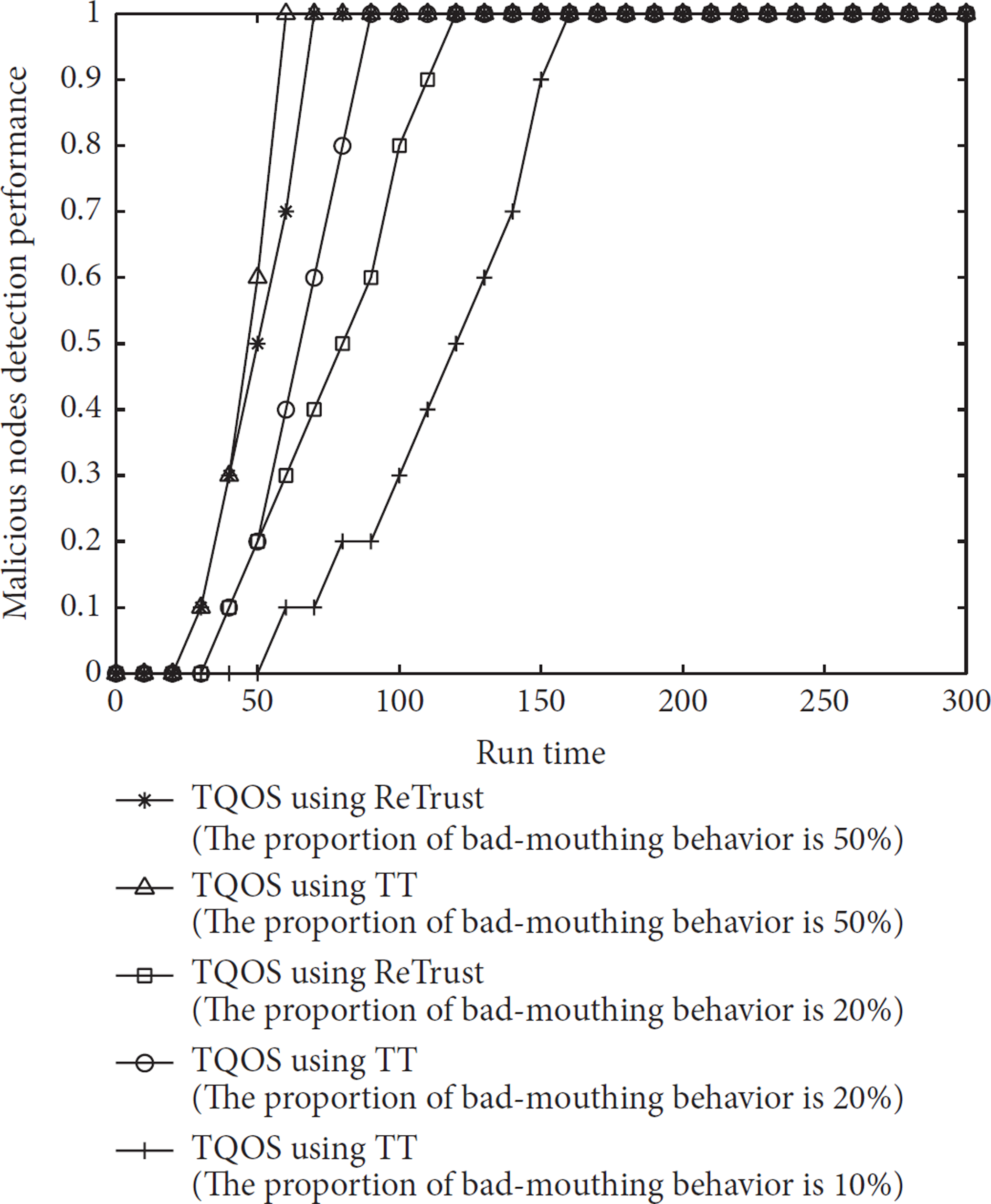
Malicious node detection performance.
4.3. Residual Energy
After the simulation is completed, the residual energy of normal nodes is shown in Figure 12. For TQOS using TT, the average value of residual energy is 0.679, and TQOS and TQOS using ReTrust are, respectively, 0.589 and 0.561. TQOS using TT does not use the message redundancy and route redundancy to build secure routing. So the number of messages is decreased. TQOS using TT has the higher residual energy. The building process of routing path is shortened by introducing Trusted Tree. The network lifetime is longer in TQOS using TT.

Residual energy.
5. Conclusions
In this paper, we proposed Trusted Tree-based trust management scheme for secure routing. The attacks in wireless sensor networks are firstly analyzed. Based on the distributed trust model with the detection of direct trust and indirect trust, the dynamic time window is used to compute the trust value of nodes. Then Trusted Tree is established on the trusted nodes. The node's path quality in Trusted Tree can aid the routing discovery process to set up the routing path. Trusted Tree-based trust management scheme can be added to the many secure routing algorithms, such as the QoS based secure routing algorithm. Compared with some current algorithms with the trust management scheme, the routing algorithm with Trusted Tree shows better performance and security, according to results of the simulation experiments.
In the future, we plan to use message type weight to develop the distributed trust mode, which can both improve the detection efficiency and enhance the network performance. We will add our proposed trust management into some actual network protocol, such as IETF RPL protocol.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work is supported by the National Natural Science Foundation of China under Grant nos. 60903159 and 61173153, the Special Fund from the Central Collegiate Basic Scientific Research Bursary N110818001 and N100218001, and Science and Technology Planning Project of Shenyang City under Grant no. 1091176-1-00. The authors would like to thank NSR (Neusoft Group Research) and research colleagues for support.