Abstract
A novel network architecture to be deployed in Korea is so called HTN (highly trusted network). The aim of HTN is the seamless communication of information in a secure manner, anytime and anywhere, in the national administration network infrastructure. In this paper, we present the results of information security modeling for the HTN. Through the use of security modeling procedure, we derive the requirements and corresponding technology for security control of the system by analyzing threat elements and attack possibility. First we analyze threat of each component for the HTN by STRIDE modeling and later construct an attack tree by analyzing attack examples for every threat. Finally we propose the security requirements and technology to respond against them, based on the analyzed threats and attack examples.
1. Introduction
HTN (highly trusted network) is a network which enables the usage, communication, and share of information in a seamless and secure manner, anytime and anywhere, regardless of wire or wireless, and may be defined as follows. “From the aspects of confidentiality, availability, quality of service, mobility, and so forth, it refers to the network technology which makes it possible to communicate between terminals, servers, and network devices in a secure manner across unreliable networks.”
Through the construction of HTN, users can securely use, communicate, and share services they want, anytime and anywhere, by using wired or wireless terminals. The novel HTN proposed in this paper consists of wired/wireless hybrid terminal, wireless AP (access point), networks, servers, and an integrated control management system. Based on this configuration, we would like to operate the HTN by using a virtualization technology.
The aim of development of HTN is to construct trusted networks so that public officers in the Korean administration network may perform their task, anytime and anywhere, in a secure manner by using wired/wireless terminals. The Korean administration network is so far being operated in a closed network environment.
While the officers may only access servers in their own domain or network which they belong to in the existing closed networks, they can perform their tasks even during their business trip to other areas via network authentication in the virtualized HTN environment. Based on the analysis of the system, we may classify the components of HTN into hybrid terminal, wireless AP, network, cloud, and global control management system. In order to operate the HTN, it is necessary to have terminal virtualization, network virtualization, and cloud technology.
IP (Internet Protocol) network technology inherently has a vulnerable security architecture. Therefore we need to develop the technology for the secure operation of HTN. The virtualization technology used for the construction of HTN is generally known as an efficient technology for the operation of national infrastructure by network separation. By the way, it also invokes new problems with regard to the security. Furthermore, as the age of IoT (Internet of Things) and IoE (Internet of Everything) is around the corner, the research on the information security of virtualization for the operation of HTN is necessary in order to provide the protection of main facilities and data. Therefore, in this paper, we would like to perform information security modeling and analyze the results for the operation of HTN in a virtualization environment.
Security modeling may be used to develop the security policy model of the corresponding system [1]. In a lower level of trust, this model becomes a general protection philosophy (principle) of the system and also includes both unofficial and official protection mechanisms in a higher level. In order to prevent the information of HTN from illegal disclosure, modification, loss, and disruption, the sensitive information must be protected. Accordingly the security policy models of HTN must be constructed, evaluated, and used.
The closely related topics for the security modeling consist of the precise description of security policy objective, design specification and verification, the analysis of covert channel, and the analysis of implementation conformance. The security objective must include confidentiality, integrity, and DoS (denial of service). The security model precisely describes the main security points and the relationship of system activities.
The main goal of security model is to make sure the necessary level for the successful implementation of core security requirements. The security requirements must be presented at the initial stage of system development process. The identification of security requirements must accompany the identification of the method to satisfy the security objective, including the higher level of security objective, automated, procedural, and physical protection methods. The identification of these types of security requirements and derivation of requirements from the identified higher level of security objectives are initial problems for the protection principle.
This paper uses attack tree model and threats modeling as security modeling methods. We derive threat elements and attack paths through the modeling process and also propose the necessary requirements and response technology for the security control in order to respond against those threats.
2. Network Environment
2.1. Closed Network
The network infrastructure closely related to our daily life is mostly based on the Internet. Thus, the information security accidents including large-scale private information leakage have been reported day after day and there is the growing concern on the secondary damage. “Enforcement Decree of Act on Promotion of Information and Communications Network Utilization and Information Protection Etc.” proclaimed on August 17, 2012, enacted the provision to block the external network (network separation) including computer accessing to the personal information processing system from February 18, 2013. Network separation is to separate the Intranet from the Internet access to block the unauthorized access between two networks [2].
For reducing the information leakage and damage by unauthorized penetration through the Internet and Intranet, the Intranet is implemented to block external access for safe operation. The external network separated as described above, that is, the network without any access point from Internet, is called “closed networks.” There are two kinds of network separation: physical separation without any connection from external networks and logical separation blocking unauthorized access using firewall and switch or network separation devices.
Closed networks by physical or logical network separation are applied to safely use the network for businesses. The external access to steal the personal information is blocked by separating the Intranet from the Internet. It is very effective to prevent security accidents including personal information leakage by blocking the intrusion path. However, the closed network disconnects the system for exchanging information and cooperating with external organizations for business purposes and blocks the business processing and acquisition of knowledge information through the Internet.
Figure 1 illustrates the concept for operating the closed network.
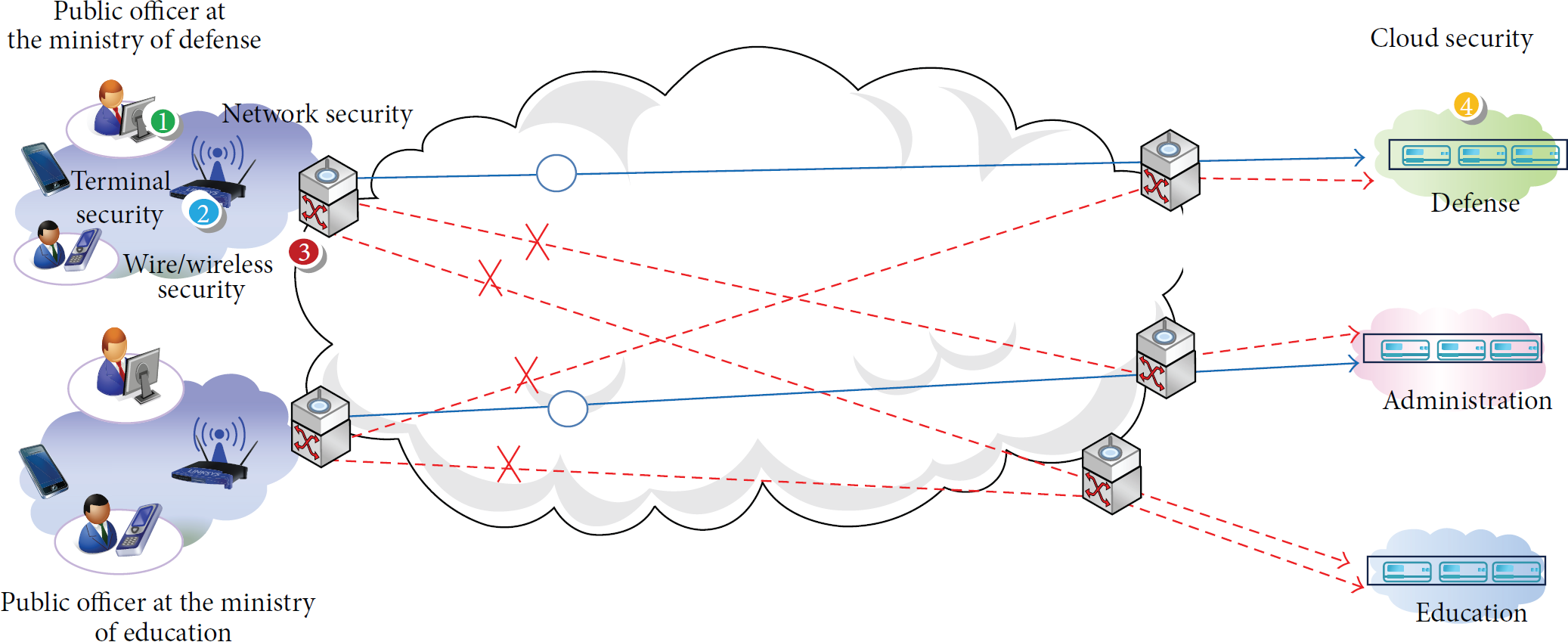
Conceptual diagram of closed networks.
As shown in Figure 1, the closed network enables government workers in different ministries to get access to the Intranet where they are authorized and basically blocks them to get access to the Intranet of other ministries.
2.2. Cloud Computing
Figure 2 illustrates the cloud computing environment. Cloud computing is the technology or service integrating a variety of information resources including HW, SW, and data into the central data center (cloud) and enabling everyone to use it in any place at any time through the communication network. The virtual resources include the following functions [4].
Sharing: a number of virtual resources are connected to one physical resource. Aggregation: a number of physical resources are integrated for physical utilization and management. Emulation: the functions which do not exist in the physical resources are enabled in the virtual resources. Insulation: the physical resource can be switched without any influence on users in the mutual mapping between physical and logical resources.
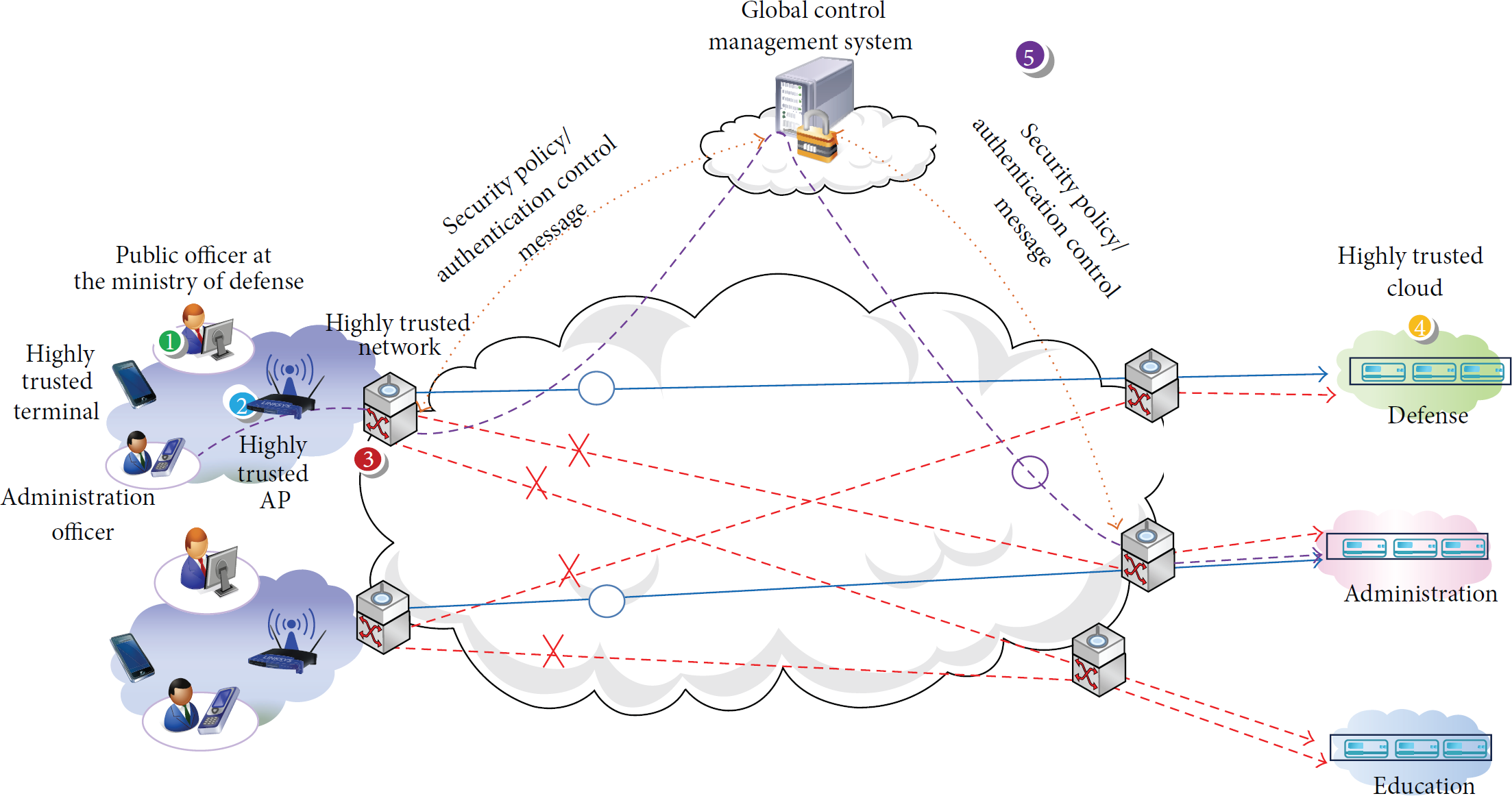
Cloud computing environment.
As described in Figure 2, the national administrative network with the cloud computing environment may enable government workers to safely execute the public businesses in any place at any time using the wired or wireless exclusive or hybrid terminals. The analysis on the vulnerability of the systems and risks and modeling is prerequisite for the network operation in such highly trusted environment. Moreover, it is required to develop the technologies to analyze security attack scenario and to respond against such attacks.
3. Introduction on Security Modeling
3.1. Modeling Procedure
Schneier introduced the attack tree for modeling the system security in 1999 [5]. The cyber security analysis using this attack tree helps to identify the basis of the system intrusion. Figure 3 illustrates the security modeling procedure applied to the highly trusted network [3]. Two similar terms used in this paper are defined as follows [6]:
Threat: environment, ability, or event invading and damaging security; in other words, potential risk trying to utilize the security vulnerability. Attack: attack to security system by elaborate attempt infringing the system security policy (in particular, methodological or technical aspects) or by skillfully evading security system.

Security modeling procedure [3].
3.2. Implementation
The implementation procedure for security modeling is described below [3].
(1) Preparation. This includes system documentation (system specification, network diagram), security assessment criteria, and schedule arrangement.
(2) System Identification. The system and operating environment are identified in this step as specified in the following:
System components and functions, Interaction between components, Interaction with other systems, Users and system management, Interaction of networks, System security mechanism.
(3) Threat Identification. This includes identification of vulnerability and threat, identification of system vulnerability and access point to vulnerability, and listing threat sources and types.
(4) Construction of Attack Tree. The node identifying and indicating the attack targets in the attack tree is root node and the subattack target is segmented as nonleaf node (AND, OR). The final subattack target and the most detailed attack target is the leaf node. Figure 4 presents the example of the attack tree [3].

Example of attack tree [3].
The attack tree in Figure 4 comprises the root node G0, intermediate nodes G1 and G2, and leaf nodes G3, G4, G5, and G6. The possible attack example to G0 is system collapse and that to G1, G2, G3, G4, G5, and G6 is software collapse, Intrusion Detection System (IDS) destruction, operating system collapse, application software collapse, network IDS destruction, and host IDS destruction, respectively.
(5) Refinement Decision. This step determines the necessity of additional refinement for the tree and checks if all identified threats are defined on the tree.
(6) Attack Tree Analysis. This step generates all possible attack scenarios and determines the security risk level.
(7) Security Threat Assessment. This step compares SRL (system risk level) with DRL (desired risk level). If SRL > DRL, this step creates the list of all possible security control (SC) approaches against the attack scenario. SC is classified into management, operating, and technical control.
(8) Selection of Responses or Requirements. This step determines the efficiency of security control to reduce SRL of the attack scenario. This paper applies the requirements instead of the security control approaches which can be applied in reality because the highly trusted system is still on the stage to set up the concepts.
(9) Report Review and Feedback. Report review and feedback are ongoing responses to investigate the analysis process in other steps. This step generates the analysis report when each step is completed and transfers the report to a reviewer for verifying the analysis results. Next, the analysis results are reflected before starting the next step of each completed step.
4. Threat Identification
This section classified major components for operating the highly trusted network into 5 categories, hybrid terminal, wired/wireless AP, network, cloud, and control system to identify the threats per component in the system identification step. This paper adopted STRIDE model proposed by Microsoft to identify the threats.
4.1. Stride Threat Modeling
Threat modeling is a kind of security modeling approaches. It aims to identify the possible problems more quickly during the operation of any information system. It has to be implemented earlier during the system development or design stage.
Two key responses of threat modeling are the key security design of the system and the definition on the possible attack groups to be considered [7]. Three general strategies for threat modeling are asset, attacker, and software [8]. The most systematic threat modeling is the software modeling. Software-centric modeling focuses on the software to be implemented or system to be installed.
This section executes the threat modeling based on STRIDE developed by Microsoft. STRIDE means 6 kinds of security properties, spoofing, tampering, repudiation, information disclosure, DoS (denial of service), and elevation of privilege [3, 6]. STRIDE draws the diagram showing the operation of system or software and examines the possible events per element on the diagram. STRIDE threat modeling aims to help the design process by identifying the attack types which may occur in systems or software in advance. OWASP also recommends STRIDE modeling by Microsoft. OSWASP describes it in the web application. However, STRIDE modeling can be applied to the virtualization structure in the highly trusted network. Table 1 presents the STRIDE threats, relevant security services, definition, and most possible threat targets [9].
Stride threats [9].

4.2. Threat Modeling per Component
This section points out the security threats identified per estimated component in the operating environment of highly trusted network. Table 2 presents the threat elements and examples of attacks in the hybrid terminals [10, 11].
Threat elements and attack examples of hybrid terminals.

Table 3 presents the threat elements and examples of attacks to wired/wireless AP [12].
Threat elements and attacks examples of wired/wireless AP.

Table 4 demonstrates the threat elements of network and the attack examples [13].
Threat elements and attack examples of networks.

Table 5 presents the threat elements and attack examples of the cloud server [14].
Threat elements and attack examples of cloud servers.

Table 6 shows the threat elements and attack examples of the management system.
Threat elements and attack examples of management system.

5. Construction and Analysis of Attack Tree
5.1. Construction of Attack Tree
This section constructs the attack tree on the basis of the threat modeling discussed in Section 4. Figure 5 illustrates the simple attack tree of highly trusted network proposed in this paper.
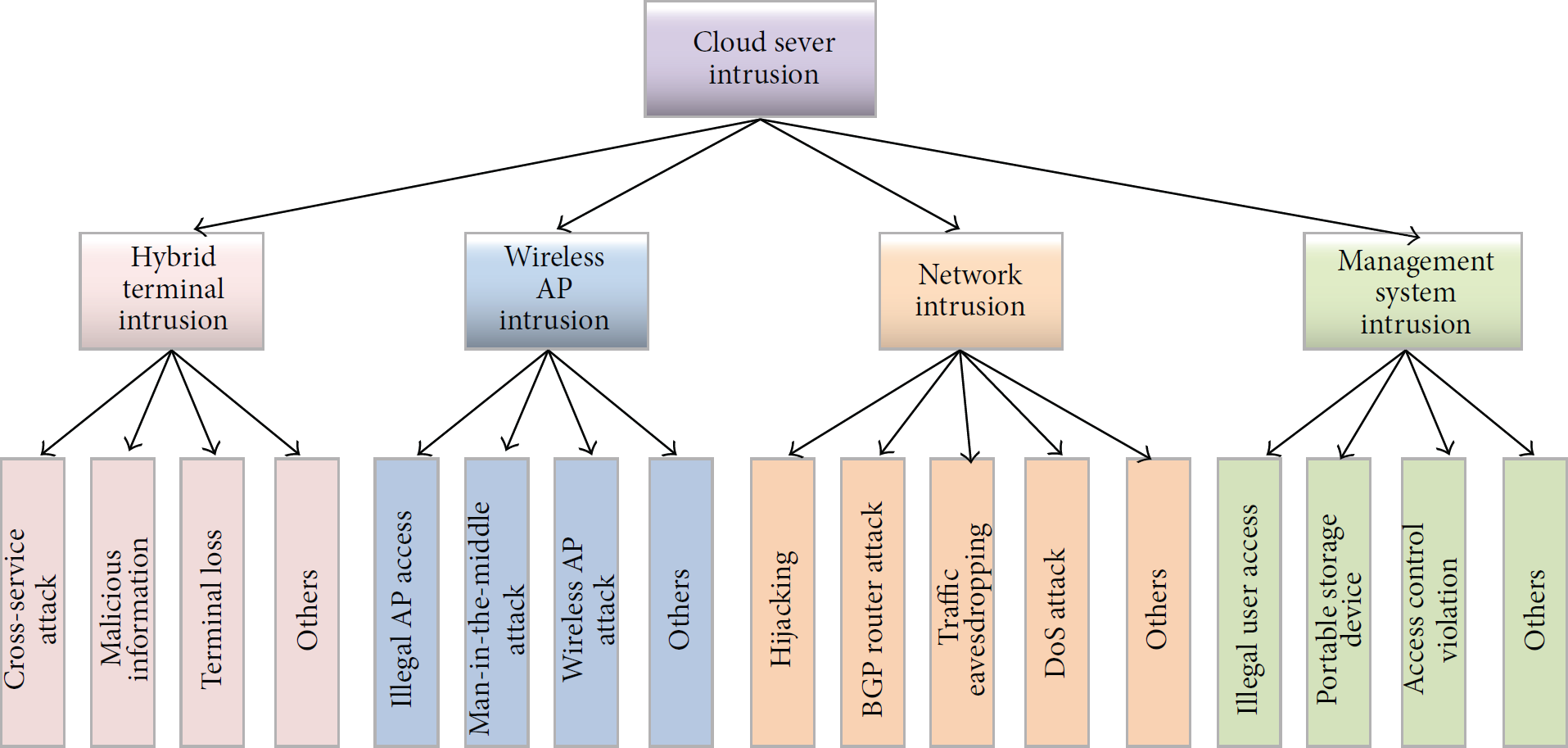
Attack tree of highly trusted network.
The attack tree in Figure 5 was generated in the simplified form by applying the attack tree modeling presented by Schneier on the basis of the identified security threat elements. The attack tree in Figure 5 comprises the nodes as specified below.
If any attacks including cross-service attack, harmful information, or loss of a terminal happen in the leaf node in intermediate node 1, the hybrid terminal can be infringed. When the hybrid terminal is attacked, the cloud server, the ultimate target, can be attacked. Even the attack to wireless AP or network may cause the cloud server, the ultimate target, to be collapsed by attack. The management system is very important system which sets up, manages, and monitors security policies. It can act as the element to attack the cloud server as follows:
Root node: cloud server. Intermediate nodes 1~4: hybrid terminal, wireless AP, network, and management system. Leaf nodes of intermediate node 1: cross-service attack, harmful information, loss of a terminal, and so forth. Leaf nodes of intermediate node 2: unauthorized AP access, mediator attack, wireless AP attack, and so forth. Leaf nodes of intermediate node 3: hijacking, BGP router attack, traffic tapping, DoS attack, and so forth. Leaf nodes of intermediate node 4: unauthorized user access, portable storage media, access control infringement, and so forth.
Figure 6 describes the attack path in accordance with data flow between devices in the security policy-based virtualization information security model in the highly trusted network system.

Attack path by data flow between devices.
The information security model in Figure 6 shows the trusted network and the possible security problems per component. Such information security model enables identifying the security policies against the possible threats to the highly trusted network and to operate the highly trusted network based on the identified security policies.
The security policy-based virtualization information security model in Figure 6 illustrates the diagram with hybrid terminal, wired/wireless AP, network, cloud server, and management system and describes the possible threat elements per component in the diagram. The model enables analyzing the locations and methods of threats or attacks. As a result, the highly trusted network is expected to be operated in a secure manner by applying the security control and response technology on the basis of the security policies.
5.2. Analysis of Attacks
OWASP recommends the STRIDE threat modeling process by Microsoft and describes the web application. However, the STRIDE threat modeling can be also applied to the virtualization structure. OWASP (Open Web Application Security Project) acknowledges OWASP Top 10 by investigating information exposure, malicious file and script, and security vulnerability related to web and analyzing the vulnerability of 10 web applications. Top 10 list includes the following: (1) injection, (2) broken authentication and session management, (3) Cross-Site scripting, (4) unstable direct object reference, (5) security misconfiguration, (6) sensitive data exposure, (7) access control to lost function level, (8) Cross-Site request forging, (9) components with known vulnerability, and (10) nullified requests and transmission. Table 7 shows the possible attacks identified by classifying the threats of the components in the highly trusted network using the OWASP Top 10 list in 2013.
Analysis of attack possibility for HTN by OWASP classification.

In accordance with the analysis for the security of highly trusted network, the protection against (1) injection, (2) broken authentication and session management, and (6) sensitive data exposure was revealed to be very important. It was also found that the protection against (7) access control function and (3) and (8) cross-service attack was important. It was also estimated that the security response for (5), (9), and (10) is required to be basically implemented. (4) Unstable direct object reference requires the response to protect because it could be serious in web environment.
6. Analysis of Requirements and Response Technology
The procedure after the identification of threats and construction and analysis of attack tree in Figure 3 is the security threat assessment. It compares the system risk level and demand risk level. If SRL > DRL, all possible security control (SC) approaches against attack scenario are listed. DoA (Degree of Assurance, that is, acceptable risks) needs to be determined by asset identification in advance in this step. However, the assets were not accurately identified due to the characteristics of this study. Thus, DoA could not be determined. Accordingly, this section describes the requirements for the next step and the selection of response technologies.
6.1. Security Attributes and Service
This section identifies the security requirements for the components for highly trusted network on the basis of the threat identification in Section 4 and the construction and analysis of attack tree in Section 5. The information security service to be enabled by highly trusted network includes access control, accountability, authentication, availability, confidentiality, and integrity. Access control is to restrict the information flow between a subject and an object. Access control types include DAC (discretionary AC), MAC (mandatory AC), and RAC (role-based AC). Accountability is to trace how and by whom a security event occurs when it occurs. It means the ability to identify a subject and trace its activities. The postsecurity technologies for accountability include watermark and forensic technology. Authentication is the security service to verify that a subject using the resources of an object is the authorized user. Authentication includes confirmation of identity, confirmation by a third party, authentication by a sender, message authentication, and entity authentication.
Three security goals for computer and network are confidentiality, integrity, and availability. They are called CIA triad. Availability is to allow an authorized user to get access to the system resources. Confidentiality means to allow only the authenticated subject to read the confidential information. Integrity is to check if the received data is identical to the data sent by an authenticated subject. Figure 7 illustrates the mapping relation between security services of highly trusted network to be explained in this section and the security property of STRIDE model.
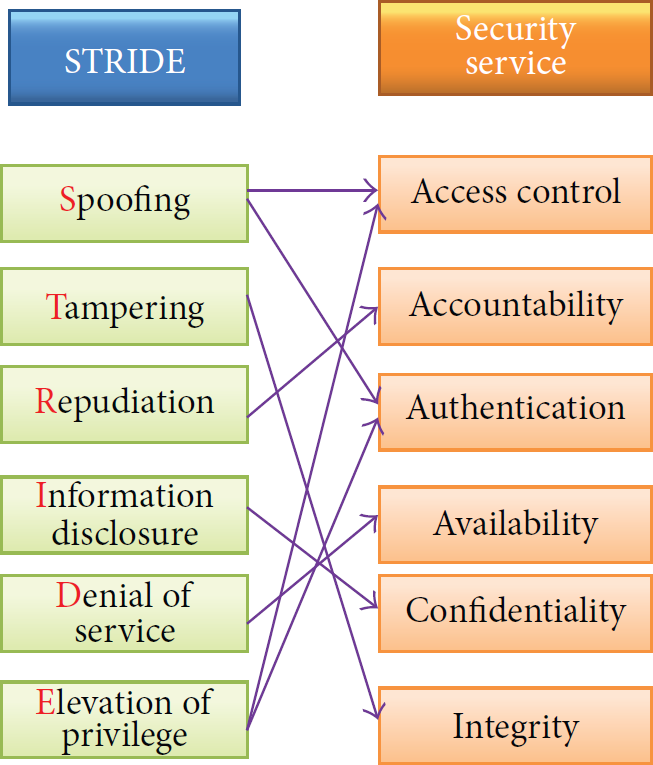
Relation between STRIDE security attributes and security service for HTN.
6.2. Security Requirements
This section describes only the security requirements of highly trusted network cloud for want of space among the security requirements on identified components [15–24].
Cloud is operated on the basis of virtualization. The security requirements for cloud include encoding between VMs because of the internal vulnerability between VMs (Virtual Machines). Furthermore, the communication monitoring between VMs is required for coping with the attack using the internal communication in virtualization space. Detection of the transmission of malicious code between VMs and DDoS security through network to use cloud service is identified as the key security requirements. Table 8 presents the security requirements for cloud. Accordingly, the safe cloud management technology is required.
Cloud security requirements for HTN.

6.3. Security Requirements Technology
From Tables 9 to 13, we analyzed the security requirement technology per component on the basis of the identified security requirements of highly trusted network in Section 6.2. Table 9 presents the security requirement technologies of hybrid terminal.
Required security technology for hybrid terminal.

The congestion control technology in the availability service for hybrid terminal listed in Table 9 means the control technology against the failure of phone (VoIP) connection with the application run on a hybrid terminal. Table 10 shows the required security technology for wireless AP.
Required security technology for wireless AP.
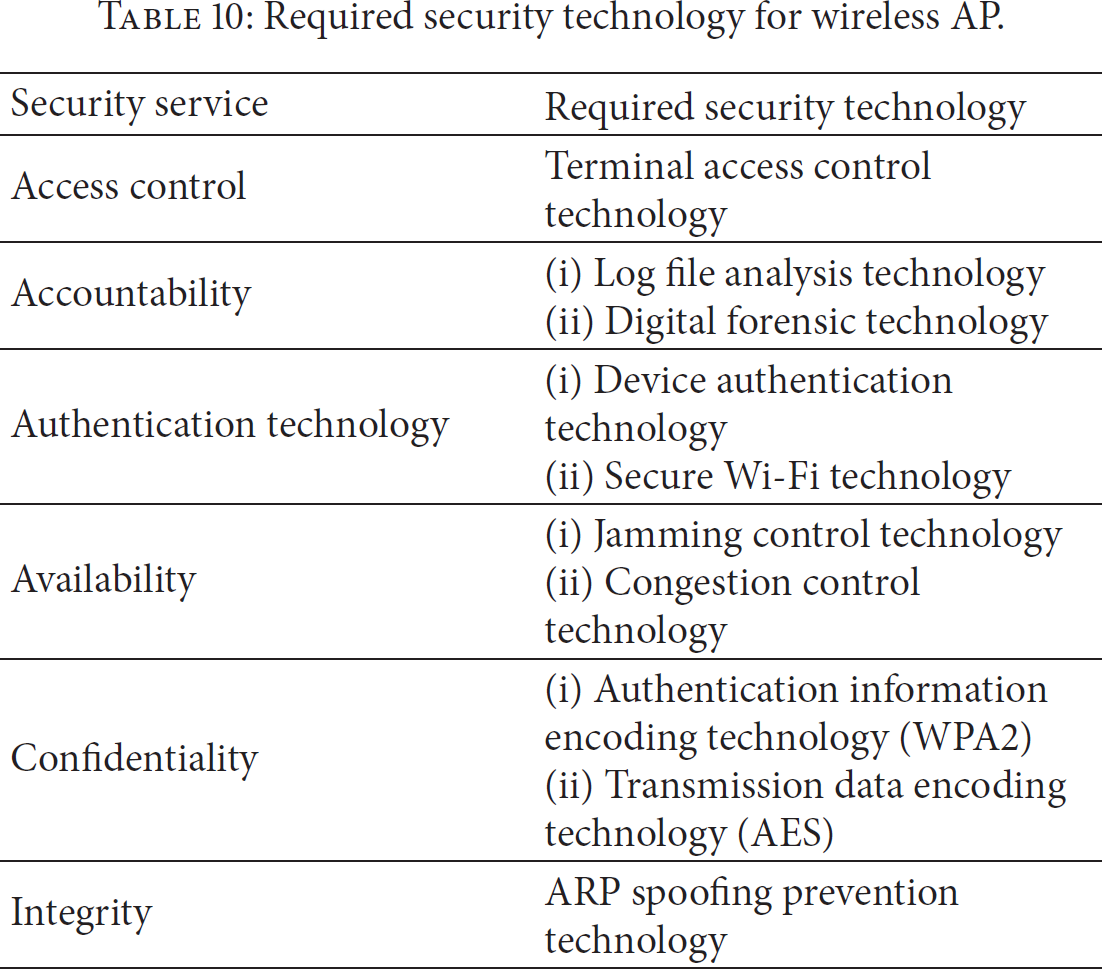
Congestion control technology in the availability service for wireless AP in Table 10 means the technology to detect, interrupt, and control the excessive connection requests intentionally made from a number of hybrid terminals. Safety related to encoding effective until 2030 is specified as follows [25]: 112 bits for symmetric encryption system and hash function; 2,048 bits for public key; 224 bits for private key.
Table 11 describes the required security technology for network.
Required security technology for network.

Congestion control technology in the availability service for network in Table 11 means the load balancing technology for traffic beyond the network bandwidth to be provided. Table 12 describes the required security technology for cloud.
Required security technology for cloud.

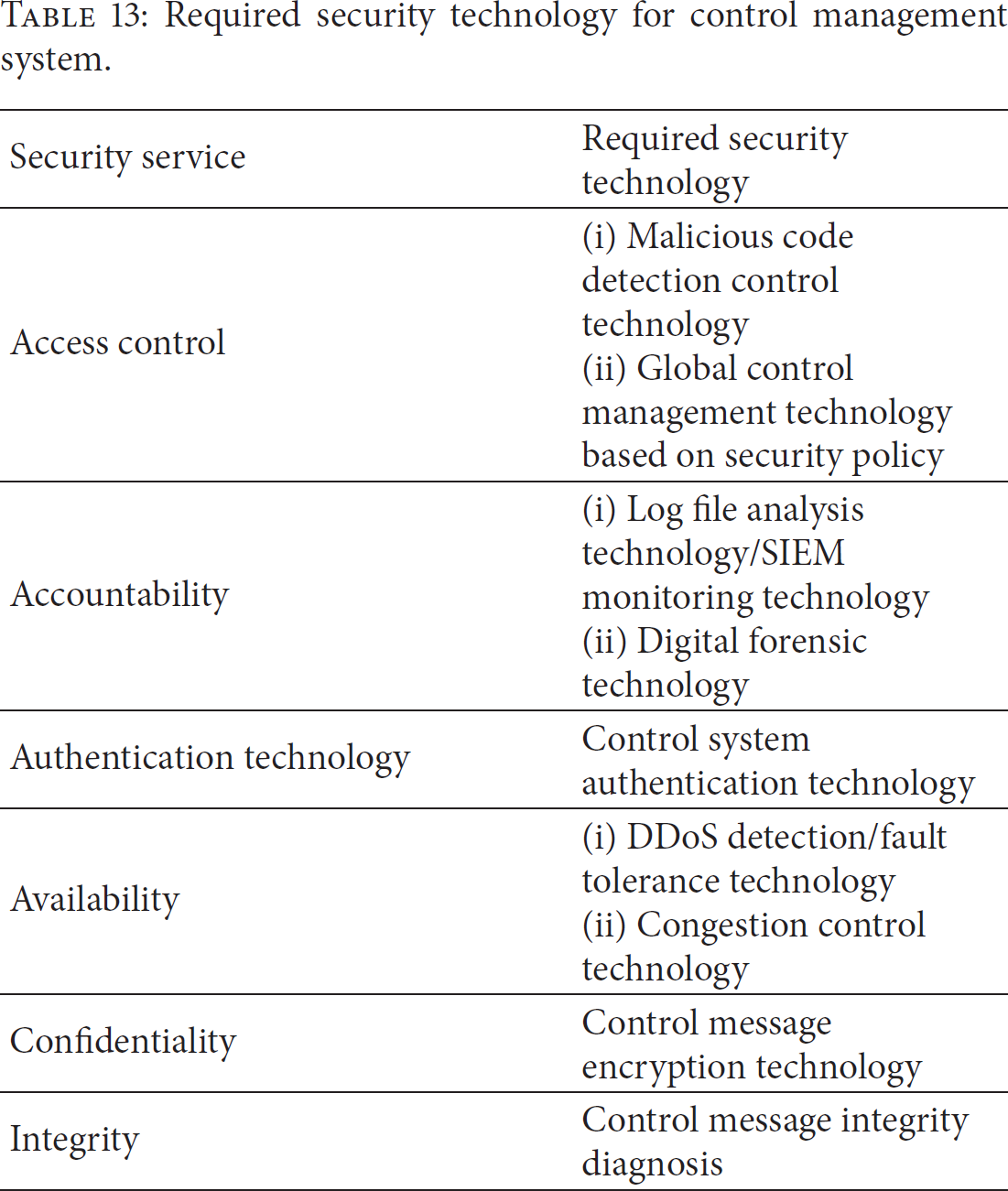
Required security technology for control management system.
Congestion control technology in the availability service for cloud in Table 12 means the technology to control consecutive threats using physical resources and another virtual machine in the physical resource by inserting the intentional code into the cloud virtualization. SIEM monitoring technology prevents the leakage of internal information as well as external attacks by monitoring the internal and external threats through the security information and event management in the information system in a company.
Table 13 presents the required security technology for control management system.
The congestion control technology in the availability service for control management system in Table 13 enables security policies to be requested and transmitted without delay along with a variety of services provided by the control management system. Refer to [26, 27] for the existing security technologies for cloud which can be applied to the highly trusted network.
7. Conclusion
The businesses by important national organizations including national defense, finance, administration, and power supply have been executed on the basis of the Internet in accordance with the remarkable development of the Internet. The Internet is vulnerable to the modification of packets transmitted through it. For safe and reliable business execution against such threats to the Internet, the highly trusted network has been investigated. This paper implemented the security modeling to identify the cyber security threats and the security requirements for the operation of highly trusted network.
Six kinds of threat elements and possible attacks per threat element of highly trusted network (HTN) were identified using the STRIDE threat modeling for identifying the information security requirements for highly trusted network. HTN attack tree was implemented and attack path and possibility were analyzed using the approach proposed by Schneier. In accordance with the analysis, it was revealed that the attack possibility against injection, session management, and sensitive data leakage was high on the basis of OWASP vulnerability classification in 2013. Then, the information security requirements and relevant response technologies for the operation of highly trusted network were analyzed for each component of hybrid terminal, wired/wireless AP, network, cloud, and control management system. The requirements were classified into 6 security services, access control, accountability, authentication, availability, confidentiality, and integrity. In accordance with the analysis, the security requirements were derived including the client virtualization and safe access control technology for hybrid terminal, secured Wi-Fi technology for wireless AP, highly trusted gateway technology applying network security technology on the basis of SDN (Software Defined Network) for network, safe cloud management technology against consecutive threats in virtual machine for cloud, security policy management technology related to the security policy, and control in the highly trusted network for the control management system. Furthermore, the response technology based on the identified requirements was analyzed and proposed.
Further study will implement the quantitative and qualitative threat and attack modeling and complete the security modeling procedure for determining the practical risk levels required in the security risk assessment step and utilizing them to develop the actual security control system.
Footnotes
Conflict of Interests
All the authors certify that there is no financial and commercial conflict of interests in this study.
Acknowledgment
This research was supported by the MSIP (Ministry of Science, ICT and Future Planning), Korea, under the ITRC (Information Technology Research Center) support program (NIPA-2014-H0301-14-1021) supervised by the NIPA (National IT Industry Promotion Agency).
