Abstract
Wireless sensor networks (WSNs) contain a large number of resource-constrained and energy-limited sensor nodes that are generally deployed in an open environment. Those sensor nodes communicate with each other or with a base station via wireless channels. Therefore, secure access control is an important issue in WSNs because sensor nodes are susceptible to various malicious attacks during the authentication and key establishment phase and the new node addition phase. In this study, we propose a new access control method based on elliptic curve cryptography and the chameleon hash function. This method addresses the security problems in the existing research. It also has additional advantages since it does not require time synchronization between communication nodes, nor does it require node verification tables. In addition to our proposal, the correctness, security, resistance to possible attacks, and the performance of the proposed method are analyzed and evaluated. The results of our study demonstrate that the proposed method has an outstanding performance and fulfills all the requirements for secure communication in WSNs.
1. Introduction
Wireless sensor networks (WSNs) consist of base stations and a large number of resource-constrained and energy-limited sensor nodes that are typically deployed in various environments. Since the base stations and sensor nodes communicate with each other via wireless channels [1], the WSN system is threatened by malicious security attacks.
In WSNs, after a prolonged period of operation, the power of some of the sensor nodes gets exhausted. This occurs due to uneven distribution of radio transmission load or damage caused by unpredictable events. The base station must dynamically add new nodes to the WSN to ensure the coverage and connectivity of sensor nodes. Following the addition of a node, the new node is authenticated by the neighboring nodes, and it establishes shared session keys with them for secure communication.
In order to attack or access communication information, malicious nodes may modify received messages, eavesdrop on transmission messages, insert false messages, or provide misleading information to legitimate sensor nodes. Therefore, access control security is a major concern in WSNs.
Zhou et al. [2] proposed an access control protocol to improve the performance of traditional public-key-based encryption protocols. This protocol was based on the elliptic curve. Each sensor node could sustain for a tolerable time interval before it was compromised, rendering the scheme unsuitable for certain practical applications. Huang [3] proposed an efficient access control protocol based on the elliptic curve and hash chains. This scheme could easily add new nodes and resist various attacks. Kim and Lee [4] proposed an enhanced access control protocol based on the scheme proposed by Huang. Their research indicated that the method proposed by Huang could not resist replay as well as active attacks. Further, it lacked hash chain renewability after the authentication and key establishment phase. In 2010, Shen et al. [5] and Zeng et al. [6] demonstrated that the scheme presented by Kim and Lee was vulnerable to masquerade attacks executed by new as well as legal nodes because it lacked hash chain renewability. In 2012, Lee et al. [7] proposed a practical access control scheme, still based on elliptic curve and hash chain. However, such a large number of key distribution schemes [2–7] are vulnerable to various adversary attacks and had huge storage overhead at the sensors node.
In 2013, Molavi et al. [8] use ECDLP method to solve security problem but still need time synchronization and had more compute time.
Our goal is to solve the problems mentioned above, and we propose a secure and flexible access control protocol. The idea of proposed scheme based on the chameleon hash function [9–12] and Diffie-Hellman key agreement. This proposed method can dynamically and securely add new nodes to the existing networks. Moreover, it overcomes the existing security problems and had a fewer number of transmissions and does not require time synchronization or the verification table.
The remainder of this paper is organized as follows. Section 2 describes the preliminary information relevant to our scheme, that is, the chameleon hash function based on the elliptic curve. In Section 3, the proposed scheme is introduced, followed by the correctness and performance analysis in Section 4. Finally, we draw our conclusions in Section 5.
2. Preliminaries
This section introduces the properties of chameleon hash functions based on elliptic curves [7, 8]. The base station initially chooses a large prime number q, an elliptic curve
The proposed chameleon hash function is as follows.
Given the hash key
According to [10], the chameleon hash function has the following properties.
Anyone that knows the public key If the private trapdoor key is not known, it is not possible to find two inputs ( The holder of the secret key information can easily find collisions for a given input, that is, two messages
Note that in signature schemes that use the chameleon hash function, there is a signer and a recipient, and two phases of execution. In the off-line phase, the signer precomputes the chameleon hash values
3. The Proposed Scheme
This section presents the proposed access control method based on the chameleon hash function [9–12] and used twice Diffie-Hellman key exchange. This study used signature parameter to archive robust authentication and key exchange. This method consists of two phases: the initialization phase and the node authentication and key establishment phase. The basic concepts and operations are as follows:
initialization phase: the base station sets the necessary values of the sensor nodes before they are deployed; node authentication and key establishment phase: a deployed node engages in mutual authentication with one of its neighboring nodes and then establishes a common session key with the neighboring node for secure communication.
In order to depict the proposed method more clearly, the notations used in this paper are listed in Notations Section.
3.1. Initialization Phase
To set up the network system parameters, the base station initially chooses a large prime number q, an elliptic curve
Step 1.
Choose random elements
Step 2.
Select random numbers
Step 3.
Compute a security key
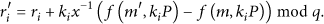
These three steps of the initialization phase are shown in Algorithm 1.
The node Preloads Choose secret key and chameleon hash value Generates Computes and
3.2. Authentication and Key Establishment Phase
After all the sensor nodes have been deployed, if node
Step 1.
Node
Step 2.
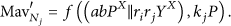
Node
Then,
If
Then,
Step 3.
When node
If
Step 4.
When
The steps of the authentication and the key establishment phase are shown in Algorithm 2.
The Node Generates Compute Compute Check CHBS ?= Compute
Note that after the sensor network has operated for a certain period of time, new nodes must be deployed in the network to extend its life. For example, for the deployment of a new node
4. Analysis of the Proposed Scheme
In this section, we analyze the correctness, the security, and the performance of the proposed access control protocol. The security analysis also shows how the proposed method can resist known security attacks.
4.1. Correctness
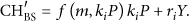
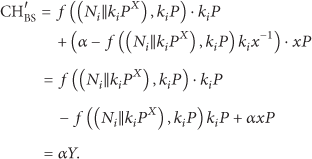
In the authentication and key establishment phase, node
Based on the received message (
If node
4.2. Security Analysis
The proposed scheme utilizes the chameleon hash function and twice Diffie-Hellman key exchange produces the mutual authentication value to establish mutual authentication between communication nodes. This study is constructed of security chameleon hash function, and further proof is in [10, 11]. For example, if nodes
After node
In addition to security analysis, the following paragraphs explain how the proposed method can resist attacks such as legal node masquerading attacks
(A) Legal Node Masquerading Attack. In this study, the authentication of node
First, the node to be authentication node
Secondly, only a legitimate node
An attacker may obtain the commutation values by eavesdropping on the communication between nodes
(B) Forgery Attack. Consider the case where an adversary has obtained the commutation values by eavesdropping on the communication channel.
The adversary may attempt to create a legitimate authentication message using the following equation:
However, it is not possible for the adversary to create a forged message because the value of
(C) New Node Masquerading Attack. When some of the sensor nodes in the wireless sensor network are damaged or have exhausted their power, new sensor nodes must be added to the network to extend its life. In the new node addition phase, the base station preloads the
(D) Replay Attack. A replay attack is the one in which an attacker captures the transmitted messages of a legitimate node and later replays them on the network in an attempt to imitate legitimate authentication messages. For example, if an attacker transmits the captured message (
In addition, if the attacker sends the value
(E) The Man-in-the-Middle Attack. In the proposed scheme, the communication nodes can mutually authenticate and establish session keys between users and servers. Although an attacker may launch a man-in-the-middle attack, the attacker can only know the values of
4.2.1. Session Key Security
The proposed scheme uses a session key. Only the communicating parties know the session key
4.3. Performance Analysis
Table 1 shows the proposed scheme compared with related works Huang [3], Kim and Lee [4], Zeng et al. [6], and Molavi et al. [8] in terms of the function of access control method. The computation cost and the transmission cost are two popular benchmarks for evaluation of the efficiency of the WSNs. Table 2 shows the computation costs of the proposed method during different phases. When compared to the computation cost of the hash chain and the elliptic curve-based schemes, the computation cost of the proposed method is slightly higher. However, our proposed method does not require time synchronization or the verification table for authentication. Hence, it is more efficient than the hash chain and elliptic curve-based methods.
Compared function of access control method.

The computation costs of the proposed method during different phases.

The energy cost of communication and cryptography in wireless sensor networks is an important consideration. In [13] indicated, the energy cost of cryptographic protocols, both from a communication energy cost and computation energy cost. According to [13] measure practical costs of computation and communication in WSN, it used TelosB sensors run Elliptic Curve Diffie-Hellman key exchange with authentication energy costs total is 130 (mJ), communication costs is 58.3 (mJ), and computation cost is 77 (mJ). As a result, we can realize that communication cost is an important consideration same as the computation cost. Table 3 presents the computation and the transmission costs incurred by using the methods put forward by Zhou et al. [2], Huang [3], Kim and Lee [4], and Lee et al. [7]. It also displays the costs incurred by using our proposed method. The protocol proposed by Huang requires seven transmissions and updates the broadcast hash chain after each authentication, key establishment, and new node addition phase. Our method requires only five transmissions. Consequently, it needs less bandwidth than the schemes proposed by Zhou et al. and Huang.
The comparison of computation costs and number of transmissions.

Therefore, the proposed scheme can be applied to applications from the WSNs criteria that had less number of transmissions and had lower data rate of communication. However, every broadcast has resulted in poor throughput of WSNs. Our proposed method does not need broadcast to update node list and verify table. Furthermore, it can be implemented by using any elliptic curve and cryptographic secure hash function.
5. Conclusion
This study demonstrated a new access control scheme for WSNs that has three characteristics. First, the proposed scheme can establish mutual authentication between two communication nodes and resist possible attacks when the base station adds a new node to the WSN. Second, the proposed scheme can establish a common session key between two nodes in an efficient manner. Moreover, it does not require time synchronization or the verification table. Third, the proposed scheme requires fewer transmissions and less bandwidth than existing schemes.
Footnotes
Notations
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This paper is the partial result of Project MOST103-2632-E-366-001. The authors would like to thank the support of the Ministry of Science and Technology, R.O.C.