Abstract
Well-designed wireless sensor networks (WSNs) usually provide vital support for collecting, processing, and forwarding the real-time information in mission-critical applications where medium access control (MAC) protocols determine the channel access control capabilities and the energy consumption properties of these networks. This paper models the MAC protocol of CSMA/CA using timed automata on the message communication and the energy harvesting and analyzes the protocol through model checking of the major CTL properties. The modeling and analysis of CSMA/CA protocol with the comparative experiments give some performance results and also reveal that timing error may cause deadlock, and the accessibility is satisfied if no deadlock exists.
1. Introduction
Wireless sensor networks (WSNs) are multihop self-organizing networks consisting of sensor nodes through wireless communication and usually provide vital support for collecting, processing, and forwarding the real-time information in mission-critical applications, but the networks face many challenges for the limit energy, memory, and computing power in the sensor nodes [1]. One of these challenges is to design the effective medium access control (MAC) protocols, which determine the channel access control capabilities and the energy consumption properties of WSNs [2]. The MAC protocol of CSMA/CA (Carrier Sense Multiple Access with Collision Avoidance) for carrier transmission in WSNs avoids collisions by transmitting only when checking to be sure the channel is idle [3].
Bertocco et al. [4] analyzed the performance of CSMA/CA-based sensor networks for industrial monitoring using the experimental tests on a test bed, which consisted of a wireless sensor network, one personal computer, and a digital oscilloscope. Zhu et al. [5] presented a slotted CSMA/CA scheme MultiCSMA for WSNs and simulated the proposed scheme to validate the performance improvement using the NS2 network simulator. Youn et al. [6] presented a QoS mechanism supporting CSMA/CA for WSNs and theoretically analyzed the proposed method. Chen et al. [7] presented an analytical model for evaluating the CSMA/CA protocol and used NS2 to evaluate the protocol performance in the small-scale application of WSNs. The above-mentioned researches have many interesting discoveries on the CSMA/CA protocol, but we still need to be sure that all explicitly stated properties are satisfied in WSNs.
To more accurately verify the CSMA/CA protocol in energy-harvesting WSNs [8], this paper models CSMA/CA using timed automata and analyzes the protocol using the UPPAAL model checker [9]. The rest of the paper is organized into four sections. Section 2 briefly introduces related work on energy harvesting for WSNs. Section 3 proposes the timed automata models of the CSMA/CA protocol in energy-harvesting WSNs. Section 4 gives the results of UPPAAL model checking and the TinyOS-based comparative experiments. Finally, the conclusions are presented in Section 5.
2. Energy Harvesting for Wireless Sensor Networks
Sensor nodes with limited energy usually prevent WSNs used in many different application areas and may use energy-harvesting technologies to make WSNs perform their functions in long lifetimes [8]. Energy harvesting is a process of obtaining energy from renewable environmental resources such as solar, wind, heat, and vibration. In energy-harvesting WSNs, each sensor node is equipped with one or more collectors to harvest energy from the environment [10]. For example, when using the solar panels as an energy collector, each node can continuously gain energy during the day, which can effectively prolong the network lifetime [11, 12]. In only battery-powered WSNs, the energy of one sensor node gradually decreases over time, while the energy of one sensor node in energy-harvesting WSNs has sustainable power supply in a certain period of time until the node stops or fails.
The MAC protocols for energy-harvesting WSNs may be different from conventional battery-powered WSNs and need some different design criteria, such as environmental adaptability, backlog estimation, and frame length selection [13, 14]. CSMA/CA requires a delay in network activity after each transmission, which is proportionate to the priority level of each device. CSMA/CA may improve access control and serve to reduce collisions in carrier transmission of energy-harvesting WSNs.
3. Modeling CSMA/CA Using Timed Automata
We model CSMA/CA for energy-harvesting WSNs using time automata, which are finite state automata with clock constraints, can be seen as the abstract models of the real-time systems, and are widely used in verifying the correctness of the real-time systems [15].
3.1. Message Communication
In energy-harvesting WSNs using CSMA/CA, one sensor node senses the information and transmits it to the sink node via multihop, during which the listen and sleep mechanism reduces the probability of packet collisions [3]. We set up a set of cursors
The timed automata model of message sending is shown in Figure 1. In the model, the initial sleep state is

Timed automata model of message sending
Figure 2 shows the timed automata model of message receiving. In the model,

Timed automata model of message receiving
As shown in Figure 3,

Time automata model of
3.2. Energy Harvesting
In energy-harvesting WSNs, the sensor nodes may have five states, including

State transformations of energy harvesting.
The energy-harvesting WSNs obtain energy from the environment; so when modeling the energy harvesting of the sensor nodes, we need to consider the energy-harvesting rates, which are not uniformly changing as they may be affected by the changes of environmental factors and human interventions, such as the light intensity, the local climate conditions, and the buildings and trees in the shade. In the CSMA/CA using energy harvesting, we focus upon the charging process in energy harvesting and give the timed automata model of energy acquisition

Time automata model of energy acquisition
In Figure 5, the initial state of one node is
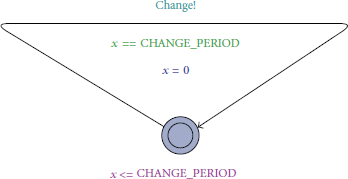
Time automata model of periodically harvesting energy.
4. Analyzing CSMA/CA Using UPPAAL
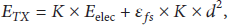
We analyze the CSMA/CA protocol in energy-harvesting WSNs using the UPPAAL model checker [9] about the CTL properties such as no deadlock, reachability, and performance factors. The performance is also comparatively evaluated through experiments on TOSSIM simulator [16], which simulates the state-of-the-art TinyOS-based CSMA/CA real applications [13, 14, 17, 18] with the SolarCastalia energy-harvesting model [19]. In the following UPPAAL model checking and experiments, the amount of energy harvested
Parameters used in analyzing CSMA/CA.
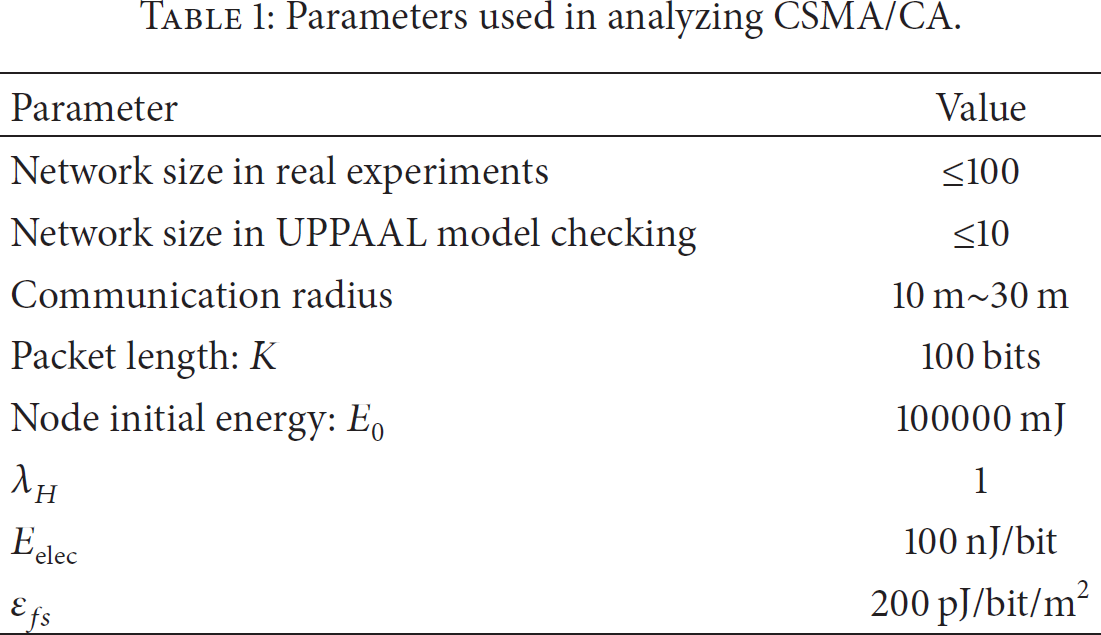
where
4.1. No Deadlock
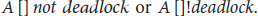
Deadlock refers to blocking between processes. In UPPAAL, the property can be specified by the CTL formula as
In the energy-harvesting WSNs, we verify the property of CSMA/CA with different timing strategies, which decide the parameter values of
4.2. Reachability
Reachability refers to the fact that if there are sensor nodes sending message, the nodes receiving the message must exist. In UPPAAL, the property can be specified by the CTL formula as

The UPPAAL and experimental results of our proposed models show that these models satisfy the reachability if no deadlock exists.
4.3. Collision Probability over Time
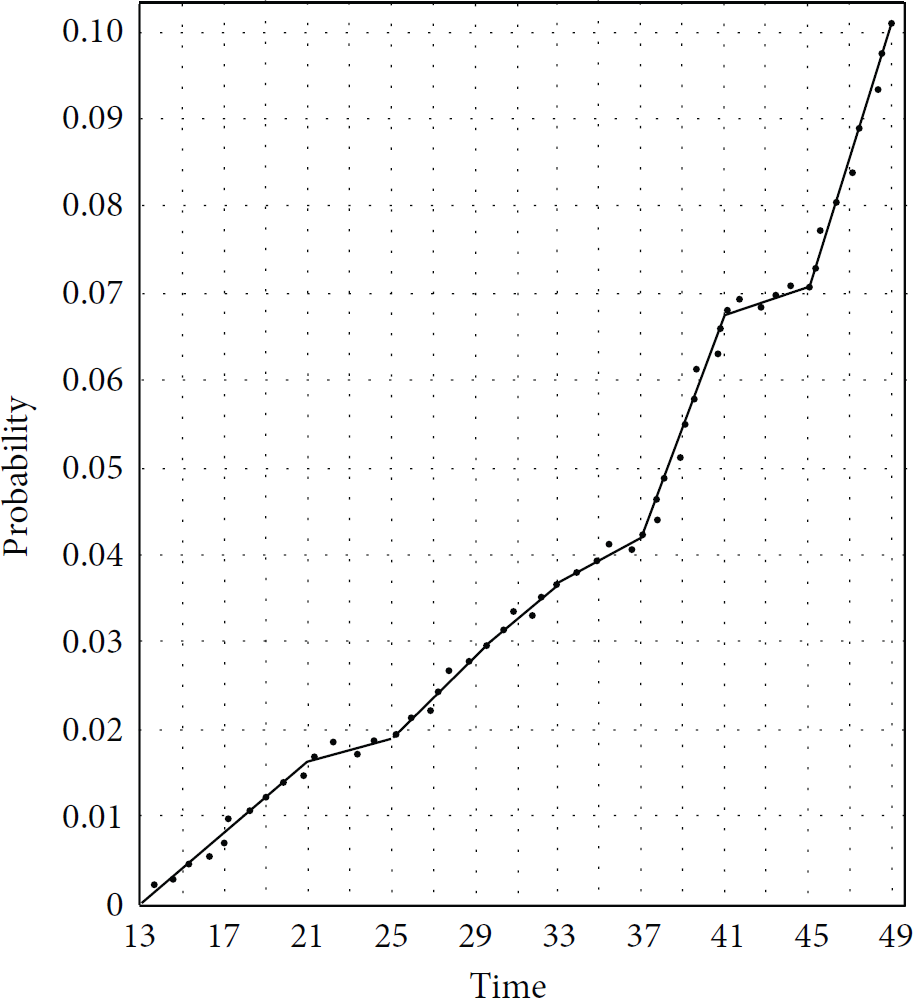
The property of collision probability over time can be specified in UPPAAL by the CTL formula as
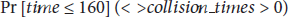
After 738 times, the confidence value is 0.95 when the probability is in 0.0713, 0.1705. In Figures 7 and 8, the line charts of UPPAAL results show two cases of the collision probability versus time in two different backoff times represented by
Case 1 of collision probability versus time.
Case 2 of collision probability versus time.
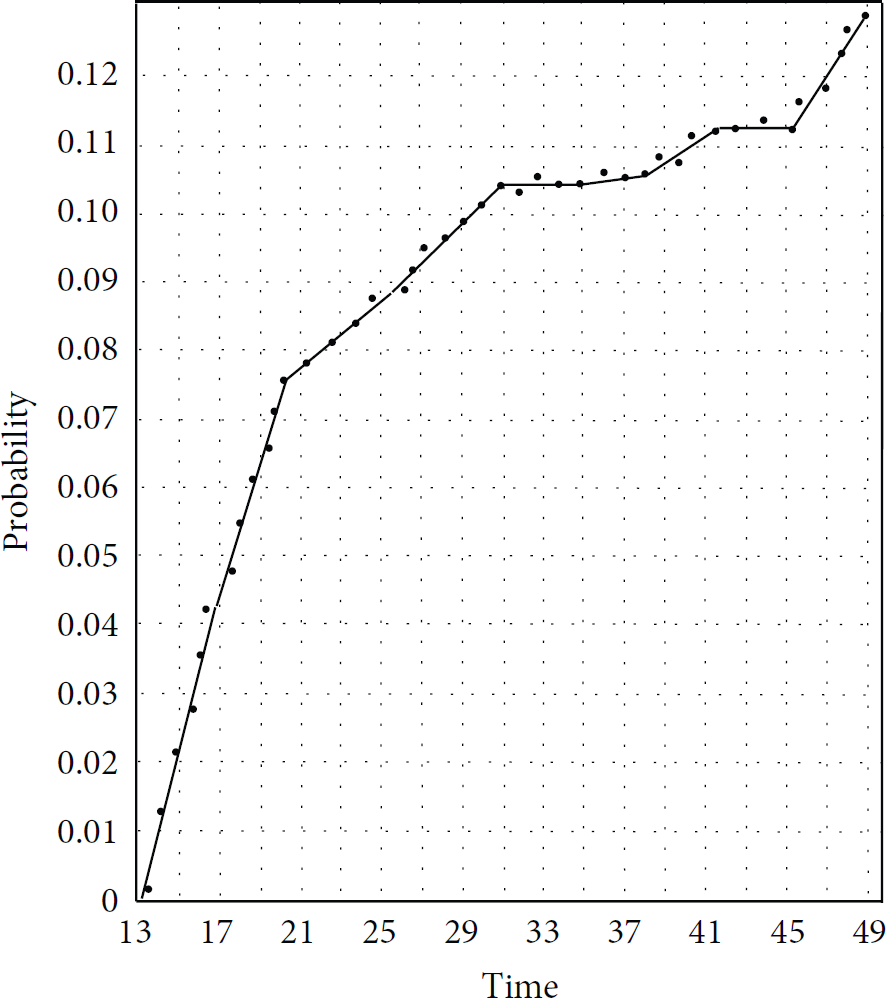
4.4. Probability of Collision Times
The property of the probability of collision times can be specified in UPPAAL by the CTL formula as

After 738 times, the confidence value is 0.95 when the probability is in 0.95, 1. In Figure 9, the line chart of UPPAAL results shows one case of the probability distribution of different collision times and indicates that the probability is growing over collision times and the probability of having one collision at least is less than 96%, which are also verified by the scattered plots of the experimental results.
One case of the probability of collision times.
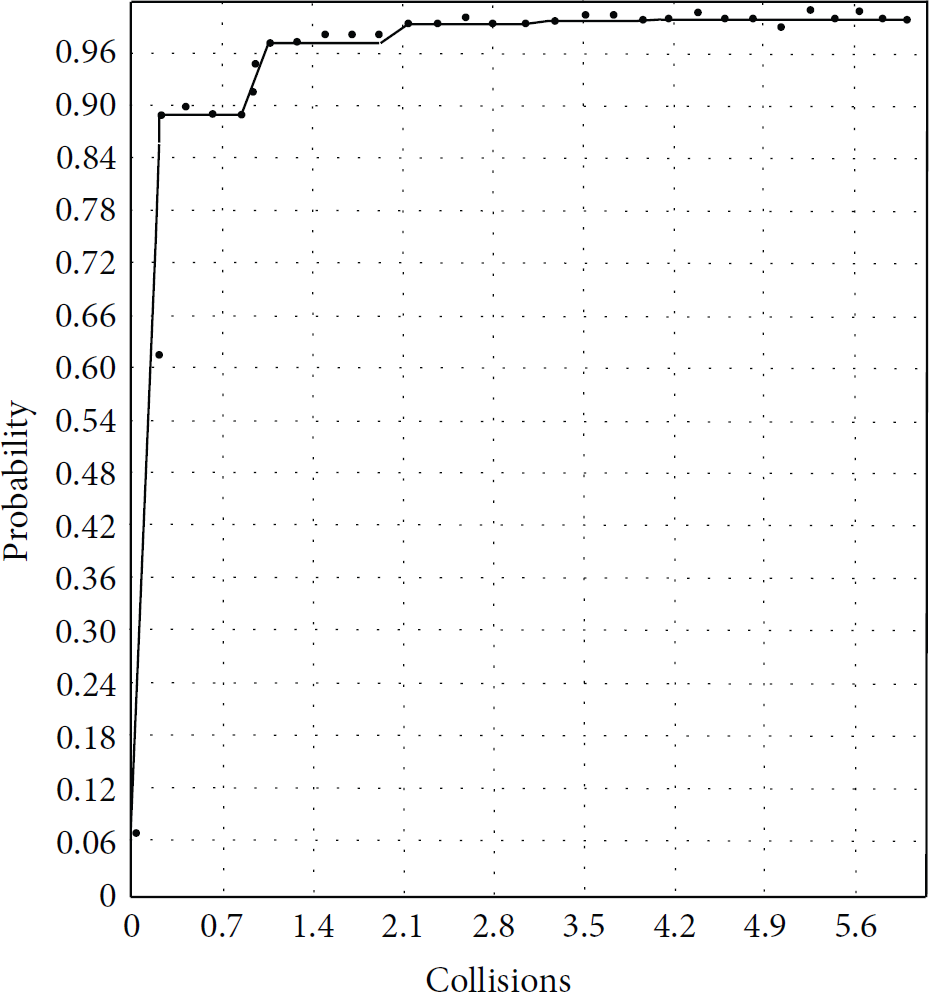
4.5. Probability of Energy Consumption
The property of the probability of energy consumption can be specified in UPPAAL by the CTL formula as

The property shows the probability of the power is smaller than 50000 and time is longer than 1000 s. In Figures 10 and 11, the line charts of UPPAAL results show two cases of the probability distribution of energy consumption in two different backoff times represented by

Case 1 of probability distribution of energy consumption.

Case 2 of probability distribution of energy consumption.
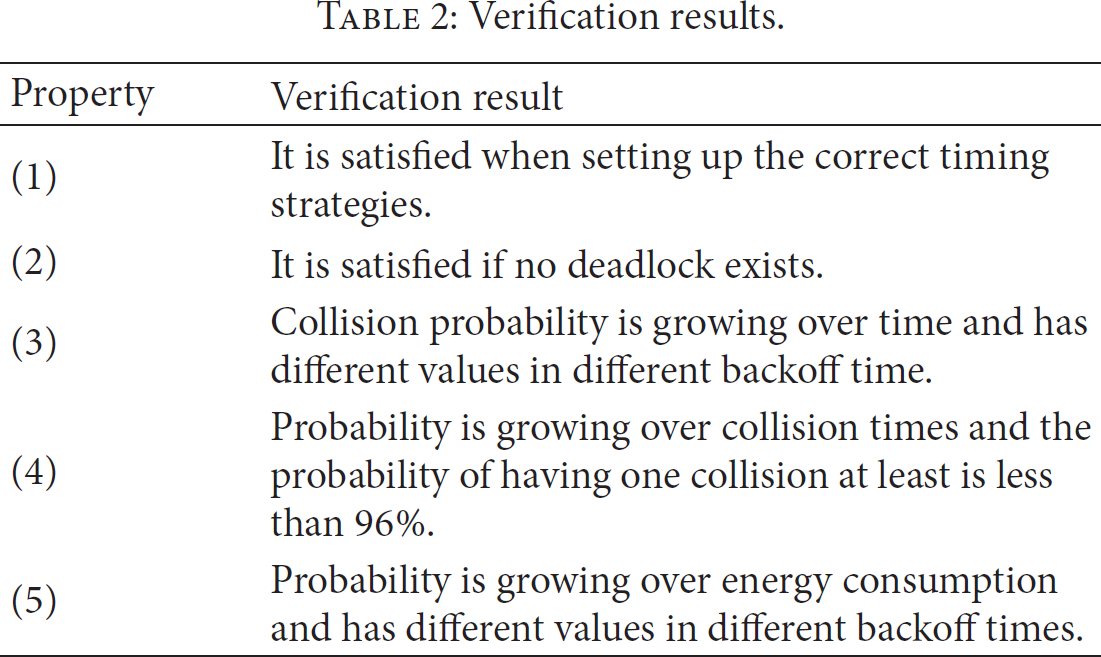
According to the verification results shown in Table 2, we may get the reasonable retreat backoff time through continual adjustments, which cannot only reduce the probability of collision but also reduce energy consumption.
Verification results.
5. Conclusions
The CSMA/CA protocol in energy-harvesting WSNs determines the distribution of channel and communication resources and constructs the underlying network structure which has a great influence upon the network performance. We propose the timed automata models of message sending, message receiving, and energy acquisition in CSMA/CA of energy-harvesting WSNs. The results of analyzing the protocol through UPPAAL model checking reveal some performance trends and show that timing error may cause deadlock, and the accessibility is satisfied if no deadlock exists. In the future work, we will verify and analyze other aspects of the CSMA/CA protocol, such as the collision processes, and help researchers to model, automatically verify, and evaluate the performance more comprehensively.
Footnotes
Conflict of Interests
The authors declare no conflict of interests.
Acknowledgments
The authors would like to thank the reviewers for the valuable comments and suggestions, which have helped to improve the paper. This work was supported by the National Natural Science Foundation of China (Grant nos. 61501253, 60905040, and 61300239), the Basic Research Program of Jiangsu Province (Natural Science Foundation) (Grant nos. BK20131382, BK20151506), the 11th Six Talent Peaks Program of Jiangsu Province (Grant no. XXRJ-009), China Postdoctoral Science Foundation (Grant no. 2013M531393), Jiangsu Planned Projects for Postdoctoral Research Funds (Grant no. 1102102C), and Jiangsu Government Scholarship for Overseas Studies (Grant no. JS-2013-209).