Abstract
This paper investigates the optimal jamming attack scheduling in Networked Sensing and Control Systems (NSCS). From viewpoint of the attacker, we formulate an optimization problem which maximizes the Linear Quadratic Gaussian (LQG) control cost with attacking energy constraint in a finite time horizon. For two special cases, we obtain that the optimal jamming attack schedule is to consecutively attack in the given time horizon. For the general case, we propose an algorithm to find the optimal schedules. Finally, we study the effectiveness of our proposed attack strategies on our established semiphysical testbed.
1. Introduction
Networked Sensing and Control Systems (NSCS) are control systems wherein physical elements, that is, plants, sensors, controllers, and actuators, are connected via wireless communication networks. NSCS have a wide range of applications in factory automation, unmanned aerial vehicles, remote surgery, intelligent transportation, smart grid, smart building, and so forth [1–5]. The essential characteristic of NSCS is that the physical elements and cyberspace are tightly integrated to carry out various jobs [6–8]. However, NSCS are vulnerable to an increasing number of malicious cyber attacks [9]. For example, an Iranian nuclear facility was attacked by “stuxnet” in 2010 and cannot operate normally in a long time since more than 60% of centrifugal control systems were destroyed [10].
In the past few years, several literatures have been focused on evaluating the effect of cyber attacks, for example, Denial-of-Service (DoS) attacks [11, 12], replay attacks [13, 14], and false data injection attacks [15, 16], on NSCS. Among these attacks, DoS attack is the most accomplishable one and can result in serious consequences [11]. Thus, it has been widely studied recently. In order to block the communication between system elements, DoS attacker can interfere with the radio frequencies on the communication channels [17]. In fact, jamming is a typical mode of DoS attack [18].
LQG control cost, which is used to synthetically consider the cost of system states and control, is an important performance in NSCS. Some researches have put emphasis on the security of LQG control under jamming attack [11, 19, 20]. Amin et al. study the optimal controller which minimize the LQG cost with safety and energy constraints when a jamming attacker takes identical independent distributed jamming actions [11]. They present semidefinite programming to solve this problem. Gupta et al. design an optimal controller to defense the intelligent jamming attack with limited actions [19]. Shisheh Foroush and Martinez propose an event-trigger control law which can prevent the periodic jamming attack with energy constraint [20]. The commonality of these works is that they all focus on the design of defense strategies under given attack patterns. However, our work stands in the viewpoint of attacker and finds the optimal attack schedules to maximize the control performance. This is of equal importance as one can provide effective defensive policies only when he grasps the attack strategies.
The goal of this paper is to design an optimal offline jamming schedule, which can maximize the attack effect on the NSCS. Specifically, in our scenario, one sensor observes the states of plant and sends the measurements to a remote estimator via a wireless channel. The attacker has a limited energy budget in the given finite time horizon. He has to decide whether or not to jam the channel from sensor to estimator at each time. The main contributions of this paper which distinguish it from the related literatures are summarized as follows:
We formulate a jamming attack scheduling problem and look for the optimal jamming schedule that maximizes the LQG cost with energy constraint in a given finite time horizon. We present the close form of the optimal jamming schedule for two special cases and provide an algorithm to search the optimal schedules for the general case. We study the effectiveness of proposed jamming schedules on the established semiphysical testbed.
The remainder of the paper is organized as follows. In Section 2, we formulate the problem. In Section 3, we study the system performance under given attack schedule. In Section 4, we present the optimal jamming attack schedules for special cases and provide an algorithm to search the optimal attack schedules for the general case. In Section 5, we demonstrate the effectiveness of proposed optimal jamming schedules on the semiphysical testbed. Finally, Section 6 concludes the paper.
Notations.
2. Problem Formulation
2.1. System Architecture
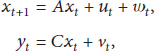
Consider the following linear time-invariant system (Figure 1):

System architecture.
In our scenario, the sensor observes the plant and gets the measurements
Let
Denote
Let
Similar to [21], we have
In order to minimize the LQG cost function
2.2. Attack Model
In our scenario, there is an attacker who wishes to deteriorate the control performance by jamming the sensor-to-estimator wireless channel. It is assumed that the attacker has a limited energy budget; that is, he can attack n times at most in the time horizon
Specifically, from the viewpoint of attacker, he aims to maximize the cost function with energy constraint which is as follows.
Problem 1.
Consider
3. Preliminaries
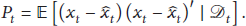
In this section, we present some properties of the estimate at the estimator side and the control performance of plant under a jamming attack.
3.1. State Estimation under Jamming Attack
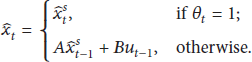
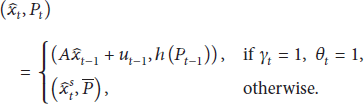
From standard Kalman filter, the estimate and corresponding error covariance at the sensor side can be calculated as follows:
Define functions
From [23], the following result holds.
Lemma 2.
The function h has the following property:
From [22], we can obtain the estimate
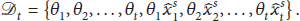
Define attack sequence
Similar to [18, 22], one can get the following result.
Lemma 3.
Let
From Lemma 3, we can see that grouping together as much as possible can lead to maximal average error covariance.
3.2. Control Performance under Jamming Attack
In order to find the optimal offline jamming attack scheduling, we have to study the control performance when the attack schedule is given.
According to [5, 24], one can obtain the following result.
Lemma 4.
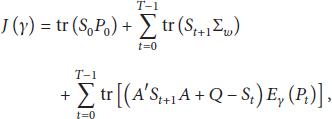
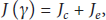
The LQG control cost function under a given attack schedule γ can be calculated as follows:
In fact, (15) converges quickly to a steady state. Thus, if
It can be seen that
Problem 5.
Consider
4. Optimal Jamming Attack Schedules
In this section, we firstly study the jamming schedules against LQG control for two special cases and present the close form of optimal schedules. Then we investigate the attack strategies for the general case.
4.1. Case I:
When
From Lemma 4, we can obtain the following conclusion.
Theorem 6.
If
According to Theorem 6, we can see that the attacker only needs to maximize
Problem 7.
Consider
From [18, 22], Problem 7 can be easily solved by the following theorem.
Theorem 8.
When
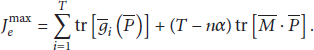
4.2. Case II:
Define
Lemma 9.
The function
According to Section 3.2, the objective of Problem 1 is equivalent to
From Lemma 9 and Theorem 3.1 in [22], we can solve this problem by the following theorem.
Theorem 10.
When
4.3. General Case Study
For the general case, it is difficult to obtain a close form of optimal attack schedule. Attacker can find the optimal jamming schedule by exhaustion method which is given in Algorithm 1. Since this schedule can be computed before the attack action begins, the computation of our proposed algorithm will not cost too much.
(1) Process begins; (2) Input: (3) (4) Compute LQG cost (14) under attack schedule γ, that is (5) (6) (7) (8) (9) Output: optimal attack schedule
5. Simulation
5.1. Testbed
There are three types testbeds for simulation of NSCS security, that is, software simulation testbeds, physical simulation testbeds, and semiphysical simulation testbeds. The software simulation testbeds cannot fully simulate the real environment. The physical simulation testbeds can employ the same experimental equipment with the real world to construct the security test platform. However, they need long cycle of construction and great cost. Fortunately, semiphysical simulation testbeds are the good choice for NSCS security since they can simulate the real working environment and save the cost. Thus, we choose a semiphysical simulation testbed to study the effectiveness of our proposed attack strategy.
Our semiphysical simulation testbed is composed of virtual plant, physical controller, and communication network. Figure 2 shows the system architecture. In our testbed, real-time system states of the virtual plant are sent to the PLC through a wireless network. After reading the system states, the controller calculates the control data and writes them back to the PLC. Then the control data are sent back to the virtual plant via a wired channel.

The structure of semiphysical testbed.
We build an inverted pendulum control system for experiments, which is based on the system presented in [5]. The parameters are given as follows:
We employ USRP N210 to simulate jamming attack on the wireless channel from sensor to controller. USRP is a universal software radio peripheral that can send and receive radio signal. We use the software GNU Radio in Ubuntu to manipulate the USRP. The frequency spectrum analyzer is adopted to detect the central frequency and waveform of transmission signals. Then we adapt the parameters on GNU Radio to configure the USRP. Experimental parameters are set as follows: center frequency is 433 MHz; waveform is saw tooth; jamming power is 16 dB and jamming signal frequency is 10k; bandwidth is 20 MHz.
We verify the proposed optimal offline attack strategies through experiments based on the semiphysical testbed. We set
5.2. Simulation Results Analysis
We study the effectiveness of jamming attack with 10 different schedules when
Attack schedules in our experiment.

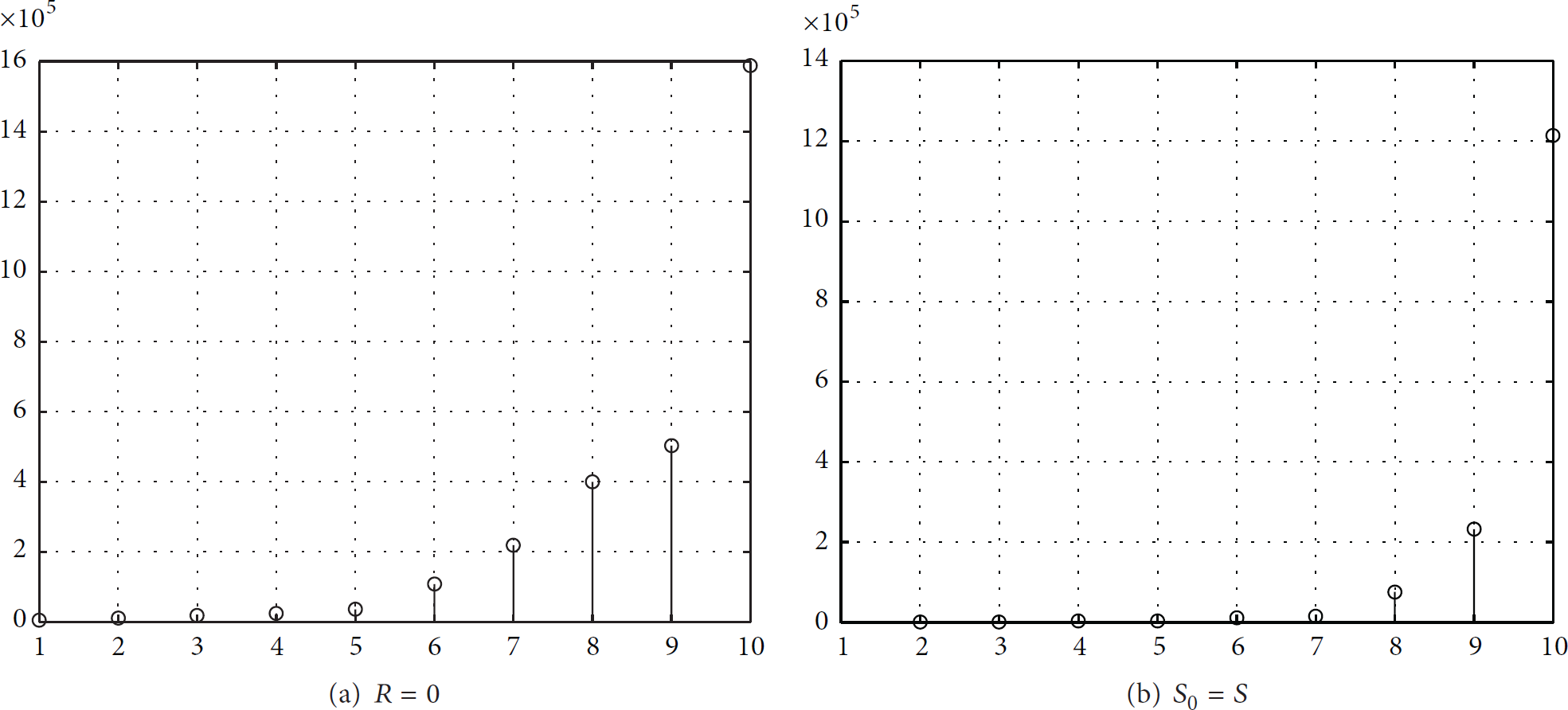
Compare the cost J under different attack strategies. The lateral axis is the mark number of attack strategy. Attack strategy 10 is the consecutive attack strategy.
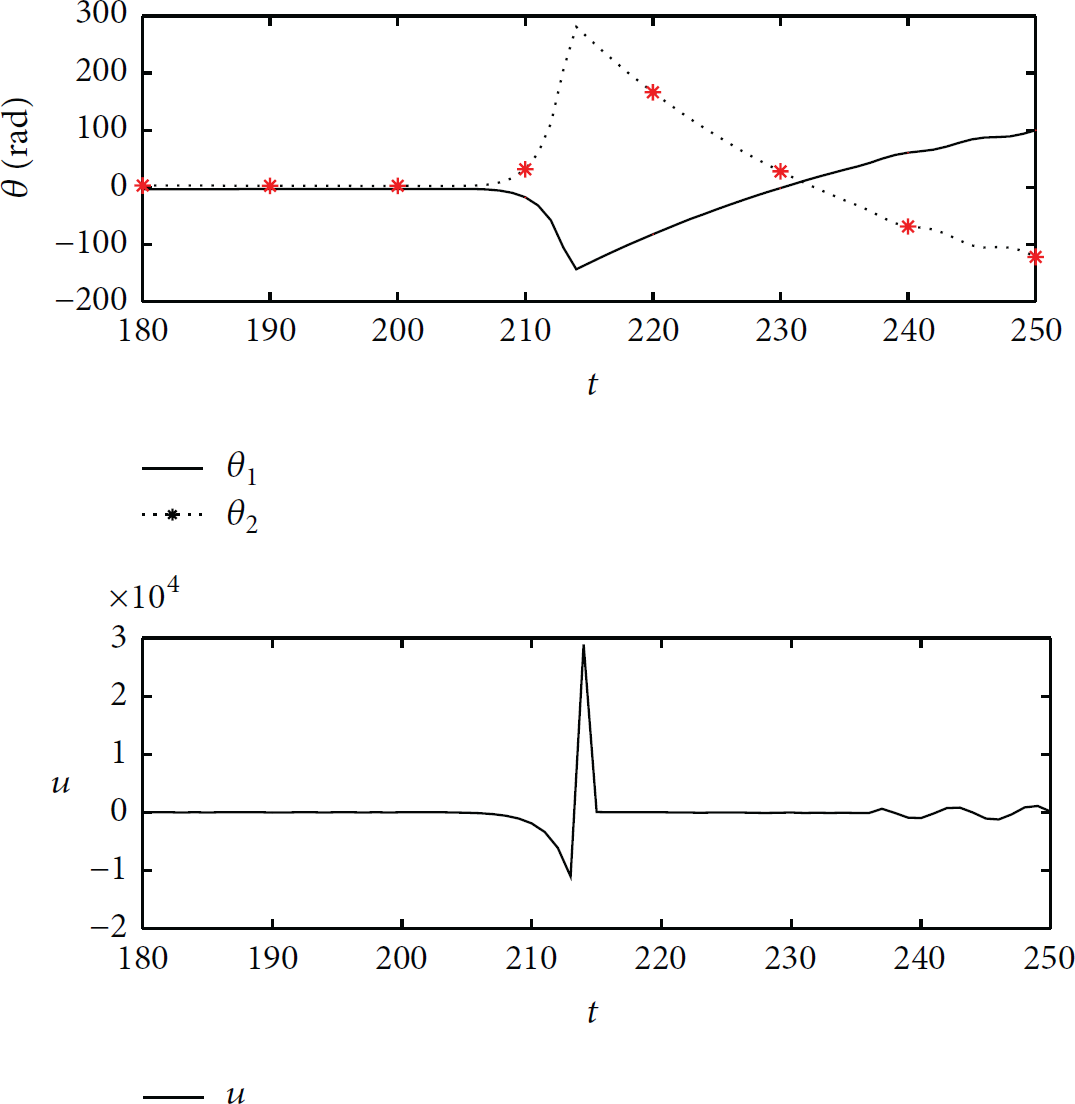
The variation of system states and control data under attack schedule 10 (optimal attack) when
6. Conclusion
In this paper, we considered the optimal jamming attack scheduling which can destroy the system control performance. We formulated an optimization problem that maximizes the LQG cost subject to attacker's energy constraint in a given finite time horizon. Optimal attack schedule has been presented for two special cases. For the general case, we provided an algorithm to find the optimal attack schedule. We also established a semiphysical testbed and studied the effectiveness of proposed attack schedules by simulation. In the future, we will study the evaluation of control performance when the NSCS is under other types of cyber attack, for example, data injection attack and replay attack. We will also design effective defense strategies to avoid the cyber attacks in NSCS.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
The work was partially supported by Professional Development Program for Visiting Scholars in Colleges and Universities under Grant FX2014144 and Zhejiang Provincial Natural Science Foundation of China under Grant Y16F030011. The work by H. Zhang was supported by NSFC under Grants 61203036, 61503147, and 71401060, the University Science Research General Project of Jiangsu Province under Grant 15KJB510002, Huaihai Institute of Technology Doctoral Research Funding under Grant KQ15007, and Lianyungang Science and Technology Projects under Grants CK1331 and CN1321.