Abstract
Applying an Intrusion Detection System (IDS) to Wireless Body Area Networks (WBANs) becomes a costly task for body sensors due to their limited resources. To solve this problem, a cloud-assisted IDS framework is proposed. We adopt a new distributed-centralized mode, where IDS agents residing in body sensors will be triggered to launch. All IDS agents are only responsible for reporting the monitored events, not intrusion decision that is processed in the cloud platform. We then employ the signaling game to construct an IDS Report Game (IDSRG) depicting interactions between a body sensor and its opponent. The pure- and mixed-strategy Bayesian Nash Equilibriums (BNEs) of the stage IDSRG are achieved, respectively. As two players interact continually, we develop the stage IDSRG into a dynamic multistage game in which the belief can be updated dynamically. Upon the current belief, the Perfect Bayesian Equilibrium (PBE) of the dynamic multistage IDSRG is attained, which helps the IDS-sensor select the optimal report strategy. We afterward design a PBE-based algorithm to make the IDS-sensor decide when to report the monitored events. Experiments show the effectiveness of the dynamic multistage IDSRG in predicting the type and optimal strategy of a malicious body sensor.
1. Introduction
Recently, a specific class of Wireless Sensor Networks, known as Wireless Body Sensor Networks (WBSNs) or Wireless Body Area Networks (WBANs), has been developed as physiological sensors and low power integrated circuits are rapidly evolving. A WBAN is generally composed of some miniaturized and intelligent sensors attached on or implanted in the body, which are able to establish wireless communication links. Such networks have attracted considerable attention since they are capable of allowing for many human-central applications such as health monitoring, sports training, interactive gaming, and personal information sharing [1–5]. However, applying WBANs has to face many issues and challenges due to limited resources of body sensors [6]. One challenge in a common healthcare scenario is how to process, store, and manage the huge amount of data gathered by body sensors. Another challenge is how to meet the strict security requirement of WBANs applications [7, 8]. The openness of the wireless media of WBANs makes a malicious attacker easy to launch various attacks. Moreover, data collected by body sensors are health related and highly sensitive. Security threats may result in a patient in a hazardous situation and even death in the case of medical applications of WBANs. Therefore, Intrusion Detection System (IDS) is required to prevent body sensors from malicious actions. However, employing IDS is a costly task for body sensors due to their limited computation capability and storage capability. Moreover, these body sensors usually hold limited power while approaches to realizing IDS are computationally expensive in general. To solve these problems, cloud computing can be seen as a good remedy.
As infrastructure, cloud computing provides various services in fields of computation, storage, data access, security, and software [9, 10]. This computing model is therefore expected to play a significant role to make up for the deficiencies of body sensors. Combining WBANs with cloud computing will provide an integrated platform that realizes combination of different WBANs, scalability of data storage, and scalability of power for processing various data analyses [11]. The concept of Software as a Service, especially Security as a Service (SECaaS) [12] that represents the provision of security applications and services via the cloud platform to the customers' systems, changes the method of protecting body sensors. Through such a cloud-assisted IDS, we are able to detect misbehavior in WBANs and send back the response commands that isolate malicious body sensors. As a result, computation cost is no longer a critical factor influencing the effectiveness of security for body sensors, since security analyses and decisions are performed in the cloud platform.
Different decisions are then emerging along with the application of a cloud-assisted IDS to body sensors. Generally, IDS agents should be initially deployed in body sensors that are referred to as IDS-sensors. After these IDS-sensors have collected other body sensors' events, a problem exists in optimizing their strategies to decide whether to report events involving malicious or normal behavior. Obviously, this problem is caused by limited resources of body sensors. On the one hand, if an IDS-sensor makes a choice not to report any events, it conserves its power and bandwidth, but no malicious body sensors will be captured. However, if an IDS-sensor reports each event it detects, the probability of capturing malicious body sensors will be increased, but the IDS-sensor will run out of its power much faster. To solve this dilemma, we are motivated to employ game theory to seek the optimal strategies.
By supplying a rich set of mathematical tools for exploring the strategic decision-making, game theory has been widely employed in different fields [13–21]. These typical applications exist in optimizing the strategy of launching IDS [22], seeking autonomously stable adaptation decisions [23], minimizing power resource allocation for interference mitigation [24], optimizing service deployment in cloud computing [25], and predicting malicious behavior of attackers [26]. Among various game types, the signaling game is profitable to depict interactions between a body sensor and its corresponding IDS-sensor. In a signaling game, one player called Sender has private information about its type set while the other called Receiver is public in its type set. Thus, we can relate a body sensor, which attempts to send messages, to Sender since it may be normal or malicious so that its type is unknown to IDS-sensors. On the other hand, the corresponding IDS-sensor is related to Receiver as it only has one type.
Our interest is then to seek the optimal report strategies for body sensors using a cloud-assisted IDS to save their limited power. We deploy IDS agents to each of the body sensors. However, only those body sensors that are chosen as relays will be triggered to launch. Their responsibility is whether to report monitored events and is not to perform intrusion decisions that are analyzed and processed in the cloud platform for utilizing its powerful capabilities of computation and storage. Thus, we address the issue that a body sensor is too limited in its resources to execute the intrusion detection task that is computationally expensive in general. Using the signaling game, we address the other issue: when should an IDS-sensor report the monitored events? We reflect economic interactions between a body sensor and its corresponding IDS-sensor by constructing an IDS Report Game (IDSRG). We gradually explore the pure- and mixed-strategy BNEs (Bayesian Nash Equilibriums) of the stage IDSRG. As two players play the game continually, we develop the stage IDSRG into a dynamic multistage IDSRG and attain the mixed-strategy PBE (Perfect Bayesian Equilibrium) of the dynamic game. Upon the advantage of PBE, we design an algorithm to guide the IDS-sensor with the optimal report strategy. In this manner, the IDS-sensor is able to prolong its battery life while reporting an acceptable amount of monitored events.
Our contributions are summarized as follows:
We propose a cloud-assisted IDS framework for WBANs, in which intrusion analyses and decisions are performed in the cloud platform. Thus, a body sensor is no longer concerned about its limited computation for realizing its security. We construct the IDSRG based on the signaling game, which satisfies the actual environment where an IDS-sensor does not know the type of its opponent and is able to properly depict economic interactions between an IDS-sensor and its opponent. We attain equilibrium theorems of the stage IDSRG as well as the dynamic multistage IDSRG, which disclose the rational behavior of the IDS-sensor and its opponent. We design a report algorithm based on PBE, which provides an IDS-sensor with the optimal strategy to decide whether to take the action Report or not. In other words, an IDS-sensor does not always report monitored events, and thus its energy is saved.
The rest of this paper is organized as follows. In Section 2, we overview related works and highlight our particular aspects. In Section 3, we illustrate our network model and construct the stage and dynamic multistage IDSRG. In Section 4, we present a cloud-assisted IDS framework for WBANs and design a report algorithm based on PBE. In Section 5, we perform experiments to show the characteristics of the dynamic multistage IDSRG. Finally, conclusions are provided in Section 6.
Notations used in this paper are mainly listed in the Notations.
2. Related Work
Integration of cloud computing and WBANs is particularly attractive as it is able to expand the computation paradigm of WBANs. This infrastructure overcomes several shortfalls of WBANs like the storage capacity of data collected by body sensors and the ability to process these data. In spite of the above benefits, their emerging influences could be hindered by various security threats. Body sensors are susceptible to attacks, including node capturing and compromising. Patient's privacy may be lost in the cloud platform or may not be correctly supervised. For solving these issues, a protocol to attain storage and computation security in cloud computing is proposed in [27]. Zhang et al. [28] presented a key agreement scheme that provides neighboring body sensors with a common key generated by electrocardiogram signals, in order to preserve the integrity and privacy of medical data. The authors in [29] proposed a combined framework for reliable and secure data transmission in WBANs. In addition, the method of establishing trust among body sensors has been regarded as efficient implement to improve the security and performance of WBANs, in which trust evaluation [30] and trust management [31] always should be performed.
Different from the above prevention-based mechanisms to guarantee network security, an IDS, as the second line of defense, is regarded as a detection-based approach that is a necessary tool for realizing security of networks [32]. Typical techniques such as the swarm based rough set [33], Kalman filter [34], support vector machine [35], and unsupervised anomaly detection [36] are applied to IDSs in different networks. Since malicious body sensors usually disrupt the normal operation of WBANs and waste limited resources of normal body sensors, an IDS is required for WBANs to detect malicious body sensors that have broken down the prevention-based mechanisms. Using the IDS, WBANs will be capable of reacting with and isolating intruders to ensure body sensors' normal operation. However, there only exist a few studies of intrusion detection towards WBANs although many intrusion detection studies [37, 38] have been done for Wireless Sensor Networks. In [39], the authors gave a security framework of WBANs for monitoring ambulatory health status. They then proposed an IDS, which is inspired by the biological immune system using the negative selection algorithm, to maintain performance of WBANs in the presence of malicious body sensors. Wu et al. [40] proposed an intrusion-tolerant scheme for WBANs, which is able to dynamically detect intrusions and provide an adaptive strategy with passive replication via the combination of threshold-based intrusion detection and replicas classification. Unfortunately, these works [39, 40] do not consider the computation cost incurred by launching IDS agents. The emergence of cloud computing allows us to tackle this burden by applying its powerful computing ability. Through IDS services, IDS-sensors can transfer the cost of analyzing and processing suspicious data into the cloud platform. Thus, the rest of the problem of IDS-sensors is whether or not to report the monitored events.
Up to now, several works have been concerned about the utilities of employing an IDS via game theory. In [41], Otrok et al. proposed a cooperative game model for catching a misbehaving cluster head through checkers, which can analyze interactions among checkers to decrease the false positive rate. Moreover, a noncooperative zero-sum game between the cluster head and malicious node is formulated to maximize the probability of detection for an elected head. They [42] also conducted a noncooperative game between the intruders and IDS to guide the IDS to select an optimal sampling strategy in order to effectively reduce the success chances of intruders. Zhu et al. [43] combined game-theoretic modeling and trust management to design an intrusion detection network. With a noncooperative N-person continuous-kernel game model, each IDS seeks reciprocal incentive-based optimal resource allocation to maximize the aggregated satisfaction levels of its neighbors. Huang et al. [44] proposed a new IDS called Markovian IDS, which is able to select the optimal defense strategy of misuse detection with noncooperative game theory and to determine the weakest nodes representing potential security risks via a Markov decision process. Zonouz et al. [45] proposed a response and recovery engine based on a two-player Stackelberg stochastic game, which applies attack-response trees to analyze undesired system-level security events and to choose optimal response actions by solving a partially observable competitive Markov decision process. Shamshirband et al. [46] introduced a method called cooperative game-based fuzzy Q-learning to implement cooperative defense counterattack scenarios for the sink node and the base station. Using the signaling game, Shen et al. [22] constructed an intrusion detection game, which is able to depict interactions between the sensor node and IDS agent. The PBE attained is applied to obtain the optimal strategy determining when to launch the IDS agent. Thus, the IDS agent is not always in work and the sensor's power required to detect malicious behavior is saved. They [47] also obtain optimal strategies to save IDS agents' power, through Quantal Response Equilibrium (QRE) that is more realistic than Nash Equilibrium. In addition, Liu et al. [48] investigated the security and dependability mechanism when service providers are facing service attacks of software and hardware and proposed a stochastic evolutionary coalition game (SECG) framework for secure and reliable defenses in Sensor-Cloud.
Our work is distinguished in some aspects compared to the related works above. We adopt an IDS to detect malicious body sensors in WBANs so as to protect patients' privacy. We integrate cloud computing into WBANs to extend body sensors' abilities of computation and storage. Thus, plenty of computation cost incurred by IDS agents can be migrated from body sensors to the cloud platform. We construct an IDSRG in which the game type and corresponding equilibriums are different from [41–44], in order to seek the optimal strategy to decide when to report events monitored by IDS-sensors. The signaling game used in our work properly depicts the actual situation in which an IDS-sensor is uncertain about the type of its opponent. Our work is especially motivated by [22]. However, when analyzing the payoffs of two players, we consider the factors, including the channel reliability, attack success rate, detection rate, and false alarm rate, while only the detection rate and the false alarm rate are considered in [22]. Consequently, we attain the optimal strategies that are more adequate than those in [22].
3. A Report Game for WBANs Using a Cloud-Assisted IDS
3.1. Network Model
In [49], Farooqi and Khan have overviewed that there are three different ways of installing IDS agents in Wireless Sensor Networks. These are purely centralized, purely distributed, and mixed. In the purely centralized mode, an IDS agent is installed in the sink or base station. For realizing this way, an additional special routing protocol that collects information from sensor nodes is required so that the IDS agent can evaluate the behavior of sensor nodes according to the collected information. On the contrary, an IDS agent is installed in every sensor node in the purely distributed mode. It checks the data received in its communication range and declares whether a sensor node is compromised or not. Different from the two modes above, in the mixed mode IDS agents are only installed in monitor sensor nodes that are initially assigned. These monitor sensor nodes not only perform activities like normal sensor nodes but also check for intrusion detection.
To exert the powerful storage and computation capability of cloud computing, we adopt a new hybrid mode to realize a cloud-assisted IDS for WBANs, as depicted in Figure 1. In our mode, we deploy IDS agents in each body sensor, unlike the traditional case that the IDS agent is only installed in monitor sensor nodes. However, not all IDS agents work continuously; only IDS agents residing in body sensors that are selected as relays to forward information will be triggered to launch. Another different aspect is that the IDS agent in our network is only responsible for the monitor task, not including intrusion decisions that are made by the IDS in the cloud platform.

Network model of WBANs using a cloud-assisted IDS.
In Figure 1, the IDS-sensor audits data coming from those body sensors that lie inside its radio range or are its neighbors. It produces alert events if any body sensor works abnormally and may report them through the sink to the detection engine that exists in the cloud platform.
Now, a problem that will arise is how to select the optimal report strategy when a cloud-assisted IDS is applied to WBANs. The optimal strategy to be attained should maximize the probability of capturing malicious body sensors but minimize the report cost. To solve this dilemma, we next employ a dynamic multistage signaling game to model interactions between a body sensor and its corresponding IDS agent.
3.2. A Stage IDS Report Game
Definition 1.
The stage IDS Report Game (IDSRG) for WBANs using a cloud-assisted IDS is a 5-tuple P:
In the stage IDSRG, we consider there are two players, that is, body sensor S and IDS-sensor I. Body sensor S has private information about its type, which may be normal, denoted by
At each time slot, each player selects its action from its action space. If body sensor S is normal, it always cooperates. Its action denoted by
To express the payoff matrix of the stage IDSRG, we introduce some parameters. A malicious body sensor can select the action Attack to waste the limited resources of WBANs and disrupt normal network operations. Such an attack can result in, for example, a failure of communication between two neighbors. The malicious body sensor, however, gets a gain from the attack while it has to pay the cost of consuming power to launch the attack. We therefore present
We can next analyze various payoffs under different action profiles of two players, which are shown in Table 1. For the action profile
Payoff matrix of the stage IDSRG.

3.3. Equilibrium Analyses of the Stage IDSRG
The stage IDSRG belongs to a game of incomplete information, since an IDS-sensor does not know its opponent's type during interactions. We should therefore change it into a complete but imperfect information game through the Harsanyi transformation to attain the corresponding BNE. During the process of the Harsanyi transformation, a virtual player Nature is introduced and moves first to choose a type of player S. Thus, the extensive form of the stage IDSRG can be constructed in Figure 2, where p chosen by Nature is the probability of a body sensor being malicious.

Extensive form of the stage IDSRG.
Theorem 2.
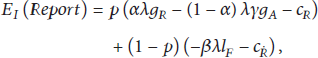
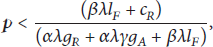
In the stage IDSRG, there exists a probability threshold of a body sensor being malicious,
Proof.
Case 1. Player S chooses the pure strategy
Under Case 1, the expected payoffs of player I selecting actions Report and Not-report are




Case 2. Player S chooses the pure strategy
To sum up, a pure-strategy BNE
The pure strategy attained from Theorem 2 means that player S always plays the action Attack for a malicious body sensor or Cooperate for a normal body sensor while player I always plays the action Not-report. This pure strategy is not practical because the equilibrium requires player I to take the action Not-report at all times, and hence malicious body sensors will not be captured forever. In fact, the equilibrium attained from Theorem 2 is referred to as Pooling Equilibrium [50] in which player I has no clue about the type of player S. Therefore, it is essential to find a mixed-strategy BNE for capturing malicious body sensors.
Theorem 3.
In the stage IDSRG, there is a mixed-strategy BNE if
Proof.
From Theorem 2, obviously, the mixed-strategy BNE to be sought exists only if 






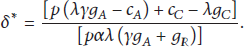
To sum up, given
Theorems 2 and 3 provide the IDS-sensor with the conditions under which the BNE can be achieved. We can obtain the probability threshold of a body sensor being malicious,
The advantage of applying Theorems 2 and 3 is that an IDS-sensor is not always in taking the action Report. As a result, the power consumption of the IDS-sensor can be conserved. However, Theorems 2 and 3 are only concerned with a slot time of interactions between an IDS-sensor and its opponent. As two players continually interact with each other, the belief (i.e., probability of a body sensor being malicious), p, which is used to compute the optimal strategy for an IDS-sensor to determine when to select the action Report, may be updated dynamically. Therefore, we should develop the stage IDSRG into a dynamic multistage IDSRG to dynamically present the belief of player I on the type of player S.
3.4. Dynamic Multistage IDSRG
Following interactions between players S and I, the stage IDSRG is repeatedly played at each continuous time slot
Definition 4.
The posterior belief hold by player I can be computed by

As described beforehand, the cloud-assisted IDS may inevitably produce detection errors and false alarms. In addition, communicating in WBANs may lose packets. Due to these factors, the actions observed by player I may not always reflect the reality accurately. We integrate these factors into computing the conditional probability 
So far, a belief system based on (15)-(16) has been presented to describe the belief building and updating process. It is easy to see that each belief to be updated is dependent on a body sensor's action player I observes at the current stage IDSRG and the prior belief it holds. With the belief system, we can define the dynamic multistage IDSRG as follows.
Definition 5.
The dynamic multistage IDSRG is a 5-tuple
For the dynamic multistage IDSRG, Perfect Bayesian Equilibrium (PBE) can be applied to seek the optimal strategies of two players. This is because the dynamic multistage IDSRG is essentially regarded as a dynamic Bayesian game. With the aforementioned belief system, the dynamic multistage IDSRG is played in a sequential manner. Players S and I will not always select the same strategies at each stage game to attain the most expected payoffs. Their best response strategies are related to the current belief that may be changed as the dynamic multistage IDSRG evolves. This relation can be disclosed by the concept of PBE. We next illustrate that the dynamic multistage IDSRG satisfies the Bayesian conditions, which guarantee that an incomplete information game has a PBE.
Lemma 6.
The dynamic multistage IDSRG satisfies the following Bayesian conditions B(i)–B(iv) referred to in [50]:
B(i):the posterior beliefs are independent, and all types of player I have the same beliefs. B(ii):the Bayesian rule is used to update beliefs from B(iii):the players do not signal what they do not know. B(iv):the posterior beliefs are consistent with a common joint distribution on
Proof.
B(i) is satisfied because player I has only one type. B(ii) is satisfied because the beliefs updated in the belief system are derived from the Bayesian rule. B(iii) means
Theorem 7.
There is a mixed-strategy PBE in the dynamic multistage IDSRG.
Proof.
At the 




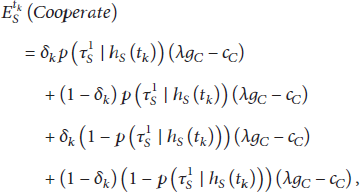


To sum up, there is a mixed-strategy PBE that can be attained with the strategy profile ((Attack with
From Theorem 7, the two rational players S and I at the
4. Applying PBE-Based Report Strategies to WBANs Using a Cloud-Assisted IDS
To facilitate the advantage of the above PBE, we propose and design a framework of applying IDSRG to WBANs using a cloud-assisted IDS, as illustrated in Figure 3. The framework consists of three entities: body sensor S, IDS-sensor I, and cloud platform. Body sensor S may be normal or malicious; it therefore signals the action Cooperate or Attack that forms Monitored Events. As the opponent of body sensor S, IDS-sensor I captures those Monitored Events and decides whether to report them to cloud platform through the sink. Once cloud platform receives the Reported Events, the IDS will be immediately triggered as a service and then examine the obtained record. Finally, according to alerts produced by the IDS Administrator may send Control Data to deal with a malicious body sensor.

Framework of applying IDSRG to WBANs using a cloud-assisted IDS.
The heart of the framework is PBE calculation whose results indict IDS-sensor I with the probability of selecting the action Report. This calculation starts with Monitored Events captured by IDS-sensor I. Administrator first configures the IDS agent in IDS-sensor I with Configuration Data for making it more reliable and accurate. He/she also defines the game parameters required, including α, β, γ, λ,
(1) (2) Initialize game parameters α, β, γ, λ, (3) Select the action Not-report; (4) Do UNTIL the end of interactions between an IDS-sensor and its opponent (5) Waked by Monitored Events; (6) IF the IDSRG is not existed (7) Construct a game; (8) ELSE (9) Get the stored game; (10) ENDIF (11) Compute (12) Compute (13) Update (14) Select the action Report with probability (15) (16) ENDDO
The other important part of the framework is the IDS in cloud platform. It consists of three main components: Detection Engine, Alert Database, and Alert Management. Detection Engine is the core component of the IDS, which decides whether an event sent from IDS-sensors through the sink is normal or abnormal. It may combine two of well-known detection techniques, including misuse and anomaly-based detection. It may compare the event to a predefined rule set or perform the process of multipattern matching. Upon completion, it distinguishes the event as normal or abnormal one and inserts the generated alerts into Alert Database. As a storage unit to maintain all the formatted events created by Detection Engine, Alert Database stores body sensor ID, the timestamp of various events, and packet information with the defined signatures. Some alert groups and statistics produced by Alert Management are also contained in Alert Database. Depending on Alert Analysis, Alert Management is applied to observe the generated alerts and relate them to previously defined attacking cases. This tool provides Administrator with a function to extract events and to produce reports based on source, time, and types of attacks. Finally, Administrator examines these findings and decides whether to send Control Data to those malicious body sensors.
5. Experiments
In this section, we employ MATLAB R2010a to illustrate the characteristics of the dynamic multistage IDSRG. Since we are the first to study the report game in WBANs using a cloud-assisted IDS, we do not compare our work with any prior work. Here, we explore the factors influencing a malicious body sensor to select the action Attack, in order to disclose its optimal attack strategies. We further, through an IDS-sensor's posterior belief computed by Algorithm 1, evaluate the performance of our proposed framework with the probability of a body sensor being malicious in terms of IDSRG parameters at the
5.1. Analyses on Optimal Attack Probabilities
We show the changeable trend of the optimal probability of a malicious body sensor selecting the action Attack in terms of α, β, and γ, in order to disclose the intension of a malicious body sensor. The rates of higher detection and lower false alarm make a cloud-assisted IDS easy to capture the malicious body sensors. Therefore, the optimal strategy of a malicious body sensor is to reduce the probability of selecting the action Attack to avoid the captured loss. On the other hand, the higher attack success rate helps a malicious body sensor attain its expected payoff more quickly. As the case we expect, the optimal probability of a malicious body sensor selecting the action Attack, from Figure 4, slowly decreases when the detection rate gradually increases from 0.5 to 1. A similar tendency is shown as the false alarm rate decreases from 0.1 to 0. In Figures 5 and 6, the decrement of the optimal attack probability selected by a malicious body sensor is followed with the increments of the attack success rate, detection rate, and false alarm rate. Further, the influence of the attack success rate is lower than that of the other two factors. When

Optimal attack probabilities in terms of α and β.
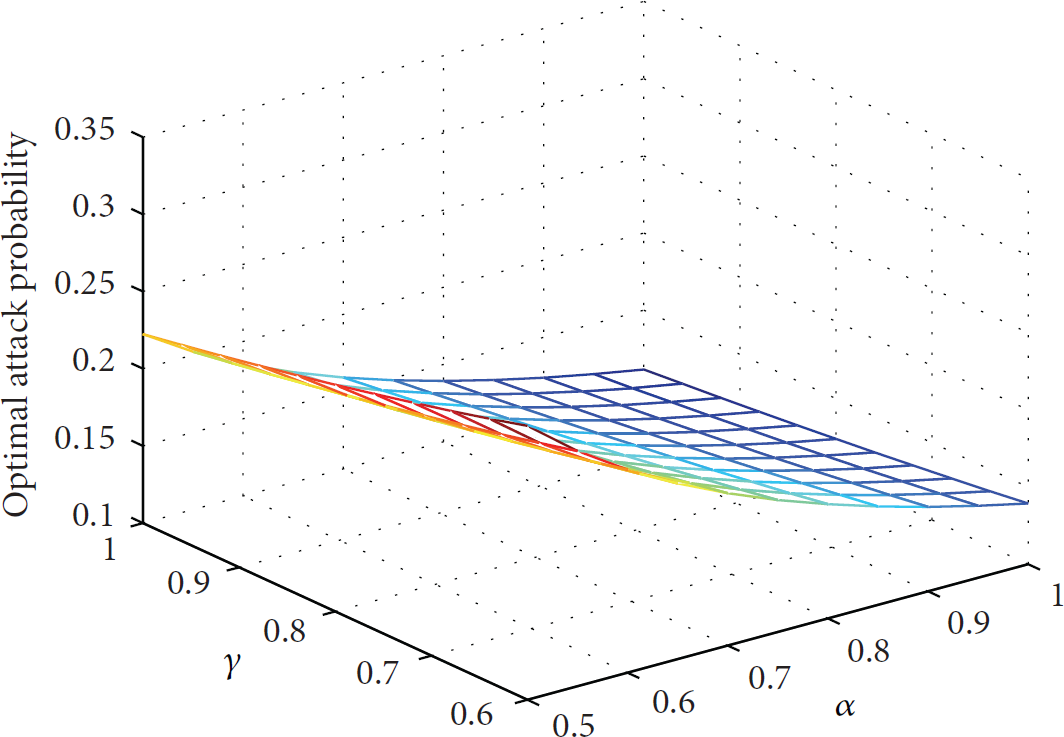
Optimal attack probabilities in terms of α and γ.
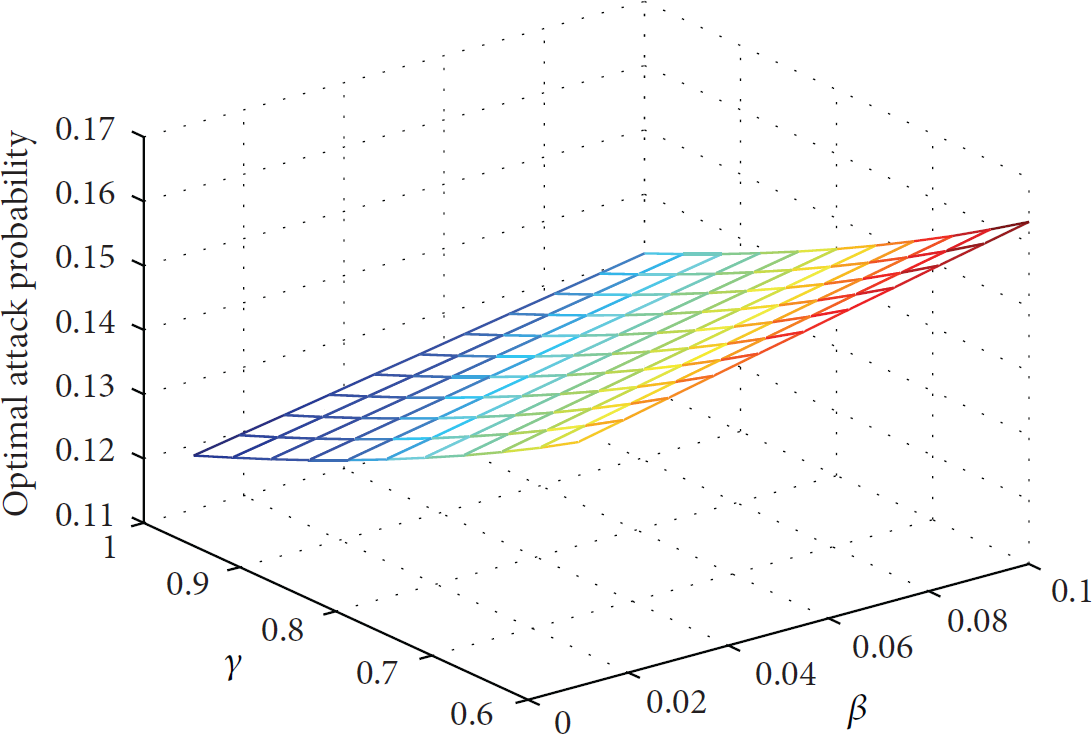
Optimal attack probabilities in terms of β and γ.
5.2. Performance Analyses
At the
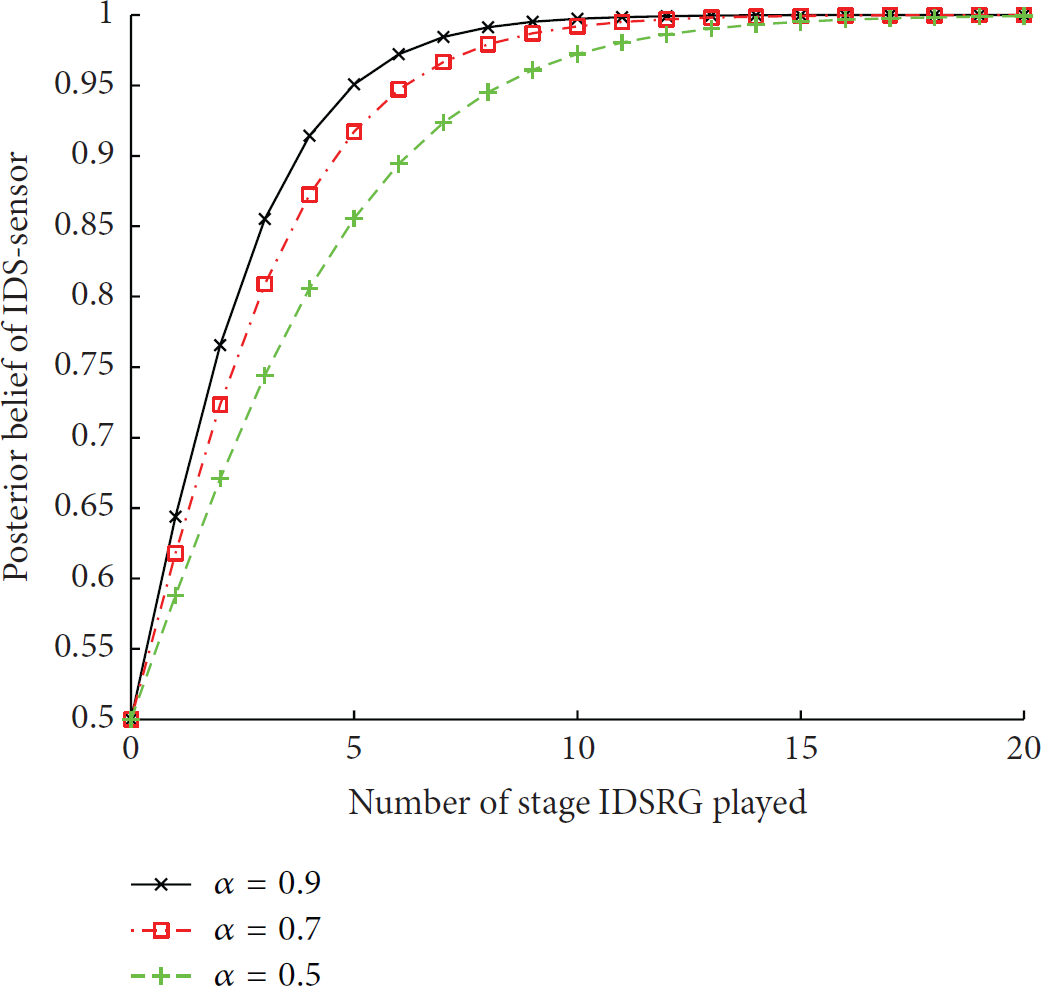
Probability of successfully detecting a malicious body sensor under different detection rates.

Probability of successfully detecting a malicious body sensor under different false alarm rates.
Figure 9 compares the convergence of an IDS-sensor's posterior belief when different actual-attack-gains denoted by
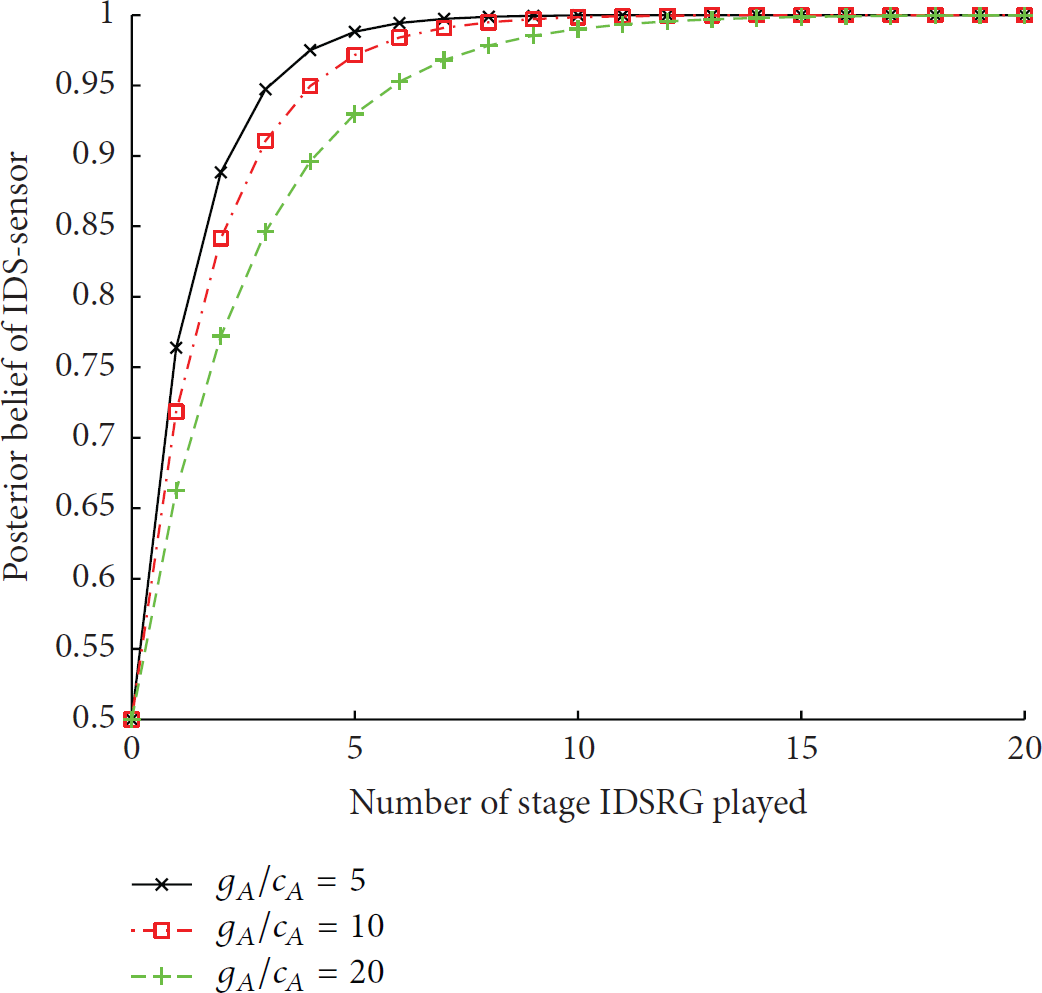
Probability of successfully detecting a malicious body sensor under different actual-attack-gains.
In Figure 10, we let

Probability of successfully detecting a malicious body sensor under different actual-report-gains.
In what follows, we analyze how the historical actions taken by a malicious body sensor influence the convergence speed of the posterior belief, as shown in Figure 11. We assume two observation sequences:
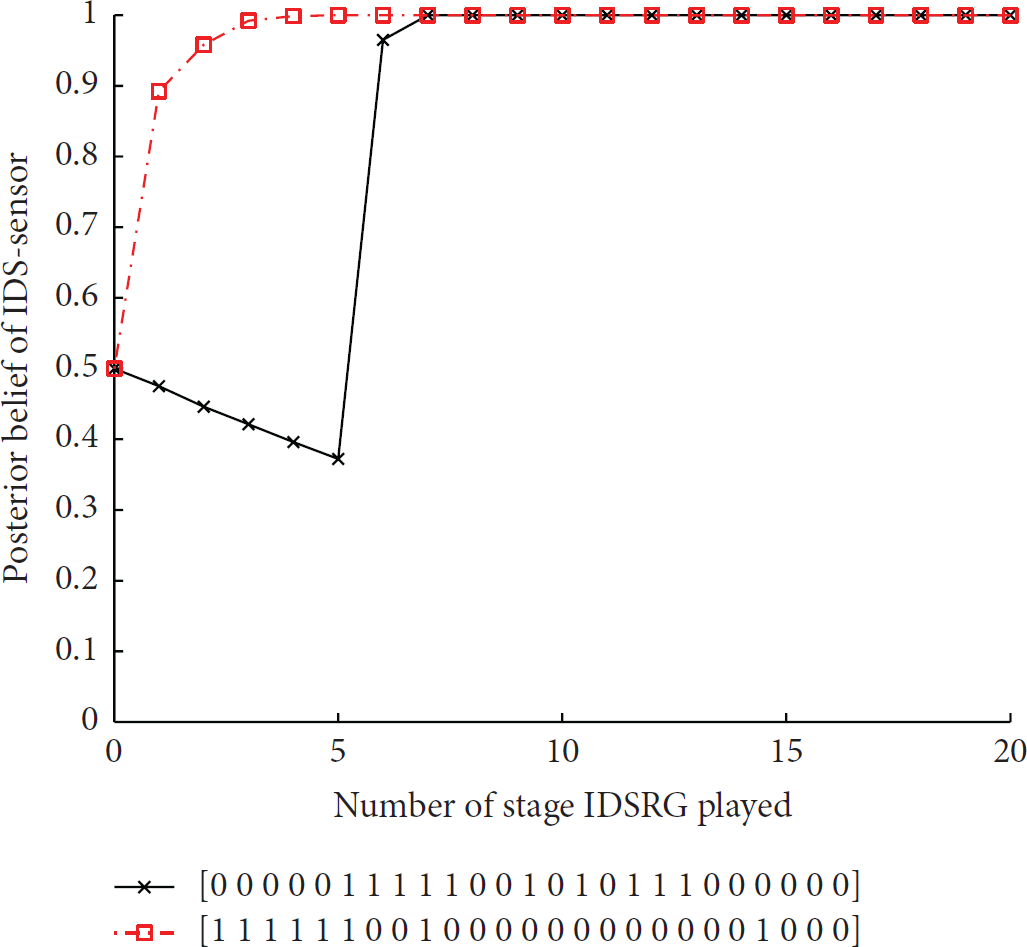
Probability of successfully detecting a malicious body sensor under historical actions.
6. Conclusion
We have presented an IDS framework with the help of cloud computing, in order to quest for security of WBANs. It extends WBANs to an integrated platform that offers scalability of data storage and computation for launching an IDS. With this framework, IDS-sensors are only responsible for whether or not to report the monitored events, not for performing the costly task of intrusion detection. Thus, the deficiency of limited resources in WBANs is no longer a problem to guarantee security of WBANs. Moreover, to solve the IDS-sensors' dilemma between saving energy and reporting the monitored events to increase the probability of capturing the malicious body sensor, we have proposed a dynamic multistage IDSRG using the signaling game. Our game is able to depict interactions between a malicious/normal body sensor and its opponent IDS-sensor and is able to reflect their payoffs. We have proven that the stage IDSRG has a pure-strategy BNE or mixed-strategy BNE under different conditions of the probability of a body sensor being malicious. As the game evolves, we have extended the stage IDSRG to a dynamic multistage IDSRG, where the belief hold by IDS-sensors can be updated rationally and dynamically according to the current and historical actions of malicious body sensors. We have also proven the existence of the mixed-strategy PBE in the dynamic IDSRG. This mixed-strategy PBE helps IDS-sensors select an optimal strategy that will prolong their lifespan while allowing them to report an acceptable amount of monitored events. A report strategy algorithm is designed to implement the mixed-strategy PBE. Experiments have shown, based on the optimal report strategies computed by the proposed algorithm, that the type and optimal strategy of a malicious body sensor can be predicted. Thus, body sensors are capable of saving their energy while the cloud-assisted IDS is able to actively defend malicious body sensors.
While the proposed approach works in principle, we plan to implement it by developing a cloud-assisted IDS testbed via Castalia 3.2, a simulator based on OMNeT++ 4.3.1. Depending on the future experiment results, a more accurate IDSRG to further enhance its decision-making capability in order to prevent body sensors from malicious attacks maybe will be attained.
Footnotes
Notations
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work was supported by the National Natural Science Foundation of China under Grant no. 61272034, by Zhejiang Provincial Natural Science Foundation of China under Grants LY13F030012 and LY13F020035, and by Science Foundation of Shaoxing University under Grant no. 20145021.
