Abstract
The ever-more-capable smart mobile phone gave birth to a novel sensing paradigm, participatory sensing. In the application environment of mobile participatory sensing networks, mobile equipment is usually weakly connected. Due to uncertainty of connection, mobile nodes sometimes need encounter opportunities to accomplish data communication and transmission. However, the participants’ reluctance would diminish their enthusiasm if there is no incentive mechanism. To address this nontrivial issue, we propose reputation-based incentive schemes to motivate participants to disseminate reliable data in participatory sensing system, named RIDD, while minimizing incentive cost for maintaining sufficient number of reliable participants. When an intended receiver receives the data packet from a participant, the receiver authorizes the participant by an acknowledgment message within an encryption code automatically generated by the data packet, which serves as a proof of successful data delivery. RIDD evaluates participants using reputation degree calculated according to the encryption code, encouraging reliable participants to keep being interested in the participatory service with rewards. We conduct simulations in different scenarios. The results show that RIDD remarkably increases the winning probability of participants who disseminate accurate data and reduces the cost for retaining sufficient number of reliable participants.
1. Introduction
Smart phones are penetrating human life and over 1 billion people make use of them globally. With the high processing power, sophisticated embedded sensors, larger storage support, and full networking capability, the mobile phones promise to support services like information sharing, mobile social networking, environmental detection, and traffic monitoring by integrating ubiquitous sensing, large-scale data collection, and cloud computing. These are the advantages that gave birth to a novel and exiting sensing paradigm, participatory sensing [1, 2]. Several universities and institutes have done relevant research in this area and a plethora of exciting participatory sensing applications have emerged in recent years. PEIR [3] is a participatory sensing application which tries to estimate the environment impact to their action based on their location information provided by mobile phone. CarTel [4] is a vehicle participatory sensing system designed to collect, process, deliver, and visualize traffic data from vehicles. Bubble-Sensing [5] is a new sensor network abstraction that allows mobile phones users to create a binding between tasks (e.g., take a photo or sample audio every hour indefinitely) and the physical world at locations of interest, which remains active for a duration set by the user.
The mobile nodes communicate with each other via cellular base stations in the traditional cell networks. With the increasing demand for faster data connectivity, different wireless technologies have been deployed in the last decade, creating a heterogeneous wireless environment. Such wireless diversity is mainly composed of 2G/3G/4G cellular base stations, IEEE 802.11 hotspots, and Community Networks [6]. Mobile participatory sensing network is often created for a local community in which the participants have frequent interactions. Smart phones can communicate with each other and exchange sensing data via their short range radios (e.g., WiFi, Bluetooth, Zigbee, and WiFi-direct). Such mobile device-to-device data transmission can increase network performance and reduce communication cost for both service providers and individual users. A crucial issue is how source nodes choose forwarding participants. The goal is to choose a participant which delivers a message to destination with high probability. Except for that goal, reliable data delivery is also very important in the realistic application environment. However, participants will eventually lose enthusiasm to remain active in participatory sensing applications without being fairly rewarded. Namely, participants may drop out unless the reward is greater than their expectation. Furthermore, there are some malicious participants who will disseminate bogus sensing data when the realistic participatory sensing networks are deployed. Malicious participants may supplant normal ones and it may be worse when they collude with each other. In such circumstances, normal participants drop out and malicious ones will control the system without hesitation. To fill this gap, we design an incentive mechanism to motivate participants to disseminate reliable sensory data.
Within the scope of this paper, we propose the reputation-based incentives for data dissemination (RIDD) to categorize and motivate participants, while minimizing incentive cost for maintaining sufficient normal participants which always disseminate reliable sensing data.
RIDD first analyzes the disseminated data to evaluate the trustworthiness of participants using accumulated reputation degree. Then a multidimensional reverse auction will be performed by RIDD and reputable participants who bid lower price will win the reward. Furthermore, RIDD will adjust each participant's bid price and increase winning probability of loser in the next auction round according to their reputation level.
The following is a list of our main contributions.
We establish reputation model to evaluate the trustworthiness of participants by reputation degree. The reputation degree is calculated according to reliability of disseminating data. High reputation degree reflects accumulation of good historical participations and vice versa. We design reputation-based incentive scheme (RIS) for data dissemination in mobile participatory sensing networks. RIS can remarkably decrease incentive cost for maintaining sufficient participants through multidimensional reverse auction where bid price and reputation degree are both considered. Virtual coupon is introduced in RIS in order to increase winning probability of the reputable participants in the next auction round. We design data dissemination algorithms based on RIS, named RIDD. RIDD is an efficient data dissemination algorithm to encourage mobile nodes to continuously participate in data dissemination activities and provide reliable data messages with low transmission cost and high delivery ratio.
The remainder of this paper is organized as follows. In Section 2, related works about data dissemination algorithm, reputation model, and incentive scheme are illustrated. Section 3 gives details of RIDD. In Section 4, RIDD is evaluated in various simulations. Finally, we conclude this paper in Section 5.
2. Related Work
2.1. Data Dissemination in Mobile Participatory Sensing Networks
Data dissemination in the mobile participatory sensing networks has opportunistic and community characteristics. The mobile nodes transmit data messages by the store-carry-forward way. The mobile node utilizes communication opportunities obtained from node movement to relay packets. Such data dissemination schemes are proposed in social opportunistic networks applications. The data dissemination in PeopleNet [7] is based on epidemic dissemination. A contact aware duplication algorithm [8] is proposed for data sharing in interconnectivity mobile network. In [9], the scheme is proposed for information sharing among people onboard vehicles. However, all of these dissemination schemes assume nodal cooperation in opportunistic networks.
Selfishness of mobile nodes has been investigated in the context of mobile ad hoc networks. Their ultimate goal is to stimulate nodes to help by forwarding packets for others. However, these incentive approaches are not directly applicable in DTNs. In [10–13], these schemes have reputation-based or credit-based incentive schemes. In all of these scenarios, receivers are beneficiary and paid for data delivery services in one way or another. Clearly, they are different from the participatory sensing data dissemination application studied in this work, where individual nodes can be data providers and push data packets to a set of receivers. All these schemes cannot preserve the reliability of the data message and prevent the malicious behaviors of the participants.
In [14], TB-SnW is a data dissemination algorithm designed based on trust management in delay tolerant networks (DTNs) that suffer from black hole attacks, which solves the issue that malicious nodes discard the data packet but not the integrity and security of the transmitted data. RCAR [15] is a reputation-based approach to tolerate misbehaving Carriers in DTNs, and there is no global agreed notion of reputation. In [16], if a relay node fails to show successful relay proofs, it is excluded from future communication. However, the permanent penalty on selfishness leads to the participants reluctant to join the participatory service.
An incentive mechanism based on being self-interest-driven (SID) is presented in [17], where cooperation between selfish nodes for ad dissemination in autonomous mobile social networks is stimulated. It provides virtual checks schemes to reward the mobile nodes in an autonomous mobile social network. We will compare SID with RIDD in Section 4.
2.2. Incentive Scheme
In order to stimulate the mobile nodes to provide reliable data dissemination service, the incentive scheme is designed in our data dissemination algorithm. Generally, incentive schemes can be classified in to two categories: Extrinsic Incentive and Intrinsic Incentive. Extrinsic Incentive involves financial rewards [18, 19] and reputation [15]. Reversely, Intrinsic Incentive confines to fun interest [17], self-improvement, self-expression, and charity.
What we consider as the most relevant work is incentive mechanism of financial rewards. In this way, the active and well-behaved nodes can obtain some remuneration for their participation [20]. The mechanism of distinguishing services mainly provides different level services to sensors according to their behavior [21]. The mechanism, by its very nature, offers more resources and services to incentive reputable nodes.
Reverse auction is a special form of offering rewards. In a general auction, buyers become bidders and the seller is an auctioneer. By comparison, in a reverse auction there is a single buyer that becomes an auctioneer while many sellers become bidders. In terms of bidding sides, auctions can also be classified as single or double ones. In a single auction, only one side of participants can bid. On the other hand, in a double auction, both sides of participants can bid.
All abovementioned auction types use bids that comprise only price, so we call it one-dimensional reverse auction. In contrast, a multidimensional reverse auction allows bidders to bid on various attributes beyond the price. Since the auctioneer selects winners based on all bidding attributes, the overall utility of a bid should be computed following various utility functions. General procedures for multidimensional auctions in e-markets have been described in [22].
Recent studies in [19] have proposed a motivation system, named the reverse auction based dynamic price incentive mechanism with virtual participation credit (RADP-VPC).
To the best of our knowledge, few studies address incentive mechanisms with multidimensional reverse auction in participatory sensing system well. RIS is the reputation-based incentive system where a multidimensional reverse auction is introduced with considering participants’ reputation.
2.3. Reputation Model
Reputation model is the measure of weight quality of the data services, which have been used in ad hoc wireless networks [23–26]. In [23, 24], reputation model based on game theory attempted to address the selfish routing problem in such networks. In [25, 26], Bayesian analysis is used to formulate a similar problem and the resulting reputation models are shown to counter any misbehaving nodes. Bayesian reputation models are quite flexible and can be adapted with relative ease in different types of applications and environments [27, 28]. The reputation frame work proposed in [29] makes use of Beta reputation [27] for associating a reputation score with each sensor node in a traditional embedded wireless sensor network. However, it takes a less aggressive approach in penalizing participants that contribute corrupted data.
To the best of our knowledge, a few research works are conducted on reputation in mobile participatory sensing networks. Huang et al. in [30] implements a noise monitoring system to identify corrupted noise data. However, the system only focuses on the sensing data provided by participants in current monitoring application without considering accumulated reputation of participants. Haofan et al. proposes using reputation management to classify the gathered data and provide useful information for campaign organizers and data analysts to facilitate their decisions [18]. However, the author just provides a simple reputation method and cannot adapt to the changeable environment when participatory sensing system deploys in the real world.
All abovementioned reputation models are not used in the data dissemination service in mobile participatory sensing networks and are not combined with the incentive schemes to measure the integrity and security of the delivering data. In our algorithm, reputation model is established to weigh the reliability of participants and provide evidence to the incentive scheme which gives rewards to recruit more reputable participants to finish the data dissemination service.
3. Reputation-Based Incentive Mechanism
In this section, we propose the reputation-based incentives for data dissemination (RIDD) in the context of mobile participatory sensing systems.
3.1. System Overview
A mobile participatory sensing network is a mixture of an opportunistic network and a centralized infrastructure (as shown in Figure 1). The opportunistic network consists of a set of intermittently connected mobile nodes. The data exchanged in this scenario is assumed to be of high magnitude, and data transmission can only occur between mobile nodes by short range communication during the contact opportunity. The centralized infrastructure consists of a number of wireless access points (APs) and a backbone connecting the APs. Mobile nodes (carrying smart devices) can only access the network when they are walking into the transmission range of any AP. The centralized server is merely responsible for executing the reputation-based incentive scheme (RIS), only exchanging control messages with mobile nodes. Each mobile node can act as a sensing data provider, a participant to disseminate the sensing data, or a data receiver. The mobile nodes can play different roles or act those roles simultaneously. A sensing data provider senses the data from his environment according to what the system desires. The participant is the mobile node who applies for participating in the data dissemination service. The participant obtains data from the provider and then transforms the data message to the data receiver or to the next mobile nodes.

Data dissemination model based on RIS.
The mixture network model enhances traditional opportunistic networks with the centralized infrastructure which takes good advantage of existing AP assets but does not burden current network. The control message is very tiny compared with the data message, so the transmission overhead of the control message can be negligible. The APs are deployed according to the density of the mobile nodes. For example, in the campus scenario, each room in the teaching buildings and library deploys at least an AP router. Therefore, the system model can avoid the hotspot problem.
The RIS server provides the services on reputation calculation and the incentive mechanism execution. The RIS server transmits only control messages but not data messages. The data messages are delivered by the participatory nodes.
3.2. Reputation-Based Incentive Schemes
In the data dissemination systems, the reliable data dissemination is vital to the quality of service. The schemes should be designed to preserve the integrity and reliability of the data message. In the proposed system, the data message is transferred between the participants and the receivers. If the participant corrupts the data message or discards the data message, only to cheat the system rewards, the RIS server could not detect the malicious behaviors of the participants.
3.2.1. The Framework of RIS
In order to tackle issue of malicious behaviors of participants, the encryption code generation scheme is proposed. When the participant transmits the data message to the receiver node, the receiver node will give feedback by an ack message to the participants.
The format of the ack message is ack<copy id, data id, digital signature, encryption code>. Digital signature is generated by the receiver node, which is the identification of the mobile node. This metric is used to estimate the data discarding behavior of the participant. If the participant really finished a data transmission, it can get the digital signature of the receiver. Encryption code is generated by the data provider. The encryption code can be a hash code of the data, which is uniquely represented by the original data. If the data have been distorted or corrupted, the encryption code will change. In the proposed system, the RIS server is authorized to be creditable. Finally, the participant accomplishes the task and submits all the feedback messages to the RIS server. The RIS server will calculate the encryption code set categorized by the data id to give out the reputation of the participant.
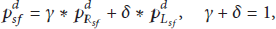
Figure 2 depicts the framework of RIS. Generally, data dissemination request is sent (e.g., by smart phone or PDA) to the participants through RIS server in mobile participatory sensing networks. After data dissemination, each participant submits the feedback messages to the server and RIS residing in the server processes all data obtained from participants.
Framework of RIS.
Firstly, encryption code will be uploaded to the Reputation Module where the reputation score of the participant is produced, respectively. After that, the reputation degree can be successfully derived based on game theory.
Then, a multidimensional reverse auction in the Incentive Module selects winners in terms of Rank Prices which are calculated based on participants’ bid prices and the virtual coupon they possess.
Finally, the participants with lower Rank Prices win out, get reward, and reset their virtual coupon to zero. Nevertheless losers will obtain virtual coupon to raise their winning probability.
3.2.2. Reputation Model
In general, the number of normal participants is usually larger than that of malicious participants in a target field, so we choose the density-based outlier detection algorithm proposed in [31] to preprocess the encryption code set of disseminating data
As shown in Figure 2, the algorithm is iterative in nature. At first, it defines and initializes
It is obvious that tighter convergences could be chosen to produce more accurate result according to specific scenarios. ε is a small positive constant for adjustment and more discussion can be found in [31].
As mentioned in Algorithm 1, normal participants are usually more than malicious ones in mobile participatory sensing networks. Consequently, the majority of participants who provide similar sensing data will have higher
Input: Number of participant Output: (1) for (2) (3) while convergence do (4) Compute A using (1); (5) for (6) Compute (7) end (8) (9) end (10) (11) end
Algorithm 1
However, in particular circumstances, the number of malicious participants would be larger than that of normal ones in sensing field which will affect overall data accuracy. It may lead to fatal error when making decisions based on such corrupted data provided by malicious ones in the networks. To tackle this issue, the source data node can generate the encryption code to the RIS server.
After several rounds, a participant will present its trustworthiness through its historical behaviors. The trimmed-mean method [32] is introduced to reflect the long-term trends accordingly. The method is a statistical measure of central tendency and involves the calculation of mean value after discarding given parts of a probability distribution or sample at the high and low ends and typically discarding an equal amount of both.
The reputation score
3.2.3. Incentive Module
To motivate participants, a multidimensional reverse auction is introduced in the Incentive Module. The objective of RBPIA is to maintain adequate number of participants for desired service quality while minimizing incentive cost by preventing cost explosion during the multidimensional reverse auction.
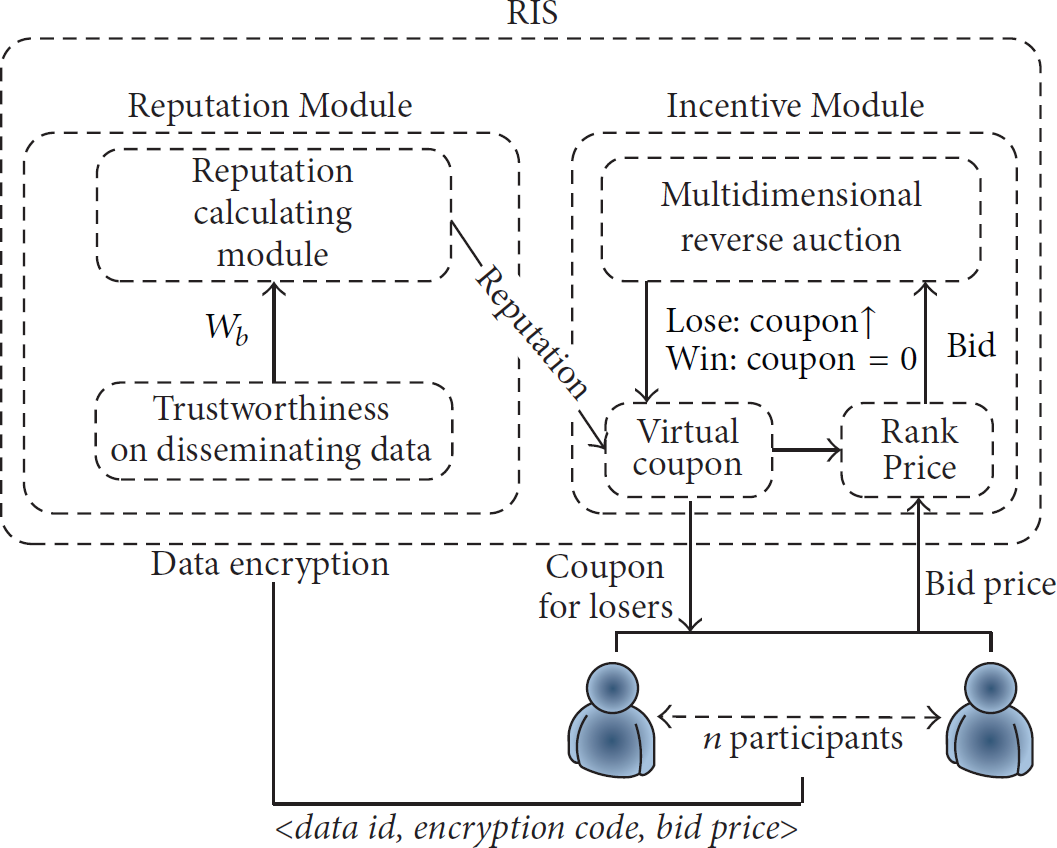
Intuitively, participants who bid lower price are more likely to become winners in one-dimensional reverse auction, as shown in Figure 3. However, the participants who always lose in auction may drop out. As a result, the winners can manipulate subsequent auctions and increase bid price to maximize their profits.
Winners and losers in one-dimensional reverse auction.
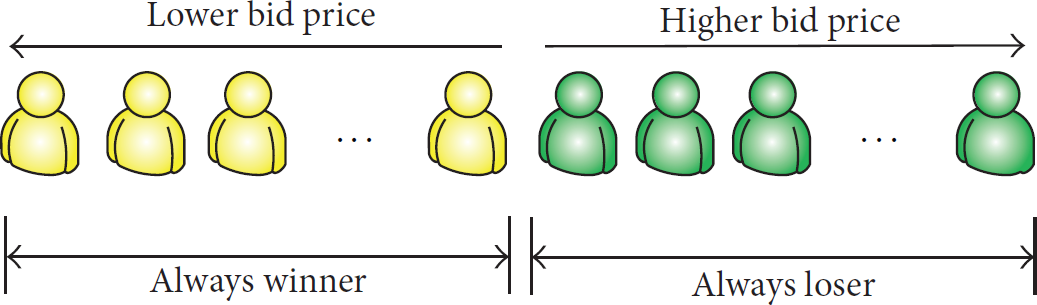
To maintain fair competition and prevent incentive cost explosion, enough participants should participate continuously in reverse auctions of RIS. For this goal, the proposed Incentive Module provides a novel winner selection strategy using virtual coupon and reputation degree.
Participant (i.e., bidder) i will receive virtual coupon as a reward when they lost in the previous auction round to increase winning probability in the next round. The virtual coupon
The virtual coupon
Two types of bid prices are defined. One is actual bid price and the other is Rank Price. The actual bid price
In the proposed Incentive Module, the Rank Price
Even participants who bid higher price can be winners by participating continuously (as shown in Figure 4). Therefore, RIS encourages continuous participation of participants in the system.

Winners and losers in multidimensional reverse auction with virtual coupon.
3.3. The Process of RIDD
The reputation degree is calculated by the RIS server; it will not influence the data transmission event. In order to increase the opportunity to transmit the data, each participant can obtain the data messages. The RIS server will estimate the reputation of every participant. If the participant misbehaved, it will be punished with no rewards. Otherwise, the participant with high reputation will gain rewards and also obtain the virtual coupon. Therefore, the high reputation the participant has, the more rewards the participant gains.
The data dissemination algorithm adopted the LOPSI [33]. It is deployed in the same scenario; it has a location prediction server, which can integrate with the RIS server; each node will choose a node with the max transmission probability to transform the data.
The LOPSI algorithm is a probabilistic routing protocol combining location prediction and the ant colony optimization. It firstly predicts possible locations of relay nodes and destinations in successive time series. The mobile nodes calculate intimacy (contact frequency) with potential relay nodes using ACO and then make a forwarding decision based on node intimacy and probabilities of node mobility. The transmission probability is calculated by
The control messages used in the system are defined as follows.
Definition 1.
SREQ is the service request message in which the data source node is sent to the RIS server. The format of SREQ is SREQ<data id, category id, source address, destination list>.
The data id uniquely represents the data message. The category id is the description of the content of the data message. Source address is the location information of the data source node. In the specific application environment, it can be AP address. The source address is used as a broadcast scope by the RBPIA server that broadcasts service recruiting messages. The destination list involves the destination node addresses where the data message will be sent. The destination node is usually the data aggregation server or the node who desires the data message.
Definition 2.
PAT is the participatory message that the mobile node sends to the RIS server. The format of PAT is PAT<participatory id, bid price, copy number, additional data>.
Additional data can be the transmission probability of the node to the source node. The bid price equals the consumption that the participant transmits one data copy. The system will pay more than the participant consumes, so the mobile nodes are willing to participate in the service. The maximum number of data copies one participant can disseminate equals copy number.
The data dissemination process is as follows.
Step 1.
The data source node sends a SREQ message to the RBPIA server. When the data sensing node finishes the data dissemination service, it will send the encryption code of the data message to the RBPIA. The encryption code may be the hash code generated by the data message. It is used to calculate the trustworthiness on disseminating data.
Step 2.
The RBPIA server broadcasts the SREQ messages to the mobile nodes nearby the source address. The broadcast domains in the campus scenario are coverage areas of the communication radius of the APs to which the data source node connects.
Step 3.
When the mobile node Ni receives the SREQ message from the RBPIA server and would like to participate in the data dissemination service, Ni will send the control message PAT to the RIS.
Step 4.
If mobile node Ni wins the bid round, it becomes the participants.
Step 5.
When participant i encounters a mobile node, the former firstly transmits the destination address to the latter. If it is the receiver, the data message will be directly delivered. And the participant will get an ack message from the receiver. Otherwise, if the node meets a mobile node who has a higher transmission probability than the participants, the former will transform the data message to the latter. And the latter node returns an ack message to the participant who would like to forward the data message.
Step 6.
The participant I transmits a data message to the data receiver, it will get an ack message. The accumulated ack messages will totally send to the RIS server and get back the rewards.
Step 7.
If the mobile node wants to be the participant, it directly sends PAT message to the RIS server; the communication cost of send a PAT message is negligible. If the mobile node agrees with the bid price that the former participant gains, it receives the data message and gets several data copies from the former nodes and becomes a participant.
Step 8.
When participant i disseminates all the data copies, it will send the total ack messages to the RIS, and the RIS pays for the participant according to the results of reputation calculation.
4. Performance Evaluation
The purpose of the experimental section is to evaluate RIDD in two scenarios and illustrate its properties.
4.1. Performance Comparison Algorithms
Spray and Wait [34] is chosen as the baseline for comparison. It is a leading opportunistic routing algorithm, without consideration of selfishness. Under Spray and Wait, a number of copies are sprayed into the network and then the network “waits” till one of these nodes meets the destination. Since Spray and Wait does not consider selfishness of mobile nodes, we implement its two variants. The first which is denoted by “SaWselfish” is under the assumption that all nodes are selfish. Thus, a node only receives its desired data message directly from the source data node. In the other variant named “SaWcooperative,” we assume that nodes are cooperative and altruistic. A node always chooses the most valuable data messages to carry for others after satisfying its own convenience, considering its resources and routing.
SID is a self-interest-driven incentive scheme to stimulate cooperation among selfish nodes for ad dissemination in autonomous mobile social networks. A virtual check is included in each ad packet. When an intended receiver receives the packet for the first time from an intermediate node, the former authorizes the latter a digitally signed check, which serves as a proof of successful ad delivery. Multiple copies of a virtual check can be created and signed by different receivers. When a node that owns a signed check meets the ad provider, it requests the provider to cash the check. Both ad packets and signed checks can be traded among mobile nodes.
4.2. Simulation Setup
The representative participatory sensing data set is UCSD WTD data set [35], which is employed in our simulation scenarios. Note that the recent work studying the nature of human mobility has proved that suitable movement models can sufficiently present the behavior of human mobility [36]. The model of mobility pattern deployed in our platform is SPMBM model [37], which is a mobility model that integrates temporal and spatial relationships and selects the shortest path for the node randomly walking in the map area.
In our simulation, the simulation parameters are shown in Table 1. There are totally 200 mobile nodes that involve 160 pedestrians and 40 cars. The number of sensing data categories is forty. Each node has a default queue size of 200 packets. When a node acts as a data provider, it generates one data message every 10 minutes in a random data category. At the same time, a node is also interested in receiving data in 5 randomly chosen data categories. If the communication range increases and becomes out of the range of APs, the mobile devices can exchange data by the distributed part of LOPSI without using location prediction scheme by different wireless communication techniques including Wi-Fi direct, BlueTooth, and ZigBee. In order to evaluate the performance of the proposed data dissemination algorithms, we conduct a series of experiments under the parameters in Table 1. The First-In, First-Out method is applied on buffer management. The TTL of a packet is set to the expiration time of the data service. It is initially set in the control packet. In the simulation, the TTL is set at variable values in order to compare the performance of the incentive mechanism. The TTL of a packet indicates how long the packet can live in the network.
Simulation parameters.

4.3. Evaluation Metrics
In order to compare the incentive schemes, the proposed mechanism in [19] is deployed in the simulation. Specifically, as shown in (6) and (7), participants drop out or rejoin in auctions based on return on investment (ROI) and expected return on investment (EROI), respectively.
4.3.1. Return on Investment
The value of ROI is derived as follows:


Moreover, (7) is used for describing rejoining behavior of the dropped out participant. The recruitment mechanism broadcasts the maximum bid value of winners only to the dropped out participants. Hence, the dropped out participants k can calculate the expected ROI value
4.3.2. Utility Function
According to the utility function in [38], the adaptive bidding behavior of auction in simulation is represented as follows. If a participant loses in the previous auction round, the bid price will be decreased by 20% of current bid price for a next participation round. Conversely, if a participant wins in the last auction round, the bid price will arise by 10% of the current bid price or stay at the current bid price with equal probability for next round. For initial bids of participants, we randomly generate the first bid of each participant uniformly distributed between true valuation and its 150%. To observe the effect of participant recruiting mechanism, when the dropped out participant tries to rejoin based on expected ROI value
4.3.3. Malicious Behavior
We classify the participants into two categories: normal participant and malicious participant.
As shown in Table 2, normal participants upload accurate data in 90–100% of participations and bid according to their true valuation (i.e., the consumption for disseminating the sensing data).
Disseminating data provided by participants.

Malicious participants are supposed to intentionally provide corrupted sensing data (only provide accurate data in 10–20% of participations) and bid normal prices. The bidding behaviors of malicious participants do not follow utility function.
We run simulations in two scenarios (marked as scenario A and scenario B), and 200 participants are involved in the simulations (see Table 3).
Participant composition in two scenarios.

4.3.4. Performance Metrics of Data Dissemination Algorithms
The delivery ratio is defined as the ratio of the total number of accurate delivered data messages (the corrupted data messages and the discarded ones are excluded) to the total number of data messages that should be disseminated to the corresponding receivers.
The average latency measures how long a receiver node waits to get the data message packet.
The transmission cost is defined as the ratio of the total number of transmissions to the total number of delivered messages. Lower overhead means less traffic in the network and lower resource consumption. In the proposed system, the control message is much smaller than the data message and, therefore, its transmission cost is negligible.
The incentive cost of the system, noted as C, measures the rewards paid to the participants. It is defined in

4.4. Simulation Results
4.4.1. Incentive Cost
We run simulations for 50 rounds in scenario A and scenario B (as shown in Table 3). We compare the RIDD and SaWcooperative under the same reward values. Figures 5 and 6 depict the tendency of incentive cost in 50 participation rounds.

Incentive cost of RIDD and SaWcooperative in scenario A.

Incentive cost of RIM and RADP-VPC in scenario B.
In scenario A, both RIDD and SaWcooperative mostly select normal participants, and there are no malicious participants in this scenario, so the two schemes both keep low incentive cost. In contrast, as we can see from Figure 6, incentive cost of SaWcooperative increases dramatically from about round 20 in scenario B due to existence of malicious participants. Such phenomenon means that SaWcooperative cannot cope with malicious participants. The malicious participants disseminate the corrupted data. The system cannot distinguish the accurate data messages and the corrupted ones. Therefore, the system pays for all the delivered data messages, which results in high incentive cost.
4.4.2. Recruiting Reputable Participants
The recruiting mechanism is introduced into both RIS and RADP-VPC. We simulate rejoining behaviors of dropped out participants in two scenarios. The recruiting mechanism helps to increase the number of active participants and reduce incentive cost. Specifically, more reputable participants rejoin a participatory sensing system to prevent the system from being controlled by malicious participants.
Without malicious participants, recruitment of RIS and RADP-VPC can remedy the loss of active participants. As depicted in Figure 7 (scenario A), the number of recruited reputable participants in two schemes is about the same.
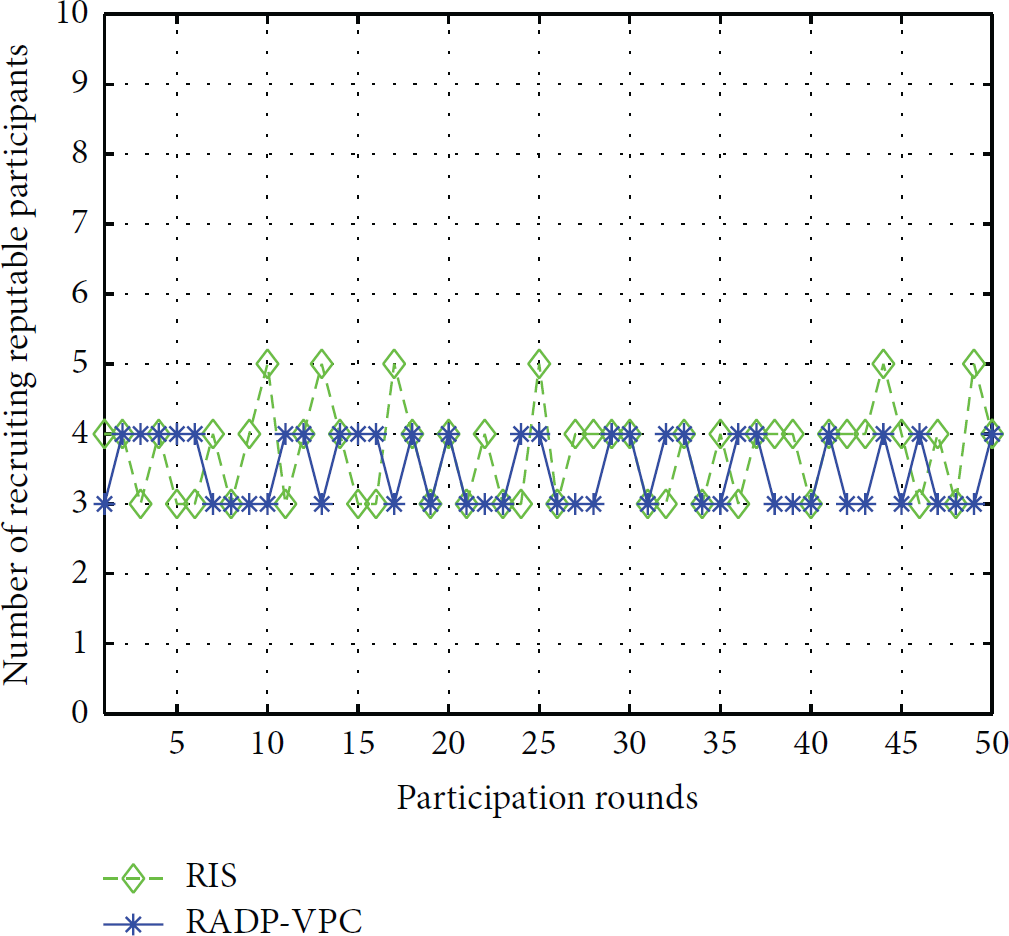
Number of recruited reputable participants in scenario A.
RADP-VPC selects winners only based on bid prices and cannot adapt to circumstances with malicious behavior. More specifically, malicious participants will bid lower prices to keep winning and kick normal ones out. RIS selects participants based on the reputation degree and the bid price. In Figure 8 (scenario B) RIS recruits more dropped out reputable participants than RADP-VPC.

Number of recruited reputable participants in scenario B.
4.4.3. Evaluation of Delivery Ratio
With the increasing ratio of malicious participants, RIDD performs well until the ratio reaches near 90%. RIDD prevents malicious participants from delivery corrupted data messages. SID has incentive mechanisms to stimulate mobile nodes to participate in the system service, yet without schemes to protect the reliability of the data messages, so the delivery ration decreases sharply. Also SaWcooperative cannot deal with the malicious behavior, so the delivery ratio decreases. Yet the collaboration of the mobile nodes is better than SID, so the decrease ratio is lower than SID. The initial delivery ratio of SaWdelfish is lower than the other schemes as the mobile node rejects to transmit the data message that does not satisfy its convenience and also have a decrease in delivery ratio with the increase of malicious participants (Figure 9).

Delivery ratio varies with the ratio of malicious participants.
The data dissemination scheme of SID is like the schemes of PROPHET [37], while RIDD is adopt the LOPSI schemes. In the proposed system, LOPSI and Spray and Wait outperform the PROPHET on delivery ratio, which have been evaluated in [33]. Therefore, the average delivery of RIDD and SaWcooperative is higher than SID.
4.4.4. Evaluation of Average Lantency
Figures 10 and 11 illustrate the average latency trend by varying such network parameters as queue size and TTL.
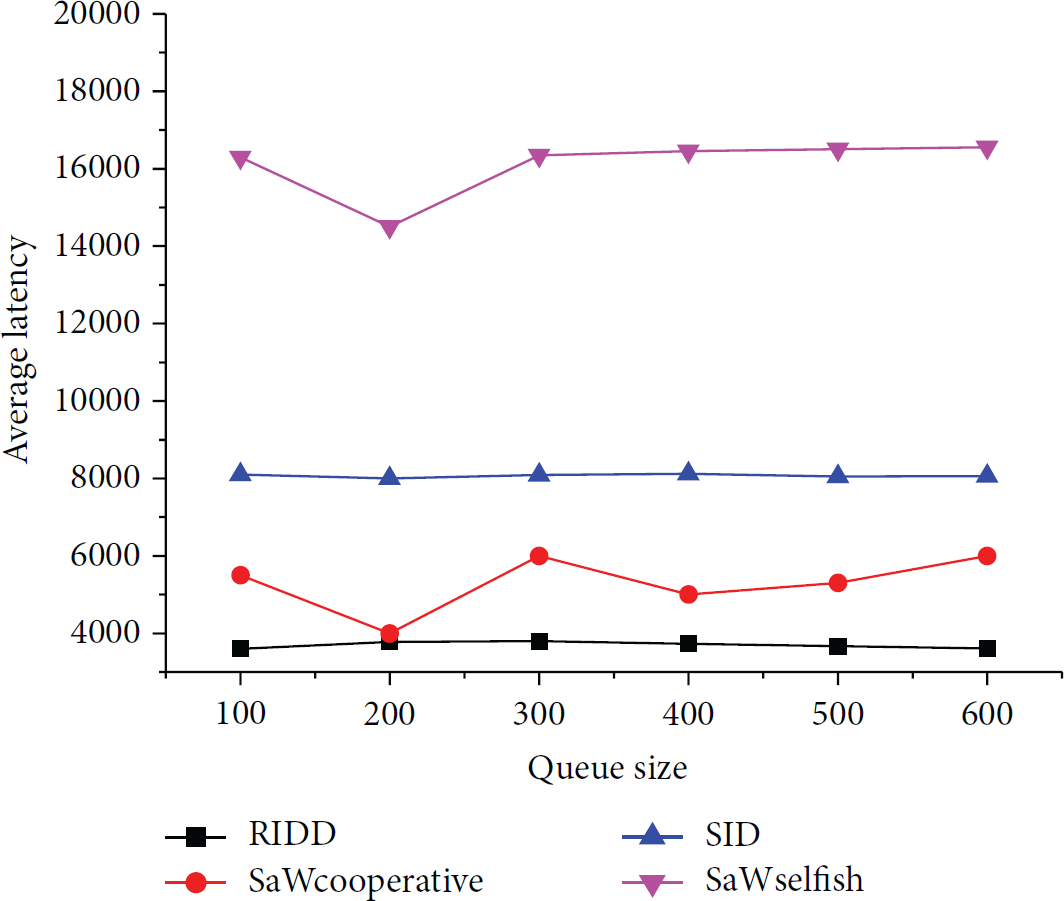
Average latency trend with increasing queue size.
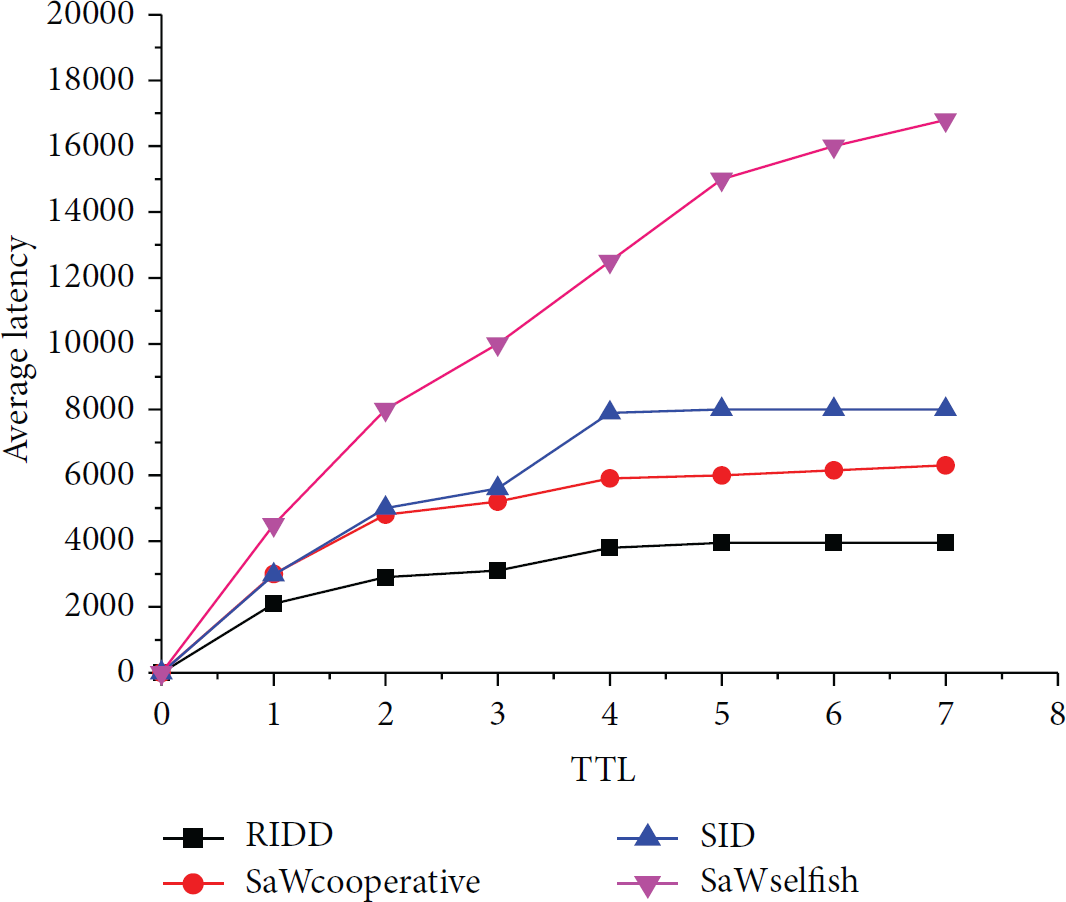
Average latency trend with increasing TTL.
With the increase of the queue size, the average latency also increases. At the initial stage a larger queue decreases the delay in SaWCooperative since it can carry more data messages. However, it simultaneously increases the chance for the data to meet their receivers. A larger queue also means data messages even with a low delivery probability. As for SaWselfish, it decreases the average latency as a large queue size increases its own resources. However, when such packets get delivered, they have already experienced long delay, thus increasing the average network delay. Therefore, the average latency increases. On the other hand, the increase of the queue size affects the performance of RIDD and SID only marginally, since RIDD is incentive to forward data for others by the system rewards and SID exchanges the packets based on its self-interest and aims to maximize its rewards. They do not aggressively utilize the increased queue size.
With a longer TTL, all schemes can deliver more packets to the destinations, until the communication capacity of the network becomes the bottleneck and dominates the network performance. As shown in Figure 11, we notice that the average delay of RIDD, SaWCooperative, and SID tends to become stable after TTL increases to 4 hours, while the delay of SaWselfish continues to increase with longer TTL. It means that in RIDD, SaWcooperative, and SID schemes most packets can be delivered within 4 hours, while SaWSelfish needs to keep data messages staying longer in the nodal buffer.
4.4.5. Evaluation of Transmission Cost
Figures 12 and 13 illustrate the transmission cost trend by varying such network parameters as queue size and TTL.

Transmission cost varying under increasing queue size.

Transmission cost under the varying TTL.
As shown in Figure 12, SaWcooperative gains significantly, because a longer queue allows a node to hold more data packets for a longer time. However, a longer queue results in a surge of transmission cost, because more duplication can be held and transmitted by the mobile nodes. The increase of the queue size affects the performance of RIDD and SID only marginally, since RIDD and SID exchange the messages based on the incentives schemes provided by the system.
As Figure 13 shows, the transmission cost increases with the increase of TTL. This is because extending TTL allows packets to stay longer in the network, which thus has a better chance to be exchanged and duplicated, yielding more overhead. While the transmission cost trend of RIDD stabilizes from 1 hour, since the data message can be delivered to the receiver with a relative high efficiency. The long TTL affects marginally the performance of RIDD.
5. Conclusion and Future Work
In this paper, we designed reputation-based incentives for data dissemination which can be used for motivating participants to deliver reliable data messages in mobile participatory sensing networks. We also address the problem of retaining a desired number of active reputable participants to provide adequate level of service quality with low incentive cost. We presented a set of simulations and highlight the properties of RIDD. The results show that RIDD remarkably increases the winning probability of participants who provide accurate data, preserves the data security in the dissemination process, and performs well in evaluation of the transmission metrics. In future work, we plan to design an adaptive technique for finding optimal schemes to keep the balance of the participant rewards and the incentive cost.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work is supported by the National Science Foundation for Distinguished Young Scholars of China under Grant nos. 61225012 and. 71325002, the Specialized Research Fund of the Doctoral Program of Higher Education for the Priority Development Areas under Grant no. 20120042130003, China MOE and China Mobile Joint Research Foundation under Grant no. MCM20130391, Liaoning BaiQianWan Talents Program under Grant no. 2013921068, and National Natural Science Foundation of China under Grant no. 61402097.