Abstract
Aiming at allocating more licensed spectrum to wireless sensor nodes (SNs) under the constraint of the information security requirement of the primary system, in this paper, we propose a cooperative relaying and jamming secure transmission (CRJS) scheme in which SNs will relay primary message and jam primary eavesdrop concurrently with SN's downlink and uplink information transmission in cognitive radio sensor networks (CRSNs). In our proposed CRJS scheme, SNs take advantages of physical layer secure technologies to protect the primary transmission and acquire some interference-free licensed spectrum as a reward. In addition, both decode-and-forward (DF) and amplify-and-forward (AF) relaying protocols are investigated in our proposed CRJS scheme. Our object is to maximize the transmission rate of SNs by optimal allocating of the relaying power, jamming power, and downlink and uplink transmit power under the target secure transmission rate requirement of the primary system. Moreover, two suboptimal algorithms are proposed to deal with these optimization problems. Furthermore, we analyze the transmission rate of SNs and allocate the relaying power, jamming power, and downlink and uplink transmit power for the asymptotic scenarios. Simulation results demonstrate the performance superiority of our developed strategy over conventional jamming scheme in terms of the transmission rate of WSN.
1. Introduction
Rapid proliferation of wireless communication devices and technologies burdens the available wireless spectrum resource and exacerbates the spectrum shortage problem. However, current fixed spectrum allocation strategy utilizes the spectrum resource with low efficiency according to the US FCC report [1] due to the neglect of vast temporal and spatial variations in the usage of allocated spectrum. Dynamic spectrum access as the main technology of cognitive radio (CR) can exploit the instantaneous availability spectrum by allowing the unlicensed users (secondary users) to access the licensed spectrum [2–5]. In cognitive radio networks (CRNs), secondary users (SUs) access the vacant licensed spectrum by sensing the surrounding spectrum environment or concurrently transmit with licensed users (primary user) under the requirement of interference constraint [6]. In addition, SUs can also cooperate with primary users (PUs) to assist the primary transmission and acquire some licensed spectrum opportunities as a reward [7].
Employing low-cost, lower-power, and low-data-rate wireless SNs in wide application areas such as military affairs, environment [8], health [9], home [10], and other commercial areas [11], wireless sensor network (WSN) has been identified as an important technology for future intelligent world. In WSNs, SNs collect sensing data and deliver it to the access node or sink node to make a global decision. However, thousands of sophisticated, overlap, and coexisted WSNs crowd the license-exempt industrial, scientific, and medical (ISM) bands which are utilized by the existing WSNs. In addition, SNs will be interfered by many other communication systems which also occupy the ISM bands such as Wi-Fi, ZigBee, and Bluetooth [12]. Therefore, WSNs face the challenge of wireless spectrum shortage problem.
Equipping SNs with cognitive ability to form a new communication paradigm denoted as CRSN is an effective method to overcome the lack of wireless spectrum resource in WSNs which can take advantages of dynamic spectrum access technology in CRNs. Recently, many works have investigated the performance of CRSN in [13–17]. Reference [13] introduced the system architecture, the application areas, the spectrum sharing method, the communication diagram, and the open research areas of CRSN. Reference [14] investigated the design issues and further extensions of CRSN. To support delay-sensitive and high-bandwidth multimedia applications in CRSN, [15] proposed a spectrum-aware clustering routing protocol with limited clusters. In addition, an energy and spectrum awareness cluster-head selection method was designed to utilize the noncontiguous available spectrum bands and support continuous transmission application. For real-time application, [16] introduced two types of channel switching methods which were periodic switching method and triggered switching method to transmit periodically generated packets and random generated packets, respectively. An energy-efficient channel management scheme was proposed with considering the constraint of SNs' lifetime in CRSN [16]. The optimal packet size of CRSN was determined in [17] under constraints of PUs' acceptable interference level and reliable event detection probability requirement at the sink. In [18], an adaptive power allocation method and sensing information correlation were utilized in the information theoretical capacity maximization frameworks.
SNs can sense the licensed spectrum or control their transmit power to access the licensed spectrum in CRSNs. However, due to the inevitable sensing errors and undetermined interference threshold, it is hard for PU to be not adversely affected by SNs in conventional spectrum sharing methods. Cooperative communication in cognitive radio networks (CRNs) can settle these problems by allowing SUs to cooperate with PUs to support their quality-of-service (QoS) requirement and acquire some spectrum opportunities as a return [19]. In [20], PUs would lease half of the frame in exchange for assistance from SUs. In addition, an optimal power allocation method and antenna weights were designed and closed-form expression of bit error rate was derived to evaluate the performance. Game theory was employed in [21] to model the cooperation between PUs and SUs. SUs would optimally adjust their action to acquire more spectrum opportunities with less energy wasting. Reference [22] proposed a schedule strategy to improve the performance of PUs and guarantee the spectrum benefit of SUs in immediate or long-term bases. Automatic repeat-request (ARQ) signals were utilized by SUs to determine whether to cooperate or to access of SUs in [23]. Full-duplex cooperation scheme was proposed in [24] where the achievable primary-secondary benefit region was studied and SUs' transmission rate maximum problem was solved. Two-path successive relaying cooperative spectrum sharing scheme was proposed in [25] where two secondary transmitters alternately relay PUs' message. In addition, superposition coding and successive interference cancelation technologies were adopted at each SU to increase the primary transmission rate. Therefore, cooperative communication is a promising technology which can benefit both PUs and SUs. In this paper, we can employ the cooperation between SNs and PUs in CRSN to efficiently utilize the licensed spectrum without adverse effect on PUs.
Cooperation between SNs and PUs can support PUs' QoS requirement and allocate some spectrum opportunities for SNs in CRSNs. However, for some PUs with malicious eavesdropping challenge, they need new cooperation diagram. Traditional cryptographic method which assumes that eavesdroppers have limited computing ability is becoming easy to be attacked due to the rapid development of computing hardware. Physical layer secure methods which take advantages of the physical layer characteristics to confirm secure communication are widely investigated recently [26]. Cooperative relaying and cooperative jamming are two commonly physical layer secrecy methods [27]. Reference [28] investigated the optimal relays selection method in CRN for secure communication in which one selected relay for secure information transmission and other relays for jamming signal transmission. Reference [29] considered the secure transmission for OFDM based CRN with relay assisted under uncertain channel state information (CSI) condition. The worst case robust formulation was utilized to optimally allocate the power and subcarriers. Secure relay and jammer selection method for multiple eavesdroppers scenario was studied in [30] where closed-form expression of secrecy outage probability was derived. Hybrid relaying and jamming scheme was proposed in [31] where an optimal cooperative node was selected as relay and the other cooperative nodes would transmit jamming signal in beamforming way. Reference [32] derived the optimal beamforming vectors for relay signal and jamming signal under the constraints of maximum signal-to-interference and noise ratios (SINR) at eavesdroppers and minimum SINR at the destination requirements. Reference [33] investigated the destination assisted jamming scheme to protect the information from eavesdropper. Inspired by the above works, for the primary secure transmission requirement in CRSN, SNs can also provide cooperative relaying and jamming to protect the primary transmission and acquire some interference-free licensed spectrum as a reward. To the best of our knowledge, this is the first work which studies the cooperation between SNs and PUs under the secure requirement of the primary system.
In this paper, we propose a CRJS scheme to maximize the transmission rate of SNs and protect the primary transmission through physical layer secure methods of cooperative relaying and jamming. In our proposed CRJS scheme, SNs will relay primary message and jam primary eavesdropper during SNs' downlink and uplink transmission stages concurrently the transmission of WSN. Specifically, our cooperation scheme is implemented into two slots. During the first slot, SNs transmit their downlink message and jamming signal concurrently with the primary information transmission. During the second slot, SNs will decode the downlink message and forward the primary message. In addition, SNs still transmit the same jamming signal concurrently with their uplink transmission. Both decode-and-forward (DF) and amplify-and-forward (AF) relaying protocols are investigated in our proposed CRJS scheme. Our object is to maximize the transmission rate of SNs by optimal allocating of the relaying power, jamming power, and downlink and uplink transmit power under the target secure transmission rate requirement of the primary system. Moreover, two suboptimal algorithms are proposed to deal with these optimization problems. Furthermore, we analyze the transmission rate of SNs and allocate the relaying power, jamming power, and downlink and uplink transmit power for asymptotic scenarios. Simulation results demonstrate the performance superiority of our developed strategy over conventional jamming scheme in terms of the transmission rate of WSN. The main contributions of this work are summarized as follows:
We propose a cooperative relaying and jamming scheme to maximize the transmission rate of SNs under primary target secure transmission rate requirement in CRSN. Our scheme will provide more licensed spectrum for SNs by employing their downlink and uplink transmission opportunities. In addition, our scheme takes advantages of physical layer characteristics to protect primary transmission. Both PUs and SNs can be benefited from this scheme. Both AF and DF relaying protocols are investigated in our scheme. For AF relaying protocol, both primary and jamming signals will be amplified and forwarded. For DF relaying protocol, the primary message will be decoded and forwarded. In addition, the same jamming signal will be transmitted to interference the primary eavesdropper. We formulate our optimization problems to maximize SN's transmission rate under primary target secure transmission rate requirement. Two sequential parametric convex approximation (SPCA) based algorithms are proposed to solve these problems and allocate the relaying power, jamming power, and downlink and uplink transmit power. For asymptotic scenarios, we also analyze SNs' transmission rate and primary secure transmission rate. Meanwhile, we also formulate our optimization problems to maximize SNs' transmission rate and allocate the relaying power, jamming power, and downlink and uplink transmit power.
The rest of this paper is organized as follows. Section 2 describes the system model and interpret the information exchange for DF and AF strategies. Section 3 interprets our cooperation scheme and formulates the optimization problems for DF and AF strategies. In addition, suboptimal algorithms are proposed to solve these problems and allocate the transmit power. In Section 4, we analyze the asymptotic scenarios. The authors conduct extensive simulations in Section 5, and Section 6 concludes the paper.
Notations. Boldface letters denote
2. System Model
In our CRSN, a WSN coexists with a primary system which is shown in Figure 1. The WSN with no licensed spectrum consists of SN and an access node (AN). Both SN and AN are willing to exchange information which can capture the wireless communication scenario where SN transmits its sensing date to AN for making a decision and then AN guides SN to make appropriate action. The primary system consists of a primary transmit (PT) and a primary receiver (PR). Due to the large-scale fading or serious interference, the direct transmission link between PT and PR always experiences outage [19, 34]. In addition, there is an external malicious eavesdropper (EV) who tries to eavesdrop the primary message. Therefore, the primary system needs the cooperation of SN and AN to confirm its secure communication and reward SN and AN with some interference-free licensed spectrum opportunities to inspire motivation of cooperation.

The system model diagram of our proposed scheme. We consider the scenario for cognitive radio sensor networks where two SNs with downlink and uplink information exchange requirement coexisted with the primary system.
We assume that AN has M antennas and all other nodes have only one antenna. The primary network synchronizes with WSN and both networks experience stationary, ergodic, independent, and block Rayleigh fading; that is, channel gains are invariant within a frame but independently vary from one frame to another [35, 36]. In our system, each frame is equally divided into two slots which correspond to the downlink and uplink transmission stages of AN and SN, respectively. The channel variables of
Our proposed cooperation scheme is implemented into two slots. During the first slot, AN transmits downlink signal and jamming signal concurrently with the transmission of primary signal. Then the receiver signals at SN are
During the second slot, SN will relay the primary message to PR and jam EV with the artificial noise. Therefore, we will interpret the information exchanging in both AF and DF relaying protocols in this slot.
2.1. AF Relaying Protocol
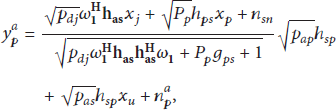
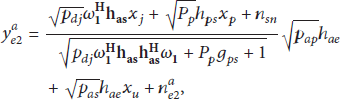
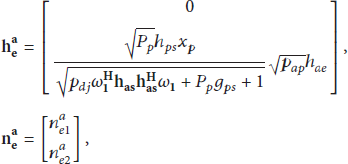
When SN adopts the AF relaying protocol, SN will decode and cancel the downlink message firstly. Then SN amplifies and forwards the remaining signals concurrently with the transmission of uplink signal. The received signals at AN are
2.2. DF Relaying Protocol
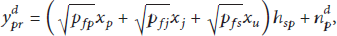
When SN adopts the DF relaying protocol, SN will decode the downlink message and primary message with the method of successive interference cancellation. Then, SN will forward PUs' signal concurrently with the uplink signal and jamming signal. In this paper, we assume that the uplink jamming signal is the same with the uplink jamming signal. AN and SN can share the same jamming signal though signal encryption method. Then, the received signals at AN are
During the signals exchanging process, the allocation of relaying power, jamming power, and downlink and uplink transmit power will affect the primary information security and the transmission rate of WSN. Then, in the next section, we will try to maximize the transmission rate of WSN under the constraint of PUs' security requirement by optimal allocating of the relaying power, jamming power, and downlink and uplink transmit power in AF and DF relaying protocols, respectively.
3. CRJS Scheme
In this section, we will interpret our proposed CRJS scheme in both AF and DF relaying protocols. Then, the optimization problems will be formulated to maximize the transmission rate of WSN under the security requirement of the primary system. In addition, SPCA based algorithms are formulated to solve these problems and allocate the relaying power, jamming power, and the downlink and uplink transmit power.
3.1. Problem Formulation
During the first slot, the downlink transmission rate at SN is
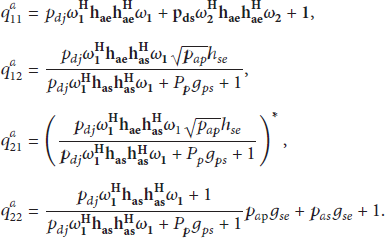
3.1.1. AF Relaying Protocol
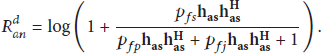
When SN utilizes AF relaying protocol, AN firstly cancels the jamming signal and acquires the uplink transmission rate as
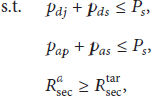
Then our optimization problem can be formulated as
3.1.2. DF Relaying Protocol
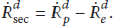
When SN employs the DF relaying protocol to forward the primary message concurrently with the uplink message and jamming signal, SN will cancel the jamming signal firstly and decode the primary message with achieved rate as
Then the secrecy rate of the primary system is
To maximize the transmission rate of SN, we formulate the optimaizaition problem as
3.2. Power Allocation Strategy
In this section, we will try to solve the optimization problems
3.2.1. AF Relaying Protocol
For problem
Set
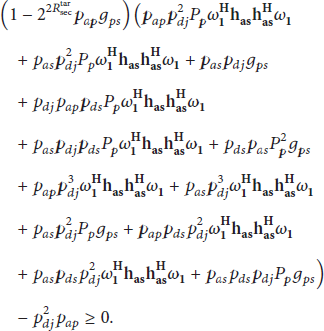
Proposition 1.
The nonconvex polynomial item
Proof.
Based on the SPCA method in [37],
Utilizing Proposition 1, P4 can be transformed into convex problem which will be solved by the conventional convex algorithm. Then, our proposed SPCA based iterative algorithm can be summarized as in Algorithm 1.
(1) Set (2) (3) Transform P4 into convex problem and solve it through Lagrange dual method. Then acquire the optimal power (4) Update (5) Update (6)
Therefore, we acquire the suboptimal relaying power, jamming power, and downlink and uplink power for AF relaying protocol.
3.2.2. DF Relaying Protocol
Similar to the AF relaying protocol, we solve the nonconvex problem P2 by transforming its nonconvex items into convex items. Set
Similarly, the last two constraints of P2 can be rewritten as
Then, the optimization problem of P2 can be written as
Utilizing Proposition 1 and constructing
(1) Set (2) (3) Transform P4 into convex problem and solve it through Lagrange dual method. Then acquire the optimal power (4) Update (5) Update (6)
Therefore, we acquire the suboptimal relaying power, jamming power, and downlink and uplink power for AF relaying protocol.
4. Asymptotic Analysis
In this section, we will analyze the asymptotic performance of our proposed scheme and allocate the relaying power, jamming power, and the downlink and uplink transmit power.
4.1. High SINR Regime with
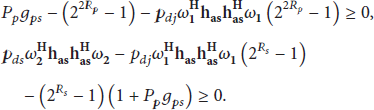
For the high SINR regime with
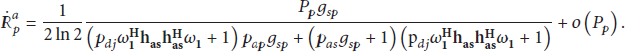
4.1.1. AF Relaying Protocol
When
4.1.2. DF Relaying Protocol
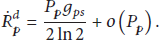
When
For this problem, we transform the nonconvex items into convex items and the optimization problem can be written as
Then, we can adopt Algorithm 2 to solve it and acquire the jamming power, relaying power, and uplink and downlink power.
4.2. Low SINR Regime with
When
4.2.1. AF Relaying Protocol
When
As
Then the optimization problem can be formulated as
For this problem, we can also adopt Algorithm 1 to solve it.
4.2.2. DF Relaying Protocol
For the DF relaying protocol with
5. Simulation Results
In this section, we will investigate the performance of our proposed scheme with empirical parameters. The communication scenario is demonstrated in Section 2. In our simulation, we assume that AN has four antennas and all other nodes have only one antenna. AN and SN locate in the middle between PT and PR. All channels experience large scale and small scale fading. The path loss parameter is set to 3. We will evaluate the transmission rate of WSN under the constraint of primary security requirement with Monte Carlo experiments. In addition, we will evaluate the cooperative jamming scheme (CJS) in [33] for comparison. For CJS, PT transmits its message during the first slot and SN cooperates with PT during the second slot. In addition, SN will transmit its signal only during the second slot.
In Figure 2, we simulate the transmission rate of our proposed scheme, underlay scheme, and the CJS scheme. In addition, we also investigate effect of the downlink decoding failure to the transmission rate and we denoted these schemes as DF-Uplink and AF-Uplink. In this figure, we can figure out that the performance of the our proposed scheme outperforms the comparison schemes. High

The transmission rate of WSN (
In Figure 3, we simulate the transmission rate of WSN versus the primary transmit power

The transmission rate of WSN under low SNR regime with different target secure rate requirements (
In Figure 4, we simulate the transmission rate of WSN versus the transmit power
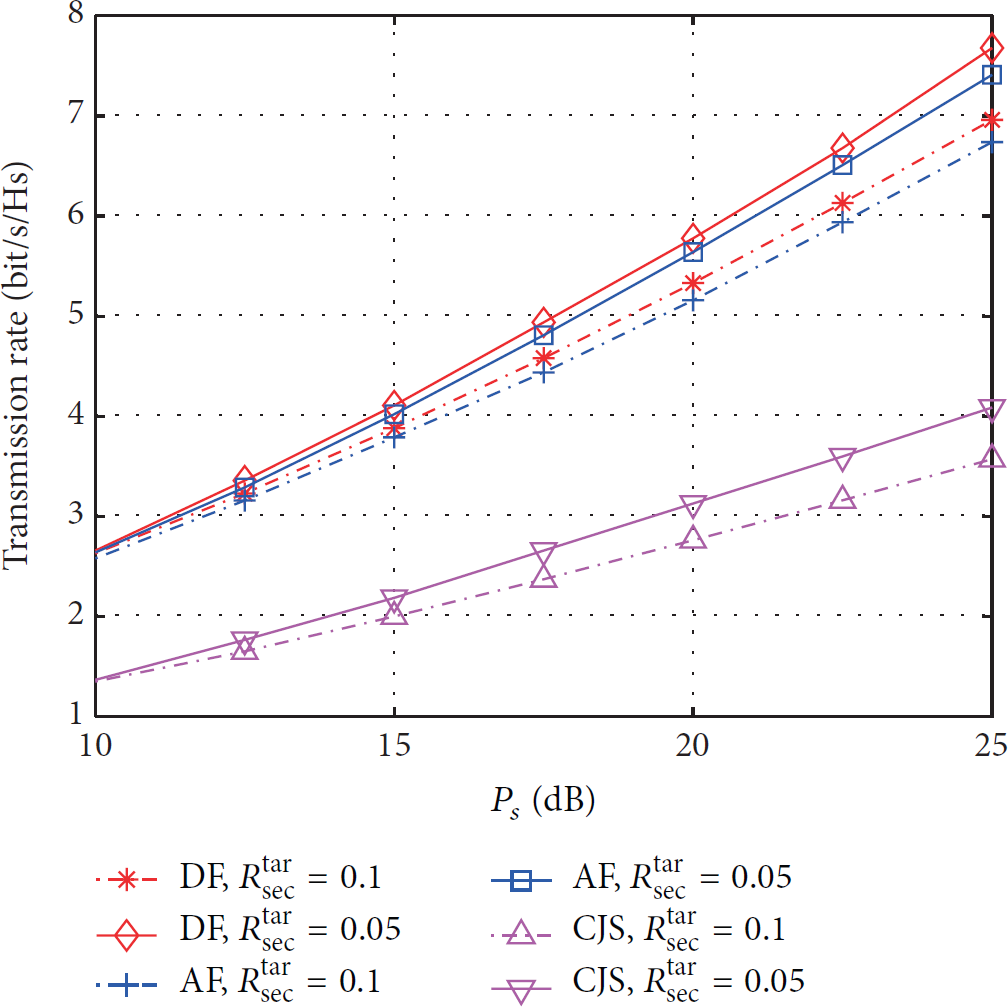
The transmission rate of WSN under high SNR regime with different target secure rate requirements (
In Figure 5, we show the transmission rate of WSN versus the transmit power of WSN under different primary target secure transmission rate requirements. Similarly, high

The transmission rate of WSN as a function of
In Figure 6, we show the transmission rate of WSN versus the distance between PT and SN under different primary target secure rate requirements. We assume that the distance between PT and PR is unit and SN will move in the line between PT and PR. When SN nears PT, there will be more power allocated for primary secure transmission during the relaying process. In addition, downlink transmission will experience strong interference from PT; therefore, the transmission rate of WSN increases slowly. When SN nears PR, the received SINR of the primary signal at SN is low. Therefore, the primary transmission will experience more outages which will waste more spectrum opportunities and the transmission of WSN increases slowly. Similarly, the DF relaying protocol still outperforms the AF relaying protocol due to the forwarding of noise. For CJS, the downlink transmission has not been considered in CJS which leads to the lower transmission rate compared with our proposed scheme.

The transmission rate of CRSN versus the distance between PT and SN under different primary target secure rate requirements (
In Figure 7, we show the transmission rate of WSN versus the distance between SN and EV under different primary target secure rate requirements. From this figure, we can figure out that when the distance between SN and EV is large, the transmission rate will increase. The reason is that when

The transmission rate of WSN versus the distance between SN and EV under different primary target secure rate requirements (
6. Conclusion
In this paper, we proposed a CRJS scheme in which SNs will relay primary message and jamming primary eavesdropper during SNs' downlink and uplink transmission stages to protect the primary message from eavesdropping and acquire some interference-free licensed spectrum opportunities. In addition, both DF and AF relaying protocols were investigated in our proposed CRJS scheme. We investigated the transmission rate maximization problems of SNs and proposed two SPCA based suboptimal algorithms to solve these problem and allocate the relaying power, jamming power, and downlink and uplink transmit power under the target secure transmission rate requirement of the primary system. Furthermore, we analyzed the transmission rate of SNs and allocate the relaying power, jamming power, and downlink and uplink transmit power for the asymptotic scenarios. Simulation results demonstrated the performance superiority of our developed strategy over conventional jamming scheme in terms of the transmission rate of WSN.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
The research work reported in this paper is supported by the National Natural Science Foundation of China under Grant no. 61431011 and the Fundamental Research Funds for the Central Universities.