Abstract
Evaluation of security risks in radio frequency identification (RFID) systems is a challenging problem in Internet of Things (IoT). This paper proposes an extended attack tree (EAT) model to identify RFID system's flaws and vulnerabilities. A corresponding formal description of the model is described which adds a probability SAND node together with the probability attribute of the node attack. In addition, we model the process of an RFID data privacy attack based on EAT, taking a sensitive information theft attack on an RFID tag as an example. To resolve the problem of assessing the risk probability of each node in EAT, we present the information feature entropy evaluation method for RFID privacy assessment. Finally, an evaluation is carried out to calculate the RFID privacy attack tree sequences and information feature entropy of the atomic node. Analysis shows that our scheme can calculate the overall risk evaluation result value for RFID privacy and comprehensively determine the risk of the weakest atomic node in RFID system.
1. Introduction
RFID is emerging as a promising technique in industry and academia with wide application in fields such as supply chain management, e-payment, environmental monitoring, smart labels, and detection. Thus, RFID is regarded as the foundation of Internet of Things. Unfortunately, it suffers from several drawbacks such as eavesdropping, relay attacks, unauthorized tag reading, and tag cloning attacks [1–3]. In particular, RFID privacy security risks are a concern as they can affect the RFID application [4, 5].
Risk management methods are composed of the following four relevant processes: risk evaluation, decision support, implementation control, and effectiveness assessment. The risk management process aims to reduce RFID system residual security risk to an acceptable degree so a review of RFID privacy risk evaluation technology is necessary.
The attack tree model [6, 7] is a feasible approach to depict behavioral characteristics of RFID privacy attacks. The complexity of constructing the model is reduced by dividing the attack procedure into several atomic attacks for system risk analysis, which are extensible and reusable. This model allows an administrator to identify system vulnerabilities, apply protective measures, and strengthen routine maintenance tasks.
However, the attack tree model has some limitations. It only portrays the attack procedure in a potential crisis but does not locate hidden risks, so it may not determine the protective measures that should be taken. Additionally, information feature entropy is a useful method to precisely decide the possibility of particular security vulnerability. This paper introduces information feature entropy to identify privacy risks based on the extended attack tree method.
The remainder of the paper is organized as follows. Section 2 introduces related work. In Section 3, we detail the extended attack tree model and give the formal description. In Section 4, we model the RFID privacy attack model based on EAT. Section 5 makes some evaluation and analysis on synthetic risks evaluation method of extended attack tree and information feature entropy. Section 6 concludes the paper.
2. Related Work
In order to determine system's flaws and identify the vulnerabilities with the highest risk, a security risk assessment should be undertaken. This enables the necessary safety measures to be identified and implemented, which can reduce the security risks of RFID systems to an acceptable degree. The current research on risk evaluations for RFID-based system can be classified into the following four methods.
The first model is the system security hierarchical evaluation model [8–10], which proposes an RFID system security assessment based on a fuzzy comprehensive method. This model divides the security levels into the object layer, criterion layer, and indicator layer. It then quantifies each factor and computes the evaluation results via fuzzy transformation rules. In addition, Lim et al. [11] created a multilevel attack model, which is used to check whether the system meets a series of RFID security attributes and computes the security level for each protocol.
The second evaluation model is based on traffic measurement [12] and utilizes a flow analysis method to identify RFID denial of service attacks. It extracts network attack features based on the collected data traffic, builds up an attack draft, and thereby enables RFID system security improvements to be made by revising RFID protocols.
The third model is based on indicator analysis [13], which determines security criteria and classifies these criteria into several subcriteria, with each one being represented by a quantized indicator. It then considers RFID security and privacy assessment through standard protocols and calculates the results by comparing the parameters of Electronic Product Code (EPC) standard, calculation costs, and data transfer rates.
The last evaluation model is based on the analysis of the working process [14] and applies the principle of queuing theory to determine the RFID attack efficacy. The issue of privacy in the RFID working process is considered individually for the tag, air interface, reader, network, and back-end parts. Privacy issues of RFID systems can be solved by dealing with individual privacy problems in each component.
Table 1 compares the four RFID system security evaluation models.
Comparison of the four RFID system security evaluation models.

In summary, for RFID privacy risk evaluation, it is necessary to establish an evaluation index system, to enable more scientific and rational assessment conclusions to be made. An improved model of RFID extended attack tree privacy risk evaluation is proposed which combines the advantages of the system security hierarchical evaluation model, indicator analysis evaluation model, and working process evaluation model, thus providing a method to identify RFID potential privacy risks. Furthermore, this method adopts information feature entropy to comprehensively identify the risk at the weakest atomic node, thus facilitating the development of appropriate security policies.
3. Extended Attack Tree Model
Definition 1 (EAT model).
The attack tree model was first proposed by Schneier [15] to enable analysis of the behavior of the system. It is mainly used in the form of a tree structure which represents the interdependence among attacks. Each node of the tree represents a subtarget attack: the root node represents the ultimate target, a node with no child is called an atomic node, and a node containing child nodes is called a subgoal node. There are two types of nodes in the traditional attack tree: “AND node” and “OR node.” In order to address the requirements of the RFID privacy attack model, our scheme proposes an extended attack tree model based on the traditional attack tree and includes three operational rules: “probability AND node,” “probability OR node,” and “probability SAND node.” Two additional properties are added: the attack probability and the attack time cost.
Definition 2 (“probability AND node” operational rule).
The target node

Probability AND node.
Definition 3 (“probability OR node” operational rule).
The alternative child node

Probability OR node.
Definition 4 (“probability SAND node” operational rule).
SAND stands for the operational rules for the “SAND,” which indicates a more accurate description of the relationship among aggressive behaviors. It obeys the accordance with the order to attack from the left child node
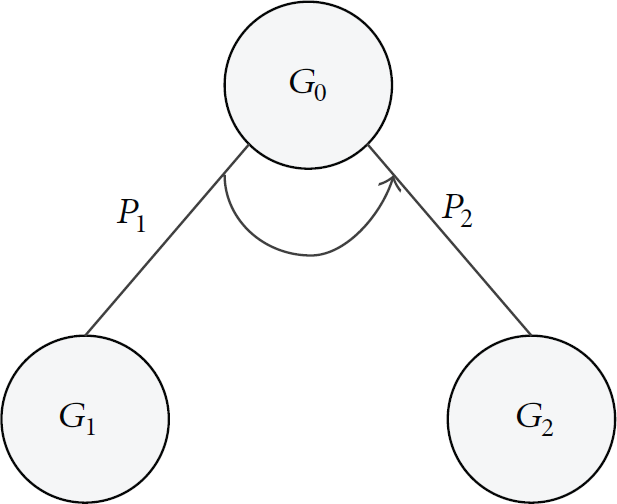
Probability SAND node.
Definition 5.
Formal description of extended attack tree is represented as
G represents a part of the nonempty finite set, in which an attacker needs to successfully break through before reaching the final attack goal. It consists of two types of nodes: the internal node (nonleaf node) and atomic node (leaf node). They may be represented as T refers to the time cost of a successful attack, which means the time required for In formula (3), the value δ is associated with safety performance of the system, which stands for the possibility of ρ refers to the successful attack representation used to calculate the probability. Based on the system risk vulnerability, it firstly determines the attack success probability 


The improved attack tree model adds the “probability SAND node” and, together with the other operational rules, can conduct a more accurate formal description of how RFID systems behave against sophisticated attacks. In addition, a probability attribute of an attack at each node is added, enabling the associated risk assessment algorithm to calculate the success rate of each different path that can be used to implement a successful attack. Hence, this model allows assessments of the safety performance of the system, so that appropriate maintenance measures can be used where required.
4. RFID Privacy Risk Evaluation Model Based on EAT
4.1. RFID Privacy Data Flows and Secure Risks
A typical RFID system considers the RFID tags as the main front-end part of the system and regards the RFID reader and database as the back-end. The RFID tag contains an ID microchip and antenna components, and the communication between tags and reader is via radio frequency electromagnetic coupling, as shown in Figure 4. Security issues relating to RFID systems depend largely on the type of tag used. Although RFID system privacy and security problems have been highlighted, up until now RFID security solutions have not been implemented. This paper attempts to establish an RFID privacy data attack model to objectively determine the vulnerability of an RFID system, thereby solving privacy issues of RFID systems.

RFID system working principle.
In this paper, we model the process of an RFID data privacy attack, taking RFID theft attack of sensitive information as an example. We assume that the reader and tag use a security protocol to ensure the safety of data transmission through wireless channels and that an attacker can monitor and analyze the entire communication process through the relevant attack techniques. The stages may be summarized as follows:
Determine if the tag is in active or passive mode. To conserve power supply, RFID tags have three working modes: passive, semipassive, and active modes. Tags in active mode surpass the passive mode in reading distance, stability, speed, and so on, which helps the attacker to determine the characteristics of the RFID system, as a different method of attack may be adopted depending on the type of tag. Scan system working frequency. The working frequency of RFID systems can be divided into low frequency (125 KHz~135 KHz), high frequency (13.56 MHz), ultra high frequency (UHF) (866~868 MHz, 902~928 MHz), microwave (2.45 GHz, 5.8 GHz), and other categories. Low frequency is more resistant to noise when the transmission distance is short; however, it requires a larger antenna size. Determination of the system's working frequency is a prerequisite for RFID invasions. Determine the tag communication distance. Depending on the communication distance, the tags are divided into four types: tightly coupled cards (reading range is less than 1 cm), near field coupled cards (reading range is less than 15 cm), sparse coupled cards (reading range is about one meter), and remote cards (reading range is from one meter to 10 meters or beyond) [16]. As the communication distance increases, RFID data is exposed to greater potential threats, including data tampering, erroneous data insertion, and data copying. Analyze the tag working protocol. Tags at different frequencies use different protocols, with common standards such as ISO10536, ISO14443, ISO15603, and ISO18000. Determine the data exchange rules. In order to steal private RFID data, it is necessary to understand the composition of the data exchange including the key exchange principle, data encryption method, and the system operation mode. Estimate the time taken to implement an RFID privacy attack. Since the RFID reader time is limited, the quicker an attack can be performed, the higher the possibility of a successful attack.
Potential current threats in an RFID system include eavesdropping, relay attack, unauthorized tag reading, and tag cloning. Table 2 summarizes the various stages of RFID and potential threats. A range of potential threats that may occur at any working stage in the RFID system are described and are graded using five grades: grade 0 indicates no correlation and grade 4 indicates a strong correlation.
Relationship between the RFID stages and potential security threats.

4.2. Privacy Attack Model
Based on the extended attack tree, our scheme achieves efficient RFID privacy attacks model, by analyzing the aggressive behaviors that RFID tags could use in information theft. In this model, the root node represents the tag data leakage, while atomic node represents a possible attack or system feature that may be exploited by attackers. A variety of possible attacks primitives defined symbols and corresponding logical relationships are described in Box 1.
AND OR AND OR SAND AND OR SAND
As can be seen from Box 1, to achieve the goal of RFID information theft, four branches should be passed, with each branch having its own subbranches. The dependencies of each attack behavior may be clearly revealed in the extended attack tree, and RFID tag privacy theft EAT model is shown in Figure 5.

RFID tag privacy theft EAT model.
4.3. Formal Description for RFID Tag Privacy Theft EAT Model
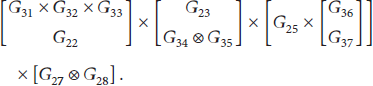
As for the RFID tag privacy theft EAT model, we give the formal description of G represents a part of the nonempty finite set. And a specific node is alternative atomic node or internal node. Take Figure 5, for example; E stands for an edge of the finite set; for example, T refers to the time cost of a successful attack. Normalized time cost of the atomic node is presented by formula (3). And the factor δ is to adjust the distribution of the time cost depending on the RFID system. θ is an internal node operational type set, used to calculate the attack sequence value according to Definitions 6 to 8. As for Figure 5, we may calculate the operation set as follows:
In addition, there are eight possible attack sequences to achieve the final target, which are listed as follows:
ρ refers to the successful attack representation used to calculate the probability. In Figure 5, it firstly considers the normalized value of the level of attack cost, level of technical difficulty, and level of attack discovered and then determines the possibility of the atomic node
4.4. Synthetic Risks Evaluation Method of Extended Attack Tree and Information Feature Entropy
4.4.1. Atomic Risk Value
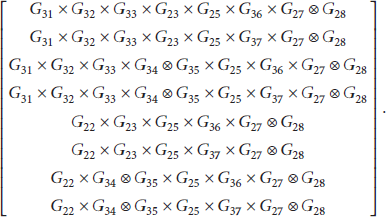
In the EAT model created for RFID privacy attacks, the overall rating of the privacy risk is mainly calculated by combining the individual atomic node risk values. Therefore, an objective and effective indicator of each atomic node's risk assessment value is required. Based on the multiattribute utility theory, we propose three attributes to describe aggressive behavior at each atomic node: level of attack cost, level of technical difficulty, and level of attack discovered, as shown in Table 3. The relevant formula is used to obtain the atomic risk value. In practical applications, we mainly consider the following guidelines, and atomic node normalized attributes are shown in Table 4.
Assessment grade of attack attributes.

Assessment grade possibility value of atomic node.
In order to balance the fairness among the indexes, the variation coefficient method is adopted to determine the weight of each index by using the characteristics of the sample data. As for the data set 
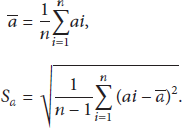
For the given set of evaluation indicators
Based on the coefficient of variation method, the weight of each indicator is defined as the following formula:

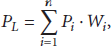
Combined with the RFID tag privacy theft of the EAT model shown in Figure 5, we get the risk of each atomic node in RFID privacy tag with the following formula:
4.4.2. Overall Risk Value
The attack sequence refers to a collection of atomic nodes in the attack tree. In order to reach the final target, the attacker needs to successfully attack all atomic nodes in the set. In the EAT model, the probabilities are not the same for the different types of internal nodes. The specific probability of attack for each collection of atomic nodes is calculated as follows.
Definition 6 (probability AND sequence value).
Assuming that a probability AND node contains m children nodes 
Definition 7 (probability OR sequence value).
As to a probability OR node with m children nodes 
Definition 8 (probability SAND sequence value).
When computing a probability SAND node with m children nodes 
4.4.3. Information Feature Entropy Evaluation
Entropy in an information system is considered as a characterization of the uncertainty of things. Assessments based on entropy are often adopted and can describe the information exchange intuitively. In order to resolve the problem of assessing the risk probability of each node in the EAT model with accuracy and provide a basis for a security engineer to assess the RFID privacy risk, we propose the information feature entropy evaluation method for RFID privacy assessment.
It calculates the entropy 
Then, it balances the link between different evaluation indicators with formula (14), so as to weigh the indicators at the same level. In the following formula, the value m represents the number of character indicators:
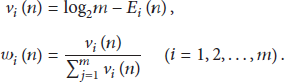
Finally, it calculates accurate information feature entropy evaluation for RFID privacy risk, which synthetically considers the entropy value, corresponding weight value, and attack time cost as well:
5. Evaluation and Analysis
5.1. Attack Tree Sequences
According to the EAT model described in Figure 5, we evaluate the RFID privacy risk possibility based on the formula mentioned in Section 4. Consider

As can be seen from formula (16), there are eight relevant sequences that may be used to reach the final goal, with the atomic node probability, probability of the secondary node, first level probability, and the probability of RFID privacy risk calculated in Table 5. For instance, the atomic node possibility in Table 5 is calculated via variation coefficient method with formulas (6) to (9), considering the four related parameters that are level of attack cost, level of technical difficulty, level of attack discovered, and time cost. And according to formulas (10) to (12), the probability AND operation in Table 5 is represented as “×,” the probability OR operation is expressed as “⊕,” and the probability SAND operation is expressed as “⊗.” When an attack occurs, the greater the possibility of the attack sequence, the greater the vulnerability to the system; thus measures should be taken to protect the RFID system at the identified nodes. As can be seen from Table 5,
Computing table of RFID risk possibility.

5.2. Information Feature Entropy of RFID Privacy
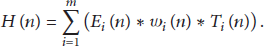
The EAT method exhibits strong performance in terms of measuring the overall RFID privacy risks and requires that all nodes must be involved in the calculation of risk probability. However, it lacks the ability to locate potential threats. To make it easier to understand the risk probability of each node, we propose calculation of the entropy of each node. Based on the information feature entropy method, Table 6 shows the calculating process of entropy values listed in Table 4.
Information feature entropy of the EAT node.

Figure 6 shows a more intuitive information feature entropy value of each atomic node in Table 6, in which we may find out that for each atomic node the risk of attack is not the same. As can be seen from Figure 6, the most vulnerable node
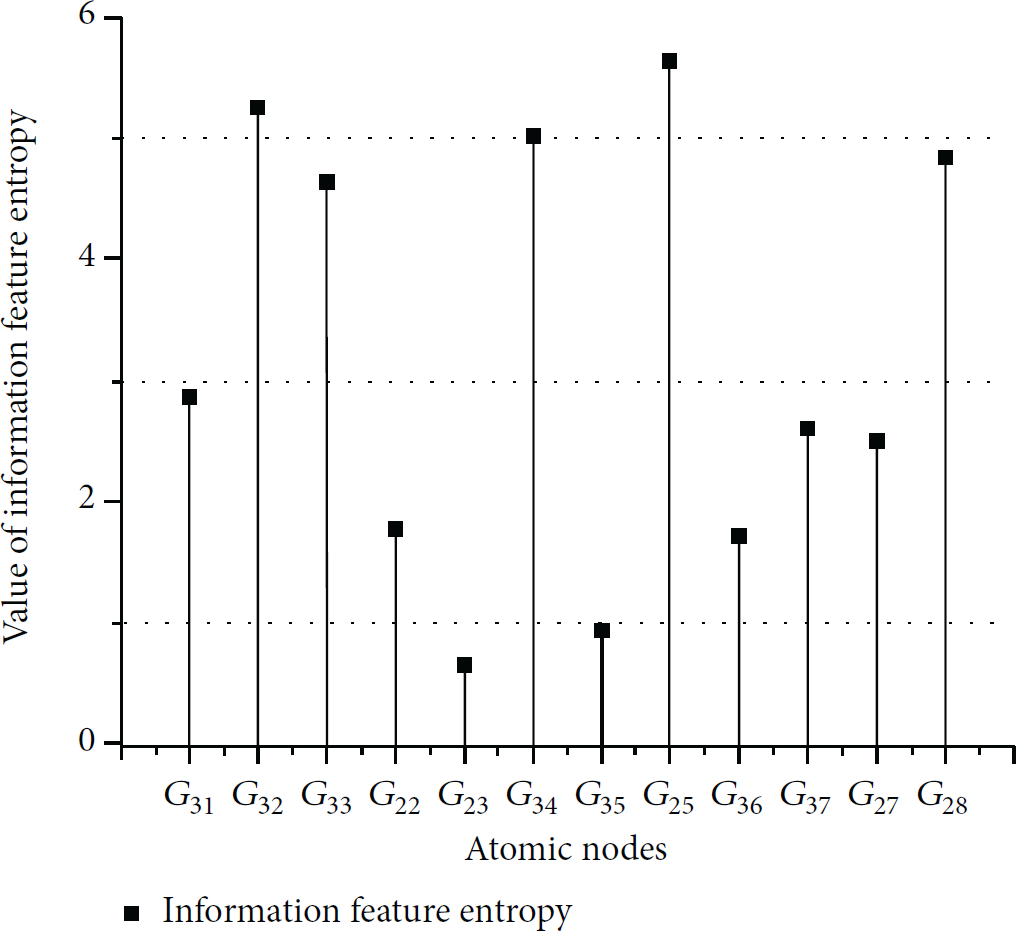
Information feature entropy value of each atom node.
6. Conclusion
On the basis of the traditional attack tree, we presented a secure and flexible extended attack tree model, in which we added a new logical operation and a new probability of success attribute. The RFID tag information theft example was taken, characteristics of the invasion were extracted, and an RFID privacy aggressive behavior EAT model was eventually established. This model applies multiattribute utility theory to calculate the risk value of all atomic nodes and thus computes the total risk value of the probability of successful attack sequences. Finally, it combines the advantages of information feature entropy to determine atomic node privacy risks and gives the relevant attack defense proposals.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
The subject is sponsored by the National Natural Science Foundation of China (no. 61170065, no. 61373017, and no. 61203217), the Natural Science Foundation of Jiangsu Province (no. BK20140886, no. BK20140888), Scientific & Technological Support Project of Jiangsu Province (no. BE2012183, no. BE2012755), Natural Science Key Fund for Colleges and Universities in Jiangsu Province (no. 12KJA520002), Jiangsu Planned Projects for Postdoctoral Research Funds (no. 1302090B, no. 1401005B), China Postdoctoral Science Foundation (no. 2014M551636, no. 2014M561696), and NUPTSF (no. NY214061, no. NY213034, and no. NY214060).
