Abstract
With the development of the wireless communication technologies, the wireless sensor networks (WSNs for short) are considered as one of the key research areas in healthcare systems. However, there is sometimes a need for removing bugs or adding new functionalities after WSNs are deployed. Wireless reprogramming is a process for propagating a new code image or relevant commands to sensor nodes in WSNs. In this paper, we propose a robust distributed reprogramming protocol of WSNs for healthcare systems, in which the security requirements are proved to be secure based on the elliptic curve discrete logarithm problem, such as existential unforgeability of signature for code image, authenticity of code image, freshness, and node compromised tolerance.
1. Introduction
Wireless sensor networks (WSNs for short) are spatially distributed sensors to gather physical or environmental information. The distributed sensors cooperate to pass their data through the network to a main location [1]. Recently, WSNs are considered as potential applications in providing high quality for healthcare services in recent years [2]. In healthcare applications, it may be necessary for removing bugs or adding new functionalities after WSNs are deployed. The reprogramming is an important operation function to propagate a new code image or relevant commands to sensor nodes in WSNs. However, an adversary may intercept or modify the transmitted messages in a WSN. Hence, it is critical to design a secure protocol for securely propagating a new code image or relevant commands to sensor nodes in WSNs.
In 2008, Das and Joshi [3] adopted orthogonality principle to design a protocol for dynamically updating sensor nodes in WSNs. A shared secret chosen by a base station has to be preinstalled on all sensor nodes before deploying them in a WSN, and the shared secret is used to validate a received advertisement message. After all sensor nodes accept a correct advertisement message, the sensor nodes dynamically update the shared secret. However, Zeng et al. [4] demonstrated that Das and Joshi's protocol is vulnerable to an impersonation attack. Assume that an adversary obtains the shared secret as he/she has compromised a sensor node. Then, the adversary can impersonate the base station to install his/her preferred program on sensor nodes by using the shared secret. Zeng et al. further proposed an improved scheme, but Wang et al. [5] pointed out that Zeng et al.'s proposed protocol [4] still suffers from an impersonation attack. In 2012, He et al. [6] showed that an adversary can impersonate a base station to install his/her preferred program on sensor nodes in a WSN, and further, the adversary can control the whole WSN. He et al. proposed two simple countermeasures which are formally validated by model checking. Soon afterwards, He et al. [7] proposed a secure and distributed reprogramming protocol (SDRP for short) based on an identity-based signature scheme in WSNs. In the SDRP, multiple authorized users are supported and each authorized user may have a different privilege for reprogramming sensor nodes. Subsequently, He et al. [8] and Yeo et al. [9] pointed out that there is a private key compromised problem in the SDRP, respectively. Furthermore, He et al. proposed an improved protocol based on Barreto et al.'s identity-based signature scheme [10]. In 2014, Shim [11] showed that He et al.'s improved protocol [8] is entirely broken and further proposed an improved protocol based on a pairing-free identity-based signature scheme. However, we find that Shim's proposed improved protocol is unworkable because the signature verification does not hold true. Among various secure protocols in WSNs [3–9, 11–24], most of the published reprogramming protocols [3, 6, 12–14, 16, 18, 20–23] are based on the centralized approach, which assumes the existence of a base station, and only the base station has the authority to reprogram sensor nodes. The centralized approach is not reliable in reality because of inefficiency, weak scalability, and vulnerability to potential attacks along the communication path [24].
Inspired from He et al.'s protocol [7], we adopt a short signature scheme to design a robust distributed reprogramming protocol of WNSs for healthcare applications. In the proposed protocol, each sensor node validates the received message by verifying the corresponding signature. The proposed protocol provides the following requirements.
Existential unforgeability of signature for code image: any adversary cannot successfully forge a signature for any code image by mounting chosen-message attacks. That is, only authorized users can construct valid reprogramming packets. Authenticity of code image: prior to the start of installation, a sensor node can verify the source of a code image. Freshness: prior to the start of installation, a sensor node can confirm that the to-be-installed program is the newest version. Node compromised tolerance: even though a sensor node is compromised, the compromised sensor node will not cause other uncompromised sensor nodes to violate authenticity of code image, integrity of code image, and freshness.
2. Overview of He et al.'s SDRP
In this section, we review the first proposed distributed reprogramming protocol (SDRP for short) proposed by He et al. [7]. The symbols used in the subsequent descriptions are listed as follows.
The Used Symbols and Descriptions
G: an additive group with an order q, where q is a large prime. P: a generator in G. q: a prime number. s: a master key for a sensor network owner.
He et al.'s SDRP includes System Initialization Phase, User Preprocessing Phase, and Sensor Node Verification Phase, and there are three kinds of roles: Sensor Network Owner (SNO for short), Authorized User (AU for short), and Sensor Node (SN for short). The detailed descriptions of each phase are given in the following.
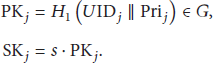
System Initialization. In this phase, a sensor network owner SNO first generates his/her own private/public key pair s/ Choose an additive group G and a multiplicative group Generate a generator P for G. Choose a bilinear mapping function Randomly choose a master key Compute the corresponding public key Choose two secure one-way hash functions Load the system parameters Assign the privilege Generate the corresponding private/public key pair Send
User Preprocessing. Suppose that an AU Partition the code image into l pages with the fixed size. Split the page i into n packets with the fixed sized, where Compute the hashing value for each packet, where the hash value for each packet in the page i is appended to the corresponding packet in the page Use the Merkle hash tree [25] for authenticating the hash values for the packets in page 1. The packets related to the Merkle hash tree are referred to in page 0. Suppose that m represent the root of the Merkle hash tree and the metadata about the code image. Sign m to generate the signature Send
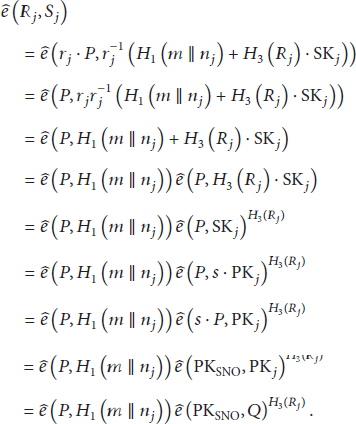
Sensor Node Verification. Upon receiving Verify the legality for the privilege Verify the signature by using SNO's public key:
If the above equality holds,
Security Analysis. According to He et al.'s [8] and Yeo et al.'s [9] analysis, He et al.'s SDRP [7] is vulnerable to a key compromise attack. Assume that
3. Our Proposed Reprogramming Protocol for Healthcare Systems
The basic idea for our proposed protocol is that maintenance staffs responsible for maintaining different healthcare applications have to register with the sensor owner. Upon the successful registration, a staff receives a smart card storing authorized private key. Then, the staff can construct secure reprogramming packets to WSNs, whenever demanded. In order to assure the validity for the packets, the sensor nodes in WSNs have to verify the signature for the packets.
Our reprogramming protocol also consists of three phases: System Initialization, User Preprocessing, and Sensor Node Verification. The descriptions for System Initialization Phase in our proposed protocol are almost the same as ones in He et al.'s SDRP [7], but an extra one-way hash function
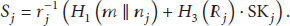
User Preprocessing. Assume that an AU Choose a random number Compute Generate the nonce Compute Send
Sensor Node Verification. Upon receiving Verify the legality for the privilege Verify the signature with the public key of the SNO and public system parameters:
where
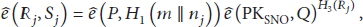
Correctness. According to the verification equation, each sensor node can verify if the signature
4. Security Analysis and Efficiency Comparison
Based on the elliptic curve discrete logarithm problem (ECDLP for short) [26, 27], the computation Diffie-Hellman problem (CDH for short) [28], the decisional Diffie-Hellman problem (DDH for short) [28], and the assumption of one-way hash function (OWHF for short) [29], we will analyze our reprogramming protocol and verify if it satisfies the security requirements: existential unforgeability of signature for code image, authenticity of code image, freshness, and node compromise tolerance. In addition, we will compare the computation costs in our proposed protocol with the ones in He et al.'s protocol [8]. The descriptions for the ECDLP, the CDH, the DDH, and the OWHF are as follows.
Definition 1 (elliptic curve discrete logarithm problem).
Let E be an elliptic curve defined over
Definition 2 (computation Diffie-Hellman problem).
Given
Definition 3 (decisional Diffie-Hellman problem).
Given
Definition 4 (one-way hash function).
Let H be a one-way hash function. The input for H is a message m with an arbitrary length, and the output for H is a hashing value
We give a formal definition for existential unforgeability of a signature for a code image under a chosen-message attack, which is based on the established notion of existential unforgeability against chosen-message attacks [30, 31]. The game between an adversary
Signature for code image: for requesting a signature the
Definition 5.
The proposed protocol is said to achieve existential unforgeability of signature for code image against chosen-message attacks if successful probability for any polynomially bounded adversary will be negligible in the above game.
Theorem 6.
The proposed protocol achieves existential unforgeability of signature for code image against chosen-message attacks in the random oracle model, assuming the hardness of the CDH problem.
Proof.
Assume that a polynomial-time algorithm
We will show how to construct a polynomial-time algorithm β that solves the CDH problem by using the
In the
In the Signature for code image: the
Let
Theorem 7.
The proposed protocol is said to achieve authenticity of code image if successful probability for any polynomially bounded adversary will be negligible.
Proof.
The source of a code image must be verified by a sensor node prior to the installation. Assume that an adversary attempts to construct reprogramming packets. Thus, a polynomial-time algorithm Given a SNO's public key Given a signature
According to the above analysis, the successful probability for the polynomial-time algorithm
Theorem 8.
The proposed protocol is said to achieve freshness if successful probability for any polynomially bounded adversary will be negligible.
Proof.
In the simulation, a polynomial-time algorithm
Theorem 9.
The proposed protocol is said to achieve node compromise tolerance if successful probability for any polynomially bounded adversary will be negligible.
Proof.
Upon compromising a sensor node, a polynomial-time algorithm
In 2012, Gouvêa et al. [32] present a software implementation for an elliptic curve cryptosystem and a pairing-based cryptosystem for the MSP430 microcontroller family, which is used in wireless sensor nodes. That is, it is practical for the pairing computation using wireless sensor nodes. Further, we do not consider the time for computing a hashing value. The descriptions of symbols for different operations are shown as follows.
The Symbols for Different Operations.
In the following, we will compare the computation costs in our proposed protocol with ones in He et al.'s protocol [8]. From Table 1, we can see that our proposed protocol is slightly outperformed and achieves additional security requirements, which is lack of in He et al.'s protocol [8].
Computation comparisons.

5. Conclusions
We propose a robust distributed reprogramming protocol providing existential unforgeability of signature for code image, authenticity of code image, freshness, and node compromised tolerance. The proposed protocol is applicable to healthcare systems, in which maintenance staffs responsible for maintaining different healthcare applications can construct secure reprogramming packets to WSNs, and the sensor nodes in WSNs can ensure the validity of the constructed packets. Considering the resource limitation of sensor node in WSNs, our future work is to design a lightweight distributed reprogramming protocol in WSNs.
Footnotes
Conflict of Interests
The author declares that there is no conflict of interests regarding the publication of this paper.
Acknowledgment
This work was supported in part by Taiwan Information Security Center (TWISC), Ministry of Science and Technology (MOST), under the grants 103-2221-E-146-005-MY2 and 103-2221-E-011-090-MY2.