Abstract
The IEEE 802.15.6 is a new standard on wireless body area network (WBAN) for short-range, extremely low power wireless communication with high data rates in the vicinity of, or inside, a human body. The standard defines two contention-based channel access schemes: slotted ALOHA and carrier sense multiple access with collision avoidance (CSMA/CA) using an alternative binary exponential backoff procedure. The standard supports quality of service (QoS) differentiation through user priorities and access phases. In this study, we develop an analytical model for the estimation of performance metrics such as energy consumption, normalized throughput, and mean frame service time, employing a Markov chain model under nonsaturated heterogeneous traffic scenarios including different access phases specified in the standard for different user priorities and access methods. We conclude that the deployment of exclusive access phase (EAP) is not necessary in a typical WBAN using CSMA/CA because it degrades the overall system throughput, consumes more energy per packet, and results in higher delay for nonemergency nodes.
1. Introduction
A WBAN is a logical set comprised of small and intelligent wireless medical sensors (which are worn or implanted into the tissues) and a common hub. These medical sensors are capable of measuring, processing, and forwarding important physiological parameters such as the heart rate, blood pressure, glucose level, body and skin temperature, oxygen saturation, and respiration rate, as well as records such as electrocardiograms and electromyograms. This enables health professionals to predict, diagnose, and react to adverse events earlier than ever. A conceptual view of medical WBAN is shown in Figure 1. The depicted WBAN includes a few sensors to monitor vital bodywide health information and send it to a remote server using a personal digital assistant (PDA) [1]. The IEEE 802.15 Working Group formed Task Group 6 (TG6) in November 2007 to develop a communication standard known as IEEE 802.15.6. The purpose of the group is to establish a communication standard optimized for low-power and short-range in-body/on-body nodes to serve a variety of medical, consumer electronics, and entertainment applications. WBANs must support a combination of reliability, quality of service (QoS), low power, high data rate, and noninterference to address the gamut of WBAN applications. The IEEE 802.15.6 standard was approved in 2012 for wireless communications in WBANs. The standard provides efficient communication solutions to ubiquitous healthcare and telemedicine systems, interactive gaming, military services, and portable audio/video systems.
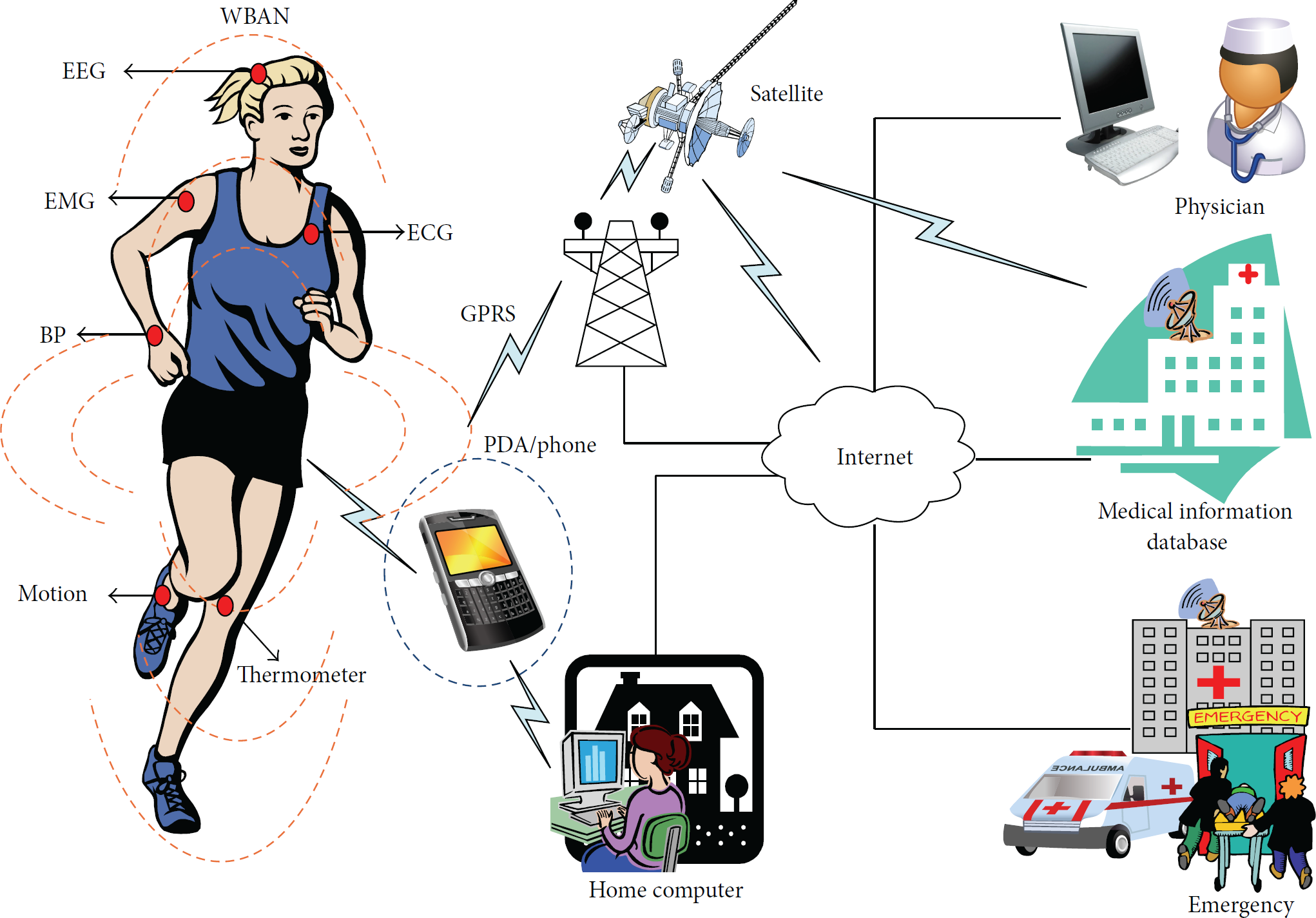
Abstract view of WBAN and its framework.
The medium access control (MAC) protocol provides a control mechanism to allow packet transmission through a shared wireless channel. The IEEE 802.15.6 supports two communication modes: (1) beacon communication mode, where the hub transmits beacons for resource allocation and synchronization, and (2) nonbeacon communication mode, where the scheduled/unscheduled allocations and polling are used [2]. In the beacon communication mode, the beacons are transmitted in the beginning of each superframe. As illustrated in Figure 2, in a beacon communication mode each superframe is divided into different access phases (APs). A superframe includes exclusive access phase 1 (EAP1), random access phase 1 (RAP1), management access phase 1 (MAP1), exclusive access phase 2 (EAP2), random access phase 2 (RAP2), management access phase 2 (MAP2), and an optional B2 frame followed by a contention access phase (CAP). The EAPs are used for life-critical traffic while the RAPs and CAP are used for regular traffic. Each AP, except RAP1, may have zero length [3].
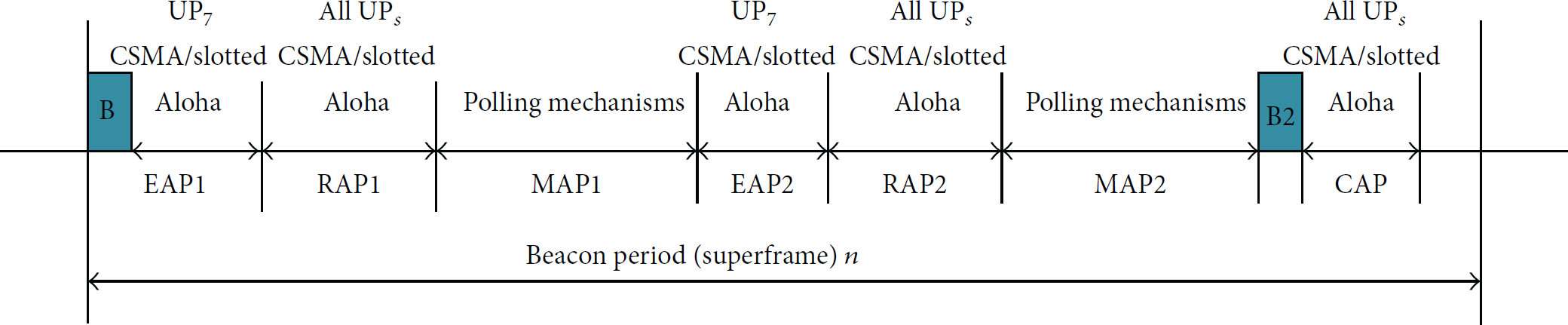
Layout of access phases with superframe boundaries [15].
In IEEE 802.15.6, the contention-based access methods for obtaining allocations are either carrier sense multiple access/collision avoidance (CSMA/CA) if a narrowband physical layer (PHY)/ultra-wideband (UWB) PHY is chosen or slotted ALOHA if UWB PHY is used [3]. The IEEE 802.15.6 CSMA/CA mechanism is different in important aspects from the CSMA/CA mechanism of other wireless standards. The backoff mechanism is not binary exponential, and the contention window doubles only when the retry counter is an even number. In addition to busy channel the node will also lock the backoff counter if it is not allowed to access the medium during the current AP or the current AP length is not long enough for a frame transmission. These differences require changes in the typical discrete time markov chains (DTMCs) adopted for the CSMA/CA mechanism of previous standards presented in [4–7] for IEEE 802.11; in [8–11] for IEEE 802.11e; in [12, 13] for IEEE 802.15.4; and in [14] for IEEE 802.15.3c.
To employ the CSMA/CA mechanism, as shown in Figure 4 the contending node i belonging to a user class
In this study, we develop analytical and simulation models to evaluate the CSMA/CA mechanism of IEEE 802.15.6 media access control (MAC), by considering a portion of the
The rest of this paper is structured as follows: Section 2 reviews the related studies available in the literature. Section 3 describes the framework of the analytical model and performance measures. The experimental results are presented in Section 4, and finally, Section 5 concludes our study.
2. Related Studies
Since the IEEE 802.15.6 standard has recently been released, there have been very few probabilistic works in the literature that analyze the CSMA/CA mechanism of the IEEE 802.15.6 standard. However, many researchers have analyzed the CSMA/CA protocol of various other communication standards in their articles. Performance analyses of the CSMA/CA mechanism for various IEEE wireless communication standards were presented in [4–7] for IEEE 802.11; in [8–11] for IEEE 802.11e; in [12, 13] for IEEE 802.15.4; and in [14] for IEEE 802.15.3c. Because the IEEE 802.15.6 CSMA/CA mechanism is different from the mechanisms of other wireless technologies, these analytical models are not appropriate for the IEEE 802.15.6 standard. In [16, 17], the authors study the performance of IEEE 802.15.6 CSMA/CA only under saturation conditions. The results indicate that the medium is accessed widely by the high-user-priority nodes, while the other nodes starve. In [18], the authors present numerical formulas to determine the theoretical throughput and delay limits of IEEE 802.15.6-based networks. They aim to optimize the packet size and to determine the upper bounds of IEEE 802.15.6 networks for different WBAN applications. They assume a collision-free network with no user priorities (UPs). The authors in [15] propose an analytical model to evaluate the performance of a contention-based IEEE 802.15.6 CSMA/CA mechanism under saturated conditions for heterogeneous WBAN scenarios. However, in most real-world IEEE 802.15.6 networks, the saturation assumption is not likely to hold, and the traffic is mostly nonsaturated. In [19] the authors study the normalized throughput performance of IEEE 802.15.6 slotted ALOHA protocol in nonsaturation conditions. In [20] the authors develop an analytical model for performance evaluation of the IEEE 802.15.6 standard under nonsaturation regime. They only calculated the mean response time of the data frames in the network. In [21] the authors develop a DTMC model for the analysis of reliability and throughput of an IEEE 802.15.6 CSMA/CA-based WBAN under saturation condition. A generalized three-dimensional Markov chain with backoff stage, backoff counter, and retransmission counter, as the stochastic parameters, is proposed in [22].
3. Performance Analysis
In order to analyze the CSMA/CA performance of the IEEE 802.15.6 MAC protocol, we introduce a DTMC model under nonsaturation modes, as shown in Figure 3. We adopt the same analytic model as presented in [23]. We consider Poisson packet arrival at the rate of λ packets/microsecond. We assume that a sensor node can have only one packet at a time so that if it has a packet to transmit, then no other packets are generated. Eight user priorities in the WBAN,
Contention window bounds for CSMA/CA.


DTMC model for the CSMA/CA behavior in nonsaturated traffic conditions.
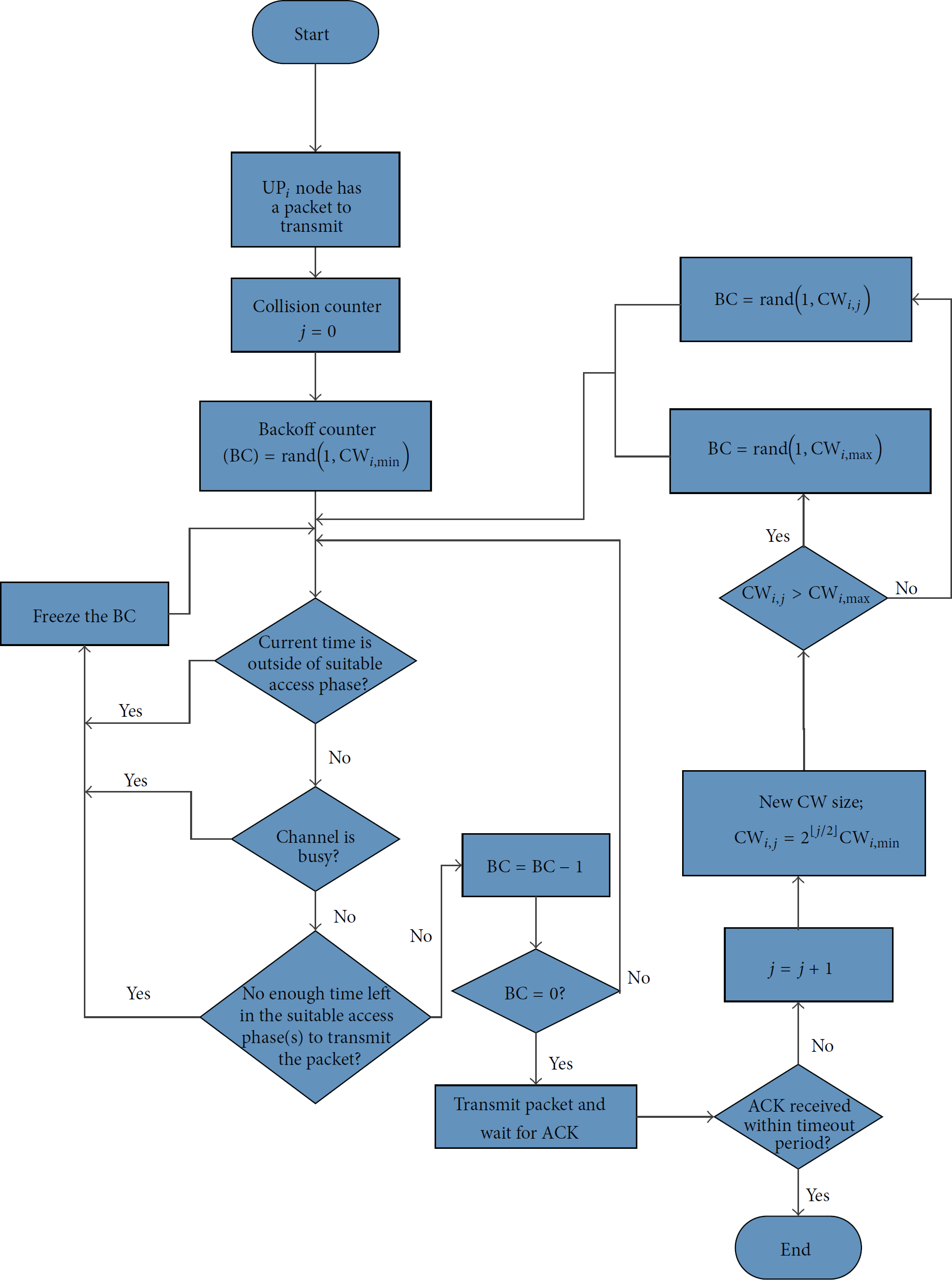
IEEE 802.15.6 CSMA/CA flowchart.
Let 
The collision probability for a class i node can be obtained as follows:

Let 
Let 
δ is the length of a pCSMAslot mentioned in the standard.
Let q be the probability that a packet is available to the MAC of a node in a given slot and let λ be the packet arrival rate. q is determined by


Let 
In a given pCSMA slot the backoff counter of a node should be locked till the beginning of the next eligible AP if there is no enough time for a packet transmission during the current AP. This probability is represented as
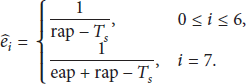
Therefore, for a 
The probability that a 
Let 
Thus, normalized system throughput can be obtained as

Let 
Energy is quite critical in WBANs, and therefore, in addition to the throughput and the mean frame service time, we are also interested in calculating the energy consumption. We estimate the energy consumption on a per-node per-packet basis. The expression for the mean frame service time 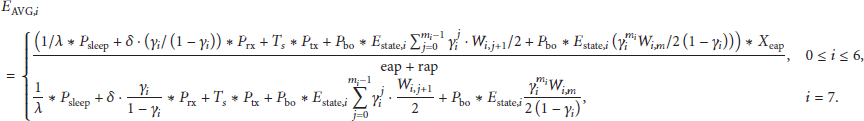
A sensor node deployed with a CSMA/CA mechanism needs to wait for a random backoff time before transmission. Let 
The first equation in (15) reflects the fact that, after each successful pCCAtime, the backoff counter is decremented. The second equation reflects the fact that, after a transmission, the nodes involved in the current transmission (at a state
For mathematical convenience, the abbreviated notations 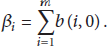
The stationary probability of being in the 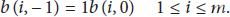
Therefore (1) can be written as
The stationary distributions 
Similarly, The stationary distribution 
The stationary distribution 
Similarly, sum of the remaining stationary distributions of the Markov chain is given by

To find the normalized equation,




Equations (2) and (26) represent a nonlinear coupled system with 16 unknown variables of
4. Results and Discussion
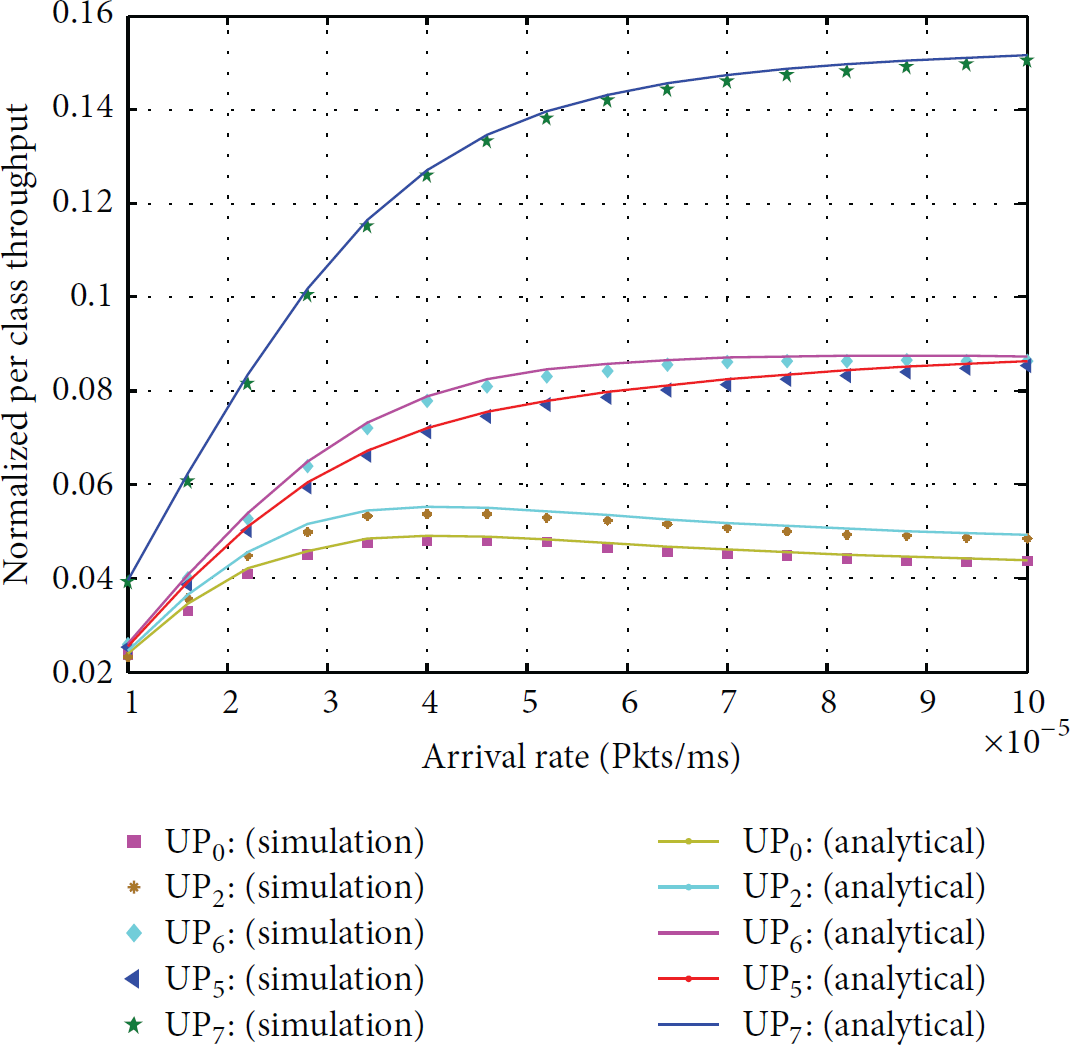
To validate the accuracy of the developed analytical model, we have compared its results with an event-driven custom-made simulation program written in the C++ programming language. The simulator closely follows the behavior of the CSMA/CA mechanism of the IEEE 802.15.6 standard. The simulations are performed for a WBAN with five user priorities by considering two nodes in each class and a hub. Here, we consider the CSMA/CA MAC mechanism running in the narrowband (NB) PHY, as described by the standard. The NB PHY operates in seven different frequency bands and offers a variable number of channels, bit rates, and modulation schemes. One of these seven frequency bands is used for an implantable WBAN, whereas the other six are used for a wearable WBAN. The focus of this analysis is on the seventh band (or the sixth band of a wearable WBAN) of the NB PHY layer of 2400~2483.5 MHz, because it is a commonly used, free Industrial, Scientific, and Medical (ISM) band. The values of the parameters used to obtain our results, for both the analytical model and the simulation, are summarized in Table 2. These parameters are specified for a narrowband PHY in the IEEE 802.15.6 standard. The packet payload has been assumed to be constant and is equal to 1020 bits, which is the average value of the largest allowed payload size for the NB PHY. For estimating energy, we used the parameters considered in [24]. In all the plots in this section, we used standard markers to represent the data obtained from the simulations and different type of lines to refer to the analytical results.
Narrowband “channel seventh” parameters and energy descriptions.

For a given number of nodes, we see that the throughput for lower-priority nodes decreases drastically as λ increases. This is because with a low arrival rate, very few nodes have packets to transmit, but when the arrival rate increases, the number of attempts decreases more for the lower-priority nodes. All these curves show that classes with smaller

Normalised per class throughput by considering both EAP and RAP as one RAP.
Normalised per class throughput, when EAP length is half of RAP.
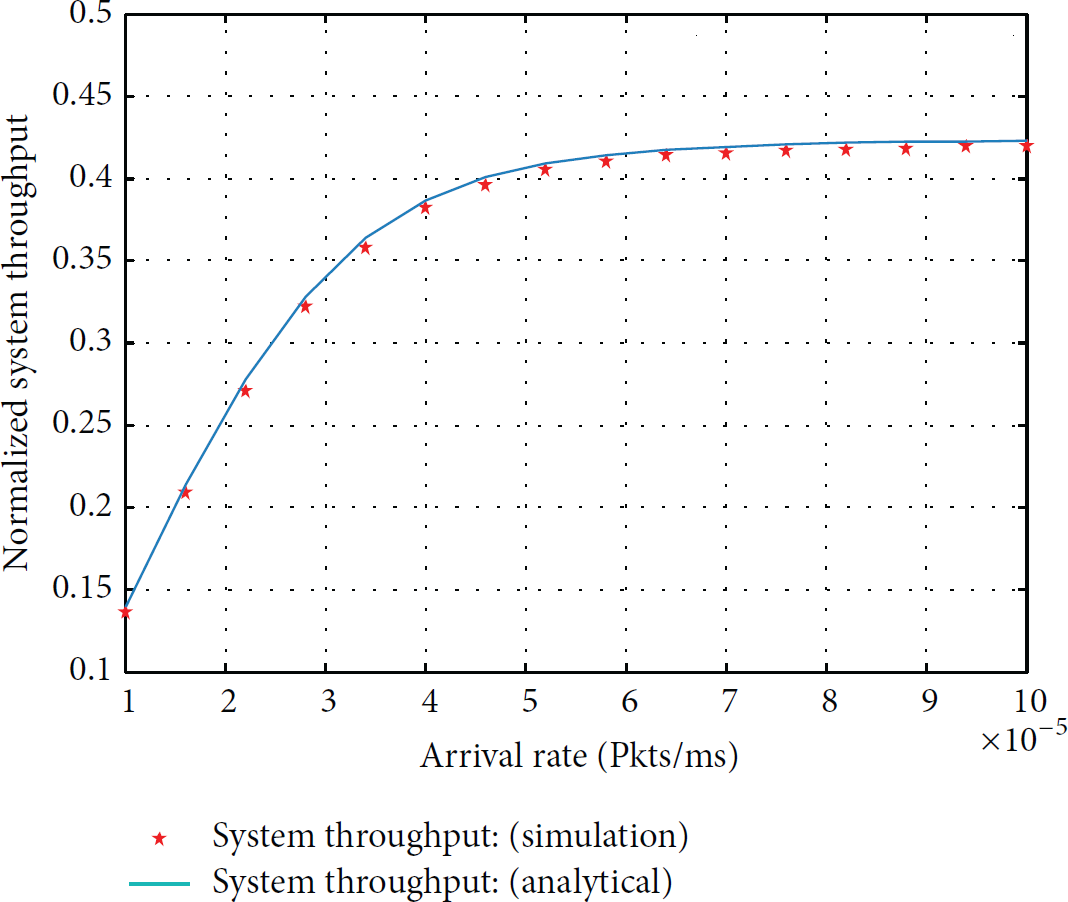
Figures 7 and 8 show the overall network throughput for the two different scenarios, that is, without access phases and with access phases, respectively. The network consists of five different user priority classes, where each class has the same number of nodes but has different combination of

Normalised system throughput by considering both EAP and RAP as one RAP.
Normalised system throughput, when EAP length is half of RAP.
The mean frame service time performance in a nonsaturated heterogeneous scenario is illustrated in Figures 9 and 10 as a function of the arrival rates. For a given

Head-of-line delay by considering both EAP and RAP as one RAP.

Head-of-line delay, when EAP length is half of RAP.
Figures 11 and 12 show the average energy consumption of a

Energy consumption by considering both EAP and RAP as one RAP.

Energy consumption, when EAP length is half of RAP.
5. Conclusions
In this study, we developed a discrete time Markov chain to model the backoff procedure of IEEE 802.15.6 CSMA/CA under nonsaturated conditions, by considering different access phases lenghts. We evaluated the performance of the IEEE 802.15.6 CSMA/CA mechanism to predict energy consumption, normalized throughput, and mean frame service time of the network by employing the proposed Markov chain model. The performance measures obtained by the analytical model were validated against accurate simulation results. Our results show that the IEEE 802.15.6 CSMA/CA mechanism utilizes the medium poorly for low priority users. In addition, the use of different access phases degrades the overall system throughput performance, resulting in higher delay for nonemergency nodes and hence more energy per packet consumed. We can optimize the length of the access phases to achieve better throughput and reasonable delay. This model will be extended in our future work, considering all the APs, error-prone channel, and multi-user environments. We also intend to fine-tune the length of the access phases and number of nodes for different user priorities, which will lead to comparatively better system throughput and minimum delay.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgment
This research was supported by the MSIP (Ministry of Science, ICT and Future Planning), Korea, under the ITRC (Information Technology Research Center) support program (IITP-2015-H8501-15-1019) supervised by the IITP (Institute for Information & communications Technology Promotion).
