Abstract
Wireless Sensor Networks (WSNs) can benefit from ad hoc networking technology characterized by multihop wireless connectivity and infrastructure less framework. These features make them suitable for next-generation networks to support several applications such M2M applications for smart cities and public safety scenarios. Pivotal design requirements for these scenarios are energy efficiency, since many of these devices will be battery powered placing a fundamental limit on network, and specifically node lifetime. Moreover, the way in which traffic is managed also influences network lifetime, since there is a high probability for some nodes to become overloaded by packet forwarding operations in order to support neighbour data exchange. These issues imply the need for energy efficient and load balanced routing approaches that can manage the network load and not only provide reduced energy consumption on the network but also prolong the network lifetime providing robust and continuous. This work proposes a new energy efficient and traffic balancing routing approach that can provide a weighted and flexible trade-off between energy consumption and load dispersion. Simulation results show that the proposed protocol achieves high energy efficiency, decreases the percentage of failed nodes due to lack of battery power, and extends the lifespan of the network.
1. Introduction
WSN is a key enabling technology for next-generation networks, having significant application in connecting a multitude of wireless tiny sensors or being able to operate in a more advanced mode by locally connecting different “things” of different capabilities, such as Personal Device Assistance (PDAs), Mobiles, and laptops, making then an ideal solution for next-generation networks. WSNs technology has a profound effect on our everyday life due to its inherent features such as being ubiquitous in nature and offering an inexpensive alternative to traditional networks.
WSNs are more specific use-cases for ad hoc wireless networks that today are autonomous in nature and support flexible topologies to deliver fast and everywhere connectivity. A self-configuring WSN, constituting distributed autonomous wireless nodes, can benefit from a multihopping ad hoc approach, in which nodes operate not only as a transceiver but also as a router and forward packets to other nodes in the network which may not be within direct transmission range of each other. Therefore, by operating in “ad hoc” mode, packet travelling from a source node toward a destination node may pass through multiple nodes to reach its destination.
A key enabler in ad hoc networks is a routing approach that needs to be robust and low in complexity to support end-to-end connectivity in highly dynamic operating environments. However, the effect of node/user mobility, dynamic topologies, frequent link breakages in the communication path, limitation on nodes resources such as battery power, and lack of central point such as base stations or servers means that routing in ad hoc networks can be a very challenging issue. Beside these aforementioned issues, there are also several qualities of service (QoS) metrics that should be considered in a communication, such as data throughput, delay, energy efficiency, traffic balancing, and the protocol overhead. Furthermore, due to the distributed and cooperated nature of ad hoc networks, attributes such as the number, velocity, and the mobility pattern of mobile nodes may affect the QoS metrics provided by the routing protocol.
Providing a concrete routing solution that is energy efficient, but on the other hand able to deliver adequate QoS, is challenging, especially in a highly mobile environment. Usually each protocol tries to focus only on one or some of these QoS metrics. Different approaches reactive and proactive have been explored, and each has distinctive advantages.
Ad Hoc On-demand Distance Vector version 2 (AODVv2) protocol [1] is a well-known routing protocol presented by Mobile Ad Hoc NETwork (MANET) group of Internet Engineering Task Force (IETF) [2]; it applies a uniformed message format and has inherent features to support many required QoS metrics, but it is limited in terms of energy and traffic management. We exploit AODVv2 as a fundamental building block and go beyond this by designing and implementing energy and traffic aware capability. This work proposes an Energy Efficient Ad Hoc On-demand Distance Vector version 2 (E2AODVv2) that can have several applications specifically in WSNs. We implemented several simulation scenarios to test the capability of E2AODVv2, where results have shown that our proposed approach achieves higher performance in terms of energy consumption and load balancing compared to the baseline routing protocols.
This work is structured as follows: Section 2 presents the literature review and related works, Section 3 describes the current implementation of the AODVv2 protocol, Section 4 introduces the new proposed E2AODVv2 routing protocol, Section 5 presents the analysis and simulation results, and finally Section 6 presents conclusions and future works.
2. Related Works
2.1. Ad Hoc Routing Protocols Category
Many routing algorithms have been proposed for ad hoc networks in the literature. These routing protocols can be divided into several categories based on various criteria. In this section, we briefly review these categories and provide one sample from each category.
2.1.1. Flat Routing Protocols
Flat routing protocols in ad hoc networks adopt a flat addressing scheme which means all nodes participating in the routing process play an equal role. Flat routing protocols may generally be classified into two main categories.
(A) Proactive Protocols. This type of protocols attempts to find and maintain consistent, up-to-date routes between all source-destination pairs regardless of the use or need of such routes. Therefore, each node maintains one or more tables to store routing information (table driven protocols). Proactive protocols require periodic control messages to maintain routes up to date for each node. Routing techniques are either link-state or distance vector (or a mixture of both) [3, 4].
Distance Vector (DV) based routing protocols: Destination Sequenced Distance Vector (DSDV) [5] is a proactive table-driven protocol based on the classical Bellman-Ford algorithm. All nodes try to find all paths to the possible destination nodes in a network and to save them in their routing tables. Link-State Based (LS) routing protocols: Optimized Link-State Routing Protocol (OLSR) [6] uses selected nodes called multipoint relays (called MPRs) for routing operations in order to forward broadcast messages during the flooding process. Link-state information is generated only by MPRs and this information is then used for route calculation.
(B) Reactive Protocols. Routes are created only when a source node requests them (on-demand protocols). Forwarding process is accomplished according to two main techniques.
Source routing protocols: Dynamic Source Routing (DSR) [7] is a source routing protocol and requires the sender to know the entire route to the destination. It is based on route discovery and route maintenance process. Discovered routes will be cached in the relative nodes. Hop-by-hop routing protocols: like Ad Hoc On-demand Distance Vector (AODV) [8], it uses the on-demand mechanism of route discovery and route maintenance from DSR and also a mechanism for the hop-by-hop routing and sequence number. Per each destination, AODV creates a routing table, while DSR uses node cache to maintain routing information.
2.1.2. Hierarchical Routing Protocols
In hierarchical routing protocols, the network's nodes are divided into clusters. Each cluster has an admin entity (head cluster) which is responsible for routing inside that cluster; therefore, in this context, nodes have different responsibilities and importance in routing algorithm. Also, the cluster head election can be a dynamical and distributed operation. Zone Routing Protocol (ZRP) [9] is a hybrid/hierarchical routing protocol that takes advantage of both proactive and reactive schemes by creating overlapped zones based on the separation distances between wireless nodes. ZRP tries to limit the flooding area per each node by assigning a routing zone to that node [10].
2.1.3. Geographical Position Based
These types of protocols assume that each node in the network is aware of its own location and the status of its one-hop neighbors, for example, via a Global Positioning System (GPS). In the Greedy Perimeter Stateless Routing (GPSR) [11] protocol, in any communication between a source-destination pair of nodes, the source node is aware of the destination node's location. All one-hop neighbors exchange beacon control messages between each other to simultaneously update their routing tables and limit control message overhead [10].
2.1.4. Hybrid Protocols
Hybrid protocols, by mixing different routing algorithms, try to take the advantage of previously mentioned protocols to reach to the highest efficiency. Temporally-Ordered Routing Algorithm (TORA) [12] is a highly adaptive loop-free distributed routing algorithm based on the concept of link reversal and it applies a reactive (on demand) source routing scheme. The key design concept of TORA is the reduction of control messages to a very small set of topological changes by performing three basic functions: route creation, route maintenance, and route deletion. All nodes in TORA use a “height” metric to establish a direct acyclic graph (DAG) rooted at the destination [13].
A category of current ad hoc routing protocols is shown in Figure 1. Also, a survey on current routing algorithms for wireless ad hoc networks can be found in [10]. The new proposed routing protocol, the so-called “E2AODVv2,” can be conveniently positioned as shown by Figure 1.

A structure of ad hoc routing protocols categories.
2.2. Power-Aware Routing Protocols
Hard QoS routing guarantee in ad hoc networks is a Nondeterministic Polynomial time- (NP-) Complete problem [14]. Therefore, the current works focus on providing a soft QoS routing guarantee for ad hoc networks as a more realistic solution. In this paper, we consider battery power consumption and traffic balancing as a measurement of efficiency.
Most of current routing protocols, proposed in MANET group of IETF [2], consider the path length metric when choosing the best route between a source (S) and a destination node (D). However, this approach may, in most cases, minimize the end-to-end delay in a communication between the source and the destination node, but it may not be adept to handle other QoS metrics such as energy efficiency and load balancing, because they do not consider the node residual energy as a criterion in the route selection process [15].
The dynamic topology in ad hoc networks implies that some nodes may relay more traffic than others, mainly because of their location in the network; these hot spots will consume their energy reserves sooner than the others. Unbalanced battery power consumption in the network nodes can leads to early node failure rate a, network partitioning, and to a reduction in the route reliability. Traffic concentration on these nodes may increase radio jamming, delay, and packet loss. Also, since the majority of the network traffic can potentially pass these nodes, they can become an important target for attackers.
Power-aware routing algorithms aim to deliver new routing paths that take into account energy as a metric [16]. Gomez et al. [17] add new intermediate nodes to a route from a source to a destination to reduce the overall required transmission power of the intermediate nodes. Lindgren and Schelen [18] improve the AODV routing protocol in terms of energy efficiency, by selecting paths through Power Base Stations (PBSs) instead of through normal nodes. Edwards et al. [19, 20] present two power-aware extensions of the original DSR ad hoc routing protocol that use energy aware metrics such as the remaining battery power to decide which nodes should participate more often in packet forwarding. Load balancing and homogeneous distribution of battery power consumptions between networks nodes are other solutions to achieve a power-aware ad hoc routing algorithm [21].
However, most of current power-aware approaches lead to some common drawbacks, such as increased delay and increase in the number of required control messages that should be created by the routing protocol to deliver users’ data packets (called Normalized Routing Load), limited scalability, among others.
3. Revised Ad Hoc On-Demand Distance Vector (AODVv2)
AODVv2 is a successor to the AODV that is being developed by IETF MANET; prior to the 26th revision [1], AODVv2 was called DYnamic MANET On-demand (DYMO).
3.1. Protocol Description
AODVv2 tries to simplify the current reactive protocols, such as DSR and AODV, and simultaneously conserves their two main well-known routing operations: route discovery and route maintenance [22]. It has multipath capability (optional) and is also a hop-by-hop routing protocol. Therefore, intermediate nodes, located in a route between a source and a destination node, are able to extract additional information from the traversing control packets. AODVv2 applies a standard generalized MANET Packet/Message format [23] for control packets: a uniformed message format, called Routing Message (RM), is used for all control messages and routing packets. Another interesting feature of AODVv2 is the capability to Internet Protocol (IP) [24] versions 4 and 6 (IPv4 and IPv6, resp.) which can be considered an essential feature for next-generation networks.
Several works analysed the performance and benefits of AODVv2 [22, 25, 26]. To improve the performance of AODVv2 [22, 25, 26], Kretschmer et al. [27] focused on reducing the delay and on increasing the packet delivery ratio, by finding routes with high probability to be used in future. Also, there are few works, such as [25], that try to extend a multipath version of AODVv2 to switch between different paths from source to destination in order to balance the battery power consumption and the traffic of the nodes on different routes. However, these works do not provide a mechanism for handling both load balancing and energy efficiency in highly dynamic topologies.
3.2. Routing Operation
All routing operation in AODVv2 can be categorized into three phases.
3.2.1. Route Request Phase
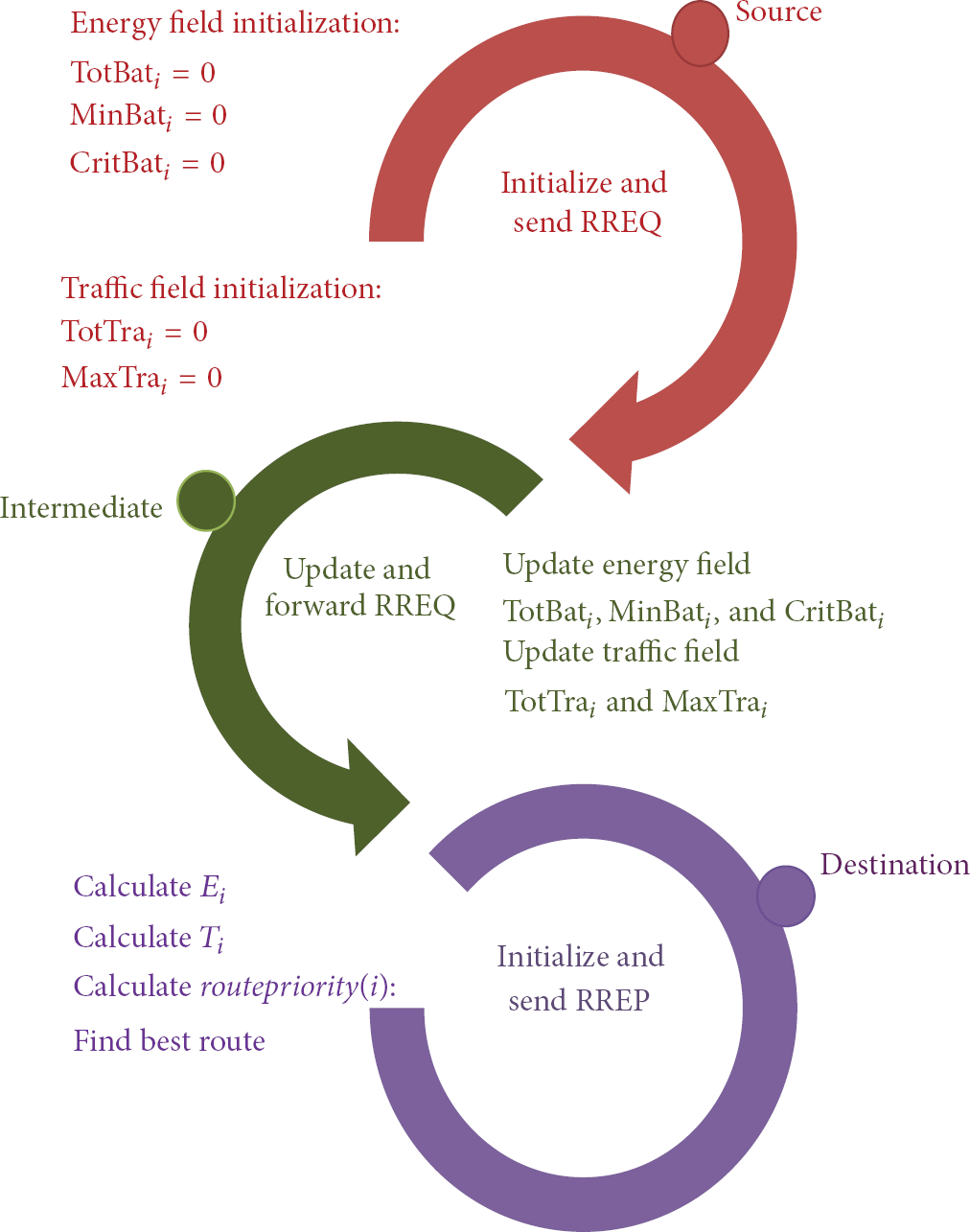
In a communication between a source node (S) and a destination node (D), S originates a Route Message (RM), called ROUTE REQUEST (RREQ) message, and broadcasts this to all of its neighbours. These RREQs are then flooded in the network until they reach D. An intermediate node which does not know the route to D should forward the RREQ to its neighbours. The intermediate node will also drop the repeated request for the same destination and will not forward them anymore, as shown by Figure 2. RM has several fields such as current node address, next node address, HopLimit (the default value is 10 based on [1]), Target (destination node address if it is an RREQ message), and the Origin (source node address if it is an RREQ message) [1]. By tracing the RREQ traversed path (called accumulated path), each node, such as intermediate or destination node, which receives an RREQ message, can extract routing information. Figure 2 shows the RREQ phase in AODVv2 routing protocol for a sample network.
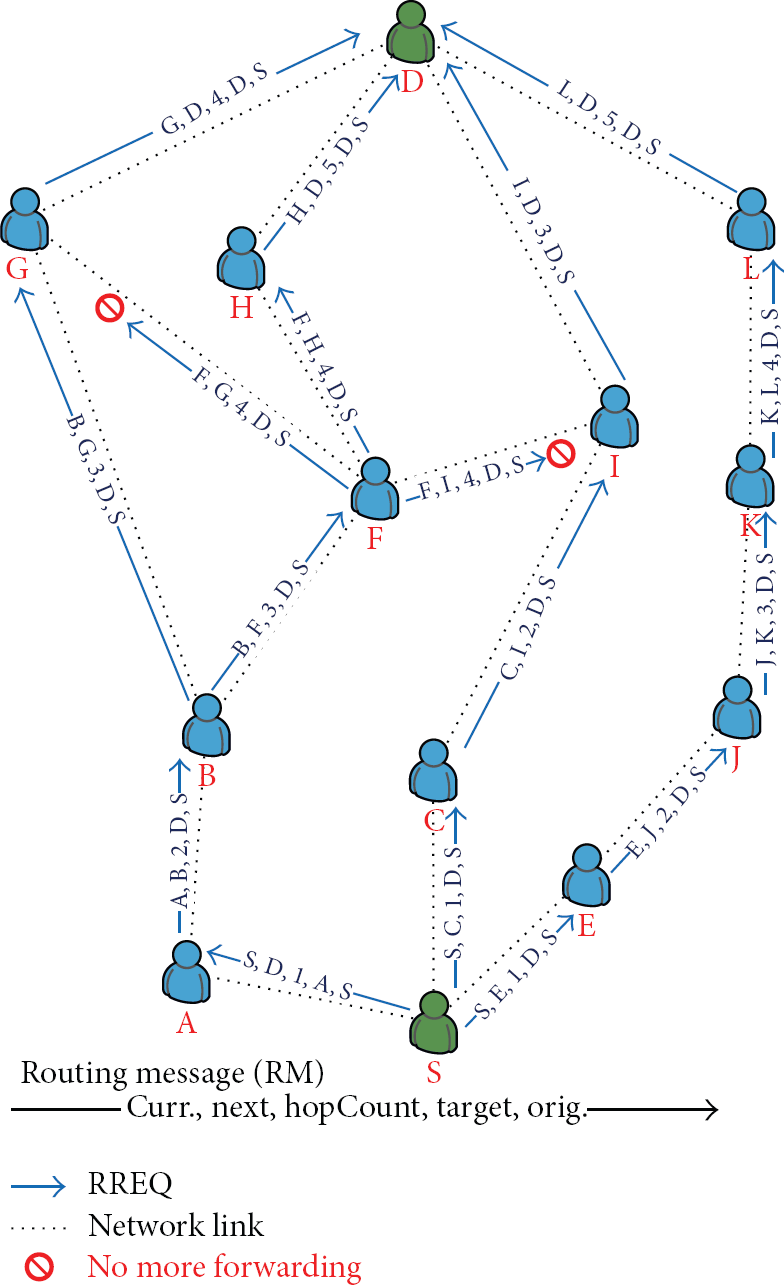
A sample of RREQ phase in AODVv2.
3.2.2. Route Reply Phase
As shown by Figure 3, when RREQs finally reach the destination node, another RM, which is called ROUTE REPLY (RREP), will be originated by the destination node. The intermediate nodes which have, in their routing table, an entire route towards that destination node also can immediately reply to the RREQ originated by the source node (known as gratitude reply and it is an optional feature of AODVv2). Both the RREQ and the RREP have the same uniform structure.

A sample of RREP phase in AODVv2.
3.2.3. Routing Operation: Route Error Phase
An intermediate node may originate an RM, called an ROUTE ERROR (RERR), in the two main scenarios. In the first case, the intermediate node does not have a valid route for the destination of a received data packet and consequently the packet is undeliverable. In the second case, the intermediate node detects a link breakage, as shown in Figure 4.

A sample of RERR phase in AODVv2.
4. Energy Efficient AODVv2 (E2AODVv2)
The inherent benefits of AODVv2 due to standardized control packets following IETF uniform packet formats and the capability to support IPv6 suggest that this protocol will have a strong legacy in ad hoc networks. Therefore, if we are to pursue energy efficient operation for routing in ad hoc networks, then exploring AODVv2 as the fundamental building block can be potentially a springboard for promoting significant energy savings in the network. In this section, we describe our proposed approach to increase the energy efficiency of AODVv2.
4.1. Routing Messages in E2AOVv2
E2AODVv2 introduces two new fields for each routing message which are discussed in this section.
4.1.1. Energy Field
Suppose that, for a communication between a source and a destination node, there are N routes and the number of nodes in the ith route, called

Multiple routes between source and destination.
Moreover, there is a Critical Battery Power Level (CBPL) whose default value is 3 (
The Energy field of RREQ in E2AODVv2 has three cells: totbat, MinBat, and CritBat. TotBati is the summation of the total battery power level of all nodes of
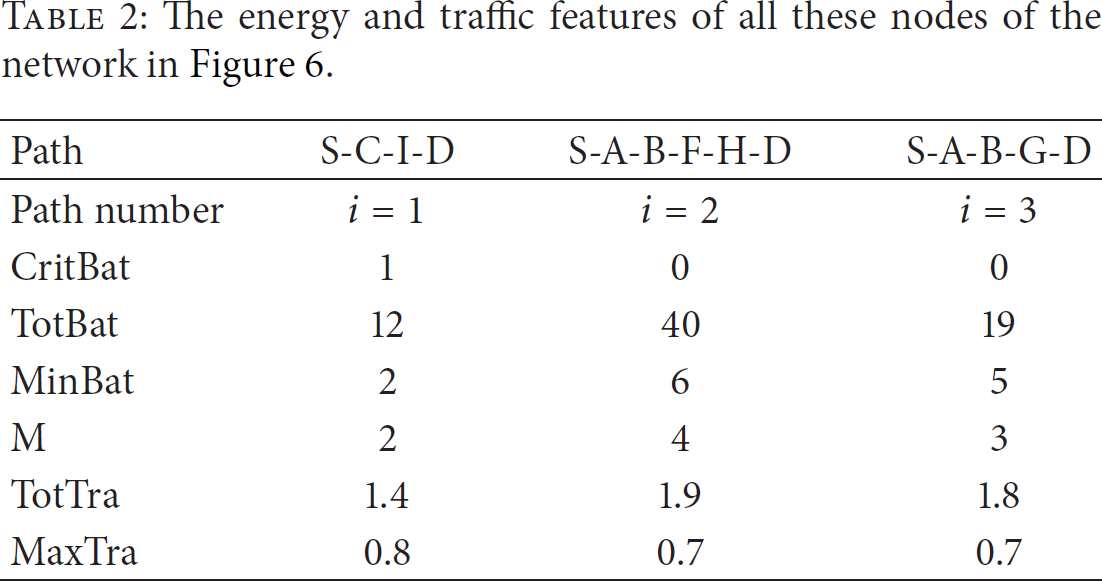
Figure 6 shows a network based on the previous sample that has a simpler topology. In this example, there are 8 nodes. The battery power level and the traffic parameter of all these nodes are given in Table 1 (the traffic parameter will be introduced later in this paper). Based on Table 1, the energy and the traffic parameters of all paths of the network in Figure 6 are calculated and given by Table 2.
Battery power level and traffic parameter of all nodes of the network in Figure 6.

The energy and traffic features of all these nodes of the network in Figure 6.

D originates route replies (RREP) toward S in AODVv2.
For example, as the first column of Table 2 shows, the first path (
For this network, the original AODVv2 chooses the shortest path (i.e., the first path S-C-I-D); however, the new proposed protocol, E2AODVv2, will choose the second path (i.e., S-A-B-F-H-D), which is a stronger alternative in terms of energy efficiency, and even traffic load which is discussed later on.
4.1.2. Traffic Field
In Figure 5, if the queue size of the interface of node k located in 

For example, as the first column of Table 2 shows, for the first path
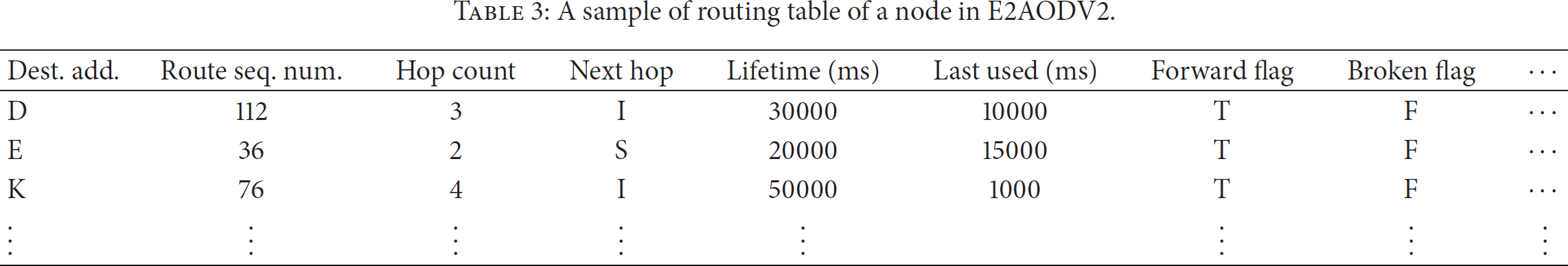
Therefore, in E2AODVv2, when the intermediate node k receives RREQ, it updates TotTrai and MaxTraiof the traffic field of the RREQ and forwards the RREQ toward the next node. A sample node routing table is shown in Table 3.
A sample of routing table of a node in E2AODV2.
4.2. Route Selection Process
In E2AODVv2, when a destination node receives several RREQs from different routes, as in Figure 5, it runs a route selection process to determine the best route in terms of energy and traffic parameters.
4.2.1. Calculating Energy Parameter of a Route in E2AODVv2
The energy parameter of 


4.2.2. Calculating Route Traffic Parameter in E2AODVv2
A route with a lower traffic metric cost has a higher priority in the routing process of E2AODVv2. Nevertheless, a route may have a low overall traffic metric even if one of its nodes is overloaded with traffic, thus creating a bottleneck, and should be potentially avoided. The traffic parameter of Route
i
is shown by 
4.2.3. Precedence Function
The function that determines the precedence of 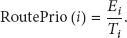
4.2.4. Routing Behaviour of Nodes in E2AODVv2
In E2AODVv2, each node shows different routing behaviour that depends on the role of the node in the communication.
Source node: when a source node wants to send an RREQ, it initializes the values of the energy and the traffic fields (they will be set to zero). Intermediate nodes: these update the energy and traffic fields accordingly: (i) each node who receives an RREQ adds its own BP to TotBat value; (ii) if the current node k in Destination nodes: when a destination node receives n RREQs from different n routes, by extracting the required information from RREQ, it can calculate the Route Priority for all these RREQs and finally the route which has the best Route Priority will be chosen.
Figure 8 shows the role of the source, the intermediate, and the destination nodes in a communication. Each route request, such as
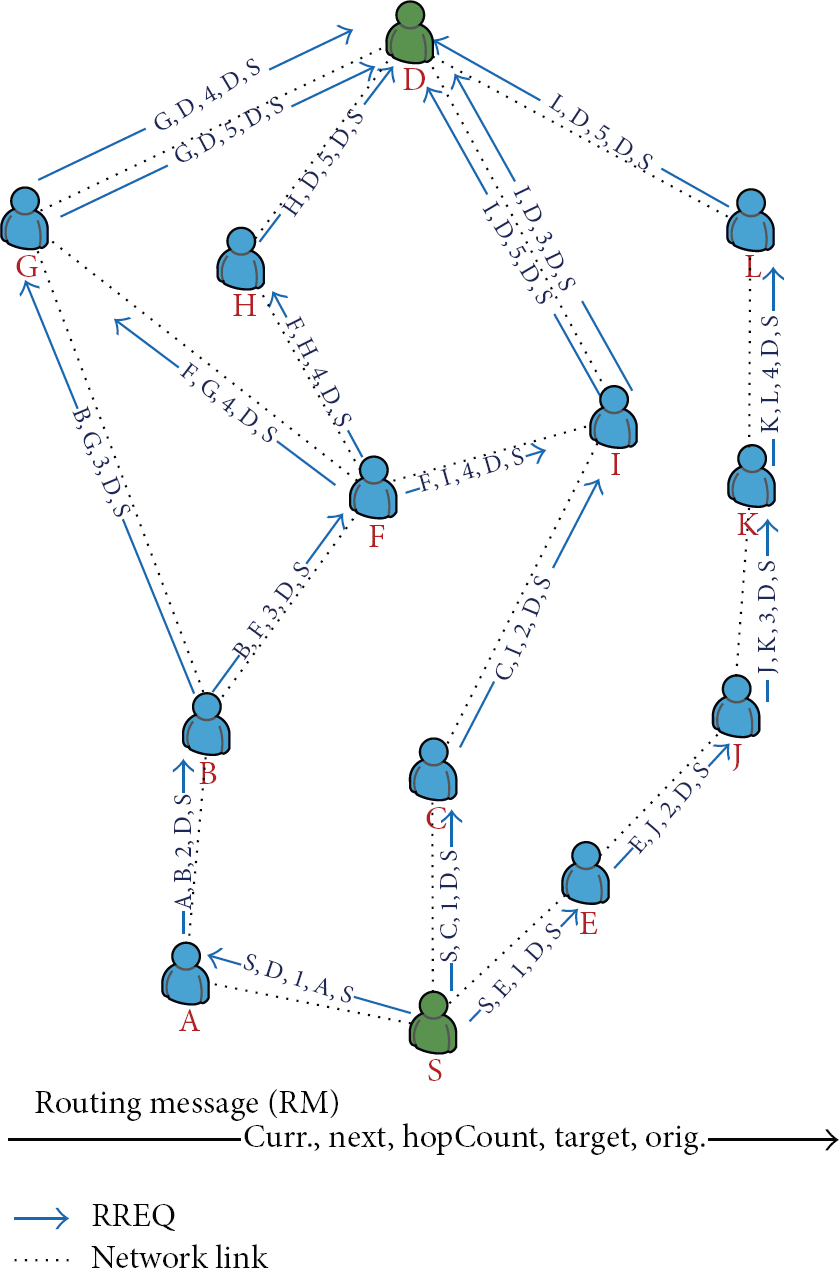
A sample of RREQ phase in E2AODVv2.
RREQ and RREP processes: the routing behaviour of source, intermediate, and destination nodes in E2AODVv2.
5. Analysis of E2AODVv2
5.1. Analytical Analysis
As we discussed in Section 4.1, the traditional AODVv2 for the network in Figure 6 chooses the first path (
The energy and traffic features of all paths in the network of Figure 9.

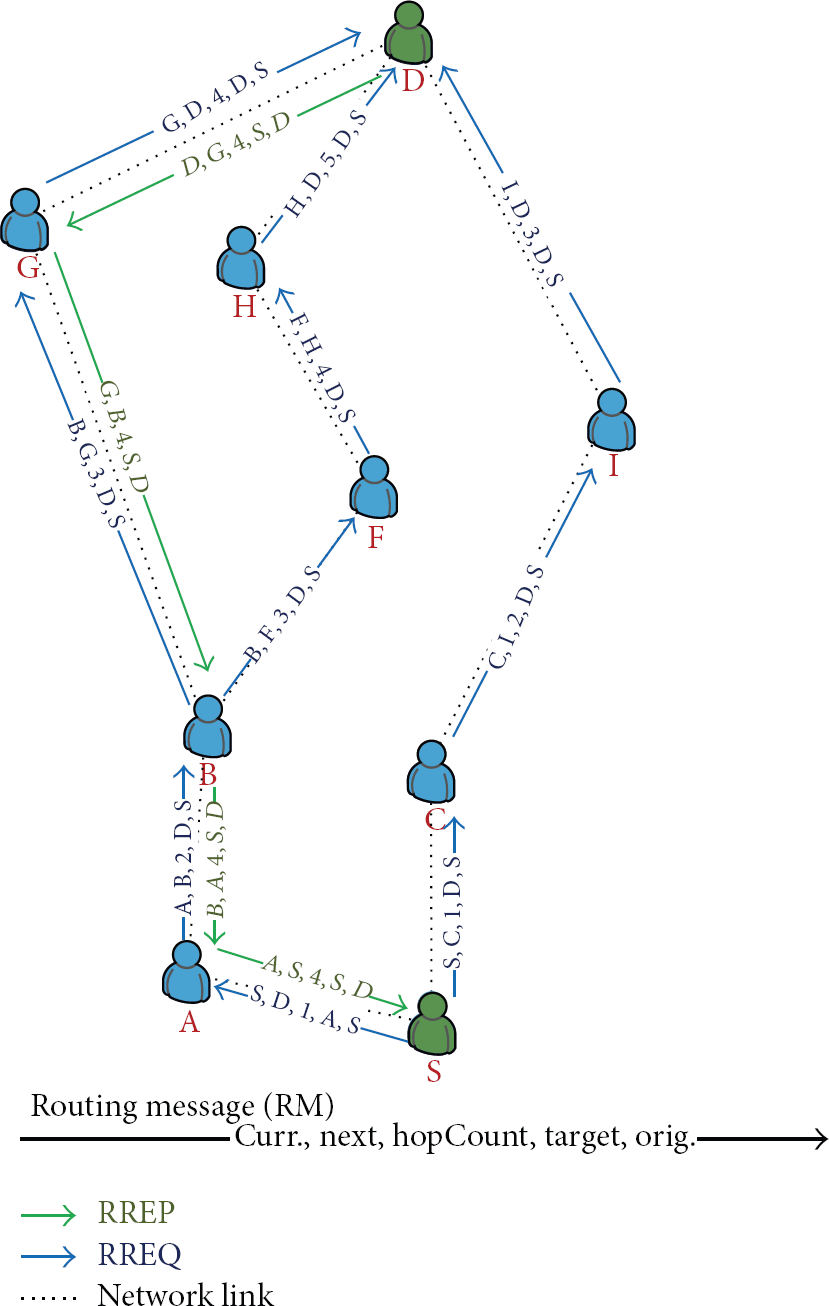
A sample of RREP phase in E2AODVv2.
5.2. Evaluating Proposed Protocol
We use Two-Ray Ground Reflection Model which considers both the direct path and a ground reflection path between two mobile nodes. Also all nodes in the network move based on the Random Way Point Mobility Model. In this movement model, a mobile node starts its travel from a random location inside the topology area after pausing for a certain period of time (called “pause time”). After the initial pause time, the mobile node chooses another random location inside the topology area and moves toward this new location by a speed that is uniformly distributed between a predefined minimum and maximum speed. Upon arrival, the mobile node pauses again for the pause time and repeats the previous process again till the simulation time is expired [3, 28].
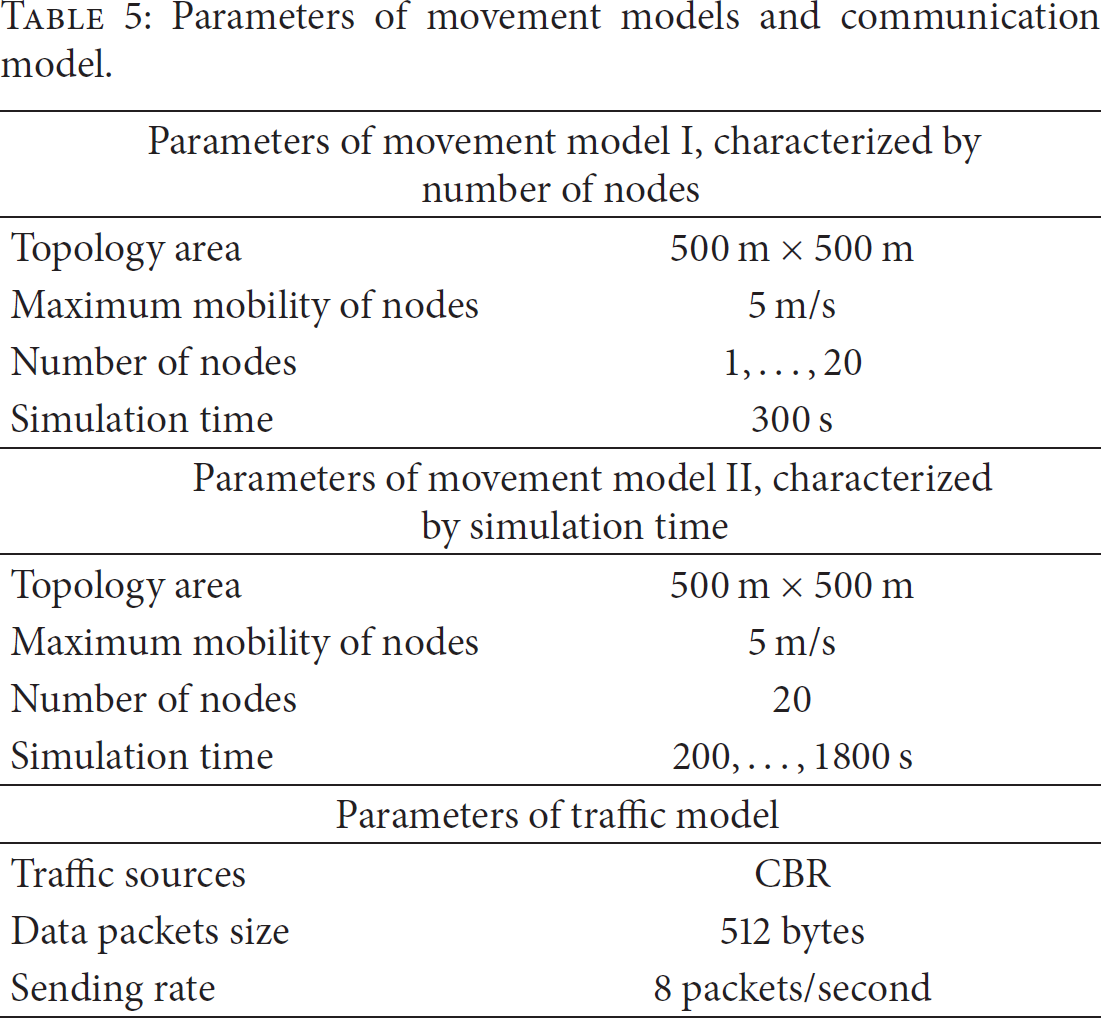
The simulation results presented in this paper were obtained using the ns-2 simulator [29]. Traffic sources are CBR (Constant Bit Rate) and the packet sending rate at the source nodes is 8 packets per second. Table 5 presents a summary of the parameters for the simulated scenarios (movement and traffic files).
Parameters of movement models and communication model.
5.2.1. Performance Metrics
We evaluated the proposed protocol using five metrics:
(I) Balancing Energy Consumption. This metric will allow measuring the effectiveness of the energy balancing algorithm used by E2AODVv2. Let us denote the energy load of all the nodes in the network consisting of N nodes; is a set
where element of this set, for example, 
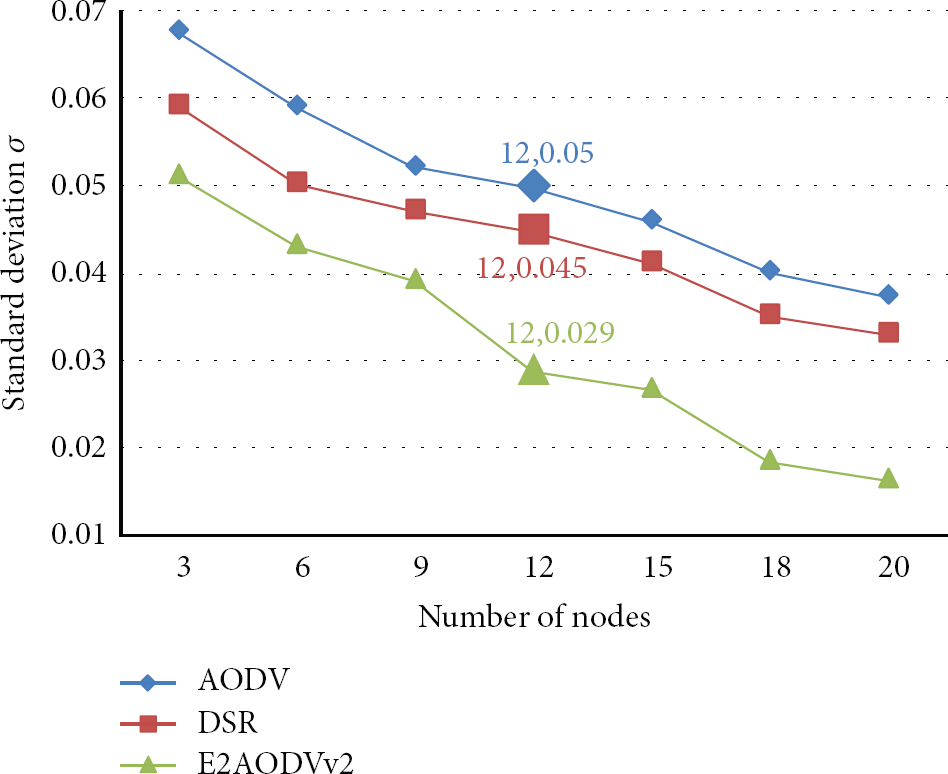
(II) Scalability. Another interesting metric is the scalability of the proposed protocol in terms of load balancing, that is, if the proposed protocol can balance the load of the network when we increase the number of network nodes (i.e., N in our settings). For this purpose we change the number of nodes N (the network size) to a maximum number (which is 20 in our setting, based on Table 5) and calculate the related
(III) Network Lifetime. Network lifetime is another important metric that reflect the load balancing capability of the routing protocol; the bigger the lifetime, the more effective the energy balancing capability. To compare the lifetime of the proposed protocol with other protocols, we take two parameters into consideration:
(IV) Node Failure Level. Finally the last performance metric that we use is the node failure level, which determines the capability of E2AODVv2 in keeping nodes alive for longer durations. The node failure level, for a time window T, is the percentage of nodes in the topology that have failed due to a depleted battery. This value is calculated as follows:

(V) Jitter. In a data transmission between a pair of source and sink nodes, jitter is the variation in the time between packets arriving at the source node. Let us assume that, at time 
5.2.2. Simulation Results
This section presents the simulation results for the comparison between two reactive protocols AODV and DSR that are considered baselines in this work, against our proposed E2AODVv2 protocol.
(A) Balancing Energy Consumption and Scalability. For this metric, simulation results are presented in terms of the capability of our approach to balance battery power (energy) consumption. The traffic model is the one presented in Table 5 with the following variants.
Distributed traffic amongst nodes: traffic sources and destinations will be chosen randomly in time. This variant is shown by “Distributed” in Table 6. Concentrated traffic with overloaded nodes: traffic destinations will be predefined (all traffic in the network goes toward those sink nodes). This variant is shown by “Concentrated” in Table 6.
The metric for energy consumption balancing in a network consisting of N nodes is
Balancing energy consumption metric

Balancing of energy consumption (

Balancing of energy consumption (
Furthermore, the value of
For the first variant, distributed traffic amongst nodes, all protocols show a similar performance (Figure 10): increasing the number of nodes leads to improved energy balancing (lower standard deviation). This can be explained due to the chosen traffic model since multiple traffic source/destinations are chosen randomly throughout the simulation, and thus more nodes will participate in the routing process.
For the second variant, that targets concentrated traffic with overloaded nodes, we chose n nodes, amongst all network nodes (N), as destination nodes (sink nodes) for the generated traffic in the network. The number of n is set to 20% of N, which due to the many-to-one traffic pattern, creates overload conditions at destination nodes. Simulation results show that, in such scenarios, the standard deviation behaviour is similar to the previous variant but with the worst performance (Figure 11). However, as in the previous scenario, all three protocols improve in terms of performance as the number of nodes in topology increases (Figure 11). As both Figures 10 and 11 show, the proposed protocol E2AODVv2 reaches a higher performance in terms of battery power efficiency, balancing, and scalability in contrast to the baselines.
(B) Network Lifetime and Node Failure Level. This metric is measured using movement model II described in Table 5. Similar to the previous case, here again there are two different traffic models: Distributed traffic amongst nodes (Figure 12) and Concentrated traffic with some overloaded nodes (Figure 13). As discussed in Section 5.2.1, we use the first failure time FTfirst and the last failure time FTlast as the network lifetime metrics. The values of FTfirst and FTlast are marked in Figures 12 and 13 and also summarized in Table 6. As these results show, E2AODVv2 has always better value for both FTfirst and FTlast. Also, as expected, the number of failing nodes increases with simulation time. When nodes use E2AODVv2, their lifetime gets extended due to the energy balancing capabilities of E2AODVv2 and shows a lower Node failure level (Figure 12). This feature is even more pronounced when traffic is concentrated in a few nodes (Figure 13).

Percentage of failed nodes versus simulation time (when distributing traffic amongst nodes).
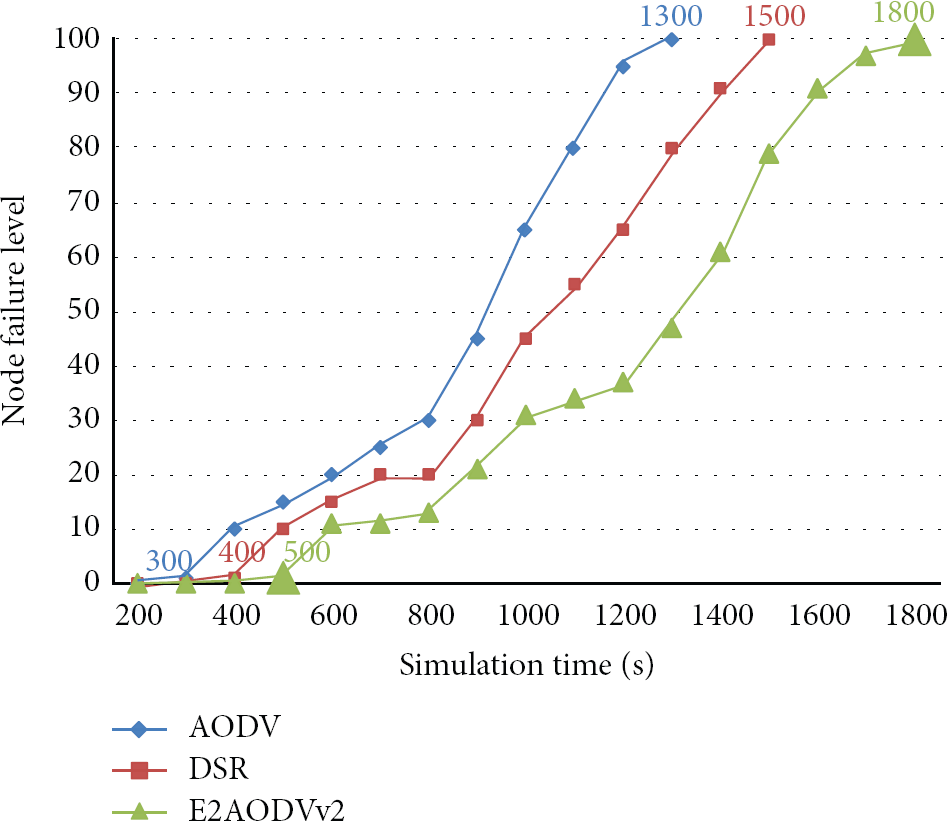
Percentage of failed nodes versus simulation time (when traffic is concentrated in a few nodes).
(C) Jitter. Jitter has several sources such as network congestion, route changes, and delaying packets in the buffer queues of the intermediate nodes in a source-sink communication session. Usually a jitter buffer is used at sink nodes to counteract the jitter.
Jitter is a measurement for the quality of the communication; a small jitter indicates a high quality communication by a low latency. As Figure 14 shows, the performance of the proposed protocol is better than DSR and very close to the original AODV. This can be explained due to the more complicated algorithm of E2AODVv2 for choosing a route which leads to a higher delay.

Jitter versus number of nodes.
Future work will extend the proposed approach in this paper for energy efficiency and load balancing to include other QoS metrics such as delay and data throughput by varying the topology area and velocity of nodes. Another metric that could be considered in the future works to obtain the required power for transmitting the data between two nodes is the signal to noise ratio (SNR). A high SNR value for a link between two neighbor nodes shows that we should find an alternative energy efficient link and eventually a path for the data transmission between a pair of source and sink nodes. This approach may also lead to the need for a cross-layer design [30] for our protocol.
6. Conclusion
Next-generation wireless sensor networks, constituting distributed autonomous wireless sensors and nodes, can benefit from ad hoc networking technology. However a key requirement for this technology that should be satisfied is an energy efficient and load balanced routing protocol. This paper proposes a new energy efficient and traffic balancing routing protocol based on the well-known IETF AODVv2 protocol, a popular approach for routing in ad hoc networks. The protocol uses a standard generalized MANET Packet/Message format. The E2AODVv2 has been enhanced with battery power efficiency and balancing capability that can detect the nodes that reach a critical battery level in the network and switch the route in order to avoid network fragmentation and to achieve a higher network lifetime. The same behaviour is also fulfilled when bottlenecks are detected in a specific route in terms of traffic load. These additional functionalities are achieved without the need to create new disruptive approach in the protocol messages. E2AODVv2 achieves a higher performance with respect to energy consumption balancing, scalability, network lifetime, and the percentage of failed nodes in comparison to well-known baseline protocols such AODV and DSR and a jitter value very close to the AODV. As shown by the simulation results, the E2AODVv2 routing protocol specifically outperforms in scenarios where the load of the network is not balanced. Moreover, the proposed approach can be said to be technology agnostic in that it can be applied to many other reactive ad hoc protocols.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgment
The research leading to these results has received funding from FEDER through the Fundação para a Ciência e Tecnologia [national reference ARTEMIS/0005/2012 - ACCUS] and the ARTEMIS JU [ART Call 2012 - 333020 ACCUS].