Abstract
Wormhole attack is a severe attack that can be easily launched by a pair of external attackers in hostile wireless sensor networks. In the wormhole attack, an attacker sniffs packets at one point in the network, and tunnels them through the wormhole link to the other attacker at another point of the network, which broadcasts them to its neighbors. Such kind of procedure can easily deteriorate the normal functionality of the networks. In this paper, we propose a novel wormhole attackers detection and positioning scheme based on mobile beacon, which can not only detect the existence of wormhole attacks, but also accurately localize the attackers for the system to eliminate them out of the network. The main idea is to detect whether the communication between the mobile beacon and each of the static beacons violates the communication properties and then the attacker can be estimated as the center of its communication area by determining the intersection point of the chords’ perpendicular bisector. The simulation results illustrate that our proposed scheme can obtain a high wormhole attack detection probability as well as a high attackers positioning accuracy.
1. Introduction
Wireless Sensor Networks (WSNs) have been applied in more and more applications, such as the emergency response systems, military field operations, and environment monitoring systems, due to the development of the low-cost, low-power, and multifunctional sensor nodes. In normal WSN applications, the sensor nodes are organized to accomplish some kind of tasks, such as event detection or data gathering. However, since WSNs are usually deployed in hostile environments, which may be attacked by some malicious attacks, the functionality of networks may be interrupted. Therefore, security is a necessary characteristic of WSNs applications.
Attackers in WSNs can be classified into two categories, external attackers and internal attackers [1]. External attackers, such as the wormhole attack, can disrupt the network functionality without passing the system's authorization, while internal attackers, such as the compromise attack, are authenticated ones which can act as inner-network nodes to break the system's security.
Generally, the wormhole attack is launched by two colluding external attackers, which can disrupt or even collapse the functionality of the WSNs. In the wormhole attack, an attacker sniffs packets at one point in the network and tunnels them through the wormhole link to another attacker at the other point of the network, which broadcasts the packets to its neighboring nodes. Such a simple operation can severely affect the localization and routing procedures. For example, as shown in Figure 1, two kinds of nodes, that is, beacons and sensors, are deployed in the network, which is attacked by a wormhole attack lunched by

The impacts of the wormhole attack on a WSN.
The above severe effects of the wormhole attack on WSN applications motivate us to propose an efficient scheme to defend against the wormhole attacks. In this paper, we first propose a novel wormhole attackers detection scheme which can detect the existence of the wormhole attacks with a high probability. Then we propose a basic positioning scheme to further localize the wormhole attackers. We also propose an enhanced positioning scheme to decrease the power consumption during the attackers positioning procedure. The main idea is to detect whether the communication between the mobile beacon and each of the static beacons violates the communication properties. The mobile beacon can localize the attacker as the center of its communication area which can be estimated by determining the intersection point of the chords’ perpendicular bisector. Also, the localization accuracy of our proposed scheme is independent of the density of beacon nodes. The main contributions of this paper can be summarized as follows.
We propose a novel wormhole attacker detection scheme based on the mobile beacon and the successful detection probability is also theoretically analyzed. We propose a basic positioning scheme to accurately localize the wormhole attacker by estimating the center of the attacker's communication area. We further propose an enhanced positioning scheme for the attackers positioning to decrease the power consumption. We conduct simulations to illustrate the effectiveness of the proposed wormhole attackers detection and positioning schemes.
The rest of this paper is organized as follows. In Section 2, we discuss the existing wormhole attack detection and secure localization schemes. Section 3 presents the system model, including the network model and attack model. In Section 4, we propose the wormhole attacker detection and positioning schemes. The performance evaluation is conducted in Section 5. Section 6 concludes this paper.
2. Related Work
Wormhole attack detection has been a hot research topic during the last decade and lots of schemes have been proposed. In [3], the “packet leashes” mechanism is proposed to use geographical and temporal leashes to detect whether or not the packets are attacked by wormhole attacks. The wormhole detection approach in [4] is based on the end-to-end location information. Another set of wormhole attack preventing techniques [5–7] use the round-trip time of packets as a measurement to detect whether a packet travels via the wormhole link or not. In [8], a “diameter” feature based on the local map is used to detect abnormalities caused by wormholes. LiteWorp [9] makes use of two-hop neighborhood information of the stationary network to reject the packets relayed by the wormhole attacks. MobiWorp [10] uses a secure central authority to isolate the attackers globally after they are detected.
As the wormhole attack dramatically changes the network topology, the network topology information can be used to detect the existence of the wormhole attacks. Wang et al. [11] propose to detect wormhole attacks by visualizing the entire network topology with some anomalies, which is caused by the wormhole attacks. The scheme in [12] uses the network connectivity information to detect wormhole attacks based on the observation that the number of independent neighbors of two nonneighboring nodes is upper bounded. Another connectivity-based wormhole detection approach is proposed in [13] which is robust to different communication models and energy efficient. A topological approach is proposed in [14] to detect the wormhole attacks. In [15], a localized algorithm that detects the wormhole attacks directly using the connectivity information implied by the underlying communication graph is designed, and it requires no specialized hardware, which makes it practical in the real-world scenarios. By detecting whether the communication violates the properties, some novel wormhole detection schemes are proposed in [2, 16, 17].
However, all the above wormhole attack detection schemes cannot localize the attackers, which motivate us to propose the wormhole attackers detection and positioning scheme in this paper. Our proposed scheme can achieve a higher detection probability with a satisfied attackers positioning accuracy.
3. System Model
3.1. Network Model
In this paper, we consider a WSN consisting of three types of nodes: mobile beacon, static beacons, and sensors. The mobile beacon is a node with a GPS device which moves around the network to conduct some special tasks, such as detecting the wormhole attacks. The static beacons are the nodes with fixed locations which can obtain their coordinates in advance by manual deployment or via GPS devices. The sensors are stationary nodes in the network that initially do not know their locations. All the nodes in the network have the same transmission range, denoted as R, and we assume that there is no packet loss during the communication between any two neighboring nodes. Note that our proposed scheme can be extended to the general scenario where packet loss exists. Each of the nodes has a unique ID in the network and all of them can cooperate with each other to realize WSNs applications, such as self-localization, target tracking, and data gathering.
3.2. Attack Model
A hostile environment is considered, in which the deployed WSN will be attacked by the wormhole attacks. A wormhole attack is typically launched by two external attackers, which collude with each other to disrupt the network's functionality. In the wormhole attack, one attacker sniffs packets at one point in the network and forwards these packets to the other attacker via a wormhole link, which will immediately broadcast them to its neighboring nodes. The communication range between the attackers and the nodes is also assumed to be R. However, the communication between two colluding attackers is considered to be symmetrical and not limited to the transmission range R since the wormhole link may be based on some certain communication technique, such as the wired communication. For simplicity, we assume that the distance between each pair of wormhole attackers is larger than
We denote the mobile beacon, static beacons, sensors, and attackers as
4. Wormhole Attacker Detection and Positioning
In this section, we will first propose the wormhole attacker detection scheme based on the mobile beacon, the detection probability of which will be theoretically analyzed. After that we will propose the wormhole attacker positioning schemes including the basic scheme and enhanced scheme, which can accurately localize the wormhole attackers.
4.1. Wormhole Attacker Detection Scheme
4.1.1. Communication Properties
Before proposing the wormhole attacker detection scheme, we firstly introduce two communication properties, which were proposed in [2] and will be the basis of the detection scheme in this paper.
Packet Uniqueness Property. A node normally cannot receive more than one copy of the same message from any of its neighbors.
Transmission Constraint Property. A node normally cannot communicate with nodes outside its transmission range.
In WSNs, the nodes may need to communicate with its neighbors to accomplish some tasks, and the communication in which should follow the above properties. For example, when a node sends a request message to one of its neighbors to get some information, such as the sensed temperature, it is considered to be normal that this neighbor sends a reply message to the sender for only once if there is no necessity of retransmission. Also, if two nodes are out of the transmission range of each other, it is considered to be normal that the packets from one of them cannot be directly received by the other.
4.1.2. Wormhole Attacker Detection Procedure
If a wormhole attack exists to disrupt the network's functionality, the packet uniqueness property and transmission constraint property may be violated by the nodes' communication. As shown in Figure 2, there are several nodes covered by the wormhole attack; that is,
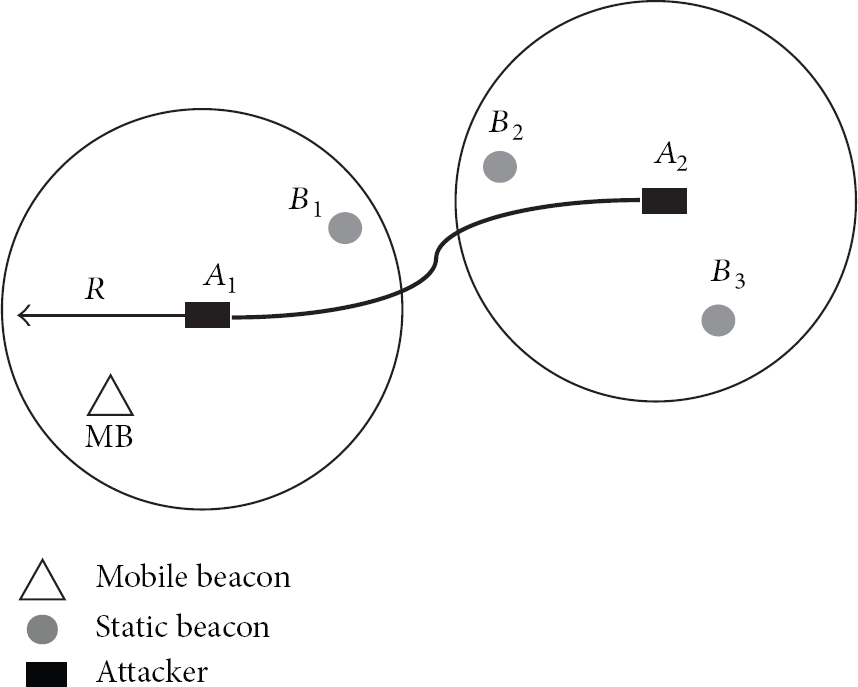
Communication procedure among the nodes under the wormhole attack.
To detect the wormhole attackers in the network, we can use a mobile beacon to detect whether the communication between itself and each of its neighboring static beacons violates the above communication properties. The wormhole attackers detection procedure is as follows.
The mobile beacon moves in the network with some direction and step length and then stops to get its current location using GPS. The details of the mobile beacon's mobility model including the moving direction and step length will be discussed in the wormhole attackers positioning scheme. At each stopping location, the mobile beacon broadcasts a request message Req to its neighboring static beacons. Each static beacon who receives the request message will immediately reply a Rep message, including its ID and coordinate, to the mobile beacon. When receiving the Rep message from the static beacon, the mobile beacon will check the receiving times of the Rep from each of the static beacons. If it receives a Rep message from a static beacon more than once, it can determine that there is a wormhole attacker within its transmission range. If the mobile beacon receives the Rep message from each of the static beacons only once, it can then calculate the Euclidean distance between itself and each of them since the received Rep message includes the replier's coordinates. If the transmission constraint property is violated, it can determine that there is a wormhole attacker within its transmission range. If nothing abnormal is detected, the mobile beacon will move to next location and perform the above wormhole attacker detection scheme until it finishes the detection of the whole network.
4.1.3. Analysis of Wormhole Attacker Detection Probability
By carefully designing the mobility model of the mobile beacon, we can guarantee that the mobile beacon will move across the communication area of each attacker. Then we can get the following theorem.
Theorem 1.
The mobile beacon can detect the existence of the wormhole attack if at least one static beacon lies in the transmission range of either of the two attackers.
Proof.
Without loss of generality, we assume that there is only a static beacon
Based on Theorem 1, we can easily analyze the wormhole attacker detection probability of our proposed scheme. We first consider the scenario with single wormhole attack. The probability that at least one static beacon lies in
Assume that the deployment of static beacons follows the Poisson distribution with the density
For the scenario with multiple wormhole attacks, we consider the detection to be successful only if the mobile beacon can detect all of the wormhole attacks. Since we consider the case that a static beacon can be attacked by at most one attacker, the detection of one of the multiple wormhole attacks is independent of that of other wormhole attacks. Thus, the detection probability that all the wormhole attacks can be successfully detected can be easily obtained as
4.2. Wormhole Attackers Positioning Schemes
Based on the above wormhole detection scheme, the mobile beacon can easily detect the wormhole attacks in the network. However, it is not enough to secure a WSN application. Thus, the mobile beacon has to further localize the attackers and then report to the system to eliminate them. In this section, we will first propose a basic positioning scheme which can localize the wormhole attackers accurately. To further reduce the power consumption during the positioning procedure, we will then propose an enhanced positioning scheme.
4.2.1. Basic Positioning Scheme
For ease of description, we assume that the WSN is deployed in a rectangular area of

Attackers positioning of the basic scheme: (a) the attackers positioning procedure; (b) determination of
When the mobile beacon enters the communication area of an attacker, such as A in Figure 3(a), it can detect the existence of the wormhole attack. Then it can save its current location as
Note that the mobile beacon only conducts the wormhole attack detection scheme every step of
The previous scheme can localize the attackers accurately when there exists only one wormhole attack. However, if multiple wormhole attacks exist and the attackers are close enough to each other, there may be some problem. For example, as shown in Figure 4, when the mobile beacon node moves from C to D, although it is out of transmission range of attacker

Attackers positioning of multiple wormhole attacks using conflicting set.
In this paper, we define the conflicting nodes of the mobile beacon node as the beacon nodes, and the communication between which and the mobile beacon node violates the packet uniqueness property or the transmission constraint property. That is to say, the conflicting nodes of the mobile beacon node are the beacon nodes which communicate with itself via the wormhole link. For example, as shown in Figure 4, when the mobile beacon node arrives at A, it can detect the wormhole attack as it can check that the communication between itself and
Thus, when the mobile beacon node enters the communication range of an attacker, we can get the following theorem.
Theorem 2.
When the mobile beacon node enters the area of
Proof.
All the beacon nodes inside
Based on Theorem 2, we can get the following corollary.
Corollary 3.
If the mobile beacon node has the same conflicting nodes at two locations, then it is within the communication range of the same attacker.
According to Corollary 3, the mobile beacon node can identify different wormhole attackers easily. For example, as shown in Figure 4, when the mobile beacon node moves to
4.2.2. Enhanced Positioning Scheme
In the basic positioning scheme, when the mobile beacon node moves forward a step, it will conduct the wormhole attack detection, in which it broadcasts a Req message to its neighboring beacon nodes and then waits for the Rep messages from them. Such kind of procedure involves the message exchange between the mobile beacon node and its neighboring beacon nodes, which is energy consuming. In this section, we will propose an enhanced positioning scheme, which can reduce the energy consumption of the positioning procedure.
Since the mobile beacon node moves across the network, it may enter the transmission range of an attacker for more than once. As shown in Figure 5, when the mobile beacon node moves from A to C, it can detect the existence of the wormhole attack after which it can determine the location of the attacker as

The procedure of the enhanced attackers positioning scheme.
5. Performance Evaluation
In this section, we present the simulation results to demonstrate the effectiveness of the proposed wormhole attackers detection and positioning scheme. We compare the proposed scheme with the label-based scheme proposed in [2] as the detection scheme of the label-based scheme is similar to our proposed scheme and it can also estimate the locations of the wormhole attackers. In the simulation, a WSN is randomly deployed in a
Figure 6 illustrates the comparison of the wormhole attack detection probability of our proposed scheme between the simulation and the theoretical model under single wormhole attack. We vary the number of beacon nodes from 10 to 30; that is, the density of the beacon nodes varies from
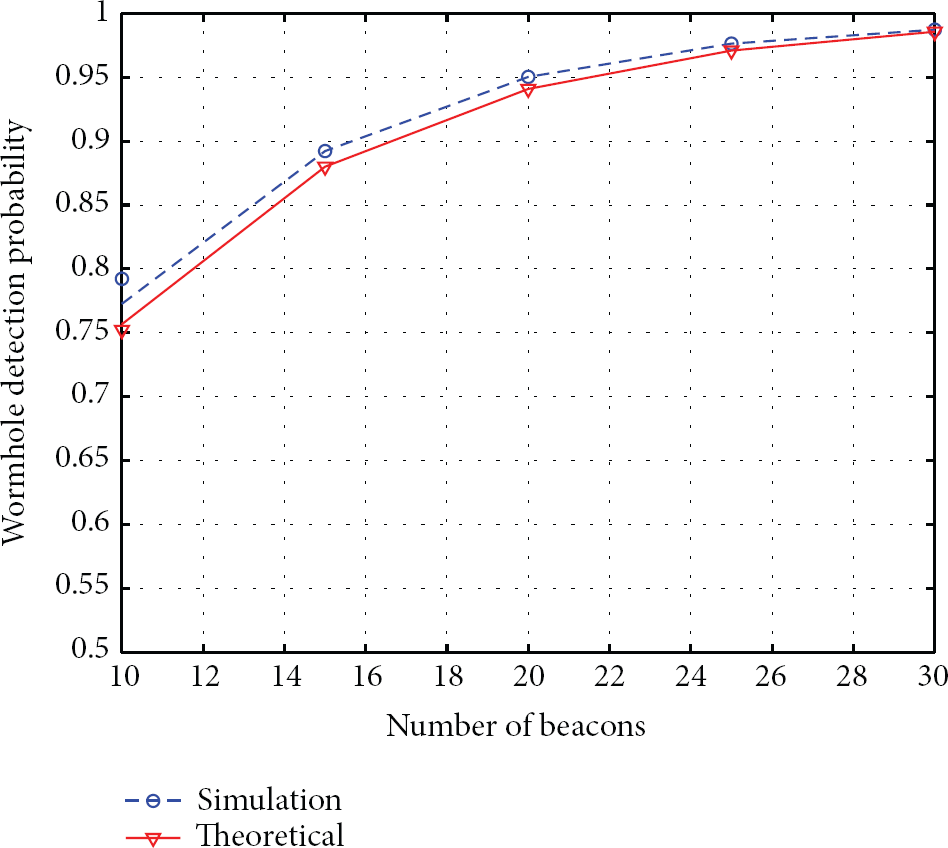
Wormhole attack detection probability: simulation versus theoretical model.
Figure 7 illustrates the wormhole detection probability of the proposed scheme and the label-based scheme when there is only a wormhole attack in the network. In the label-based scheme, the wormhole attack can be detected by checking whether the communications between the beacon nodes violate the properties and the precondition is that there exists at least one beacon node within the communication range of each of the attackers. In our proposed scheme, we select

Wormhole detection probability of the proposed scheme and the label-based scheme with only single wormhole attack.
Figure 8 illustrates the wormhole detection probability of our proposed scheme with different number of wormhole attacks in which the settings of

The effects of the number of wormholes on the detection probability.
Figure 9 illustrates the wormhole attacker positioning error of our proposed scheme and the label-based scheme in which the settings of

The average positioning error of our proposed scheme and the label-based scheme.
Figure 10 illustrates the effects of the moving step lengths

The effects of mobile beacon node's moving step length on the attacker positioning accuracy.
Figure 11 illustrates the comparison of the detection times between the basic scheme and the enhanced scheme under different number of wormholes. The detection times here mean the total times that the mobile beacon node stop to conduct the wormhole attack detection in the whole network. Since the energy consumption in the proposed scheme mainly occurs during the wormhole attack detection, which requires the nodes to exchange messages, we can analyze the energy consumption of the scheme by directly evaluating the detection times. We adopt

The comparison of the detection times between the basic scheme and the enhanced scheme.
The effects of the moving step length

The effects of mobile beacon node's moving step length on the detection times of the proposed enhanced scheme.
6. Conclusions
In this paper, we proposed a novel wormhole attackers detection and positioning scheme, which can not only detect the existence of wormhole attacks, but also localize the attackers with a high accuracy for the system to eliminate them out of the network. The main idea is to detect whether the communication between the mobile beacon and the static beacons violates the communication properties and then the attacker can be localized as the center of its communication disk by finding the intersection point of the chords' perpendicular bisector. The simulation results illustrated that our proposed scheme can obtain a high wormhole attack detection probability together with a high accuracy for localizing the attackers.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work was supported in part by NSFC Grants no. 61309023, no. 61273079, and no. 61272463, Shandong Provincial Natural Science Foundation, China (no. ZR2013FQ032), the Fundamental Research Funds for the Central Universities (no. 13CX02100A), Open Project in Zhejiang Provincial Key Lab of Intelligent Processing Research of Visual Media (no. 2012008), State Key Laboratory of Industrial Control Technology under Grants no. ICT1206 and no. ICT1207, Hong Kong GRF Grants (PolyU-524308, PolyU-521312), and HKPU Grants (A-PL16, A-PL84).