Abstract
This paper develops an efficient and distributed boundary detection algorithm to precisely recognize wireless sensor network (WSN) boundaries using only local connectivity information. Specifically, given any node in a WSN, the proposed algorithm constructs its 2-hop isocontour and locally makes a rough decision on whether this node is suspected to be on boundaries of the WSN by examining the associated 2-hop isocontour. Then, a heuristic operation is performed to refine this decision, with the result that the suspected boundary node set is significantly shrunk. Lastly, tight boundary cycles corresponding to both inner and outer WSN boundaries are derived by searching the suspected boundary node set. Furthermore, regarding WSNs with relatively low node densities, the proposed algorithm is adapted to improve the quality of boundary detection. Even though the proposed algorithm is initially presented under the assumption of the idealized unit disk graph (UDG) model, we further consider the more realistic quasi-UDG (QUDG) model. In addition, a message complexity analysis confirms the energy efficiency of the proposed algorithm. Finally, we carry out a thorough evaluation showing that our algorithm is applicable to both dense and sparse deployments of WSNs and is able to produce accurate results.
1. Introduction
Wireless sensor networks (WSNs), comprised of hundreds or thousands of small and inexpensive (sensor) nodes with constrained computing power, limited memory, and short battery lifetime, can be used to monitor and collect data in a region of interest [1]. Given a WSN, nodes on or near boundaries normally play a more important role than the other nodes. First, these nodes directly interact with the outside environment, such as events entering or leaving the region monitored by the WSN [2–4] and any communication with the outside environment [5]. Second, these nodes help to extract further information about the WSN structure which is useful for routing, guiding, and management purposes [6–10]. Third, due to the correspondence between the boundaries of a WSN and its physical environment, such as a building floor plan, a map of a transportation network, terrain variations, and obstacles (buildings, lakes, etc), these nodes are important for keeping track of the WSN shape which indicates significant features of the underlying environment [11, 12]. Last but not least, in contrast to the outer boundary of a WSN, inner boundaries denote boundaries of inner holes of the WSN and are important indicators of the general health of a WSN, such as insufficient coverage and connectivity [13, 14]; for instance, identifying inner boundaries reveals groups of destroyed sensors due to physical destruction or power depletion, where additional sensor deployment is needed [15]. Therefore, boundary detection is of great importance for various WSN applications, such that considerable efforts have been invested in the development of boundary detection algorithms [16–35].
In this paper, we focus on detecting WSN boundaries by making use of only low-cost connectivity information between neighboring nodes and develop an efficient and distributed algorithm precisely discovering both inner and outer boundaries. At the beginning, we assume that wireless communications satisfy the idealized unit disk graph (UDG) model, where two nodes are connected by an edge if and only if their distance is at most
The remainder of this paper is organized as follows. The next section briefly reviews the literature of boundary detection. Section 3 formulates the problem of boundary detection. Section 4 describes the proposed algorithm in detail, and Section 5 discusses practical issues in relation to applying the proposed algorithm. Section 6 presents extensive simulations to confirm our results. Finally, we conclude this paper in Section 7.
2. Related Work
Normally, boundary detection algorithms can be classified into three categories: geometric, statistical, and topological methods.
Geometric methods [16, 24] use geographical location information to find nodes on boundaries. The first paper on this topic, by Fang et al. [16], assumes that the nodes know their geographical locations and that the wireless channel follows the UDG model. The definition of holes in [16] is intimately associated with geographical forwarding such that a packet can only get stuck at a node on hole boundaries. Fang et al. also proposed a simple algorithm that greedily sweeps along hole boundaries and eventually discovers boundary cycles. Though the geometric method can find more accurate boundary nodes than other two kinds of methods in a WSN, the requirement of node geometric location information limits its application, especially in large scale WSNs.
Unlike geometric methods, statistical methods [17, 19, 21, 29] usually make assumptions about the probability distribution of the node deployment. Thus, boundary nodes can be probabilistically identified based on some statistical properties under certain network conditions. Fekete et al. [17] proposed a boundary detection algorithm for sensors uniformly and randomly deployed inside a geometric region. The basic idea is that nodes on the boundaries have much lower average node degrees than nodes in the “interior” of the network. Statistical arguments yield an appropriate degree threshold to differentiate boundary nodes. By exploiting the number of 2-hop neighbor nodes, Chen et al. [29] proposed an algorithm with a significant improvement in boundary recognition contrasted with Fekete's algorithm in low-density WSNs. Another statistical approach in [19] computes the “restricted stress centrality” of a node, which measures the number of shortest paths going through this node with a bounded length. Due to the fact that interior nodes tend to have higher centralities than the nodes on the boundaries in WSNs with sufficiently high node densities, the centrality thus can be used to realize boundary detection. One major weakness of the statistical methods is the unrealistic requirement on node distribution and density (e.g., the average node degree needs to be 100 or higher in [17]). Another major weakness lies in that the criteria for identifying boundary nodes acquired from the statistical characteristics cannot guarantee finding out boundary nodes precisely.
Topological methods [18, 20, 22, 23, 25, 26, 28, 30, 31, 34] use the topological properties such as the information of connectivity to identify the boundary nodes. Normally, topological method has higher packet control overheard than the previous two methods due to having to collect information from neighboring nodes; however, it does not need location information and has better accuracy of finding boundary nodes than statistical method. Ghrist and Muhammad [18] proposed an algorithm that detects holes via homology; however, the algorithm is centralized, with assumptions that both the sensing range and communication range are disks with radii carefully tuned. Kröller et al. [22] presented a new algorithm by searching for combinatorial structures called flowers and augmented cycles; they make less restrictive assumptions on the problem setup by he quasi-UDG (QUDG) model in which two nodes are connected if their distance is below d (<1), are disconnected if above 1, and may or may not be connected if in between; the success of this algorithm critically depends on the identification of at least one flower structure, which may not always be the case especially in a sparse network.
Towards a practical solution, Funke and Klein [20] developed a simple heuristic with only connectivity information; the basic idea is to construct isocontours based on hop count from a root node and identify where the contours are broken; under the UDG model and a sufficient node density, the algorithm outputs nodes marked as boundary with certain guarantees; the simplicity of the algorithm is appealing, but the algorithm only identifies nodes that are near the boundaries and the density requirement of the algorithm is also rather high. Khan et al. [26] proposed a variant of [20] by examining the 2-hop isocontour of each node and show that if there exists a closed cycle in the 2-hop isocontour of one node, this node is an interior node, and vice versa. Another algorithm proposed by Chu and Ssu [30], similar to [26], relaxes the condition of differentiating boundary nodes from interior nodes and thus identifies more nodes as boundary nodes. Although, these algorithms are as simple as the one in [20], they have the same weakness as well, namely, requiring a high node density, identifying more nodes than actual ones, and not showing how the identified boundary nodes are connected in a meaningful way. The proposed algorithm is also based on examining isocontours of nodes in a WSN but will turn out to produce superior results in contrast to existing algorithms.
3. Problem Formulation
Suppose a large number of (sensor) nodes, say n nodes, are scattered in a 2-dimensional geometric region where nearby nodes are connected with each other to form a WSN. For ease of presentation, we assume that the wireless communications follow the UDG model. This WSN can be modeled as a graph
From the geometric point of view, the outer boundary of the WSN is the minimal closed curve enclosing the graph

The outer and inner geometric boundaries (solid curves) of a WSN. The dashed line denotes communication links.
With the above geometric boundaries, we can readily define boundary nodes as follows. First, nodes belonging to boundaries are definitely boundary nodes. Second, if any segment is involved in a boundary, edges and nodes belonging to this boundary will not be able to form a (closed) boundary cycle corresponding to this boundary, so that extra nodes must be incorporated as boundary nodes. Existing works [22, 23] search for the shortest path between the pair of boundary nodes which are the ends of a segment or a series of connected segments of a boundary and group the nodes along the shortest path into boundary nodes. For example, nodes 1 and 2 in Figure 1 do not lie on any boundaries but are also regarded as boundary nodes so as to form boundary cycles. As opposed to boundary nodes, all the other nodes are named interior nodes. In principle, the task of boundary (and hole) detection is to identify boundary nodes and then construct corresponding boundary cycles.
As pointed out in [25], a connectivity domain description of a WSN (e.g.,
For clarification, we call the nodes belonging to boundaries as actual boundary nodes and call the other nodes as actual interior nodes. Therefore, using given local connectivity information, our goal is to approximately discover a boundary node set, including not only actual boundary nodes but also some actual interior nodes near WSN boundaries, to try to reduce the size of the boundary node set and further to extract precise boundary cycles from the discovered boundary node set.
4. Proposed Boundary Detection Algorithm
The basic idea of the proposed algorithm is firstly identifying a set of suspected boundary nodes, then refining them, and lastly searching them for tight boundary cycles. The outline is listed below.
Each node, say node After exchanging the values of Each suspected boundary node, say node The suspected boundary nodes cooperatively search for boundary cycles based on their values of

Snapshots of each step during the execution of the proposed algorithm in a WSN with the average node degree of 18.8 and with a circular hole. (a) The Node deployment in the WSN. (b) The snapshot after initializing
In what follows, we will describe each step of the proposed algorithm in detail. Due to the fact that the power at each node in WSNs is limited and message transmission is the main source of energy consumption, we also provide a message complexity analysis of the proposed algorithm at each step. For ease of analysis, we suppose that the considered WSN is synchronized, for example, using the methods in [36, 37], and message transmission is collision-free.
4.1. Initializing
In this step, node
The function
procedure (1) Construct (2) Index nodes in (3) (4) (5) (6) (7) (8) (9) (10) (11) (12) (13) (14) (15) (16) return (17) (18) (19) (20) (21) (22) (23) (24) (25) (26) (27) (28) (29) (30) (31) (32) (33) break (34) (35) (36) return 1 (37)
In the implementation of the function
According to the CLOSED-CYCLE condition, nodes with
In this step, each node needs to broadcast three messages so as to construct the required subgraph
4.2. Performing the Erosion Operation
After the initialization of
Observations indicate that a majority of 1-hop neighbor nodes of actual boundary nodes have
The erosion operation only demands that each node exchanges
4.3. Determining
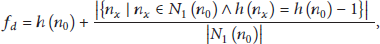
In this step, we define a new local variable, denoted by
To compute
It is evident that the greater
To determine
4.4. Searching for Boundary Cycles
In order to present our result in a meaningful way, we strive to obtain precise boundary cycles corresponding to both inner and outer boundaries of the WSN. To do so, the proposed algorithm searches all the suspected boundary nodes based on the same principle of the function
First, unlike the function
Second, node is arbitrarily expanded in the function
Like
With boundary cycles, it is straightforward to distinguish an outer boundary from each inner boundary by comparing the lengths of their corresponding boundary cycles or by comparing the length of each boundary cycle with the perimeter of the WSN which can be roughly estimated based on the deployment information. Moreover, we can further refine the set of suspected boundary nodes by excluding the nodes which are more than 1-hop to boundary cycles.
Due to the possible conflicts caused by concurrent search processes, it is extremely difficult to analyze the message complexity of this step. In the ideal case that each suspected boundary node is expanded at most once, the number of messages is limited by the size of the suspected boundary node set and thus has the order of
To sum up, we can conclude that the message complexity of the proposed algorithm is
5. Practical Issues
In this section, we will discuss two practical issues in relation to applying the proposed algorithm.
5.1. Working with Realistic Channel Models
The algorithm is proposed in the idealized UDG model. Although the UDG model is simple, practical wireless communications can never satisfy it, and, hence, more realistic channel models, for example, the QUDG model, are developed. With the QUDG model, it is possible that the 2-hop isocontours of some actual boundary nodes can form closed cycles so as to satisfy the CLOSED-CYCLE condition, and, as a result, they are mistakenly identified as interior nodes (e.g., the boundary nodes with red circles in Figure 7(a)), which degrades the quality of the proposed algorithm.
Provided that an actual boundary node is identified as an interior node due to
On these grounds, we design another heuristic operation, termed dilation, which to some extent is similar to the dilation operation in image processing, to adjust the value of
If the dilation operation is performed, additional message transmission is required. Specifically, n messages are transmitted for the dilation, with the result that the total message complexity is increased by
5.2. Working with Low Node Densities
With decreasing the node density (e.g., by reducing the communication ranges), the number of 2-hop neighbor nodes of any node in a WSN is generally reduced, so that it becomes difficult to have the CLOSED-CYCLE condition satisfied, and, as a result, a portion of actual interior nodes are mistakenly grouped into the set of suspected boundary nodes, which remarkably damages the performance of the proposed algorithm. Therefore, we must alter our algorithm to be suitable for low-density WSNs.
One intuitive approach is including more neighbor nodes in the construction of the isocontour at each node. To do so, we can replace the original graph
On replacing
If power graphs are used in our algorithm, the messages transmitted are
6. Performance Evaluation
We carry out extensive simulations in various scenarios, with the goal to evaluate the performance of the proposed algorithm with respect to the node density and distribution, the wireless channel model, existing boundary detection algorithms, and so forth.
6.1. Effect of Node Density
In this simulation, we assume the UDG model and deploy 2700 sensor nodes according to a uniform and random distribution in a square region of size 240 m with one circular hole of radius 50 m, which is the same as the WSN shown in Figure 2. The average node degree of the graph is varied by adjusting the communication radius of the UDG model. The choices of
As illustrated in Figures 3 and 2(d), the proposed algorithm generates precise boundary cycles in general. Moreover, it can be observed that the larger the average node degree is, the more accurate the suspected boundary nodes are, the tighter the boundary cycles are, and, hence, the better the performance of the proposed algorithm is. The underlying reason is that a larger node density increases the possibility of forming a closed path enclosing each interior node due to having more 2-hop neighbor nodes and thus lowers the chance of mistakenly identifying interior nodes as suspected boundary nodes.

Results of applying the proposed algorithm in a WSN with a circular hole: (a) the average node degree is 15.6; (b) the average node degree is 22.4.
In the simulation, when the average node degree is below 14, the proposed algorithm cannot correctly recognize the boundaries due to insufficient connectivity. Faced with this situation, we use the second power graph instead of the original graph in the function of

Using the power graph instead of the original graph to improve the performance of the proposed algorithm. The average node degree is 9.2.
Furthermore, we plot the results of applying the proposed algorithm in a couple of WSNs with interesting shapes in Figure 5.

Results of applying the proposed algorithm in two WSNs with interesting shapes. (a) The average node degree is 18.1; (b) the average node degree is 19.2.
6.2. Perturbed Grid Node Distribution
We still assume the UDG model but deploy 2700 sensor nodes on a grid of size 4 and perturb the position of each node by an independent and identically distributed random shift. The random shift is described by a pair of random variables with a uniform distribution in
As illustrated in Figure 6, the proposed algorithm attains satisfactory results even if the average node degree is as low as 10 or 7 when using the power graph. Compared with the uniform and random node distribution, the perturbed grid node distribution has nodes deployed in a more symmetrical fashion, reduces the risk of having clusters and small holes, and consequently displays a superior performance.

Results for perturbed grid node distribution. (a) The average node degree is 7; (b) the average node degree is 10.

Results under the QUDG model. The average node degree is 16.5.
6.3. QUDG Model
In this simulation, we implement the proposed algorithm with the dilation operation under the QUDG model. Specifically, we use the same WSN as simulated in Figure 2 but assume that two nodes are connected if their distance is below 8 m and are disconnected if above 13. The choice of
As shown in Figure 7(b), the two actual boundary nodes surrounded by red circles, which are identified as interior nodes after the first step of our algorithm, are corrected to be suspected boundary nodes by the dilation operation and are finally included in the boundary cycles. Consequently, both the outer and inner boundaries are accurately detected.
6.4. Comparison with Other Methods
For comparison, we implement another three typical connectivity-based boundary detection algorithms [20, 23, 30]. In this simulation, we consider the same WSN that is simulated in Figure 2.
As can be seen in Figure 8, the algorithm in [20] can only identify a small portion of actual boundary nodes but cannot correctly find boundaries of the WSN; the algorithm in [30] can identify all the actual boundary nodes but mistakenly include many actual interior nodes. In contrast, the proposed algorithm obviously delivers superior results and appears to achieve nearly the same successful rate as the algorithm in [23], as shown in Figure 2.

7. Conclusions
In this paper, we developed an efficient, distributed, and connectivity-based boundary detection algorithm for WSNs. Our algorithm first identifies suspected boundary nodes by examining whether a closed path exists in the 2-hop isocontour of each node and encloses this node. Then, the erosion operation is applied to heuristically shrink the suspected boundary node set. At last, precise boundary cycles corresponding inner and outer boundaries are obtained and provide much valuable knowledge as to the boundaries of WSNs. In order to have the proposed algorithm work normally in low-density WSNs, we replaced the original graph of a WSN by its power graph in the first step of the algorithm. Moreover, we expanded our algorithm from the idealized UDG model to the more realistic QUDG model by introducing the dilation operation. In addition, a message complexity analysis confirmed the energy efficiency of our algorithm. Finally, we carried out a thorough evaluation verifying the accuracy of our algorithm and its applicability in both dense and sparse deployments of WSNs.
However, there are certain restrictions in applying the proposed algorithm. As shown in Figure 2(b), for each boundary, a certain “thickness” of nodes are discovered as suspected boundary nodes. When two boundaries are very close to each other, their relevant suspected boundary nodes are often connected, with the result that the proposed algorithm cannot separate them to correctly identify any of them. Empirically, any two boundaries should be at least 5 hops away from each other. Moreover, the proposed algorithm is not suitable for recognizing those holes with small perimeters.
In future work, we would like to discover more topology information (e.g., skeleton) of WSNs based on the proposed algorithm and to apply the proposed algorithm in more complicated scenarios, for example, 3-dimensional WSNs.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work is supported by the Natural Science Foundation of Inner Mongolia under 2014MS0604, the Program of Higher-Level Talents of Inner Mongolia University under 125124, and the Inner Mongolia Autonomous Region Science and Technology Innovation Guide Reward Fund Project under 20121317.