Abstract
Since the SDN (Software Defined Network) technology based on OpenFlow was born, domestic and foreign research institutions have had increasing attention to this emerging field. The OpenFlow technology which is known for standardization and compatibility network virtualization has brought a lot of innovative solutions in the field of research. As the wireless sensor network node is complex and difficult to move and the network topology is changing rapidly with time, this requires a routing protocol for it to be able to adapt to this high topology change. Because traditional WSNS protocol communication needs to consider energy consumption, load balancing and other factors, it is difficult to find one to take into account all aspects of network algorithms. In this paper, we put forward a new solution for WSNS in accordance with the OpenFlow technology research in the application of traditional network.
1. Introduction
With the development of wireless communications, electronics and sensing technology, wireless sensor network (WSN) has attracted widespread attention [1]. WSNs are composed of the sensor with functions of sensing, data processing, and short-distance wireless communication. In military defense, disaster relief, environmental monitoring, biological and commercial applications, and other fields have broad application prospects [2].
1.1. WSN Routing Technology
Routing protocol is one of key technologies in wireless sensor network and is presently one of the hotspot research problems. In multiple hops network, source node cannot send the data packet to the destination node directly and only leans on the help of intermediate nodes to forward these grouped data. In the network intermediate nodes (including source node) must correctly determine which neighboring node to send the received data packets to and to find the shortest path to enable it to reach destination along the shortest path [3].
Traditional ad hoc network focused on high-quality and efficient communication; therefore, the design goal of routing protocol is to find the shortest communication delay between two nodes, to improve the utilization of network bandwidth, and thus to avoid traffic congestion caused by routing loops and at the same time to control the number of intermediate forwarding about multihop communication and balance network traffic.
WSN have the traditional characteristics of the wireless network does not exist. It is far from the center of the network, in the architecture, addressing method, the communication mode, and routing structures which are different from the traditional network. Compared with common networks, sensor networks have more nodes. The nodes is very difficult to move but its network topology showed a strong nonstationary, which requested that its high routing protocol must be able to adapt to the topology changes [4].
WSN node has no energy supplement and its energy is constrained. In order to improve the network's lifetime, routing protocols must be involved in reducing energy consumption and load balancing. According to the literature [5–13] we classify routing protocols. Based on wireless sensor networks and the various similarities and differences between traditional networks, the existing routing protocols for wireless sensor networks have the following characteristics.
(1) Limited Energy. Wireless sensor network node is numerous, mobility is weak, and energy supplement cannot be timely, so the energy consumption is one of the challenges of wireless sensor network.
(2) Local Topology Information. Because the energy is limited, how to save energy and ensure the efficient of routing mechanism is a big challenge for WSN.
(3) High Topology Changes. Compared with common networks, sensor networks have more nodes. The nodes is very dofficult to move but its network topology showed a strong nonstationary, which requested that its high routing protocol must be able to adapt to the topology changes.
(4) Big Data Redundancy. In the existing wireless sensor network, due to the random distribution of nodes, Node has no special logo, multiple nodes simultaneously to collect the same data redundancy information is great.
(5) Application Specific. Applications of wireless sensor network environment vary widely, so there is no routing mechanism suitable for all applications: different applications need to adopt different systems.
1.2. Classification of WSN Routing Protocols
According the number of paths in the transmission process, Routing protocols can be divided into single-path routing protocol and multipath routing protocol. According to the node differences in the hierarchy and the role during the routing process, Routing protocols can be divided into flat routing protocols and hierarchical routing protocols. According to the relationship between the route when established and data transmission Routing protocols can be divided into proactive routing protocols and hybrid routing protocols. According to whether the location is identified based on the destination and if the route calculation uses the location information, Routing protocols can be divided into location-based routing protocol and non-location-based routing protocol. According to whether they identify the destination by the daa, can be divided into routing protocols based on data and the routing protocols not based on data. According to whether the node addressing, whether to identify the destination addresses the routing protocols can be divided into data aggregation and non-data aggregation. According to the choice of routing whether considering the QoS constraints, the routing protocols can be divided into guaranteed QoS routing protocols and not guaranteed QoS routing protocols. According to whether the process of data transmission deals with aggregation, the routing protocols can be divided into data aggregation and non-data aggregation. According to whether the routing is designated by the source node, the routing protocols can be divided into source station and passive station. According to whether the routing time is involved in the query, the routing protocols can be divided into query driven routing protocols and non-query-driven routing protocols.
Because of the great number of sensor nodes and high density, sensor node energy, computing power, and storage capacity are limited; network topology changes frequently and has the self-organizing ability. When choosing wireless sensor network routing protocol we need to take into account the node energy, the communication load balancing, routing protocol fault tolerance, routing protocol security mechanisms, and so on. It is difficult to design a kind that has the most efficient wireless sensor network routing protocol.
2. The Key Components and Architecture of OpenFlow Based on SDN
The control logic of traditional Internet and data forwarding tight coupling device on the network, resulting in network control plane management of complex, but also makes updating and development of the network control plane is difficult to directly deploy new technologies on existing networks, flexibility and scalability difficult to adapt to the rapid development of the network. Network control forward separation architecture proposed by proprietary equipment deployment of high-level strategy, under the guidance of senior policy data forwarding, can be done. And it reduces the network equipment of many complicated functions, and at the same time, it can also improve the flexibility and operability of the network based on the new technology. This control logic control and data forwarding thinking separation technology research foundation SDN. Initially OpenFlow is put forward as a prototype of SDN [14], it mainly has two parts, OpenFlow switch and controller. OpenFlow switch forwarding packets according to the flow table represents the data forwarding plane; controller achieves the control function through the network view. The control logic represents the control plane [15].
The rapid development of the Internet can be attributed to the TCP/IP architecture and open application layer software design. However, due to the particularity of hardware devices, WSN is largely closed. In wireless sensor network, we put forward a model of wireless sensor network based on OpenFlow/SDN. The control function of the traditional distributed network equipment will be migrated to the controlled computing devices. The underlying network infrastructure can be abstracted by upper-layer network services and applications [15]. At last, it through the open programmable software pattern realizes the automation of network control function. This model consists of three basic roles: master node, center node, normal node. The master node as the controller of the network structure (programmable control unit of the central executive) according to the control unit (including topology, transmission capacity, and routing restrictions) will decide how to achieve synergy and interaction between nodes for themselves. The function of center node is similar to the OpenFlow switch. It is responsible for matching and forwarding data stream in the wireless sensor network. The responsibility of normal node is only to receive data flow [16].
2.1. Master Node/Controller
In the Software Defined Network, the controller is the core of the network NOS (network operating system) to realize control logic function. NOX is the programmable controlled central execution unit of the OpenFlow network. In fact, as shown in the Figure 1 in this case, the NOX is the control software of SDN. It can achieve different logic control functions by running different applications on NOX.

NOX-based OpenFlow network.
In wireless sensor network (WSN), we give the master node as a controller. In the WSN based on the OpenFlow/SDN, master node is the core of the network, and center node is the operating entity, NOX, by maintaining the basic information of the network view to maintain the entire network. Like topology, the network unit provides services. The application runs on the top of NOX by calling the global data network view to operate center node to the entire network. In the Software Defined Network [4].
In order to make the controller able to be directly deployed in real networks and solve the problem of multiple controllers to OpenFlow switch control sharing, at the same time, as shown in Figure 2 the controller should meet the real needs of network virtualization and FlowVisor has implemented the network virtualization layer based on OpenFlow between the controller and OpenFlow switch. It makes hardware forwarding plane able to be shared by multiple network logical slices. Each section has a different logical strategy forward. In this slice mode, multiple controllers can manage a switch at the same time, and network administrator can control network in parallel. Therefore, normal network traffic can run on a separate slice mode, thus ensuring the normal flow uninterrupted. In traditional WSN routing protocol, the node is also facing resources implosion problem (one node receives multiple copies of data from neighbor nodes almost at the same time) and overlapping (node has received the same data from the same area). The problems of center node can be solved based on this biopsy strategy.

FlowVisor based OpenFlow virtualization.
2.2. Center Node/OpenFlow Switch
As shown in Figure 3 OpenFlow switch is responsible for data forwarding function. Main technical details are made up of three parts: flow table, secure channel, and OpenFlow protocol.
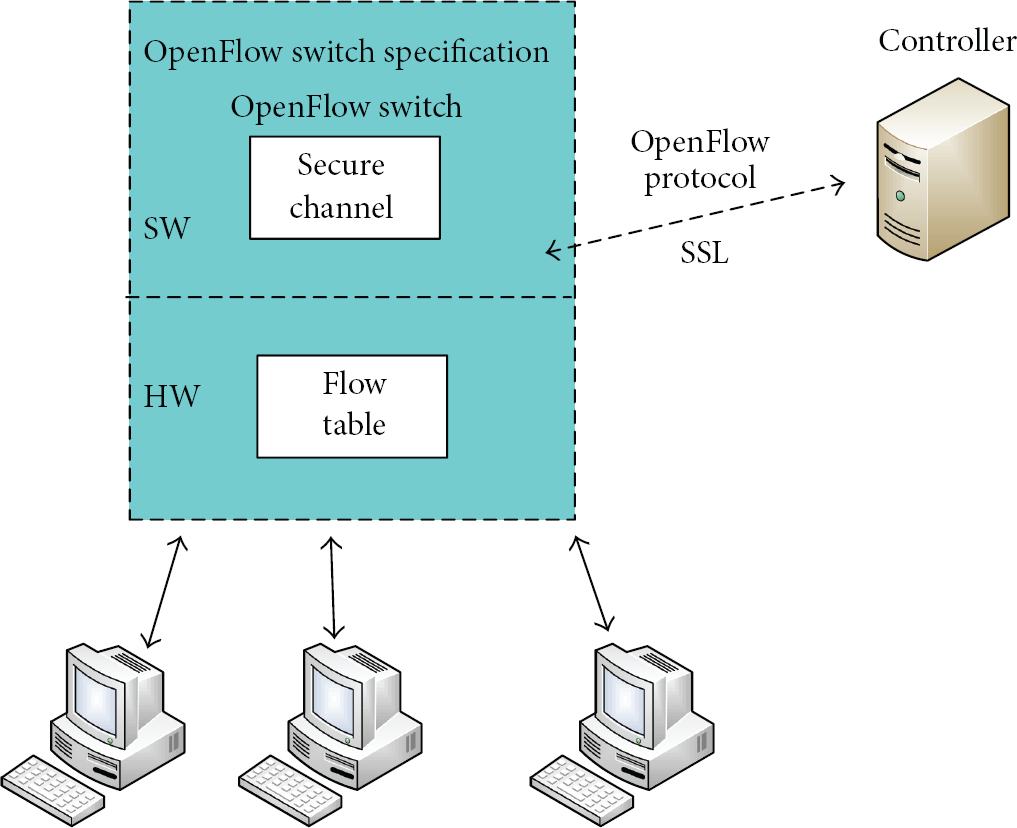
OpenFlow infrastructure.
Each OpenFlow switch processing unit consists of flow table, and each flow table is made up of many flow table entries. Flow table entry represents the forwarding rules. In order to enhance the efficiency of the query traffic,the current flow table query through multistage flow table and pipeline mode. Flow table item is mainly composed of match fields,counters and instructions. The structure of matching field contains a lot of matchs, as the link layer,network layer and transport layer identifies. The counter is used for statistical basic data stream. Action represents the data packets which have been matched with the stream table entry and should perform the next step. Secure channel is an interface that can connect OpenFlow switches to controllers. Through this interface, we can configure and manage OpenFlow switches by the format specified of OpenFlow protocol. Besides matching flow table item, center node needs to identify various existing WSNS routing protocols, by reserved interface it is convenient for extensions in the future [17].
3. A Typical WSN Based on OpenFlow Network Structure
As shown in Figure 4 The main ideas of this network architecture are that center node can be controlled by the master node, the specific forwarding strategy entirely depends on the master node, the whole message link is completely controllable, when normal nodes have some abnormal conditions such as energy depletion and fault conditions, the master node can adjust strategy or change the forwarding path.

A typical WSN based on OpenFlow network structure.
The core of this framework is the information dissemination strategy. The master node can establish a transmission path for the information according to the QoS of the information. The master node through the secure channel among the center node and master node can generate flow table.
When the center node first received the information forwarding requests, the center node matches the flow table information and will feed the node information back to the master node. After it receives the feedback information, the master node begins to construct an optimal forwarding policy based on the information of QoS and the network topology maintained by the center node. When the master node has chosen a path, the center node will be informed through the flow table to be added to it. When the information arrives at the center node, the message can be forwarded according to the strategy that has been built. Because the forwarding strategy is the optimal path chosen by the QoS, node status, and the network topology, the message forwarding efficiency will be very high. When the information is sent over and the next flow of information arrives, the center node will check the flow table at first. If the information can be matched with the last, it means the QoS, node status, and the network topology are consistent with the previous one. There is no need to construct a new forward path. If the flow table exists, flow table entry cannot be forwarded, center node will feed the information back to the master node and request the construction of a new path.
Since every information forwarding has selected the optimal strategy and fully controllable, the stability and efficiency of the network are much higher than traditional WSN routing protocol.
4. WSN Network Center Node Deployed
In order to avoid the problem that the location of the center node unreasonable such as concentration or in the network edge, literature [18] suggests an algorithm. The center node location improvement by a distance-aware route algorithm for cloud computing is based on CAN. As shown in Figure 5 In order to measure the distance between two points, we introduce the cosine similarity to compare and calculate the similarity of two primary frequency plots, and then we can calculate the distance between two points. Frequency plot is the quantitative expression of the relative position based on the CDN network. It is a set of n-dimensional vector. It recorded the redirection information in a fixed time interval from the CDN network.
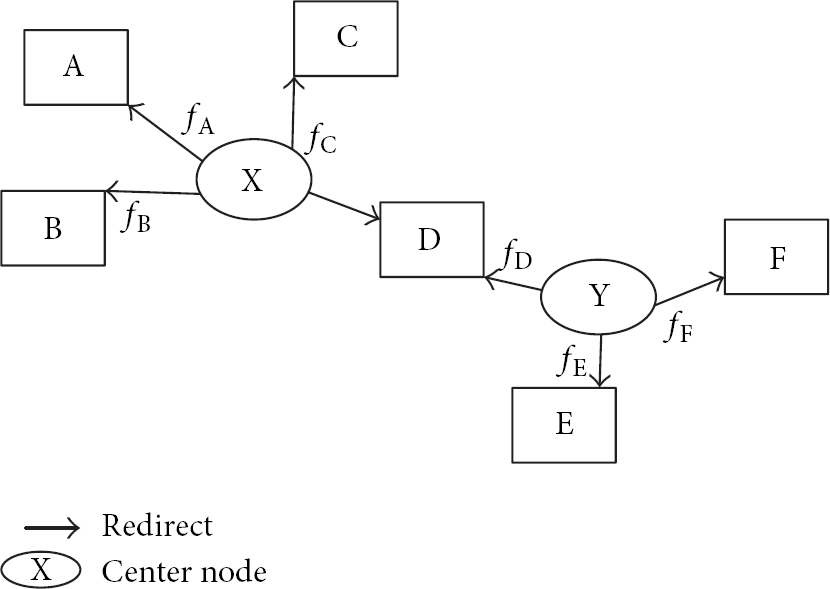
The relative position to determine.
In accordance with the cosine similarity formula, we put the vector a and the vector b, respectively, into the formula; we obtained two primary frequency figures a and b as follows:
Center node. As shown in Figure 6 Center node is the physical center of the area representative clustering; center node can locate areas by junior or senior frequency diagram, based on the measurement system, only when the physical distance between the nodes and center node is less than certain value. This node is in center node area. Regional Unified Virtual Radius. When nodes are less than MaxPeer already in the area, we need to set a uniform distance d, with a constant value as a screening normal node reference. Regional unified virtual radius d is a variable, and it can be set according to the size of the network and the demand.
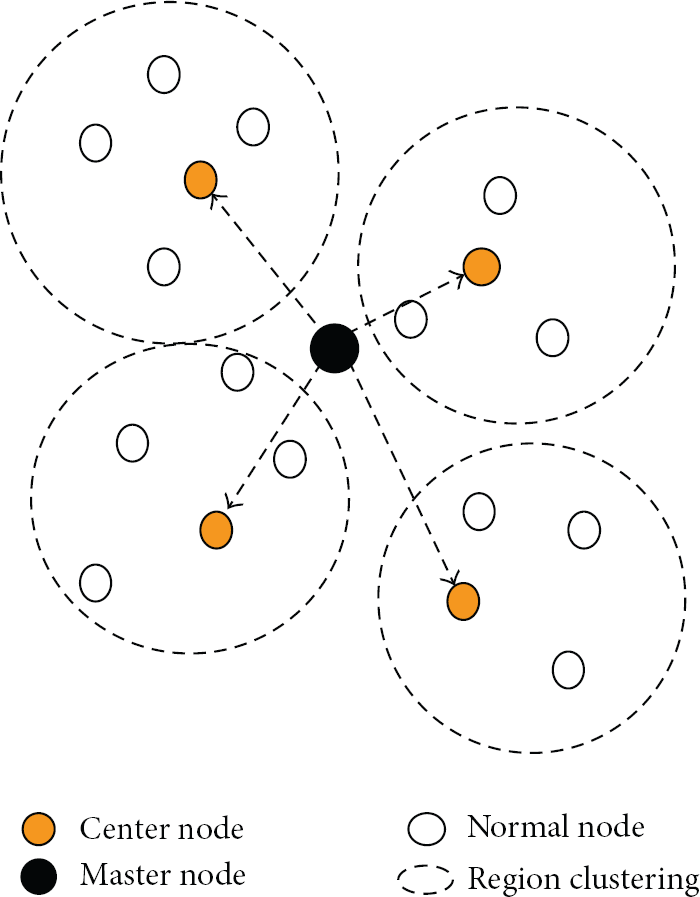
A master node in its control unit structure.
5. Experiment Results
In order to verify the effectiveness of the network structure in this paper, we use a professional experiment tool MATLAB and put the results compared with the traditional routing protocol. The sense for the experiment as nodes distributed in an area 100 m × 100 m; the node number is 100; the master node/base station is located in the center region and the energy can be supplied:
initial energy message size 4000 bit,
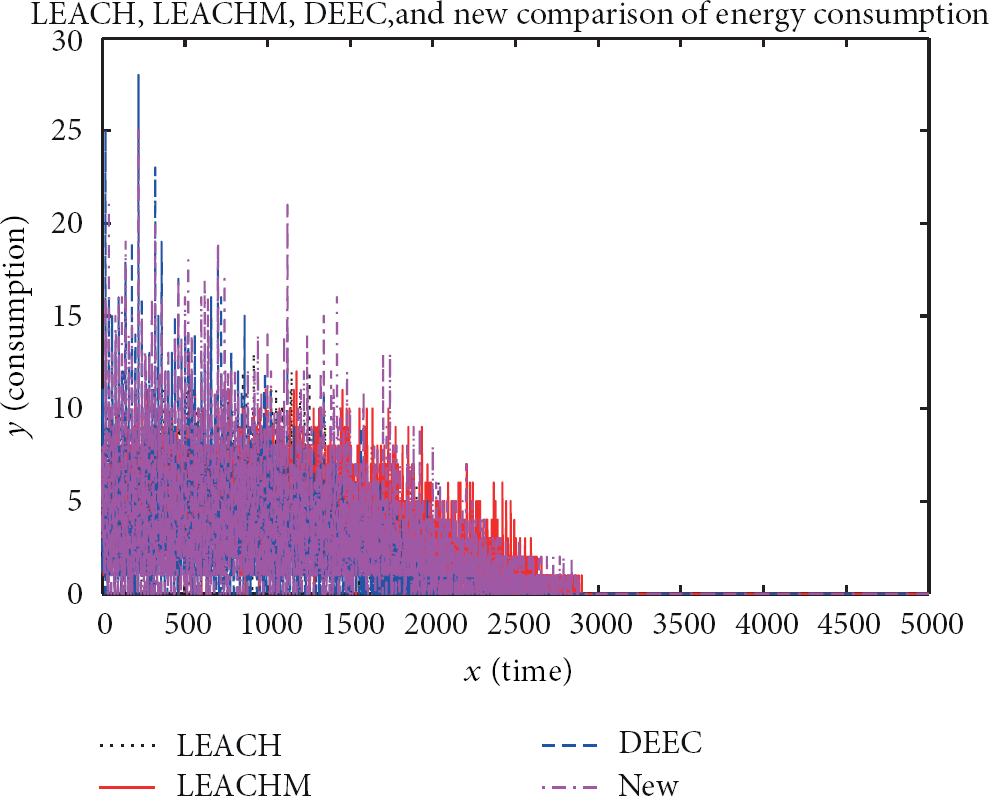
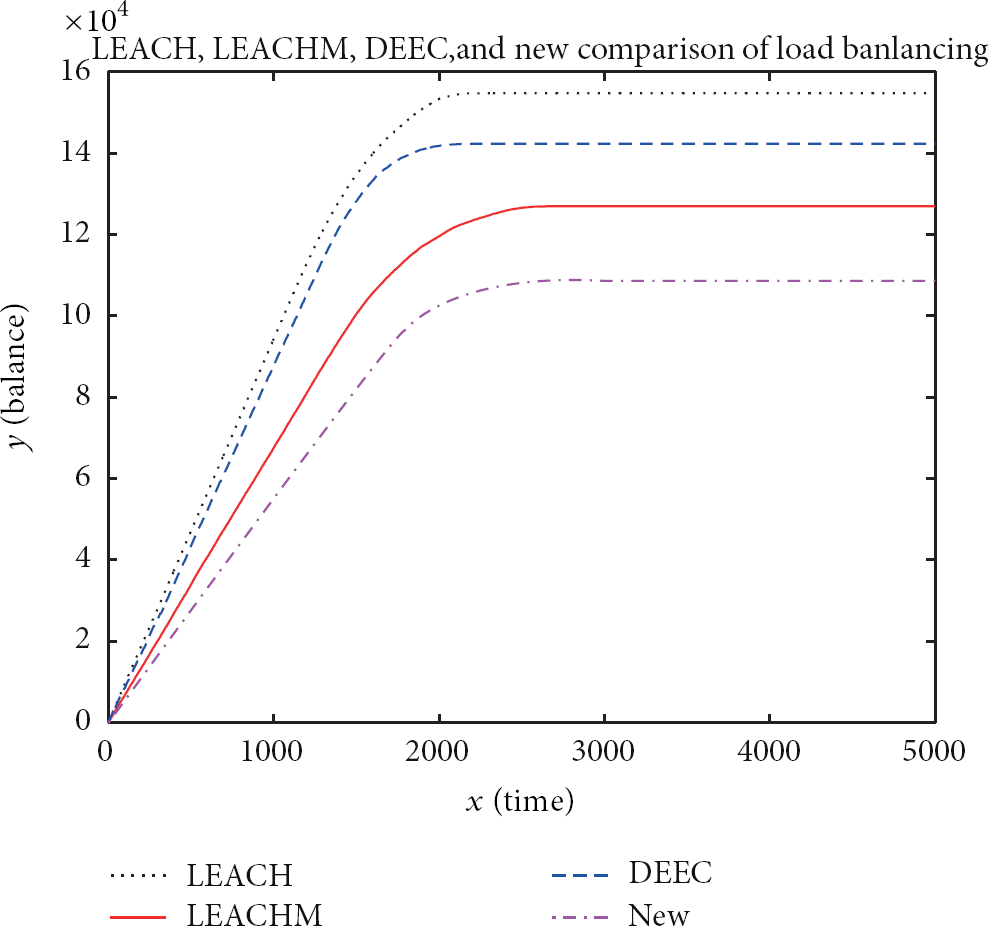
In order to facilitate the comparison with LEACH, LEACHM, and DEEC routing protocol, we ignore the influence of random factors such as wireless channel interference. We can get Figure 7 when the network is performed 5000 times and we compared the WSN structure based on the technology of SDN with the LEACH, LEACHM, and DEEC.
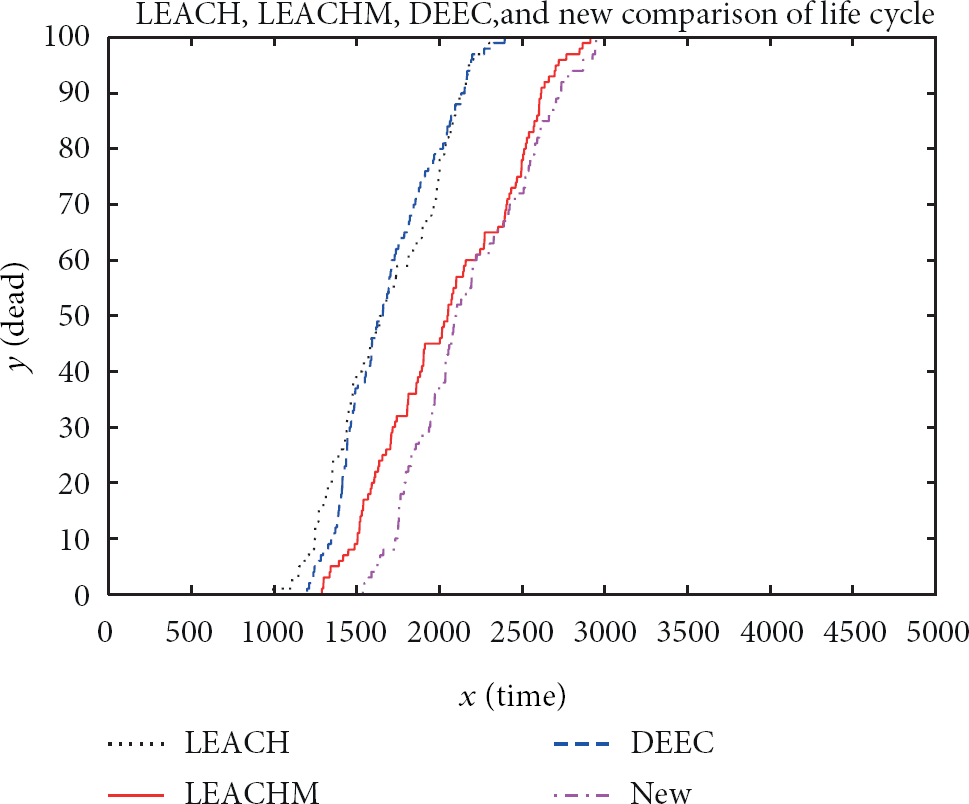
From Figure 7 we can compare the difference of the number of death nodes between the new structure and the traditional routing protocols. The death node appeared when LEAC, LEACHM, and DEEC protocol execution are 1000–1300 times. When the system runs 2500 times, all of the nodes are dead and when it uses DEEC protocol, the system runs 3000 times. The death node appeared when the system ran the new structure and all of the nodes died when it ran 3000 times. So we can see that, compared with traditional routing protocol, the new structure is more stable.
From Figure 8 we can see the changes of energy consumption, the new structure is relatively stable and remains on a lower power consumption level on the node. When the network topology changes, some nodes has high instantaneous energy consumption, but the network has a long life. The traditional LEACH protocol energy consumption is relatively stable in the early times, with the selection of cluster head and changes of the network topology; the energy consumption was exhausted when it runs 2500 times. We can see that though some nodes have high instantaneous energy consumption, the life of the network is longer than that of the traditional routing protocols.
From Figure 9 we can see the load balancing of the new structure is lower than others, the highest load balancing rate of the new structure is 1, and the rate of LEACH protocol is 1.5, another two rates between 1 and 1.5.
From Figure 10 we can see that the new structure has a great advantage in the data transmission. In the process of work, LEACH and LEACHM protocol need to select the clusters heads several times; due to the limitations of the protocol they cannot guarantee the efficiency of the network and the nodes. In the early stages of the network lifetime, the traditional LEACH protocol and DEEC protocol can maintain a higher coverage. but with the energy depletion of the nodes, the position of cluster head has changed. Network coverage decreased rapidly, so the whole life of the network is very short. The WSNS structure is based on the SDN. Because center nodes have relatively fixed position and they can flexibly choose routing protocol according to the change of network topology, the network coverage can maintain a high level. The whole network maximum to avoid the waste of energy. From Figure 7 we can see that, compared with the traditional routing protocols, the new structure has brought very big rise.

6. Conclusion
Because many factors should be considered when we design routing protocols such as node energy, load balancing, and network topology changes, under the original design concept, it is difficult for us to design a routing protocol that can be suitable for all situations. In this paper, a kind of WSN structure based on the technology of SDN is a good solution to these questions. However, we have some problems to solve such as the energy limit of center node and master node, normal nodes are missing, node zoning and so forth. Next step We will design algorithm to solve these problems.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgment
The work supported by the National Natural Science Foundation of China (Grants no. 61103195, and no. 61373137).

