Abstract
The user authentication scheme in ubiquitous wireless sensor networks (WSNs) is an important security mechanism that allows users to access sensors through wireless networks. Therefore, many user authentication schemes in ubiquitous WSNs have been proposed. However, many user authentication schemes are vulnerable to impersonation attacks, parallel session attacks, password guessing attacks, stolen smart card attacks, and so forth. In this paper, we propose a secure and efficient user authentication scheme for use in ubiquitous WSNs. Our proposed scheme is secure against various attacks and provides mutual authentication and session key establishment. Furthermore, our proposed scheme is efficient at using the hash function and exclusive-OR operation.
1. Introduction
In a ubiquitous wireless sensor network (WSN), a sensor is configured as a network. WSN technology has been actively researched globally and has expanded into a ubiquitous paradigm that can access a computing environment anytime and anywhere [1–3]. The main characteristics of a WSN include the following: power consumption constraints for nodes using batteries or energy harvesting, ability to cope with node failures, mobility of nodes, communication failures, heterogeneity of nodes, scalability to large-scale deployment, ability to withstand harsh environmental conditions, and ease of use [4].
WSN-related software platforms such as TinyOS [5], Nano-Qplus [6], Contiki [7], and LiteOS [8] support a variety of standards and protocols. WSN-related standards include 6LoWPAN [9] by the Internet Engineering Task Force (IETF), ROLL [10] by the IETF, CoRE [11] by the IETF, ZigBee [12], Wireless HART [13], and ISA 100 [14].
Some applications of ubiquitous WSN technology include area monitoring, environmental/earth monitoring, industrial monitoring, agriculture, passive localization and tracking, and smart home monitoring [15, 16]. In these applications, the ubiquitous WSN must have a user authentication scheme in which the user has secure access to the sensor nodes. As a result, many user authentication schemes have been proposed for ubiquitous WSNs. However, the existing proposed schemes are vulnerable to various attacks and are not efficient. Therefore, in this paper, we propose a secure and efficient user authentication and key-establishment scheme for use in ubiquitous WSNs.
This study is organized as follows. Section 2 describes related work, and Section 3 proposes a secure and efficient user authentication scheme for ubiquitous WSNs. In Section 4, we analyze and compare related work. Section 5 presents our conclusion.
2. Related Work
In 2004, Watro et al. [17] proposed TinyPK, a user authentication scheme that uses RSA and the Diffie-Hellman algorithm. However, Das [18] proposed that TinyPK is vulnerable to “masquerade as sensor node to an unknowing user” attack. In 2006, Wong et al. [19] proposed a dynamic strong-password-based scheme to address this access control problem and adapted it into the WSN environment. Their scheme imposes a very light computational load and requires simple operations, such as a one-way hash function and exclusive-OR. Unfortunately, Das also proposed that in Wong et al.'s scheme, many logged-in users are vulnerable to the same login-id attack and stolen-verifier attack.
Das [18] proposed a user authentication scheme that eliminates the weaknesses of Wong et al.'s scheme and provides better security and efficiency. Later, Nyang and Lee [20] found that Das's scheme is vulnerable to an offline password guessing attack by insiders and showed a security-enhanced user authentication scheme to overcome this vulnerability without sacrificing efficiency and usability.
In 2010, He et al. [21] demonstrated that Das's scheme suffers from insider attacks and impersonation attacks, and users cannot change their passwords. As a solution to these weaknesses in Das's scheme, He et al. [21] proposed an enhanced two-factor user authentication scheme. In the same year, Khan and Alghathbar [22] found that Das's scheme is vulnerable to gateway (
Further, Huang et al. [24] found that Das's scheme is still vulnerable to masquerade attacks and cannot provide user anonymity, so they proposed an improvement to remedy these weakness. In addition, Vaidya et al. [25] showed that both Das's scheme and Khan and Alghathbar's scheme have flaws and remain vulnerable to various attacks including stolen smart card attacks. Thus, they proposed an improved two-factor user authentication that is resilient to stolen smart card attacks as well as other common types of attacks. Chen and Shih [26] found that Das's scheme cannot provide mutual authentication. To address this problem, they proposed a robust mutual authentication scheme for WSN. Recently, Xue et al. [27] proposed a temporal credential-based mutual authentication and key agreement scheme for WSNs.
3. The Proposed Scheme
In this section, we propose a secure and efficient user authentication scheme for use in ubiquitous WSNs. The
3.1. Notation
Table 1 summarizes the notation used to describe our proposed scheme.
Notation of our proposed scheme.

3.2. Registration Phase
Figure 1 illustrates the procedure of the registration phase. When a new user

Registration phase of our proposed scheme.
Step R1
Step R2 
Step R3.
3.3. Login Phase
If the user
Step L1.
Step L2. The smart card computes
Step L3. The smart card computes the following:

Step L4
3.4. Authentication and Key Establishment Phase
The procedure that is followed in the authentication and key establishment phase is illustrated in Figure 2. After receiving the login request message

Login and authentication and key establishment phase of our propose scheme.
Step A1 (the 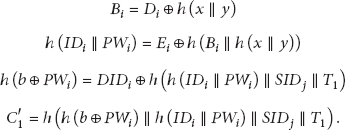
Then the 
Step A2 (
Step A3 (
Then 
Step A4 (
Step A5 (the 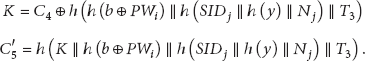
Then the 
Step A6 (
Step A7 (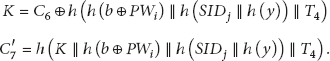
3.5. Password Change Phase
The procedure that is followed in the password change phase is depicted in Figure 3. If user

Password change phase of our proposed scheme.
Step P1.
Step P2. The smart card computes
Step P3.
Step P4. The smart card computes the following:

4. Security and Efficiency Analysis of the Proposed Scheme
4.1. Security Analysis
Table 2 compares the security of existing schemes with that of our proposed scheme. Our scheme uses the security properties described in the following subsections.
Security analysis of the compared schemes.

4.1.1. User Anonymity
Even if an attacker eavesdrops on
4.1.2. Impersonation Attack
Because an attacker cannot know x, y, b,
4.1.3. Parallel Session Attack
Suppose an attacker eavesdrops on a login request message
4.1.4. Password Guessing Attack
Even when an attacker eavesdrops on
4.1.5. Replay Attack
We assume that an attacker intercepts
4.1.6. Stolen Smart Card Attack
We assume that an attacker steals
4.1.7. Stolen-Verifier Attack
The proposed scheme can resist stolen-verifier attacks. In other words, in the proposed scheme, the
4.1.8. Mutual Authentication
The
4.2. Efficiency Analysis
Table 3 compares the performance of existing schemes with that of our proposed scheme. Our proposed scheme incurs less computational overhead than Nyang and Lee's [20] or Xue et al.'s [27] schemes. Although our proposed scheme incurs slightly more computational overhead than conventional schemes, it is more secure against various attacks than conventional schemes [18, 21, 22, 24, 25, 27].
Performance analysis of the compared schemes.

h: hash function operation; ⊕: XOR operation; K: key derivation function operation; M: message authentication code; E: symmetric encryption; D: symmetric decryption.
5. Results
5.1. Simulation Environments
In Section 4.2, we compared the performance of existing schemes with that of our proposed scheme. As a result, we implemented a simulation for various schemes. The simulation was performed and evaluated in a standard PC environment. The algorithm for the schemes was implemented using JAVA, and the simulation environment was evaluated with an Intel Core i5-2537 M (1.40 MHz) with 4 GB of RAM.
5.2. Simulation Results
Our simulation calculated the average time to perform the 10 simulation tests because the measured results were slightly different each time. Figure 4 shows the measured results for users performing the login and authentication phase. As shown in Figure 4, our proposed scheme incurs a little more computational time than existing schemes [18, 21, 22, 24–26]. However, our proposed scheme is more secure against various attacks than existing schemes and provides mutual authentication between the user and the

Analysis of time according to number of users.
6. Conclusion
In this paper, we proposed a secure and efficient mutual user authentication and key establishment scheme that can be used in ubiquitous WSNs. The proposed scheme provides mutual authentication between the user and the
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work was supported by the National Research Foundation of Korea (NRF) Grant funded by the Korean government (MSIP) (no. NRF-2012R1A2A2A01010886). This work was supported by the Soonchunhyang University Research Fund.
