Abstract
The communication between network nodes within different protocol domains is often regarded simply as a black box with unknown configuration conditions in the path. We address network heterogeneity using a white box approach and focus on its interconnection processes. To achieve this purpose, a Performance Analysis Framework (PAF) is proposed which is composed of the formalization of the latter using process algebra (PA) and the corresponding teletraffic performance models. In this contribution, we target the IEEE 802.16 and IEEE 802.11 protocols. For the teletraffic models, we extend previous models for such scenario with the inclusion of the following protocol operational parameters (metrics): bit error rate (BER), packet error ratio (PER), and packet length (pl). From the framework teletraffic models, the optimal packet length (OPL), end to end throughput, delay, and packet loss are obtained. The PAF outperforms previous modeling solutions in terms of delay and throughput relative to NS3 simulation results.
1. Introduction
Recently, the numbers of users and the quantity of information in heterogeneous networks have grown rapidly in metropolitan areas. The interconnection between nodes within different protocol domains is often regarded simply as a black box with unknown configuration conditions in the path. With increased demand, it has become necessary to analyze and develop new models to understand the performance of heterogeneous metropolitan area networks (HMAN). There are a number of factors that decrease the transmission efficiency between networks, such as
The 802.16 protocol supports M2M applications in the 802.16p version [5]. This protocol enables a range of M2M applications in which the communication device requires wide-area wireless coverage in licensed bands and is automated, rather than human initiated or human-controlled. This is for purposes such as observation and control. The requirements that 802.16 is intended to address include low power consumption, a large number of devices, short-burst transmissions, and device tampering, detection, and reporting. The 802.16 protocol acts as an aggregation point for 802.16 M2M devices and supports peer to peer (P2P) connectivity between these devices [5, 8].
The 802.11 protocol in the version of IEEE802.11ah standard has been found as an optimal candidate for M2M communication in wireless communication systems. This protocol considers sensing applications and will address required functions such as low power consumption, large number of devices, long-range and short-burst data transmissions [9].
The 802.16 and 802.11 protocols can be part of an M2M network where M2M devices (communication enabled) form an M2M area network. This M2M area network is based on the IEEE802.11 protocol, whilst the access network that connects the M2M gateway (nodes with two interfaces: 802.11 and 802.16) to the M2M core (e.g., the 3rd Generation Partnership Project (3GPP) Initiative for mobile communication technologies) is based on the IEEE802.16 protocol. In the M2M service platform, the M2M gateway is connected to the M2M management server (through the communication network) whereby the M2M applications (smart metering, smart transport, healthcare database, etc.) are reached [3].
Most network performance models consider only the homogeneous specification (common part) of the protocols that build the network rather than also including the differences among them. We believe that end to end performance analysis of heterogeneous networks should consider (i) the detailed specification (physical (PHY) and media access control (MAC) layers) and operational parameters of each protocol (BER, PER and pl, etc.), and (ii) the interconnection process that makes the heterogeneous network possible. Most research focuses on homogeneous behavior [10–17]; therefore, new and novel approaches are required to explore heterogeneous network performance specifically based on the IEEE802.16 and IEEE802.11 protocols. We define a heterogeneous network as interconnected networks with different software, protocols, hardware, operational speed, technology, and so forth but yet still capable of interoperability. We address network heterogeneity using white box approach and focus on its interconnection processes Box 1. For this purpose, a Performance Analysis Framework (PAF) is proposed which is composed of the formalization of the latter using process algebra (PA) and the corresponding teletraffic performance models. In this contribution, we target the IEEE802.16 and IEEE802.11 protocols.
(1) Identify the network heterogeneity. This includes all the involved communication protocols across the available communication paths and domains. Use an end to end communication perspective. (2) Define the metrics to models. (3) Survey available teletraffic models for the identified communication protocols from each domain. (4) Extend and adapt the previous models according to the network design and corresponding performance metrics for each communication protocol or network domain. Use the CLD approach. (5) Identify the gateway nodes and the corresponding interconnection tasks defined in the protocol specification and network design. Base this identification process on the roles established on Section 4.1 (6) Derive the interconnection teletraffic models for the gateway nodes. (7) Based on the processes defined in Section 4.1, integrate all the involved teletraffic models across the communication paths under an end to end perspective. (8) Validate the end to end performance models using test bed implementations or network simulation. Improve teletraffic models if necessary.
The main contribution of this paper is the evaluation of end to end throughput and delay in a HMAN by considering the effect of different layers based on CLD (layer 2 and layer 1 of OSI model). For this purpose, a PAF is proposed. A WiFi/WiMAX HMAN is used as a case study. The proposed PAF consists of the following key elements.
The first element is formalization of the end to end communication process of a HMAN using PA. The second element is teletraffic performance models. We derived end to end performance models for heterogeneous environments which take into consideration the interconnection process of different protocol domain networks, bit error rate, packet error ratio, and packet length. In our proposed models, we consider realistic error-prone channel conditions which have not been considered in previous related works.
The paper is structured as follows. Section 2 presents the related work. In Section 3, we present the theoretical background of the IEEE802.11 and IEEE802.16 protocols. The PAF (the formalization of the end to end communication process of a HMAN using PA and teletraffic performance models) is presented in Section 4. In Section 5, the experimental work is presented. The simulation results and discussions are presented in Section 6. Finally, some conclusions and future work are drawn up in Section 7.
2. Related Work
In this section, we present a review of some relevant related work. The review is divided into two categories: homogeneous and heterogeneous approaches.
2.1. Homogeneous Approaches
The homogeneous approaches reviewed are described below.
Bianchi's analytical model [10] is used to estimate the throughput of an IEEE802.11 network using the Distributed Coordination Function (DCF) under saturated conditions. This assumes (i) any transmission queue that always has packets to be sent, (ii) an ideal channel, and (iii) a finite number of stations. The model considers two DCF techniques: basic and RTS/CTS (request to send/clear to send). The approach adopted is to analyze a single station modeled using a Markov Chain. The results demonstrate that better performance is achieved when the RTS/CTS mechanism is used.
Duffy et al. in [11] present an extension of Bianchi's model. They consider on-saturated network conditions. They assume a perfect PHY layer, so transmission errors are caused only by collisions and do not occur due to noise on the medium. The analysis is focused on the throughput, collision probability, delay, total offered load, and (the optimal) minimum contention window. They employ three load types: Poisson, conditional, and uniform.
In [12], Lin and Wong's model (IEEE802.11n) addresses a unidirectional and bidirectional RTS/CTS access mechanism in the presence of collisions and channel errors in the system. This model, which is an extension of Bianchi's model, considers BER probability, minimum contention window length, and a maximum back-off stage. Their model also includes the MAC Protocol Data Unit Aggregation (A-MPDU) and MAC Service Data Unit Aggregation (A-MSDU) techniques to improve the MAC protocol performance. Simulation and analytical results are presented for throughput and delay. This is done for a different number of aggregation MPDUs and BER conditions.
Hwang et al. present in [13] a teletraffic mathematical analysis for the delay of bandwidth requests based on unicast, multicast, and broadcast IEEE802.16d/e polling in IEEE802.16d/e under error-free/error-prone wireless channel conditions. They derived the distribution for delays and the truncated binary exponential back-off (adopted as a contention resolution) by means of analytical methods. The authors study bandwidth efficiency and the utilization of transmission opportunity which is defined as a ratio of successful transmission opportunities and total transmission opportunities within a frame. Based on numerical analysis, they obtained optimum values for parameters such as number of transmission opportunities (or slots), the initial back-off window size, and Quality of Service (QoS) requirement on delay and loss.
In [14], Tian et al. propose a novel MAC scheme used for the DCF named Scheduled Random Access protocol (SRAP). This scheme is dived in two parts: schedule and contention. For the former the protocol allows a throughput close to the transmission capacity in a saturate case while for the latter a low delay is observed in low traffic load conditions. The analysis of simulation results showed that SRAP can improve the throughput with low delay. The throughput analysis is based on a teletraffic model and they state that SRAP achieves throughput close to the theoretical upper bound.
In [15], Calì et al. develop as an analytical model for the throughput a p-persistent IEEE802.11 protocol, which differs from the standard protocol in terms of the selection of the back-off interval. The standard protocol uses the binary exponential back-off while in the p-persistent case, the back-off is sampled from a geometric distribution with a parameter p. Also, they demonstrated that (i) the standard protocol can operate very far from the theoretical throughput limit depending on the network conditions and (ii) the IEEE802.11 protocol is close to the theoretical throughput limit when the p-persistent (geometric distribution) back-off algorithm is employed.
In [16], Liu et al. proposed a scheduling algorithm based on Cross-Layer Design (CLD) between the MAC layer and PHY layer. Each connection employs adaptive modulation and coding (AMC) and considers the QoS requirements. The algorithm operational parameters are derived from a series of teletraffic models which consider performance metrics such as bandwidth efficiency, throughput, delay, PER, and Signal to Noise Ratio (SNR). Simulations were implemented for the IEEE802.16 standard.
Chang et al. in [17] analyze throughput using the Markov model of Vinel et al. using different window sizes and Subscriber Station (SS) numbers. The SS employs a polling MAC instead of random access control, based on the uplink subframe of a (Worldwide Interoperability for Microwave Access) WiMAX Network.
2.2. Heterogeneous Approaches
The heterogeneous approaches reviewed are described below.
In [18] El-Azouzi et al. study an HMAN formed using the IEEE802.11 and IEEE802.16 protocols. The aim is to study how to integrate different technologies cooperating to provide universal connectivity and opportunity for the best suited services to users at anytime from anywhere. This is envisioned as a common scenario for fourth generation (4G) networks. They believe that the integration of IEEE802.11 and IEEE802.16 is one likely solution for distribution of high data rate services for next generation wireless networks (NGWN). They study the stability of the nodes which extend the WiMAX cell, in particular, gateway nodes. The gateway nodes have two interfaces: IEEE802.11 and IEEE802.16. They develop a CLD mathematical model for the throughput and delay and assume stable conditions in the queues. It considers layers 2 and 3. In the latter, two queues are employed: forwarding and high layer traffic queues. The Weighted Fair Queueing (WFQ) [19] is used as the scheduling mechanism under an assumption of saturation. From the model, they conclude that WiMAX parameters do not impact the performance in terms of throughput of pure ad hoc nodes and vice versa. We believe that the approach followed by the authors fits well for modeling the integration of different technologies allowing combining strengths and making up individual limitations. The solution from [18] has been applied in several works as follows: (i) for studying stability-throughput trade-off in wireless ad hoc networks in [20]; (ii) for performance analysis of delay, throughput, and energy consumption using a comprehensive analytical model of the IEEE802.11 [21]; and (iii) for end to end delay performance analysis in wireless ad hoc networks under CLD as presented in [22]. In this paper, the work from [18] is referred to as the reference model.
Yang et al. in [23] consider an 802.11 wireless local area network (WLAN) which shares a common set of multiradio devices with another network named CO-NETWORK which uses WiMAX. They assume saturated network conditions for all WLAN radios. They study how the throughput of a WLAN can be affected by scheduling the CO-NETWORK. Based on teletraffic modeling, they show that this issue can be minimized using proposed scheduling optimization criteria for the CO-NETWORK.
A convergence-bridge is proposed in [24]. It unifies the WiFi/WiMAX Frequency Bands. In other words, by modifying the WiFi Orthogonal frequency-division multiplexing (OFDM) PHY layer, WiFi devices are enabled to join the WiMAX-OFDM wireless network. The convergence-bridge is a thin layer in the WiFi OFDM PHY layer with 64 carriers. The WiMAX OFDM is fixed with 256 carriers. The main proposal for the convergence-bridge is to use multiple carriers which fit both technologies.
Different aspects of the interconnection process for both homogeneous and heterogeneous networks have been studied in the literature. There are many challenges to overcome before there is widespread adoption of heterogeneous technologies of this kind into MAN scenarios [25] (e.g., embedded system and devices). OPL and BER for WiFi/WiMAX still require further analysis. This is the focus of this work in terms of teletraffic modeling.
3. IEEE802.16 and IEEE802.16 Protocols Theoretical Background
3.1. Overview of IEEE802.16
MAC Layer. We focused only on Time Division Duplexing (TDD) which is divided into two transmission periods: downlink (DL) and uplink (UP). The DL is generally broadcast. TDD handles a duplex scheme, where DL and UP transmissions occur in different times but share the same frequency. The maximum transition time (round trip time) between transmitter and receiver is 2 μs. The TDD is built from the base station (BS) and SS transmissions [7].
PHY Layer. The physical layer is based on wireless MAN-OFDM interface according to the standard IEEE802.16-2004 [7]. This interface uses 256 subcarriers of which 192 are data subcarriers, 8 are pilot subcarriers, and 56 are null. The pilot subcarriers are used to minimize frequency and phase shift. The 56 null carriers are used for guard bands and DC frequencies.
3.2. Overview of IEEE802.11
MAC Layer. The DCF is employed in this research. The DCF is the fundamental mechanism to access the medium based on carrier sense multiple accesses with collision avoidance (CSMA/CA). The DCF employs a binary exponential back-off scheme. When a station wants to transmit a new packet, it monitors the channel activity. If the channel is idle for a period equal to the distributed interframe space (DIFS), the station transmits the packet. On the other hand, if the channel is busy (either during or immediately after the DIFS), the station continues to monitor the channel until it is sensed idle for the DIFS.
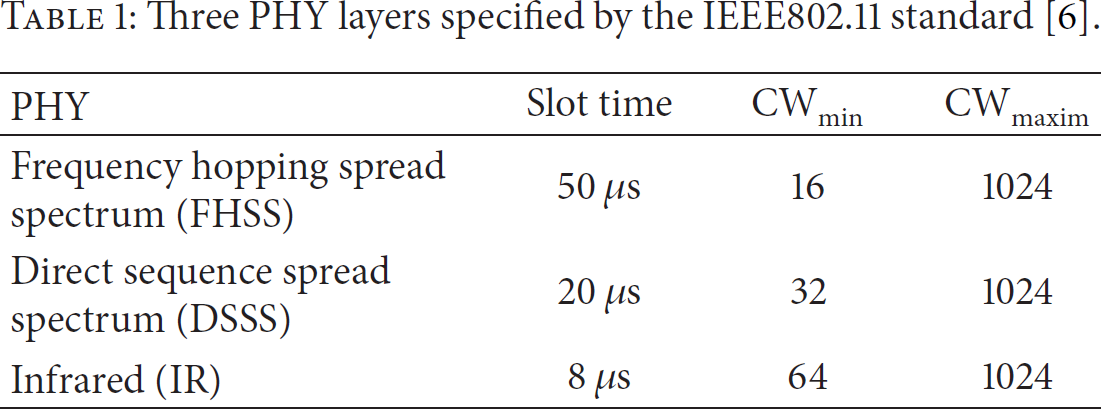
The station generates a random back-off interval before it transmits the packet. After an idle DIFS, a time slot is available and a station is allowed to transmit only at the start of each time. The time slot depends on the PHY layer (see Table 1). The back-off time is chosen in the interval 0 to W-1 in each packet transmission. The value W represents the contention window (
Three PHY layers specified by the IEEE802.11 standard [6].
The attempt rate is defined in [10] as the probability that a station transmits in a randomly chosen slot time.
PHY Layer. The PHY layer employed in this research is the IEEE802.11g protocol. This protocol was finalized until June 2003; 802.11g is a relative late-comer to the wireless marketplace. Despite the late start, 802.11g is now the de facto standard wireless networking protocol. This standard is used on most laptops and handheld devices. The 802.11g protocol uses the same industrial, scientific and medical (ISM) frequency range as the 802.11b protocol.
This physical layer is based on DSSS according to the IEEE Standard 802.11 [6]. This PHY operates in the 2.4 GHz ISM band and at a maximum raw data rate of 54 Mbit/s (with usable throughput of about 22 Mbps). Also, this physical layer can consider OFDM modulation. This makes it incompatible with 802.11b, and the higher frequency means shorter range compared to 802.11b/g at the same power.
The frequency range is 2.400–2.495 GHz, which is used by the 802.11b and 802.11g radio standards (corresponding to wavelengths of about 12.5 cm). A single 802.11g link may use 54 Mbps radios, but it will only provide up to 22 Mbps of actual throughput. The remaining bandwidth is the overhead that the radios need in order to coordinate their signals using the 802.11g protocol.
Since the 802.11g wireless equipment is half duplex (i.e., it only transmits or receives, never both at once), the required throughput must be doubled accordingly, for a total of 10 Mbps. The wireless links must provide that capacity every second, or conversations will lag.
4. The HMAN Performance Analysis Framework (PAF)
In this section, we propose the PAF which addresses the transmission performance in an HMAN and is composed by (i) the formalization of the end to end communication process of an HMAN using PA and (ii) teletraffic performance models. In (i), PA is used to formally define the communication between the homogeneous (single protocol domain) and the heterogeneous (multiprotocol domain) network sections whilst, in (ii), several teletraffic performance models are defined and represent the network's behavior across the transmission path. The PAF is a general framework for HMAN which will be deeply described on the following subsections based a case study for IEEE802.11 and IEEE802.16 heterogeneous networks. The PAF is depicted in Figure 1.

The PAF.
4.1. The Formalization of the HMAN Model Description
General Strategy. The end to end communication process of an HMAN can be modeled by PA. This formalism represents a mathematically rigorous framework for modelling system processes.
We define a HMAN as a septuple
Figure 2 shows the process graph that models the end to end communication flows in an HMAN. The reception and transmission flows set are represented by 

Process Graph.
Any communication process
When a packet is transmitted, the source awaits an acknowledgment from the receiver. This acknowledgement packet is symbolized as
The transmission process from the source is defined as
The receiving process at the destination node is defined as

The communication process for any intermediate node is defined as

The bridging process for a gateway node is defined as

Aggregation occurs at bridge node when two or more source packets are embedded into a single forwarding packet. This depends on the packet size source protocol and the forwarding payload size protocol. This aggregation process is defined as follows:
The defined PA defines all the processes and entities involved in any HMAN. A second aspect, which is addressed by the PAF. is the network behavior. This is discussed next.
4.2. Network Behavior Modeling
Methodology. Teletraffic theory is considered as a tool to model and analyze the HMAN behavior. We propose white box approach modeling methodology.
4.3. Case Study: The 802.11 and 802.16 HMAN
We model the end to end communication process for the HMAN study case by PA as follows:
The teletraffic performance models are derived from an HMAN based on the IEEE802.11 and IEEE802.16 standards considered as
We extend the reference model with the inclusion of the following protocol operational parameters (metrics): bit error rate (BER), packet error ratio (PER), and packet length (pl). Thus, our HMAN model considers BER, PER, and pl; therefore we get end to end throughput and delay under error-prone channel conditions.
The CLD from [18] considers both network and MAC parameters. The network layer handles two queues scheduled using a WFQ scheme [19]; we modify the CLD model from [18]. We now conceive that the WFQ is between the network layer and the MAC Layer. This is done in order to reduce network bandwidth usage. Each node has the same network layer and WFQ. This design permits the exchange of communication and information between layers and allows greater flexibility. The queue controls two queues: high layer packets (hlp) and forward packets (fp) which have an infinite capacity. The fp is the forwarding queue which carries the packets from other nodes to their destinations and the hlp which contains packets generated by node i itself. Each queue has its own transmitted probability:
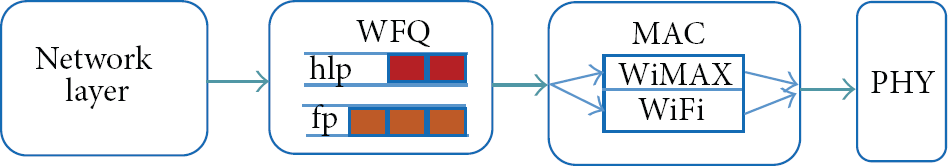
CLD for HMAN Model.
4.3.1. Mathematical Model for IEEE802.16
The mathematical model for IEEE802.16 is based on Fakhri et al.'s model [27]. This model is focused on the optimization of throughput, BER, and OPL in a wireless system for OFDM modulation. There are some assumptions made when developing this mathematical model. The transmitter sends packets of 

A symbol error in the packet automatically results in a packet loss, and the PSR is given in terms of symbol error rate (SER) 


4.3.2. Mathematical Model for IEEE802.11
In our research, we consider the PER which is determined from the BER. The BER is defined as the number of bit errors divided by the total number of bits transferred in a time interval and the pl [12]. The PER is denoted by 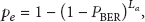


4.3.3. HMAN End to End Throughput Model
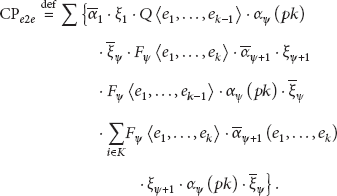
The expression for throughput in [18] is
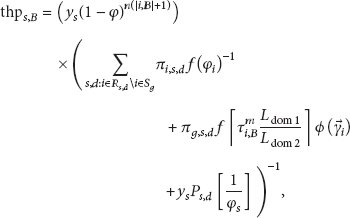
The throughput of the HMAN model is based on [12, 27, 28]. However, they address only homogeneous networks. In our proposed model (see (17)), we introduce the PER as dividend and consider the heterogeneity of the network (802.11 and 802.16). The end to end throughput under error-prone channel conditions is then estimated as follows:

Now, using (14), the throughput of the HMAN model is rewritten as follows:

4.3.4. HMAN End to End Throughput Optimization
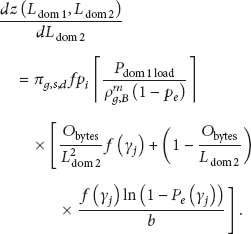
We employed a variable change in the throughput equation (18) in order to differentiate this equation with respect to packet length 
4.3.5. Optimal WiMAX Packet Length
We get the optimal WiMAX pl 

Setting this to zero produces an equation in 

4.3.6. Optimal Ad Hoc Packet Length
We differentiate (18) with 


4.3.7. End to End Delay
The mean end to end delay 

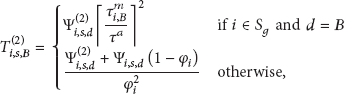

The delay of the HMAN Model is derived using (18) as follows:

5. The Experimental Work
Both WiMAX and WiFi networks are used in the simulations. The objective is to evaluate the proposed HMAN model against the reference model [18]. The simulation experiments are described as follows.
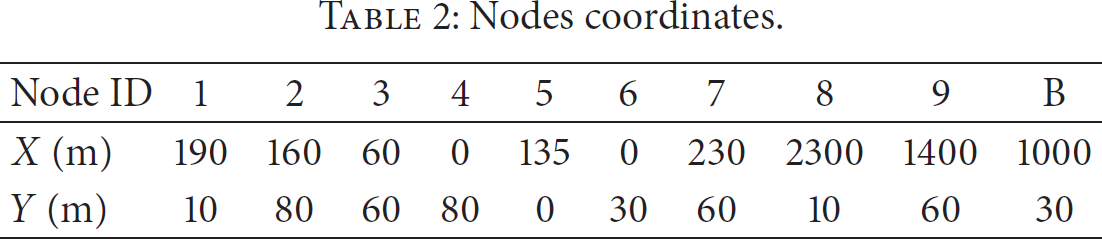
The experimental work was carried out on the ns3 network simulator [30]. The simulation scenario, shown in Figure 4, is set for an M2M heterogeneous network of 9 SS of which 5 are WiFi nodes, 2 are gateways (multiple interfaces WiFi and WiMAX), and 2 are WiMAX nodes. There is a base station (BS) WiMAX and each node has an ID, from 1 to 9; node IDs are sorted as follows: 2 to 6 are the WiFi nodes, 8 and 9 are WiMAX nodes, and 1 and 7 are the gateways node (IEEE802.11 and IEEE802.16). The nodes are distributed based on Table 2. IEEE802.11 PHY uses Direct-Sequence Spread Spectrum (DSSS) [12]. IEEE802.11 MAC was used as the MAC protocol. Some characteristics of the model were based on IEEE802.11 and IEEE802.16 standards. The simulation time was 500 s and the number of transmitted packets was 500 (based on the central limit theorem).
Nodes coordinates.

PyViz illustration on NS3.
We consider a Constant Speed Propagation Delay Model and a Friss Propagation Loss Model which correspond well to our Model. The Friss propagation Loss Model considers a frequency of 5.5 GHz at 300 000 km/s. Optimized Link State Routing (OLSR) [31] was used for instantaneous updates for each routing table.
There are three data flows: a, b, and c, shown in Figure 5. Node 4 is considered as the source for all data flows. The destination nodes are: node 9 for flow a, node 8 for flow b, and node 9 for flow c. Nodes 9 and 8 are configured with Quadrature Phase Shift Keying (QPSK) modulation. We develop two scenarios in which both have the same simulation parameters (from Section 5.1). In scenario

HMAN topology.
The HMAN network topology is depicted in Figure 5.
5.1. Simulation Parameters
Some simulation parameters are summarized in Tables 3, 4, 5, and 6. The following parameters are used in both scenarios.
Simulation parameters.

ACM settings for IEEE 802.16 [7].

Attempt rate probability (for each node i).

IEEE 802.16 MAC headers [7].

Table 4 shows the spectral efficiencies (rate) using IEEE802.16 adaptive coding and modulation (ACM) settings.
6. Simulation Results and Discussions
To validate the HMAN Model, we compare the obtained results with those obtained by the solution from [18]. We analyzed the following metrics: PSR, end to end throughput, end to end delay, BER, and OPL. The main goal for the analysis is to compare the HMAN performance against the solution from [18] and to verify that the HMAN model agrees with the NS3 simulation.
6.1. Packet Success Ratio (PSR)
PSR was analyzed for ranged pl mentioned above in 12 subscenarios corresponding to scenarios 1 and 2. Figure 6(a) shows PSR versus SNR using QPSK for flows a, b, and c. Flows a and c employ the scenario 1 configuration whilst flow b uses the scenario 2. Figure 6(b) shows PSR versus SNR using 16-QAM modulation results for flows a, b, and c. Flows a and c employ the scenario 2 configuration whilst flow b uses the scenario 1 configuration. The SNR values are derived from the obtained PSR using

(a) QPSK: PSR versus SNR in connection a (scenario 1), b (scenario 2), and c (scenario 1), respectively. (b) 16-QAM: PSR versus SNR in connection a (scenario 2), b (scenario 1), and c (scenario 2), respectively.
6.2. BER
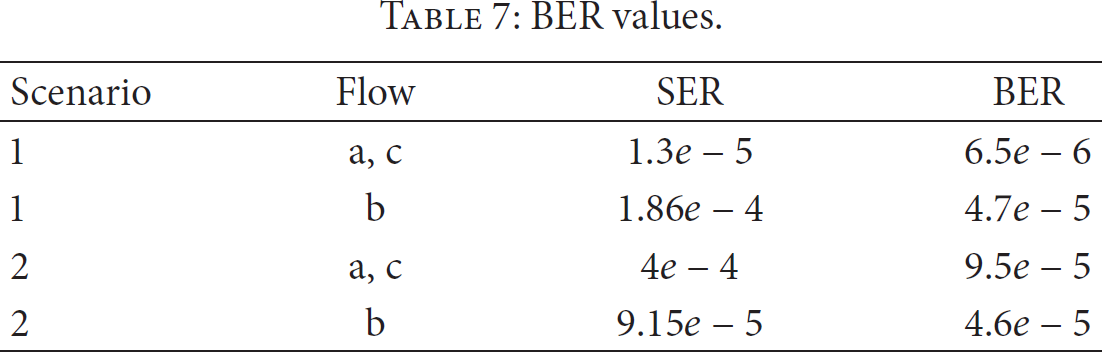
The BER and SER values are obtained from (10), (11), and (12) using the PSR simulation results. Table 7 presents the average values for the 12 subscenarios corresponding to scenarios 1 and 2. We observed that when the same modulation scheme is employed for both WiFi and WiMAX domains the BER value is lower than the BER value using a different scheme.
BER values.
6.3. Symbol Error Rate (SER)
Two important metrics for an HMAN end to end performance analysis are the PSR and SER. In the case of the WiMAX domain, these metrics are derived from (10), (11), and (12). Figure 7 shows the PSR and SER relation under different modulation schemes. It is observed that as the number of bits increases per symbol for a given SER value, the PSR decreases significantly. Note that the corresponding BER and SER simulation result values (Table 7) are shown within the BER range of Figure 7.

PSR versus SER.
6.4. End to End Throughput
End to end throughput was analyzed for both scenarios in an error-prone channel with different BER values from Table 7 for CSMA/CA with RTS/CTS. Figure 8 shows the throughput versus variable pl results for flows a and c using scenario 2, whilst flow b used scenario 1. As shown in Table 7 the chosen BER values are representative of the protocols under test and have been selected to evaluate the models under diverse network conditions. Reference model [18] and HMAN model results are obtained from (10) and (9), respectively.

End to end throughput versus pl (bytes) in connections (a), (b), and (c), respectively.
From the above experimental results, we calculated the mean square error (MSE) for both models in each communication flow. We can observe in Figure 8 that the throughput obtained by the HMAN model is 11.46% more accurate in all the flows than the throughput obtained by the reference model. Also, the results of HMAN are closer to the results of NS3 as can be seen in Figure 8.
6.5. End to End Delay
End to end delay was analyzed in both scenarios. Figure 9 shows end to end delay versus variable pl in flows a, b, and c. From Figure 9, it is predictably observed that the delay increases as the pl is increased. The average absolute error (AAE) is obtained between the HMAN model and NS3 simulation results. The AAE is 4.14% for flow a, 4.39% for flow c, and 8.75% for flow c (100–1200 bytes). Flow b employs scenario 1 whilst flows a and c employ scenario 2. We consider an error-prone channel with the BER values of Table 7 in both scenarios. It is observed that the HMAN model and reference model are smooth; by contrast the NS3 simulation results are undulating. This is because NS3 is directly modeling the processing entities, for example, network interfaces. The HMAN model outperforms previous solutions in terms of delay and throughput relative to the NS3 results and is largely indifferent to pl. Reference model and the HMAN model results are obtained from (28) and (32), respectively.

End to end delay (ms) versus pl (bytes) in connections (a), (b), and (c), respectively.
From the above experimental results, we calculated the MSE for both models in each flow communication. The delay obtained by the HMAN model is 34.21% more accurate in all the flows than the delay obtained by the reference model. Also, the results of HMAN are closer to the results of NS3 as can be seen in Figure 9.
6.6. OPL
Efforts were made to find the OPL for both scenarios; there will be pl that maximizes the throughput in an error-prone channel. We used the PER obtained from both scenarios as shown in Table 7. In Figure 10(a), it is observed that for flow a from scenario 2 the OPL is 135 bytes for a PER of 0.1 and the OPL decreases as the PER is increased. Figure 10(b) shows flow b from scenario 1 where the OPL is 293 bytes for a PER of 0.01. Again the OPL decreases as the PER is increased. These results are obtained from (16) (a) for

OPL versus PER in connection: (a) and (b).
7. Conclusions
We analyzed a heterogeneous network composed of a WiMAX cell and a WiFi network. The WiMAX protocol shares many characteristics with cellular networks such as architectural support for billing, mobility, and QoS. The main contribution in this paper is the evaluation of end to end throughput and delay in a HMAN by considering the effect of different layers within the CLD (layer 2 and layer 1 of OSI model). We extended previous models for such a scenario with the inclusion of the following protocol operational parameters (metrics): BER, PER, pl, and OPL. Further, numerical and simulation results were performed to validate our HMAN model. The HMAN model outperforms previous modeling solutions in terms of delay and throughput relative to the NS3 results and is largely indifferent to pl. In a WiMAX system, the OPL depends on the SNR per symbol, error probability, and the constellation size. In a WiFi system, the OPL depends on the BER. By using our HMAN expression, we can compute the OPL for a given set of network conditions to improve network adaptability; this could be applied dynamically. The HMAN can be further extended to consider other network metrics such as jitter and frame segmentation and other protocols such as CAN, Zigbee, and Bluetooth. The scenarios can also be applied to a number of different modulation schemes and node densities.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
