Abstract
The function privacy notion was proposed by Boneh, Raghunathan, and Segev in August 2013. It guarantees that the secret key reveals nothing to malicious adversary, beyond the unavoidable minimal information such as the length of ciphertext. They constructed a function private identity-based encryption that contains equality functionality. In this work we construct a new function private attribute-based encryption which supports more complex functionality. And we transform it to a searchable encryption. In searchable encryption, the trapdoor of searching keywords can be seen as the secret key. Hence, using this system can efficiently resist keyword guessing attack.
1. Introduction
Functional encryption [1, 2] is now being seen as a powerful tool especially on the application of cloud security, such as searchable encryption, secure auditing, and secure data sharing. It is a new paradigm for public key encryption. In this system, the decryption ability of a receiver is determined by whether the secret key and the ciphertext can be computed by the function. Identity-based encryption (IBE) [3, 4] can be seen as a functional encryption that supports a equality functionality. Fuzzy identity-based encryption [5] is the first functional encryption that supports nontrivial functionality, whose functionality is a k out of n threshold function. Then it is extended to attribute-based encryption (ABE) [6] classified as key-policy ABE(KP-ABE) and ciphertext-policy ABE(CP-ABE). Subsequently, many other functional encryption schemes are constructed to support certain specific functionality such as predicate encryption [7] and inner product encryption [8]. Security is also concerned about by scholars, from a selective-set security model [5–7] to a fully security model [8]. Meanwhile, other public key cryptographic primitives are also developed [9, 10]. Gorbunov et al. [11] extended the access control policy to polynomial size circuit based on LWE assumption. They used a novel technique named as “Two-to-One Recoding” (TOR) to achieve this goal and also built a scheme based on bilinear maps using a weak TOR scheme. Then, Boneh et al. [12] built an attribute-based encryption for arithmetic circuits with much shorter secret keys. And their scheme is more suitable to the access policies that can be naturally represented as arithmetic circuits.
Recently, Boneh et al. [13, 14] put forth a novel security notion, function private, to protect the privacy of secret key in identity-based encryption. If a scheme is function private, the secret key of the scheme is indistinguishable with a random element chosen from the secret key space. They introduced an approach called “Extract-Augment-Combine” to achieve the function privacy. However, in their schemes, only the function privacy of IBE is realized, and how to construct a function private functional encryption is left as an open problem. We partly solved it in this work by proposing a function privacy KP-ABE scheme using a similar technique introduced in [13].
Searchable encryption is also a special class of function encryption, which is motivated by the demand for applying securely search on remote encrypted data. It is firstly introduced by Song et al. [15]. It is built on private key, so it is used to be called searchable symmetric encryption. However, it was not fully secure and only supported the two-party model. Then, many secure searchable encryptions based on symmetric encryption are proposed [16, 17]. But these schemes were still unsuitable to the third-party situation. Boneh et al. proposed the first searchable public key encryption, public key encryption with keyword search (PEKS) [18]. It is the first searchable public key encryption that enables a third party to implement a keyword search. Abdalla et al. [19] proposed a transformation from anonymous IBE to PEKS and fulfilled the security definition. All of the above schemes only support single designated receiver. Han et al. [20] constructed a scheme that supports nondesignated receivers using KP-ABE. The scheme is secure and satisfies a weak anonymity called attribute private. They also proposed a general transformation from KP-ABE to ABEKS (attribute-based encryption with keyword search) and constructed a secure searchable attribute-based encryption.
Recently, Byun et al. [21] raised an attack called off-line keyword guessing attack (KGA) on searchable encryption, due to the relatively small keywords set (such as a frequently using keyword “urgent”). So an attacker can use the brute-force technique to searching by all keywords to find a collision of the keyword. Jeong et al. [22] asserted that the consistency of searchable public key encryption contradicts keyword guessing attack. Subsequently, scholars studied this attack and proposed some schemes which can resist keyword guessing attack [23–25]. In this paper, we proved that function privacy of function encryption can be transformed to the KGA security of searchable encryption.
Our Contributions. Inspired by the work of Boneh et al. [13], we construct a function private attribute-based encryption based on the scheme of [20]. Moreover, our scheme achieves data security, attribute privacy, and function privacy. Then, we construct a searchable attribute-based encryption against keyword guessing attack using the transformation introduced in [20]; our construction is more natural compared with previous constructions [23–25].
2. Preliminaries
Notations. For an integer
The min-entropy of a random variable X is
Definition 1 (access structure, see [26]).
Let
In our settings, attributes will play the role of parties. We will only deal with the monotone access structures.
We now introduce the LSSS definition adapted from [26].
Definition 2 (linear secret sharing scheme (LSSS)).
A secret sharing scheme Π over a set of parties 𝒫 is called linear (over
the shares for each party form a vector over there exists a matrix A called the share-generating matrix for Π. The matrix A has l rows and n columns. For all
The linear reconstruction property is described as follows. Assume that Π is an LSSS for access structure A. Let S be an authorized set, and define
Definition 3 (see [13]).
A collection ℋ of functions
Lemma 4 (see [13], leftover hash lemma for block sources).
Let ℋ be a universal collection of function
The proof is omitted here; we refer the readers to [13] for more detail.
The security model for function private attribute-based encryption is described as follows. This model is derived from [13]. The original model in [13] is for identity-based encryption; our security model is for attribute-based encryption.
Definition 5 (real-or-random function-privacy oracle for ABE).
The real-or-random function-privacy oracle
Definition 6 (function-privacy adversary, see [13]).
An
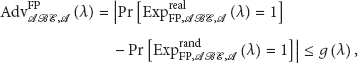
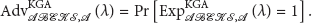
Definition 7 (function privacy of ABE).
An attribute-based encryption scheme ABE = (Setup, KeyGen, Enc, Dec) is
where, for each
(pp, msk) ← Setup( Output b.
3. The Concrete Scheme
3.1. The Original Scheme
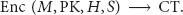
The construction of attribute-based encryption in [20] is described as follows;
First, the algorithm chooses a bilinear group G of order
This algorithm picks up a random
which also includes the hashed attributed set
where 𝔸 is a matrix,
Let
The message can be recovered by
3.2. The Modification
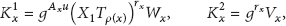
Above, the original scheme is proved to be data secure and attribute private in [20]. To make our scheme function private, we need to modify the KeyGen algorithm and Dec algorithm.
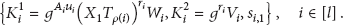
In KeyGen algorithm, we let the matrix 𝔸 be
In Dec algorithm, the decrypter finds constants
In the Dec computation, we let
So we can enable our modified scheme to act like the original scheme.
4. Security Analysis
Our modification does not violate the original scheme's security. Since the data security and attribute privacy is proved in [20]; we will prove the function privacy of the modified scheme only.
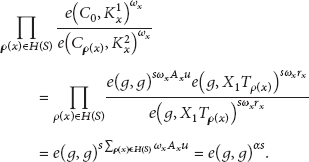
Function Privacy. Let 𝒜 be a computational bounded adversary that makes a polynomial number of queries to the
By simulating, the adversary queries KeyGen and
for
Note that the collection of functions
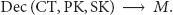
5. Extension to Searchable Encryption
We have constructed a function private attribute-based encryption. In the above scheme, the entropy of secret key is large enough. By the transformation described in [20], we can easily get a searchable attribute-based encryption (ABEKS). Consider
Since an adversary cannot efficiently guess a concrete trapdoor built on some access structure owing to the privacy of secret key of ABE scheme, our scheme can resist keyword guessing attack. In fact, when an adversary 𝒜 implements a keyword guessing attack, he will randomly pick a valid access control policy associated with a keywords set and run a test to determine whether this keyword set is used to generate a trapdoor.
The security experiment is described as follows:
If
We define the advantage of 𝒜 in the above experiment as
Theorem 8.
ABEKS scheme can resist keyword guessing attack, if the original ABE scheme is function private.
Proof.
Let 𝒜 be a polynomial time algorithm that implements a keyword guessing attack on ABEKS and let ℬ be an adversary that breaks the function privacy of ABE. If 𝒜 can efficiently obtain a valid keywords set corresponding with some trapdoor, then ℬ can distinguish the secret key with some random element sampled from secret key space using this trapdoor (i.e., secret key in ABE); that is,
Hence, the proof is completed.
6. Conclusion
In this paper, we present a function private attribute-based encryption, which at the heart of our construction is a method of randomizing the secret key, so we have achieved that the secret key in our scheme is indistinguishable with the random element sampled from the secret key space. And then we extend it to a searchable attribute-based encryption which resists keyword guessing attack.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgment
The authors want to express their sincere thanks to the anonymous referees for their valuable comments and suggestions. This work is supported by the National Nature Science Foundation of China under Grant no. 61272091 and the National Nature Science Foundation of Shandong Province under Grant no. ZR2012FM005.