Abstract
In recent years, the adaptation of wireless sensor networks (WSNs) to application areas requiring mobility increased the security threats against confidentiality, integrity, and privacy of the information as well as against their connectivity. Since key management plays an important role in securing both information and connectivity, a proper authentication and key management scheme is required in mobility enabled applications where the authentication of a node with the network is a critical issue. In this paper, we present an authentication and key management scheme supporting node mobility in a heterogeneous WSN that consists of several mobile sensor nodes and a few fixed sensor nodes. We analyze our proposed solution by using the OMNET++ simulator to show that it requires less memory space and provides better connectivity and network resilience against node capture attacks compared to some existing schemes. We also propose two levels of secure authentication methods for the mobile sensor nodes for secure authentication and key establishment.
1. Introduction
The wireless sensor network (WSN) was initially considered to be used for military applications but the popularity of WSN, because of its small size, low cost, and being easy to deploy and manage, makes it used in a variety of applications. This opens a door to new research challenges to the research community. Since sensor nodes are usually deployed in possibly remote and unattended locations, they are definitely prone to security attacks. Hence to secure the network operation and securely gather and forward the information, security threats and their countermeasures should be considered at design time in terms of both requirements and implementation techniques. However, such tasks are not trivial due to the limited energy, computation, memory, and bandwidth resources available in sensor nodes. Fundamentally, any practical WSN security countermeasure must be, on the one hand, secure enough to satisfy the initial requirements and, on the other hand, lightweight enough not to interfere with normal WSN operations.
The design of security algorithms considering the homogeneous sensor networks where all nodes have the same capabilities (memory, radio range, computational power, battery life, etc.) was the first step to secure sensor networks. However, some research work has shown, both theoretically [1–3] and through simulation experiments and test bed measurements [4], that homogeneous sensor networks have high communication and computation overheads and high storage requirements and suffer from severe performance bottlenecks. Hence, recent research work [5–9] introduced heterogeneous sensor networks, which consists of a small number of powerful high-end sensors (H-sensors) and large number of low-end sensors (L-sensors). To achieve better performance and scalability, H-sensors have more resources in terms of energy, computation power, storage capacity, and transmission power, and so forth compared to L-sensors. However, both H-Sensors and L-sensors are still highly vulnerable in nature and are exposed to several security threats and particularly prone to physical attacks. Thus, proper security mechanisms should be applied to protect these nodes against specific attacks including Denial of Service (DoS) attacks, Sybil attacks, compromised node attacks, node replication attacks, and physical tampering. Physical attacks become even more troublesome when the nodes are mobile and the possible intruder can more easily target them. Most security features to provide secure communication and authentication essentially rely on encryption. Nevertheless, encryption is not possible in such a distributed environment without adequate key management mechanisms. For this reason, the adoption of a suitable key management scheme plays a central role in the definition of a secure WSN.
1.1. Key Ideas of the Proposed Approach
A key management scheme for heterogeneous wireless sensor network is proposed to overcome the scalability issues by providing almost 100% network connectivity, reducing memory cost while increasing the network resilience against attacks, and reducing communication overhead to save the energy and increase of network lifetime.
Hence, a novel key management scheme for heterogeneous sensor networks suitable for scenarios with partial mobility is presented. The proposed solution relies on two types of keys: authentication keys and secret communication codes used to generate secret keys whenever needed. The key material is assigned to the different nodes of the network by adopting adequate key predistribution mechanisms. The remaining of the paper is organized as follows. Section 2 presents existing work. Section 3 describes the proposed key management scheme, while in Section 4 a performance analysis and evaluation of the proposed scheme is provided based on simulations results. Section 5 describes the security analysis of the proposed scheme, and finally conclusions are provided in Section 6.
2. Related Work
To make a system secure, cryptography is considered as one of the important security blocks which helps in implementing many security features. However, the management of these cryptographic keys has always been a challenging task.
To secure wireless sensor networks, Perrig et al. [10] proposed SPINS, in which there is a secure central entity called server which is responsible for establishing a key among the sensor nodes. Before the network deployment, each node is assigned a secret key while its corresponding key is assigned to the base station. Each sensor node needs to authenticate itself to the server (base station) during the initialization phase using the assigned key. Since it is based on centralized base station approach, two sensor nodes can only establish a secret key through its centralized trusted base station. However, the failure of base station severely affects the performance of network because of the existence of single centralized entity (base station).
To overcome the abovementioned issue, a randomly key distributed approach is proposed by Eschenauer and Gligor [7]. In this scheme, there is no centralized entity like a base station for key distribution and management. Each node in the network is assigned a set of randomly selected keys from a large key set. Since the keys are distributed randomly, the two communicating nodes need to have at least one common key in their sets for secure communication. However, the nonexistence of a common key in their sets affects the network connectivity but it improves the network security against node capturing attacks. To further improve the network security, sharing of at least q-keys concept for establishing a secret key is introduced by Chan et al. [11]. This scheme improves the network security but it further degrades the network connectivity and increases the memory requirements. But the prior knowledge of node's deployment in the network helps in increasing the network connectivity and reduces the memory requirements [12] combined with Rabin's scheme [13]. The use of Rabin's scheme makes the approach computationally expensive. Hence to achieve better security and network connectivity with less memory requirements with low computational cost, NPKPS scheme is proposed by Zhang et al. [14] for wireless sensor networks.
The above described approaches are suitable for the static networks only. Because introducing node's mobility needs to increase the size of assigned key set which increases the memory requirements. Hence to reduce the memory cost, a level-based key management scheme for multicast communication is proposed by Kim and Ramakrishna [15] while a two-layered dynamic key management for clustered based wireless sensor networks is presented by Chuang et al. [16].
The management of secret keys (MASY) protocol is presented by Maerien et al. in [17] which is based on the trust assumption among the networks managers/base stations. When a node enters into an unknown networks, it can establish a secret key with the new network's manager/base station using the trust relationship assumption among the networks managers/base stations.
To further improve the network connectivity and reduce the memory requirements of the symmetric key distribution approaches, Du et al. [9] present an asymmetric key predistribution (AP) approach. Du sensor network model consists of two different types of nodes making it heterogeneous sensor networks (HSNs). This assumption significantly increases the network connectivity and reduces memory requirements compared to the existing symmetric key management approaches. Nodes with high capabilities act as cluster head and are assigned m keys, while nodes with low capabilities act as normal nodes and are assigned l keys, where
Network Model. The considered network model is a Heterogeneous Sensor Network (HSN) composed of H-sensors, that is, powerful nodes and L-sensors, that is, having limited capabilities. More specifically, H-sensors and L-sensors have different computational resources, available storage capacity, and battery lifetime, but we assume that all nodes use the same transmission power and have the same transmission rate. In addition, a Base Station (BS) acts as a reference sink node in HSNs and as a gateway offering connectivity towards other types of networks. With respect to mobility, H-sensors have the role of fixed nodes (FNs) thus defining, along with the BS, a sort of fixed WSN infrastructure, while L-sensors are considered as mobile nodes (MNs). The virtual network organization is shown in Figure 1. From the security point of view, sensor nodes are allowed to communicate only after being authenticated by the network and having established a communication key with the peer node.

Virtual network architecture.
In this proposed network architecture, the base station and the fixed nodes are more powerful than mobile nodes, hence given the responsibility to play an important role in the authentication and key management. More specifically, the fixed nodes act as cluster heads (CHs) while the mobile nodes act as cluster members. The selection of cluster head by the mobile node is based on the received signal strength of fixed nodes. Since the fixed nodes and mobile nodes are using the same transmission power, a MN may come in the coverage range of transmission of more than one fixed node. Hence a mobile node selects a fixed node with the highest signal strength as its cluster head.
To introduce the mobility in the network, we use a realistic mobility model in the OMNET++ simulator. The considered mobility model for the proposed scheme is the random way-point model [21]. This model ensures that all the targeted destinations are equiprobable. Each node in the network is given (1) its initial deployed location, (2) target location, (3) velocity, and (4) time duration for taking a random decision. Once the timer expires, the node randomly chooses next location as a target and keeps its velocity constant and starts its journey toward the new selected target location in the given area. When it arrives to the new location, it repeats the process again. However, the selection of a target location in a given scenario is based on a uniform distribution.
Here we describe a list of abbreviations used in the proposed solution:
CH: cluster head, MN: mobile node, FN: fixed node, Kplc: public key, Kprt: private key, prand(): prime number generator, AUTH: authentication code, PRM: generated prime number, SPMN: scalar product of a mobile node, SPFN: scalar product of a fixed node, SCC: secret communication code.
3. Proposed Scheme
The proposed key management scheme is built on top of the above network model to provide effective authentication and dynamic key establishment. The key material is generated at the BS. More specifically, a large key pool
The key pool key predistribution to the different sensor nodes, that is, FNs and MNs; node authentication; communication key establishment among the nodes within the network.
Further details will be provided in the following subsections. Furthermore, Figure 2 presents a graphical description of all the operations foreseen in the proposed solution.

Overview of the proposed key management scheme.
3.1. Key Predistribution
As already mentioned, in our proposed scheme, the key material is organized at the BS in a large key pool
Concerning the authentication key material, each FN and each MN are assigned an elliptic curve
As previously described, FNs and the BS compose the fixed infrastructure of the overall heterogeneous sensor network; they are powerful devices and are responsible for the authentication and key management services offered to the MNs. In order to maintain the availability of these services and to avoid the full network being compromised by attackers, a higher level of security is thus required for FNs and the BS. As a consequence, the authentication of FNs to the network and the communication between the FNs and between a FN and the BS will be based on a standard ECC-based private/public key mechanism. Accordingly, each FN has its own private key and the public key of the BS and of all the other FNs of the network. At the same time, the BS has the public keys of all the FNs.
All the previously introduced key material is transferred to each node of the network by means of secure side channels. Then, after this predistribution phase, the specific key material assigned to each type of node of the network is as follows:
the BS owns all the key material that needs to be predistributed (plus, as already described, the public key of each FN); each FN i has been given each MN j has been given
3.2. Node Authentication
After the deployment and key predistribution phase, each FN of the network broadcasts periodic Hello messages. This mechanism enables each FN to fill a table with all neighboring MNs. These Hello messages include the FN ID and a random nonce signed by the FN's private key. Upon the reception of those Hello messages, each MN selects a FN as its cluster head (CH), for example, the one with the highest signal strength, after the verification of Hello message by using the FN public key. Since Hello message verification is a part of the authentication phase, at this point the authentication phase among the FNs and the MNs can start. To this aim, each
3.3. Communication Key Establishment
Once the MN and CH/FN authenticate each other successfully, the key establishment phase starts. During this phase, the MN sends one of its secret communication codes
3.4. Handover
The MNs are moving and they may leave their current CH and join a new CH. In order to know when they need to perform the handover to remain connected to the network, each MN monitors (e.g., by sending periodically a signal strength inquiry message) the SNR of its CH. Once the MN detects that its CH SNR is below a predefined threshold value, it broadcasts a request to find its neighboring FNs. Upon the reception of the response, the MN selects the FN with the highest SNR as its new CH. When the MN performs the transition from its old CH to the new CH, it sends its old CH identity,
3.5. Protection of Key Material
Since the sensor network may be deployed in unattended or even hostile areas, for example, when used for military applications, node capture and physical damage cannot be avoided. In order to protect the key material, we assume that each node is provided with tamper resistant hardware [23] and with a mechanism operating in such a way that when a node is captured and physically damaged, its keys become invalid. More specifically, once a manumission attempt is detected, both the original authentication and communication keys and the relevant IDs are replaced by fake ones: this would ensure that the original keys material is never revealed to an adversary.
Once the FN receives a joining request and key request from a compromised MN, it will inform the BS and all its neighboring FNs about the compromised MN's ID so that each FN can delete the key map of this compromised MN. In case the FN itself is compromised, however, it would not be able to generate the secret key and when it tries to authenticate the MN, the MN will understand that the FN is compromised. The MN would then contact other neighboring FNs for authentication and communication key establishment and eventually notify them about the compromised FN. This information will be also propagated to the BS for verification. The BS will then ask the compromised FN about its communication key IDs. If the BS receives the wrong key IDs, then the BS would declare this FN as compromised and inform all the other FNs of the network about it.
4. Performance Evaluation
In this section, we discuss the results obtained by using OMNET++ simulators. In order to introduce the mobility in OMNET++ simulation, we use MixiM 2.0.1 framework. Simulations are based on a network with 400 mobile nodes (MNs) and 16 fixed nodes (FNs). The area where the MNs are deployed and move is 400 m × 400 m. As mentioned earlier, we are using the same transmission power for both the fixed nodes and the mobile nodes, using the CSMA 802.15.4 standard and the radio specifications based on the CC2420 radio chip. The velocity of the mobile nodes is kept constant at 1 m/s while the next target's location selection interval is set to 0.1 s. The transmission power is set to 10 mW and the receiver sensitivity is set to −95 dBm.
4.1. Connectivity
Network connectivity is considered an essential part in evaluating the performance of the network. From the security point of view, two neighboring nodes in a network are said to be connected if they have a secret key for secure communication. In this section, we are evaluating the performance of the proposed scheme against some existing schemes in terms of probability that two nodes can authenticate each other and establish a secret key (i.e., connectivity). In the scheme discussed above, we use both (1) online key generation for authentication and (2) secret communication key establishment and key predistribution to ensure one-hop network connectivity among the MNs.
Here the network connectivity is evaluated by using the OMNET++ simulation results. In case of the key predistribution techniques, the probability of single key sharing defines the network connectivity and is given by
Figure 3 represents the OMNET++ simulation results comparing the connectivity of a MN to the CH with some of the existing schemes [7, 9, 14, 24]. It is clear that the online authentication key generation technique substantially improves the network connectivity because the network connectivity provided by the proposed scheme is almost 100%.

Single authentication key sharing probability between fixed node and mobile node.
In order to further analyze the effect of key pool size on network connectivity in the key predistribution schemes, we carried out OMNET++ simulation to find the key sharing probability between the FNs and MNs by limiting the MN key pool sizes (

Single key sharing probability with different key pool size.
The deployment of the fixed nodes is such that it covers the whole area of the network. Under this assumption, a mobile node may come into the coverage area of more than one fixed node; hence the probability of authentication of each MN by any in-range authentic FN is given by

MN authentication probability by more than one FN

Single key sharing probability among the mobile nodes.
4.2. Memory Cost
The secret communication code key pool
Let us assume that
4.3. Node Energy Consumption
In this section, the energy consumption in the authentication and in key establishment phases has been observed using OMNET++ by optimizing the proposed algorithm in terms of the total number of exchanged message. Figure 2 shows that we need only two messages in the proposed scheme for the authentication purpose compared to [25–27] which require 4, 3, and 3 messages, respectively. Hence it is clear that less messages exchange consumes less energy in the proposed scheme. Again the total number of messages required in key establishment phase has been reduced to only two messages in the proposed scheme which is less than the existing approaches [25–27]. Hence the overall message exchanges by each node in the authentication phase and in the key establishment phase, including the acknowledgement, of the proposed algorithm are 5 while in the other schemes [25–27] they are 6, 7, and 6, respectively.
Figure 7 shows the comparison of the overall energy consumption of a node in the proposed algorithm with [25–27]. It is clear from the results that the proposed scheme consumes less energy than other algorithms. Hence it increases the network life time.

Overall energy consumption of a node.
5. Security Evaluation
5.1. Denial of Service Attack
In this section we describe some kind of Denial of Service attacks (DoS attacks) that can be brought against our proposed scheme, as well as possible countermeasures. The main objective of DoS attacks is to make the resources unavailable to an intended user of the network.
( 1) FN Hello Messages. The first possible DoS attack against the proposed scheme is to broadcast Hello messages pretending to be a FN of the network to exhaust the resources of the MNs. Since each Hello message is signed by the private key of the FN, MNs will verify it using the public key of that FN. Since the adversary FN is not an authentic node, the MN would not be able to verify that Hello message and once a MN detects this attack, it will inform its other neighboring authentic FNs. The authentic FNs would then inform the BS and neighboring MNs about this fake FN ID so that they can avoid the messages from that node.
( 2) MN Hello Messages. When a MN finds its current CH signal strength value below a threshold value, it starts broadcasting the MN Hello messages to know about its new neighboring FNs. The attacker can launch such MN Hello message broadcast attack by introducing a fake MN. Since the MN Hello broadcast message is also signed by the MN private key, the new FNs first verify it by using the MN public key. This would not be possible for a fake MN. Thus the FNs inform the BS and other neighboring FNs about this malicious MN.
5.2. Sybil Attack
Sybil attacks are those in which a malicious node illegitimately takes on multiple identities. We call the nodes performing these attacks as Sybil nodes. Sybil attacks can be of different forms, for example, using direct or indirect communication and fabricated or stolen identities. In the direct communication Sybil attacks, a Sybil node communicates directly with a legitimate node. But since, in the proposed scheme, the Sybil node is first authenticated by sending a message signed with its private key, the FN would not be able to authenticate it. In the indirect communication Sybil attacks, malicious node (who deploys Sybil nodes in the network) becomes a router for forwarding the communication to the Sybil node from the FN which is not possible in the proposed scheme because each MN is the end user of the network. In the fabricated Sybil attacks, the attacker assigns an unuse identity to the Sybil node. In this case, this Sybil node needs to authenticate itself to the FNs which would again not be possible in the proposed scheme as described above. Stolen identity based Sybil attacks are very dangerous in such resource constrained networks. But this type of Sybil attack does not affect the proposed scheme because each communication is encrypted with the key agreed already with the original node having this ID, and the Sybil node does not have these keys.
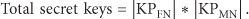
However, we compare the proposed scheme with the balanced key predistribution scheme [7] and an unbalanced key predistribution scheme [9] to show the effectiveness of proposed scheme. Although the proposed scheme is partially based on key predistribution approach by assigning
In the key predistribution approach, if every MN is assigned
Figure 8 shows the probability of successfully generated Sybil nodes in the proposed scheme compared with scheme [7, 9].
Probability of generation Sybil nodes.
5.3. Node Compromission
As described in Section 3.5, we assume that a node is secured by hardware means against access to its keys. However, no such scheme is ever perfect; hence here we analyze the effects of such attacks on our key management scheme.
In existing key predistribution schemes for both homogeneous and heterogeneous sensor networks, each node is assigned a key pool, and for secure communication the two nodes must have a shared common key. In that case, once the node is compromised by an adversary, it can compromise all the secure links with neighbors with whom this node has a shared key. Thus the fraction of communications compromised by compromising c MNs is given by

Network resilience against compromised mobile nodes.
6. Conclusion
In this paper, we proposed a new authentication and key management scheme for heterogeneous sensor networks including mobile nodes. The relevant network and mobility models have been presented as well. The proposed key management scheme is based on two different types of the key pools, that is, an authentication key pool and a communication key pool. Based on these pools, a key predistribution mechanism has been defined. Moreover, we compared our solution with some of the existing key management protocols for both homogeneous and heterogeneous sensor networks. The results showed that the two considered key pools not only provide better network connectivity in terms of authentication key sharing in the mobile scenario but also offer better security, while consuming less memory space compared with balanced key predistribution protocols. Furthermore, the proposed solution provides better network resilience against the node capture attacks compared to the other reference protocols considered.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding to the publication of this paper.
Acknowledgment
This paper has been partially supported by the European FP7 project BUTLER, under Contract no. 287901.