Abstract
WSNs are significantly different from the traditional network architecture due to its wireless communication, energy limitation, and computation constraint and environment of the application. Because of these differences, security becomes a critical issue. The path-based denial of service (PDoS) attacks harm the network maintenance and cause serious damage in the resource constrained WSNs. In a PDoS attack, an adversary can overwhelm sensor node and cluster head node to flood packets along the routing path so that intermediate node must keep active mode and exhaust the energy. In this paper, we creatively propose a novel method, which is operated at the base station to detect the malicious behavior. The proposed method is combined with triple exponential smoothing and Markov chain, so that it makes the detection results more accurate. Meanwhile, we first use the concept of black hole to defend the PDoS attack in WSNs. Simulation results are provided to evaluate the performance and illustrate the contribution of this mechanism.
1. Introduction
Wireless sensor networks (WSNs) are generally covered by hundreds of sensor nodes with computation, sensing, and wireless communication modes. And the applications of the WSNs are usually environment monitoring, home-care surveillance, habitat monitoring, military surveillance, and so forth. The sensor nodes are not only low power electronic devices but also deployed in remote areas where power resources are limited. Besides, they are subject to open wireless communication. Since the resources of the sensor nodes are severely constrained and may be deployed in an unattended or even hostile environment, WSNs can be easily attacked by denial-of-service (DoS) attacks, which cause information loss along with large energy expenditure [1]. In DoS attack, an adversary may compromise a sensor node to access all data stored on the node and perform insider attacks [2].
Different types of DoS attacks in different layers have been discussed in [3], and some countermeasures to defend against them are proposed. But in the numerous DoS attack, there is a special form of attack called the path-based DoS (PDoS). The PDoS was first pointed out by Deng et al. [4] in 2005. They described that a PDoS attack begins with the sensor nodes and cluster heads (CHs), compromised of an adversary that floods numerous packets through multihop communication to base station or sink node along the established routing path. As a result, the intermediate nodes in the routing path have to keep active mode and forward the packets so that they cannot return to sleep mode normally. Generally speaking, the PDoS targets the intermediate nodes within the routing path to exhaust their energy. Figure 1 has shown how the PDoS launches the attack.
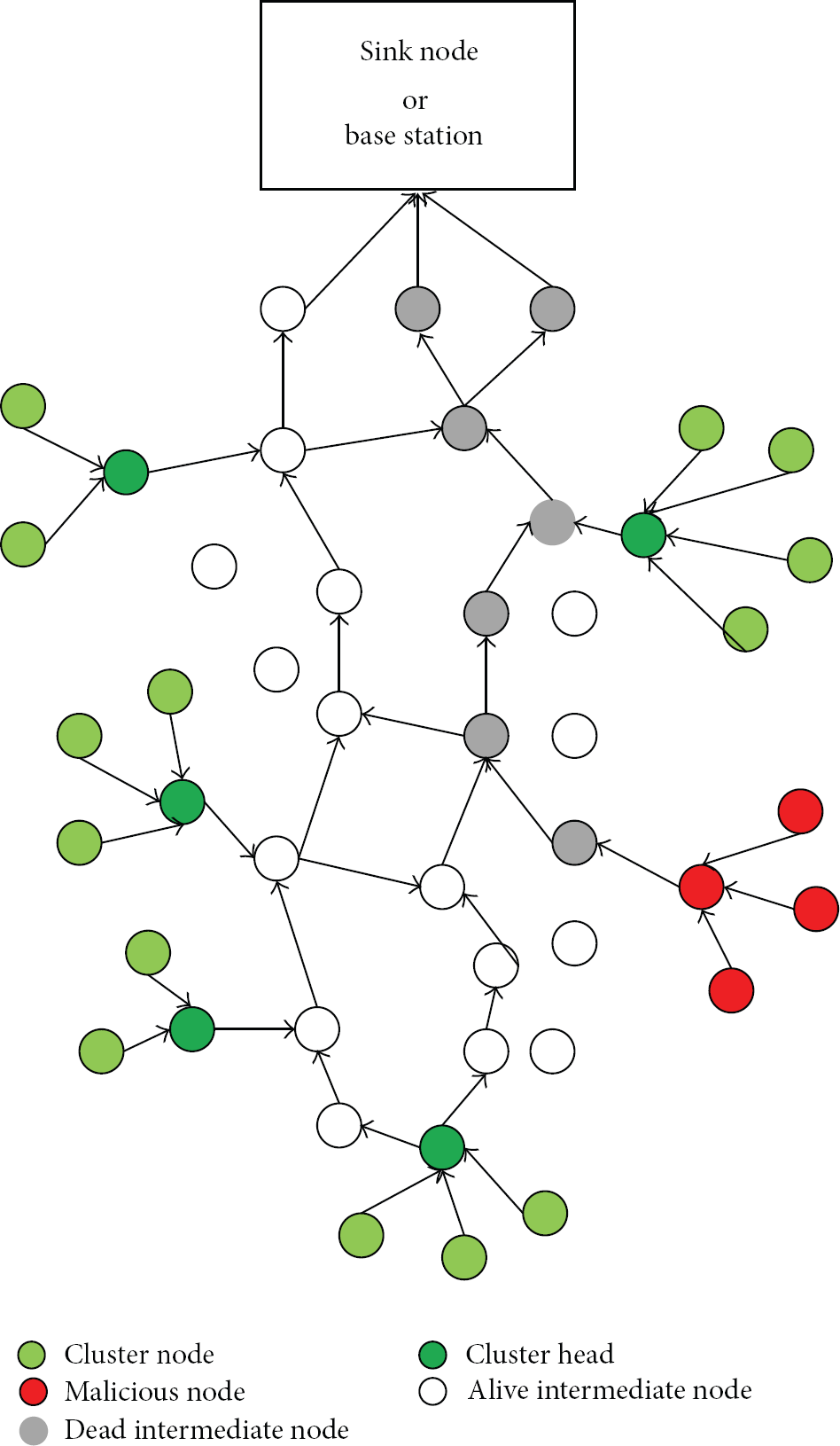
Network attacked by PDoS.
In this paper, we propose a novel method, which combines triple exponential smoothing and Markov chain for detecting the attack behavior. This method is completely different from other detecting algorithms. The proposed method is operated on the base station or sink node rather than in the intermediate nodes, because they have more power and energy. It brings great benefit in conserving energy of the intermediate nodes. Meanwhile, inspired by the concept of black hole, we propose the one-hop black holes mechanism to defend the attack packets sent by the compromised CH. In our mechanism, we put the one-hop intermediate nodes away from the attack CH as the black holes, which attract the malicious packets and drop them. Moreover, the one-hop black hole nodes do not receive the normal data packets.
The rest of the paper is organized as follows. First, we discuss some previous schemes and indicate their problems in Section 2. Section 3 presents the adversary model and network model in the proposed framework. In Section 4, we show the details of our attack behavior detection algorithm. Section 5 illustrates how the mechanism of one-hop black holes defends the PDoS attack. The simulation results are shown in Section 6. Finally, we conclude the paper and give the future works.
2. Related Work
In order to defend against a PDoS attack, the intermediate nodes should be able to detect the malicious packets and then reject them. Deng et al. pointed out that two ways generally are adopted. One is to have the source node establish a separate shared key with other sensor nodes in the routing path. The other is rate control, which limits the number of packets an intermediate node can forward per second. But the highly restricted packet size and nodes at different locations need to forward different numbers of packets per second making these two ways hard to directly defend the PDoS attack. However, several schemes have been proposed to defend the PDoS attack, which are also based on these two ways.
Deng et al. [4] proposed a lightweight secure mechanism, which uses one-way hash chain to defend against PDoS attacks on intermediate nodes in a multihop end-to-end data path in WSNs. Perrig et al. [5] proposed a loosely time synchronous mechanism called the timed efficient stream loss-tolerant authentication (TESLA) broadcast authentication protocol, and it copes with the denial-of-service attacks. However, the time asynchronous problem causes the sensor node to be unverifiable whether the messages are valid or not before the trusted party releases the trapdoor key.
The en-route filtering schemes are widely proposed for intermediate nodes filtering the false data, which are generated by malicious aggregator nodes. Besides, they detect intruders engaged in what we have termed PDoS attacks. The basic idea is that the intermediate nodes share some keys with their member nodes in a node group or cluster. Member nodes generate MACs for reporting data by using the shared keys, and intermediate nodes verify the MACs before forwarding packets [6]. The bloom filter of the statistical en-route filtering (SEF) scheme was proposed by Ye et al. [7] and it is used to reduce the MACs size and ensure their security. Kraub et al. [8] proposed a secure ticket-based en-route filtering (STEF) scheme to protect the data-report. In the data-report, a certain commitment is added through this scheme and the commitment is created by the hash function such as SHA-256. Therefore, the data-report cannot be modified and forged by an attacker. Their proposed scheme defended against an adversary to inject false data into the sensor network.
Cheng et al. [9] proposed an efficient QoS-aware GOR (EQGOR) algorithm. To some extent, this algorithm can resist DoS attack and has a very low time complexity, which is specifically tailored for the resource limitation of sensor devices. But this mechanism is designed for the QoS provisioning in WSNs, and, in some respect, it does not meet the requirements of completely defending the DoS attack.
Li and Batten [10] proposed a solution that uses mobile agents to detect PDoS attacks easily. But this method is just suitable for the small scale WSNs. Ghosal et al. [11] proposed a dynamic TDMA based scheme, which can defend the PDoS attacks. However, it is not designed for the PDoS attack; the performance may be dissatisfactory.
Hence, most previous schemes need intermediate nodes to verify the truthfulness of each data that they received and decide to forward or drop. This wastes the energy consumption of the intermediate nodes. Moreover, the cluster heads have to increase the bits in packet for verification, and this extra overhead also consumes the energy of intermediate nodes when the packets are forwarded. Compared with the previous papers, our mechanism is a novel solution to defend the PDoS and achieves the energy conservation for the intermediate nodes, and hence the network lifetime becomes longer.
3. Assumptions
3.1. Network Model
We focus on two-level distributed heterogeneous sensor network, in which the capacity of computation and energy of cluster head is higher than the sensor nodes. The CHs act as aggregator nodes and are compromised by the adversary. We call the nodes that just forward the packet as intermediate nodes or en-route nodes. Normally, the base station (BS) or base station has no limit on energy and the computation ability is much larger than other sensor nodes. Also, the BS or the sink knows the structure of nodes deployment; the base station knows all neighbor nodes of each other. But, it does not mean that the sink node has known the topology of the network.
3.2. Adversary Model
The adversary controls the compromised nodes and accesses all the secret data to perform insider attacks. The compromised CH floods numerous replayed and false data. Herein, we mainly consider a single point of attack which is able to damage the network for the CHs have more energy. If the adversary is mobile, the resilience scheme can defend the malicious attack.
4. Attack Behavior Detection Algorithm
Without loss of generality, the base station has better capability on energy and computation. Due to the reduced energy of the intermediate nodes, we adopt the base station to validate that the network has been attacked by PDoS or not.
But in this way there are two challenges that we have to overcome: (1) how to effectively and accurately judge that the network is attacked; (2) how to validate the PDoS attack as quickly as possible, so that the network can be resolved quickly and reduces the energy consumption. In this section, we adopt triple exponential smoothing of the time series forecasting and the Markov model based on the nodes energy to solve these problems [12, 13]. Two evaluation factors are considered, the number of the packets and the energy state of the node. Therefore, we can greatly improve the accuracy of the detection and prediction.
4.1. Prediction of the Packets Number with Triple Exponential Smoothing
Due to the located special environment and the characteristics of WSNs, the number of transmitted packets in the network fluctuates over time. For that reason, we choose triple exponential smoothing, which is more suitable for processing time sequence in quadratic curve shape, and forecasting and verifying the attacks. Packets number received by base station in each phase has been shown in Table 1.
Packets number received by base station in each phase.
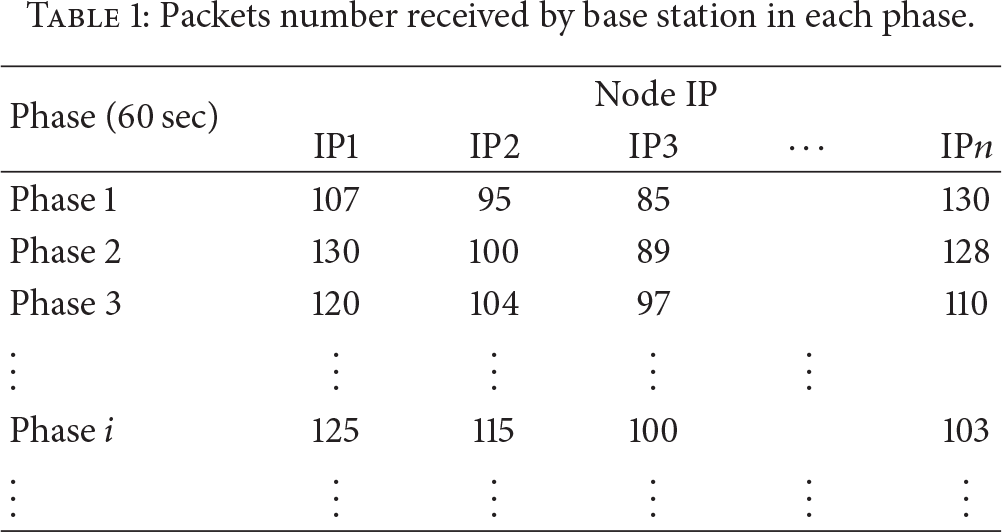
Firstly, the base station will calculate the number of packets that is received from different node in each phase (60 sec) and then take the triple exponential smoothing method to forecast and verify.
Because the triple exponential smoothing values are the third time exponential smoothing based on the quadratic exponential smoothing values, so we need to calculate the first exponential smoothing value and then the secondary exponential smoothing values.
The formula of once and twice exponential smoothing are shown as follows:
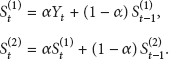
Then, according to the following, we continue to get the third exponential smoothing value:

The
In particular, because the attack happens at any time, we will increase the value of α to improve the weight of recent data and relatively reduce the value of
The prediction of the packet numbers of any target phase is 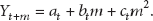
The variable m is the forecast period; namely, the prediction of phase 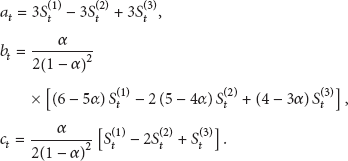
Then, we can get the forecasting value of the phase
The main characteristic of the PDoS attack is continuously sending large number of packets into the network, wasting the energy and power of immediate nodes. In a fixed time period, the number of attack packets is much greater than the normal packets. According to the experiment results and practical experience, we set an upper bound threshold θ, which means that the number of packets sent by the same normal node cannot be larger than θ. Herein, the value of θ can be set freely according to the actual situation in the experiment environment.
Firstly, we acquire the forecasting values of phase
However, this method cannot represent the attack launched by PDoS. Because there are many reasons causing the packet to attack. For example, the intermediate nodes repeatedly forward the same packet when the hardware failure or the ACK packets are not received.
In order to solve this problem and judge the PDoS attack accurately, we further monitor the residual energy of nodes which is based on the node energy consumption value. The energy consumption of nodes is built by the Markov model; it further determines whether the network is attacked by PDoS.
4.2. Prediction Model of the Node Status Based on Markov Chain
By monitoring the nodes energy consumption in each phase, we mark the status of nodes in different time. Therefore, we can get the transfer probability of different status. Based on the transfer probability, we recall a Markov chain model to predict the node energy status in next phase.
First of all, we need to declare some basic conditions.
In each phase, the working time of each node is T, and in this paper If the energy of node is consumed too much in the unit interval Without loss of generality, the energy consumption of each node is from high to low.
The energy of each node is divided into five levels, such as 100%, 75%, 50%, 25%, and 0%. Note that the percentage of energy is based on the residual energy of nodes. The monitor time is
In order to display the individual state of the Markov chain intuitively, we use characters “1,” “2,” “3,” “4,” and “5” to represent the 100%, 75%, 50%, 25%, and 0, respectively. After that, we acquire the Markov state transition diagram as Figure 2.

The transition diagram of Markov state.
Also, we derive the state-transition matrix from the transition diagram as follows:

In the following content, we use an example to elaborate and illustrate how to forecast the energy state of the node.
In the phase i, base station detects the energy information of each node per one second and records the state as normal or abnormal. Therefore, there are 60 states, which are 25 normal states and 35 abnormal states.
The number of state transitions from normal state to normal state is 11; the number of state transitions from normal state to abnormal state is 15; the number of state transitions from abnormal state to normal states is 12; the number of state transitions from abnormal state to abnormal state is 21.
Then, we make the “character 1” to present the normal state, and “character 2” presents the abnormal state. Hence, we can conclude the state as follows:

The state transition matrix of the Markov chain is
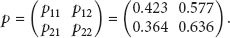
From the matrix of p, we find that
Combining these two methods described above, we are able to judge exactly whether the network has been attacked by PDoS. Firstly, the base station adopts the method of triple exponential smoothing to forecast the number of the packets at phases
The flow diagram of attack behavior detection algorithm is shown in Figure 3.
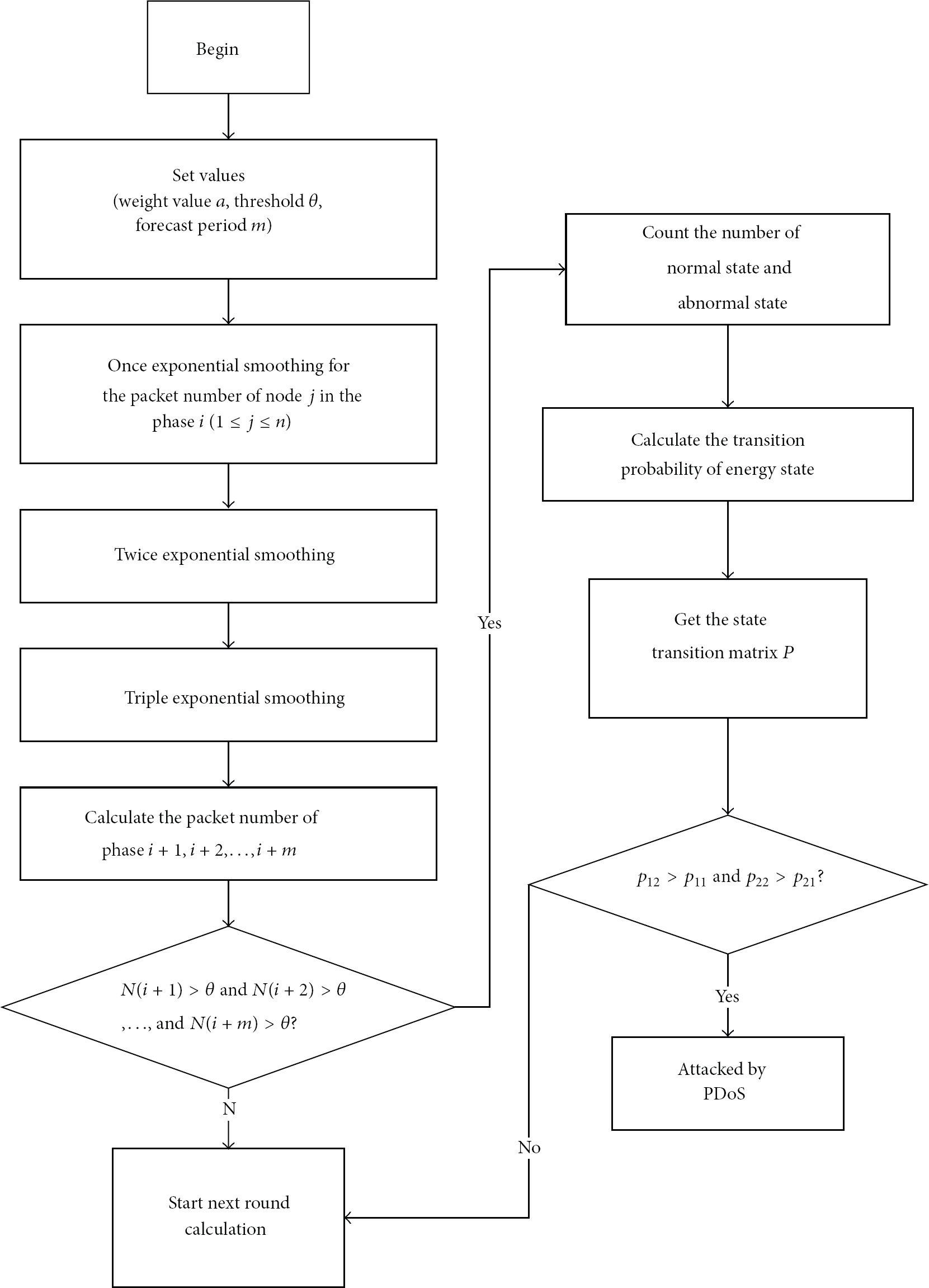
The flow diagram of attack behavior detection algorithm.
5. One-Hop Black Holes Mechanism
By using the attack behavior detection algorithm that has been described above in detail, it would be easy to detect whether the network has been attacked and locate where the adversary launched an attack accurately. However, just detecting attack behavior is not our ultimate goal because the network is still vulnerable to the PDoS attack. In addition, we are committed to propose an efficient mechanism, which is called one-hop black hole mechanism to defend the PDoS attack and make the attacked network return to normal. The details of this mechanism are described below.
Once the base station or base station detects that the network has been attacked, it also knows the IP address or other information that can uniquely identify the attack node (in this paper, CH is the attack node) through the proposed attack behavior detection algorithm. Then, it is easy to know the location of the adversary and the IP addresses that are one hop away from the adversary node for the base station knows the structure of the network in advance. With this information in hand, the base station will broadcast some specific packets that contain the corresponding IP addresses to the specific intermediate nodes. We call these special packets control packets. And these specific intermediate nodes are the nodes that are one hop away from the compromised CH. The purpose of the control packet is to turn the one-hop nodes around the compromised CH into the black holes. In other words, the control packets will transform these one-hop intermediate nodes into one-hop black holes. Using the only receiving/not forwarding character of black hole, the one-hop black holes will just receive the attacking packets sent by the compromised CH and then drop them without forwarding. At the same time, they will not receive the normal packets. Then, the attack packets cannot be flooded into the network, and the network successfully defends the PDoS attack. Figure 4 shows how the one-hop black holes defend the PDoS attack.

One-hop black holes mechanism.
5.1. AODV Protocol
In order to verify and prove our scheme, we select the well-known AODV protocol as the routing protocol.
AODV is an on demand routing protocol and is capable of both unicast and multicast routing. It establishes routes between nodes only as desired by source nodes. It maintains these routes as long as they are needed by the source nodes. Additionally, the AODV protocol forms tree structure which connects multicast group members. The trees are composed of the group members, and the nodes need to connect the members. AODV uses sequence numbers to ensure the freshness of routes. It is loop-free, self-starting, and large scales of member nodes.
The routing table of AODV protocol is composed of the following fields:
destination IP address; destination sequence number; destination only flag; next hop IP address; hop count; precursor list; life time; network layer interface; other state and routing flags.
There are three main message types in the AODV protocol, which are route requests (RREQs), route replies (RREPs), and route errors (RERRs). Herein, we mainly introduced the RRER packets, because the following control packet is designed and modified by the RRER packets. The format of the RRER message is depicted in Table 2 and contains the following fields:
Type: 3; N: no delete flag; set when a node has performed a local repair of a link, and upstream nodes should not delete the route; Reserved: set as 0; ignored on reception; DestCount: the number of unreachable destinations included in the message and must be at least 1; Unreachable destination IP address: the IP address of the destination became the unreachable address due to break link; Unreachable destination sequence number: the sequence number in the route table entry for the destination listed in the previous unreachable destination IP address field.
The format of RRER packets.

However, the AODV protocol is designed for applying in the ad hoc network; it is not completely suitable for the path-based and hierarchical WSNs. For this reason, we modified the AODV protocol to make it applicable. According to the characters of the AODV, the control packet and the routing table are also revised and redesigned.
We design the control packet based on the RRER packet, and the format is shown in Table 3.
The packet format of the designed control packet.
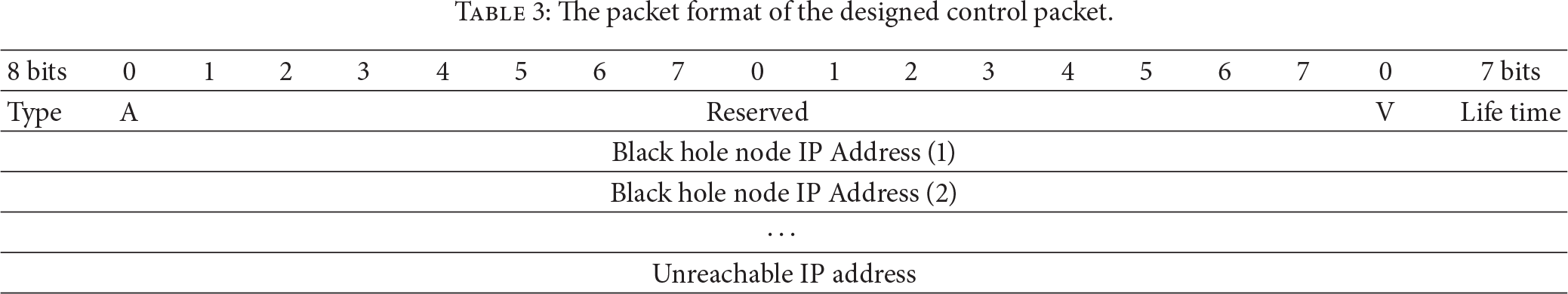
The meaning of each field is described as follows:
Type: 5; A: acknowledgment required; Reserved: set as 0; V: void; it means the entry that unreachable IP address which is the destination IP address of the routing table belongs to void or invalid during the life time; Life time: it means the length of invalid time; if the time goes out, the entry will return valid state from invalid; Unreachable IP address: the address of base station or BS; Black hole node IP address: the destination of the control packet; Black hole node sequence number: the sequence number in the route table entry for the destination listed in the previous unreachable destination IP address field.
The base station will first broadcast the control packet. The nodes that received the control packet will verify the destination or not by themselves. The verification is checked through the black hole node IP address field of the control packet. If the IP address is not from black hole node, they will forward it again. When the one-hop nodes of the compromised CH receive the packet, they will send an acknowledgement message to the base station first. It is checked according to the field of A in control packet. Then, the routing table is updated. On the other hand, one-hop node/nodes of the compromised CH will locate the entry/entries that the unreachable IP address is set to the destination IP address of the routing table. After that, the other state and routing flags field of the entry/entries is/are set with V, to make the entry/entries void or invalid. This step ensures that the one-hop nodes of the compromised CH become the black holes. Then, the attack packets will be received and dropped by black hole nodes and cannot be flooded into the network.
Additionally, the time length that the entry is invalid can be set in the life time field based on the control packet. If time is out, the entry returns valid from the invalid state. This reflects the resilience of our scheme. When the attack has stopped or the compromised CH has exhausted the energy before the black holes, the black hole nodes can return to normal intermediate nodes and forward the normal packets with this scheme.
5.2. Modification of the SMAC Protocol
However, there is an important challenge that we should solve. If the network has been attacked in a period of time, which means the attacking path has been established. The control packet cannot be received by the black hole nodes since they are busy with forwarding the attacking packet. In order to handle this problem, we make a little modification on the SMAC protocol. SMAC mechanism allows nodes to sleep periodically after a certain time of listening for reducing energy consumption.
Figure 5 describes the frame structure of the SMAC protocol. If the attacking path has been established, the SMAC needs to continue the receiving state and receives the attacking packets. Here, we add a timer in the SMAC, setting a threshold T for receiving state. As illustrated in Figure 6, the receiving state will be forced into sleep state if timeout. The value of T can be set initially and adjusted through the practical application. It would be specially mentioned that there is no a unique optimized value of T. According to the observation of our simulation, while the sending rate of the attack packet is different, the value of T should be set different values to defend the attack with the shortest time. Then, the control packet may defeat the attacking packets when they compete with each other for the media at the new frame. Besides, the control packet can be successfully received by the one-hop nodes of the compromised. As the mentioned before, these nodes are able to become the black holes and defend the PDoS attack.

The frame structure of the SMAC.
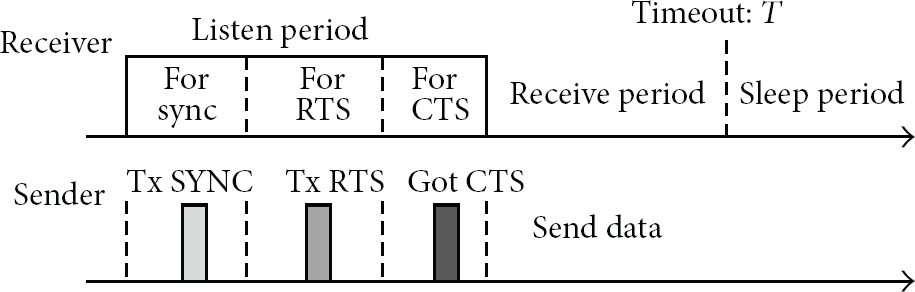
The revised structure of the SMAC.
6. Simulation
The simulation is conducted on NS2 simulator, and the used parameters are shown in Table 4.
Simulation parameters.

We experiment a scenario to simulate the energy consumption of intermediate nodes. Figure 7 shows that the network was attacked at 4 minutes, and the base station detects that the number of packets was larger than 15000 in the next few minutes. Then, the control packet was sent to the one-hop nodes which are one hop away from the malicious nodes, and, after a short period of time, our scheme begun to defend the PDoS. Therefore, the energy conservation of the proposed scheme is higher than the result without scheme.

The remained energy with varying time.
Figure 8 shows that the congestion level of the network is attacked by PDoS. The congestion level was measured with the ratio of the total number of packets and the maximum number of packets in the network at the current moment. From Figure 8, we can see that the congestion level was keeping about 80%. It would be specially mentioned that the nodes that are in the attacking path may not include all intermediate nodes in PDoS. That is, the congestion level cannot reach 100% or 0%. The congestion level is kept in a high ratio which means that the intermediate nodes cannot return to sleep mode from the forwarding state. Then, the energy must exhaust quickly. Figure 9 has shown the congestion level of the network protected by our scheme after 9 minutes. We found that there is a sharp decline of the congestion level, which is a significant improvement. Finally, the network trends to be normal. Just like the reason that we have mentioned above, the ratio of the congestion level cannot reach 0%.
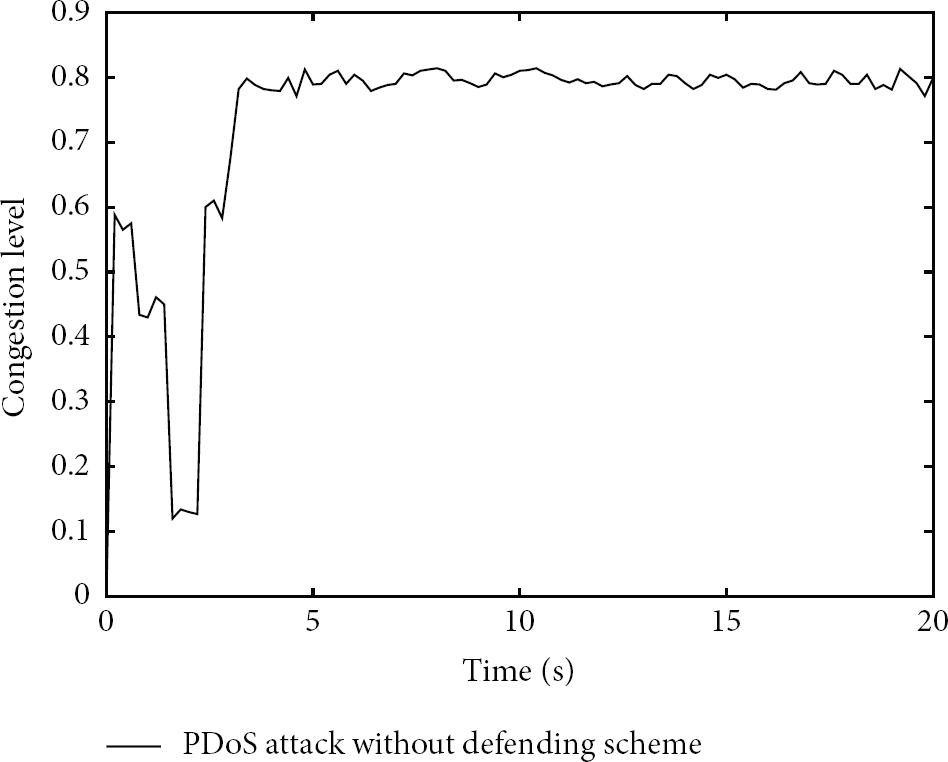
Congestion level of the network with PDoS attack.

Congestion level of the network with our scheme.
7. Conclusion and Future Work
In this paper, we propose a novel solution to defend the PDoS attack. We put forward an attack behavior detection algorithm using triple exponential smoothing and Markov chain. In particular, this algorithm is operated at the base station, which makes the minimum energy consumption of the intermediate nodes. Therefore, they do not need to detect every packet for verifying they are normal or abnormal. And two evaluation factors are considered, the number of the packets and the energy state of the node. These two factors are guaranteed to achieve the accuracy detection. Meanwhile, in order to completely defend the PDoS attack, we propose one-hop black holes mechanism, which makes the intermediate nodes that are one hop away around the malicious CH as the black holes. These nodes can just receive the attacked packets which are sent by malicious nodes and drop them. In addition, we design the recovery scheme for the one-hop black hole nodes to make the whole mechanism more flexible. In the future, we want to apply this mechanism to various and different network protocols and improve it for the better energy-efficient based on the existing basis.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This research is supported by the National Natural Science Foundation under Grant no. 61371071, Beijing Natural Science Foundation under Grant no. 4132057, Beijing Science and Technology Program under Grant no. Z121100007612003, and Academic Discipline and Postgraduate Education Project of Beijing Municipal Commission of Education.
