Abstract
The process of creating secure embedded systems with sensor network is highly challenging and complex, particularly from a technical viewpoint. A secure embedded system is used for a specific purpose and operation, and needs hardware-software codesign methodology. As such, there are many considerations in terms of system design when the system developer creates or constructs a secure embedded system with sensor network. However, there is a lack of research into quality models in the area of secure embedded systems in sensor network. This paper seeks to redress this issue by presenting a quality model for a secure embedded system with sensor network. Each quality for the secure embedded system is constructed according to DeLone and McLean's success information system, and has subcriteria according to their characteristics. The present research also focuses on making a quality model network which considers the correlation between the qualities' attributes.
1. Introduction
The computer communication system demands user or human centric system that it can guarantee security properties such as authenticity, integrity, privacy, anonymity, and availability [1]. Nowadays, embedded system has been applied to many areas like smart phones, communication system, information system, control system, and so on. And embedded real-time systems become more and more complex as the traditional development process of manual coding from scratch followed by tedious testing is becoming inadequate. Nowadays success in the development of embedded systems depends on aspects such as low cost, reliability, quickness to market, and cost-effective variations in the product [2]. In an embedded systems environment, there are often limitations in terms of processing power, storage capacity, network bandwidth, and so on, and these factors are at odds with the computationally intensive nature of the cryptographic algorithms underlying many security protocols [3].
In particular, in sensor network environment [4–7], embedded system needs more security technique to improve reliability and efficiency. We call it to secure embedded system. Secure embedded systems are vulnerable to attacks, like physical tampering, malware, and side-channel attacks. Therefore design of secure embedded systems has to be guided by the following factors: small form factor, good performance, low energy consumption, longer battery life, and robustness to attacks [3]. So, when the engineer or system designer develops a secure embedded system with sensor network, they have to consider the environment of specific application: secure embedded software must typically fulfill stringent QoS (Quality of Service) (nonfunctional) requirements imposed by the runtime environment such as severely limited CPU power and memory, network bandwidth, authenticity, and the application domain such as hard real-time constraints. However it is difficult to consider all of these characteristics at the same time. And it needs to identify the quality criteria and to consider the correlation. In the contents, there is a lack of research into practical quality models for secure embedded systems with sensor network.
Decision-making systems could be helpful in identifying the relationship between the quality criterions and to extract important criteria from among these. The Analytic Hierarchy Process (AHP) [8] is one of the widely used approaches to handle such a multicriteria decision-making problem. However, a significant limitation of AHP is the assumption of independency among the various criteria of decision-making. The analytic network process (ANP), on the other hand, captures interdependencies among the decision attributes, thus allowing for a more systematic analysis. It also allows inclusion of all the relevant criteria that have some bearing on arriving at the best decision. Contrary to AHP, ANP provides a more generalized model in decision-making without making assumptions about the independency of the higher-level elements from lower-level elements and also of the elements within a level. Despite all these merits, the applications of ANP are not very common in a decision-making problem scenario. However, in recent years, there has been an increase in the use of ANP in multicriteria decision-making problems [9].
In this paper, this research aims to present a quality model for secure embedded systems with sensor network which takes into consideration the correlation between the quality criterions. Each of quality criteria has been extracted from DeLone and McLean's model, which is one of the most famous and successful models. The quality criteria of the system have many subcriteria resulting in different characteristics for the secure embedded system. For multicriteria decision-making problems, this research uses ANP. Finally, the research will suggest what the important criteria in secure embedded systems with sensor network for system engineer are.
2. A Secure Embedded System and Its Quality Model
2.1. A Secure Embedded System with Sensor Network
Generally, embedded systems are commonplace; in industrialized countries they outnumber people by about an order of magnitude. This includes smart phones and applications, cars, entertainment devices, and broadband modems. With our increasing dependence on embedded systems, their reliability and security become the most important issue, because embedded systems (e.g., smart phones) are used to perform financial transactions and also to store increasing amounts of sensitive personal data [10]. Therefore secure embedded systems are typically characterized by a specific functionality in a specific domain, where the software element is taking an increasingly important role [11]. Secure embedded software typically faces some unique constraints not found in desktop software or enterprise systems, such as limited resources, real-time requirements, hardware integration, cryptographic algorithms, and authenticity. Sadeghi and Stüble [1] suggest fundamental security requirements for building secure systems as follows.
Trusted Computing Base (TCB): all components that can violate the defined security policy should be correct and trustworthy. Integrity of the TCB: the TCB should be protected from manipulations to guarantee the enforcement of security policies. Confidentiality and integrity of application code and data. Enforcing least privilege: a process should not be given more privilege than necessary to perform a task. Trusted path to user: the inputs/outputs of the application a user interacts with should be protected from unauthorized access by other applications. Secure channel to devices and between applications: the integrity, confidentiality, and authenticity of interapplication communication should be maintained. Secure random numbers.
Besides, many secure embedded devices are often a part of some safety-critical system where failures are not acceptable. So, embedded devices should be reliable [2] and lightweight. In this case, lightweight means having an ability to easily be secure embedded in applications. Brinksma et al. [12] describe a lightweight component model that is being used to develop low-level programmable networking software. This model incorporates lightweight reflective mechanisms to assist in run-time deployment and dynamic reconfiguration of component compositions. Coulson et al. [13] proposes a model that can be implemented on a wide range of device types, including very small devices such as sensor motes.
2.2. A System Quality Model
Generally, QoS aspects with security requirements are a nontrivial operation involving both the description of the system functional behavior and the definition of the performance-related configuration parameters [14]. In a well-known success QoS model for the system, DeLone and McLean aimed to present influential criteria and their relationships. Since their introduction, the model has been applied and modified across hundreds of studies which prove that a general approach is needed to measure success. DeLone and McLean modified their model later and instead of five criteria (“system quality,” “information quality,” “use,” “user satisfaction,” and “individual impact”) that influence “organizational impact” the new model includes six criteria that influence “net benefits.” The developed model included “service quality” as a new criterion, “individual impact” was removed, and “intention to use” was added in relation to “use.” In addition, “net benefits” replaced “organizational impact” as an output of the measure [15]. DeLone and McLean [16] described the subcriterions which are in each quality of the model as follows.
System quality measures the desired characteristics of a system. Usability, availability, reliability, adaptability, and response time (e.g., download time) are examples of qualities that are valued by users of a system. Information quality captures the e-commerce content issue. Web content should be personalized, complete, relevant, easy to understand, and secure if we expect prospective buyers or suppliers to initiate transactions via the Internet and return to our site on a regular basis. Service quality, the overall support delivered by the service provider, applies regardless of whether this support is delivered by the IS department, a new organizational unit, or outsourced to an Internet service provider (ISP). Usage measures everything from a visit to a Web site, to navigation within the site, to information retrieval, to execution of a transaction. User satisfaction remains an important means of measuring our customers' opinions of our e-commerce system and should cover the entire customer experience cycle from information retrieval through purchase, payment, receipt, and service. Net benefits are the most important success measures as they capture the balance of positive and negative impacts of e-commerce on our customers, suppliers, employees, organizations, markets, industries, and economies and even our societies.
3. The Analytic Network Process
The analytic network process (ANP) is the most comprehensive framework for the analysis of public, governmental, and corporate decisions. It allows the decision maker to include all the factors and tangible or intangible criteria that have a significant effect on making a best decision. The ANP allows both interaction and feedback within clusters of elements (inner dependence) and between clusters (outer dependence). Such feedback best captures the complex effects of interplay in human society, especially when risk and uncertainty are involved [17]. The determination of relative weights in ANP is based on the pairwise comparison as in the standard AHP. Pairwise comparisons of the elements in each level are conducted with respect to their relative importance towards their control criterion based on the principle of AHP. Saaty [18] suggested a scale of 1–9 when comparing two criterions as shown in Table 1.
Scale of 1–9 of Saaty.
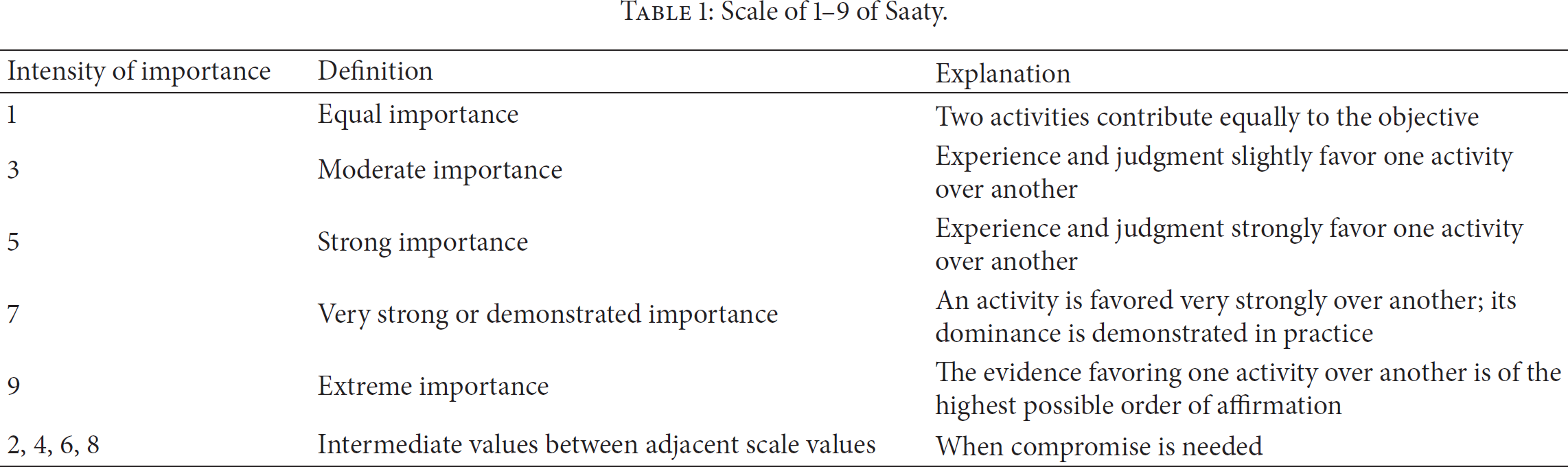
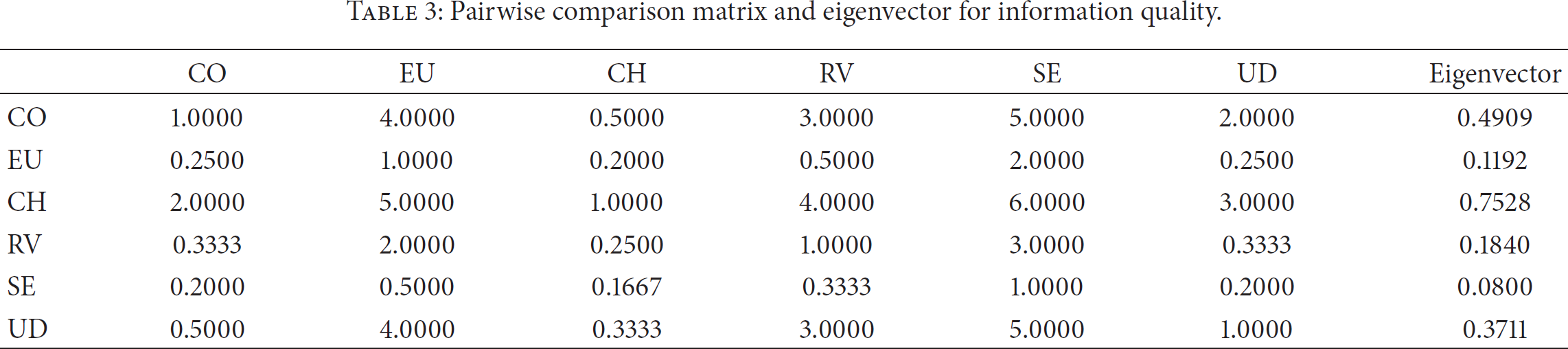
The score of 
4. Quality Attributes for a Secure Embedded System with Sensor Network
The advantage of this methodology is that it not only supports decision-making for multicriteria on a secure embedded system but also suggests significant factors to the system developers or us. For this process, this research has to identify the quality attributes for a secure embedded system. However, the DeLone and McLean model is not suited to secure embedded systems in sensor network environment.
In particular, to consider security factor, Ravi et al. [19] propose the security requirements for embedded systems as follows.
User identification refers to the process of validating users before allowing them to use the system. Secure network access provides a network connection or service access only if the device is authorized. Secure communications functions include authenticating communicating peers, ensuring confidentiality and integrity of communicated data, preventing repudiation of a communication transaction, and protecting the identity of communicating entities. Secure storage mandates confidentiality and integrity of sensitive information stored in the system. Content security enforces the usage restrictions of the digital content stored or accessed by the system. Availability ensures that the system can perform its intended function and service legitimate users at all times, without being disrupted by denial-of-service attacks.
In terms of quality issues for secure embedded systems, it is necessary to consider criterion with security in embedded environments which have limited resources. These include memory and screen size, in addition to system performance such as CPU speed, and key pads, authenticity, reliability, each applying differently to its environment according to its individual purpose. Therefore the research extracts each criterion from the existing DeLone and McLean model and adapts it to our purpose. The proposed secure embedded system's quality consists of 5 criteria, system quality, information quality, function quality, efficiency quality, and maintenance quality, as described below.
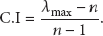
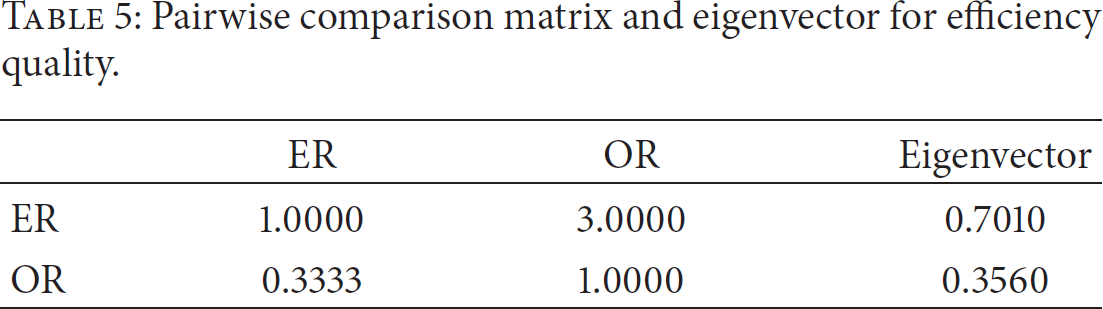
Systems quality has 8 subcriteria: adaptability (AD), availability (AV), reliability (RE), response time (RT), maturity (MA), fault tolerance (FT), recoverability (RA), and stability (ST). Information quality has 6 subcriteria: completeness (CO), ease of understanding (EU), characterization (CH), relevance (RV), security (SE), and being up-to-date (UD). Function quality has 6 subcriteria: assurance (AS), responsiveness (RP), usability (UA), operability (OP), interoperability (IP), and suitability (SU). Efficiency quality has 2 subcriteria: error rate (ER) and operation rate (OR). Maintenance quality has 4 subcriteria: analyzability (AA), changeability (CA), MTTR (mean time between repair (MR)), and MTBF (mean time between failures (MF)).
5. ANP Model for a Secure Embedded System with Sensor Network
Using the proposed quality attributes, this research proposes a quality model which is of benefit to a secure embedded system. According to the relation of each quality shown in Figure 1, this research considered the correlation between the subcriteria and calculated pairwise comparisons and eigenvectors.

Proposed quality model for a secure embedded system.
Table 2 shows the value after processing of system quality;
Pairwise comparison matrix and eigenvector for system quality.

Pairwise comparison matrix and eigenvector for information quality.
Pairwise comparison matrix and eigenvector for function quality.

Pairwise comparison matrix and eigenvector for efficiency quality.
Pairwise comparison matrix and eigenvector for maintenance quality.

As a result of this process, this research shows the numerical value of the degree of influence of each quality and subcriteria for the secure embedded system. The result of the final priority weight calculation is summarized in Table 7. In this result, to develop a successful secure embedded system, this research considered the following criteria as significant factors: adaptability (AD) in system quality, characterization (CH) in information quality, suitability (SU) in function quality, operation rate (OR) in efficiency quality, and MTTR (mean time between repair (MR)) in maintenance quality.
The result of the final priority weight calculation by ANP.

6. Conclusions
This paper aimed to address the need for a quality model for secure embedded systems which use ANP. In particular, the quality attributes have to consider the special environment of the secure embedded system, such as situations that have many limitations to use or develop applications or software. This research constructed 5 criteria—systems quality, information quality, function quality, efficiency quality, and maintenance quality, for secure embedded systems. The research also addressed each criterion's relation to and influence on other criteria. Ultimately, this research was able to find the most significant criterion between the qualities as a result of the ANP process.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
The research was supported by the Ministry of Science, ICT and Future Planning (MSIP), Republic of Korea, under the Information Technology Research Center (ITRC) support program (NIPA-2014-H0301-13-4007) supervised by the National IT Industry Promotion Agency (NIPA).
