Abstract
Data source location privacy (DSLP) is of great importance for some asset monitoring applications in wireless sensor networks (WSNs). Besides the source simulation (SS) method to protect the DSLP against a global eavesdropper in WSNs, other existing methods are based on the panda-hunter game model (PHGM) without considering the communication between data sources and reporter sources, which can cause them to be ineffective. Moreover, there are two limitations in SS. First, the reporter source cannot generate effective event reports. Second, it is unsuitable to track multiobjects accurately. To address the former issue, an improved source simulation (ISS) method is proposed which adjusts the event report strategy. To solve the latter issue, an updated-panda-hunter game model (UPHGM) is proposed and a formal model of the DSLP issues is also presented. Then, based on the UPHGM, an energy-efficient grid-based pull (GBP) scheme is designed to protect the DSLP by combining a light-weight security object collection scheme with an effective grid partition method. Analysis and simulation results show that GBP outperforms SS and ISS in terms of energy cost on the whole.
1. Introduction
A wireless sensor network (WSN) typically consists of a large number of nodes which integrate sensor modules, processing modules, wireless communication modules, and energy modules to sense physical or environmental conditions and collect data. WSNs have promising application prospects in both military and civil domains, such as military surveillance, wildlife habitat monitoring, target tracking, and home automation [1–3]. Compared with traditional networks and ad hoc networks, WSNs have several typical characteristics, such as restricted-resource, no infrastructure, and large number of nodes. These characteristics lead to more challenges in the research of security problems in WSNs [4, 5].
Many works to date in WSN security have focused on providing authentication, confidentiality, integrity, and freshness services. However, for some special applications, it is not enough to provide those security services solely. For example, in the panda-hunter scenario [6], called panda-hunter game model (PHGM), a WSN is deployed to track endangered giant pandas in a vast panda habitat. Each panda carries an electronic tag, called tag-node in this paper, to emit event-trigger-signals, which can be detected by sensors. When a sensor node, called reporter source, detects this signal, it generates an event report and then sends it to a sink node with the help of a security route mechanism. An adversary (the hunter) may locate the monitored pandas, called data sources in this paper, either by detecting the event-trigger-signals or via eavesdropping on the communication between the reporter sources and the sink nodes. Therefore, it is very important to provide the data source location privacy (DSLP) service for this kind of applications.
At present, many efforts have been done to protect the DSLP in WSNs [7, 8]. However, most of them are effective only for local adversaries who merely monitor the local network traffic. For a global adversary, who can monitor the whole network traffic, these approaches would not work. Recently, several schemes have been proposed to protect the DSLP against a global adversary [9–19]. However, most of them except the source simulation (SS) method in [9, 10] ignore the communication between data sources and reporter sources, which makes these approaches ineffective. Moreover, the SS method also has two limitations. (1) The reporter source cannot generate effective event reports. (2) It is unsuitable to track multiobjects accurately.
In this paper, we focus on protecting the DSLP against a global adversary who can monitor and collect all the messages transmitted in the network at all time. The contributions of this work are summarized in the following.
We point out the existing problems of the source simulation method in [9, 10] and propose an improved source simulation (ISS) method under the panda-hunter game model (PHGM) by adjusting the event report strategy. The ISS method copes with the defect existing in SS, in which the reporter source cannot generate effective event reports. We propose an updated-panda-hunter game model (UPHGM), which overcomes the disadvantage of the PHGM and is suitable to monitor multiobject sources. Also a formal model of the DSLP issues under the UPHGM is given. We present an energy-efficient grid-based pull scheme to protect the DSLP under the UPHGM, which includes a light-weight security object collection scheme and an effective grid partition method. It can make sure at wherever a data source lies there is at least one node which can authenticate and collect its related information; meanwhile it can provide security services including confidentiality, authentication, integrity, freshness, and source location privacy. Compared with the source simulation method and the improved source simulation method, it is more energy-efficient. We evaluate the energy overhead in both theory and simulation. The results show that (1) the grid-based pull (GBP) method outperforms the SS method and the ISS method on energy overhead on the whole; (2) the energy cost of ISS is comparable to that of SS under low privacy requirement.
The rest of the paper is organized as follows. Section 2 discusses related work. In Section 3, the improved source simulation (ISS) method under the panda-hunter game model (PHGM) is described. In Section 4, the updated-panda-hunter game model (UPHGM) and the formal model of the DSLP issues are presented. In Section 5, the grid-based pull scheme under the UPHGM is proposed. Section 6 describes our evaluations, and Section 7 concludes the paper.
2. Related Work
In [7, 8], extensive surveys have been conducted on the location privacy problem in WSNs. According to adversaries' capability of monitoring network traffic, existing approaches can be classified into three classes: countering a local adversary [6, 20–28], countering several local adversaries [29], and countering a global adversary [9–19]. In this section, we briefly survey the major related works to provide the DSLP under a global adversary in WSNs.
In [9, 10], two techniques, called periodic collection and source simulation, respectively, were proposed to prevent the leakage of the DSLP. The main idea of the periodic collection method, also called ConstRate scheme in [11], is to make the traffic pattern independent of the presence of real objects. Each node periodically sends packets at a reasonable frequency regardless of whether it has real data to send or not. However, this approach consumes a substantial amount of energy for latency sensitive applications. And it does not consider the traffic generated by electronic tags, which can also be used to infer the locations of monitored objects by the adversary. By simulating the movement patterns of real objects, the source simulation (SS) method creates candidate traces in the network to hide the traffic generated by real objects. It works as follows: before deployment, select L nodes as token node and preload each of them with a unique token ID. After deployment, each token node can mask as a real object to emit event-trigger-signals for event detection. When a node detects the signal, it generates an event report and delivers it to the sink node. The token node then determines the token node of the next round in its neighborhood (including itself) and passes the token to the selected node. In order to prevent the adversary using the token pass messages to distinguish real objects from fake ones, the nodes that detect the real object also need to send a masked token pass message each round. However, this approach has two problems to affect the information collection about real objects. First, as the event-trigger-signals emitted by token nodes and real objects are the same, not only the adversary cannot distinguish from them, but also nodes in the network cannot distinguish from them. As a result, nodes cannot determine whether real event reports or dummy event reports are generated. Second, when there are two or more objects in the network, if a node detects two event-trigger-signals in two rounds, it cannot distinguish whether the signals come from two objects or from one object. Hence, it cannot track multiobjects accurately.
A fitted probabilistic rate scheme, called FitProbRate, was devised in [11] to reduce the event report delay in ProbRate scheme. In ProbRate scheme, the time intervals between message transmissions follow the exponential distribution. In order to reduce the real event report latency, the nodes send the real event reports as soon as possible while keeping the message transmission intervals following the same distribution. Based on the FitProbRate, a distributed resource allocation algorithm was proposed to achieve data source anonymity by mixing real event messages with carefully chosen dummy traffic in [12]. However, the FitProbRate scheme only considers the event indistinguishability, in which the intertransmission times of the real event reports are indistinguishable from the desired distribution of fake transmissions, and ignores the interval indistinguishability, in which the intertransmission times of fake and real intervals are indistinguishable. The adversary can distinguish the real intervals from the fake intervals and then discovers the real objects. In order to solve this problem, an improved method was proposed in [13, 14]. They introduced the same correlation of intertransmission times during real intervals to intertransmission times during fake intervals.
To reduce the traffic caused by the ConstRate scheme in [9, 10] and the ProbRate scheme in [11], based on proxies and data aggregation, a proxy-based filtering scheme (PFS) and a tree-based filtering scheme (TFS) were presented in [15]. In PFS, proxies are selected to collect and filter dummy messages from surrounding nodes. Also proxies are formed into a tree hierarchy and the dummy messages are dropped on the way from proxies to sink nodes. In order to explore the impacts on the network lifetime of proxy filtering approaches, different proxy assignment strategies and different deployment scenarios were investigated in [16]. In [17], a data aggregation scheme based on a cluster-tree hierarchical architecture was proposed to reduce the message overhead by aggregating multiple messages in a single transmission. However, these approaches are also not suited for latency sensitive applications, because when a node detects a real event, it delays the transmission of the real event report such that the next intermessage interval follows the normal application distribution. Similar to periodic collection in [9, 10], these approaches also do not consider the traffic generated by electronic tags.
In [18], four schemes, called naïve, global, greedy, and probabilistic, were proposed to protect the DSLP against a global adversary. The naïve scheme is similar to the periodic collection method in [9, 10]. Every node periodically sends a real or forge message. The time interval between message transmissions is usually quite long to reduce the communication cost. Therefore, this approach can cause long delay. In order to reduce the delivery latency, the global and the greedy approaches were presented to discover the shortest delivery latency path. However, the global approach requires the knowledge of global network topology and transmission schedules, which are impractical for every node to store the topology of the whole network and to compute the fastest path. The greedy approach is a heuristic method. Every node chooses the neighbor that has the shortest waiting time and is closer to the sink node as the next hop route node. In order to reduce the communication overhead, a probabilistic approach was proposed. This approach lets every node probabilistically transmit messages to guarantee that every node can hear a message during any fixed period of time. However, it ignores that a real object may be detected by some nodes simultaneously, which will generate event reports and lead to more network traffic around the object. This abnormal traffic can help the adversary to discover the real object.
In [19], a spatiotemporal process replication scheme for generating dummy network traffic was proposed to disguise the real event report. The method assumed that monitored events obey a Poisson temporal distribution with a known rate and uniform spatial distribution over the network area. A subset of nodes regularly acts as fake sources and generates dummy network traffic with the same event distribution. However, the method ignores the spatial correlation of events about a real object, which can help the adversary locate the real object. For example, the traces of a panda do not follow uniform spatial distribution over the network during a relatively short period of time. The adversary can locate the panda by observing the traces in a relatively small network area.
3. Improved Source Simulation (ISS) Method under the PHGM
As mentioned above, all of the prior approaches except the SS method in [9, 10] ignored the event trigger process from tag-nodes. The adversary can defeat all of these approaches by monitoring the additional traffic from tag-nodes. Therefore, to avoid this situation, we should adopt the SS method to simulate the additional traffic pattern generated by tag-nodes. However, as described in Section 2, the SS method has two defects. First, a reporter source cannot generate effective event reports since the event-trigger-signals emitted by token nodes and tag-nodes are indistinguishable. Second, it is not suited to track multiobjects accurately. In this section, we propose an improved source simulation (ISS) method to solve the first problem for single-object monitoring applications. For multiobjects monitoring applications, in order to track the objects effectively and accurately, the event-trigger-signals should contain related information of the monitored objects. The corresponding solving approach will be presented in Section 5.
3.1. Protocol Description
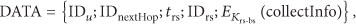
Before deployment, randomly select L nodes as token nodes and preload each of them with a unique token ID. Every token node will mask as a real object to emit event-trigger-signals for event detection. We assume that the infrastructure of secure communications has been established after deployment. Note that, in this approach, the adversary is similar to the one considered in [9–16, 18, 19]; that is, it cannot compromise any sensor node. The event report process includes the following three steps as shown in Figure 1.

Event report process of the ISS scheme.
(1) Emit Event-Trigger-Signal. A token node or a tag-node emits an event-trigger-signal for event detection around its local area. A node that detects the signal sets itself as a candidate reporter source.
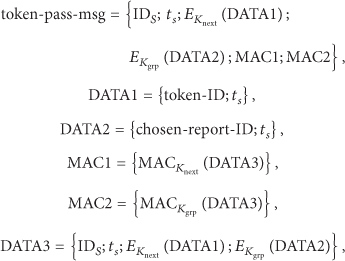
(2) Pass Token. The token node and the candidate reporter sources send the messages called token-pass-msg according to their roles, respectively. We assume that the length of the time interval for passing the token-pass-msg, called token-pass-slot, is
After the token node emits an event-trigger-signal, it sets a timer called timer-for-token-passing with value
Upon detecting the event-trigger-signal, the candidate reporter source also sets a timer called timer-for-token-passing with value
Upon receiving a token-pass-msg, the node
(3) Generate and Send Event Reports. When the token-pass-slot is over, the token node and the candidate reporter sources generate and send event reports according to the following situations.
If the generate-flag of the node If the report-flag of the node
Compared with source simulation method in [9, 10], the ISS method has two main advantages. (1) Candidate report sources can distinguish real events from fake events by authenticating token-pass-msgs. (2) Only one node generates an event report for each event-trigger-signal and the amount of network traffic can be reduced largely.
4. UPHGM and Problem Formalization
Although prior work for protecting the DSLP against a global adversary was mainly based on the PHGM described in section one, only the SS method in [9, 10] considered reporter sources to generate real event reports depending on event-trigger-signals. It is more realistic than the assumption that nodes of the protected network can sense the monitored objects while the adversary cannot. In practice, directly recognizing an object is a very challenging work due to the difficulty of distinguishing the physical features of the objects from background noises [10]. In this section, we will present an updated-panda-hunter game model (UPHGM). We also assume that every monitored object is equipped with a sensor node to emit signals which can be detected by nodes in the network as [9, 10]. The UPHGM includes a network model and an attack model.
4.1. Network Model
We assume that a homogeneous WSN, called obj-WSN, is deployed by an organization to monitor specific objects such as giant pandas, as shown in Figure 2. The obj-WSN consists of N common nodes and one sink node. All of the common nodes have roughly the same resources. Each common node u has a unique node identifier (
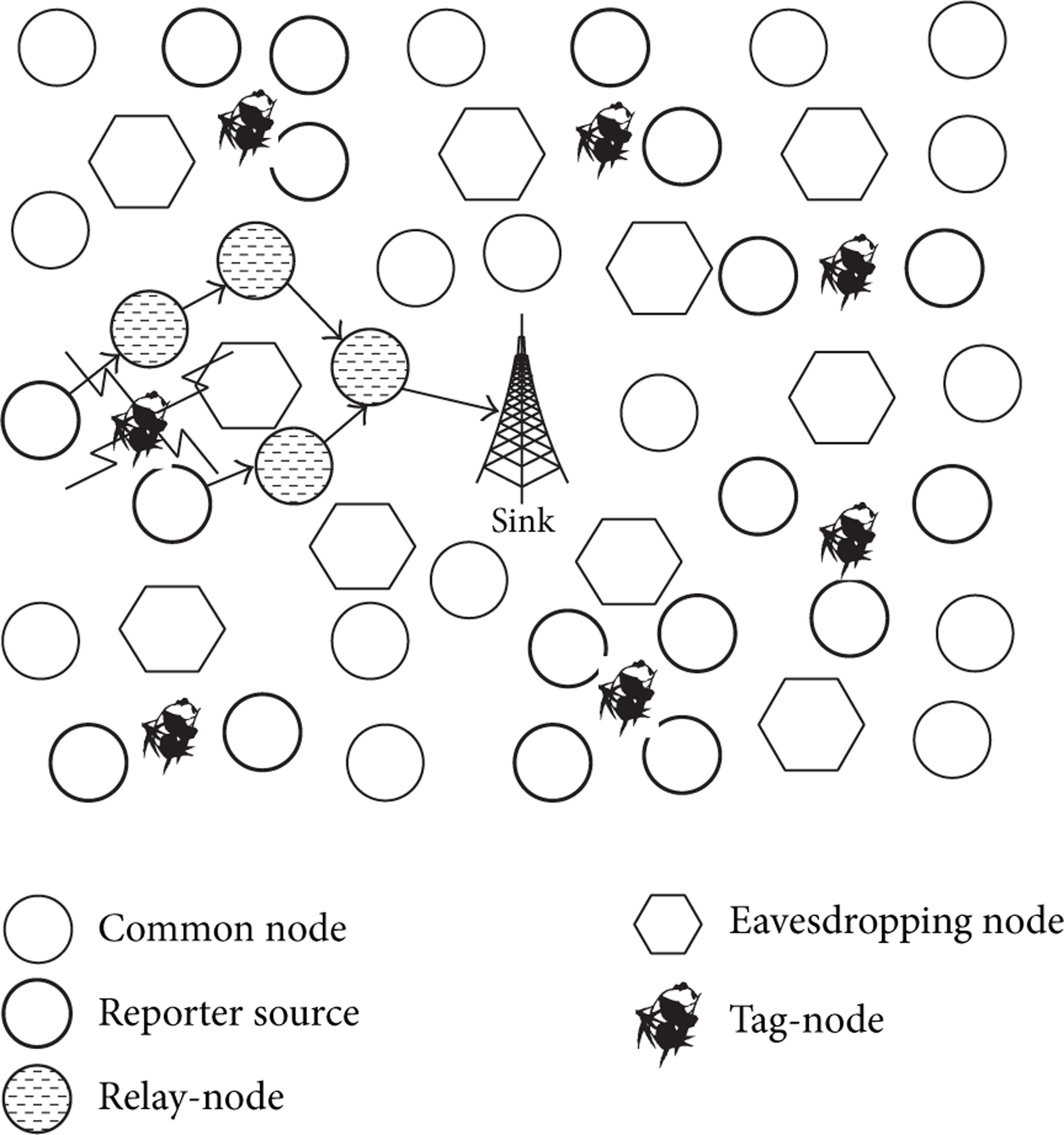
The considered network architecture.
4.2. Attack Model
We assume that the adversary has his/her own sensor network deployed in the same area, as shown in Figure 2, to monitor the global network traffic of the obj-WSN as [9, 10]. Note that the deployment time of the adversary's network is later than that of the obj-WSN. More specifically, we assume that when the infrastructure of secure communications of the obj-WSN has been established, then the adversary's network can be deployed. The adversary can monitor the whole network traffic including the Object-msgs emitted by tag-nodes. Knowing a global view of the network traffic, the adversary can easily deduce where the objects are moving around. For example, an object is very likely close to tag-nodes and reporter sources. We do not consider the situations that the monitored objects can be directly recognized by sensors. If that happens, then the adversary can launch the direct sensing attack and any defense mechanism cannot protect the location privacy of the monitored objects.
In addition, the adversary has the following characteristics.
To appropriately study privacy, we apply Kerckhoff's principle [30]. We assume that the adversary knows the communication protocols and defense mechanisms of the obj-WSN. Each eavesdropping node knows its own location, as shown in Figure 2. To be invisible from obj-WSN, the adversary considered in this paper may launch only passive attacks and avoid active attacks as [9, 10]. However, since the network may also be attacked by other adversaries with the different attack aims, we also need to prevent them from launching some active attacks such as injecting bogus data by utilizing the security weaknesses of the defense mechanisms.
4.3. Distinguish with the PHGM
The main difference between UPHGM and PHGM is that the former considers the Object-msg containing the TID of the tag-node and other interest-info, which is more suitable for many practical applications. For example, for multiobjects monitoring applications, if Object-msg contains no information of a monitored object and is only used to trigger event detection, a reporter source cannot generate an accurate event report for the corresponding object, because it does not know which tag-node emits the received Object-msg. And for many applications, we may want to know the state information or health characteristic information about monitored objects. Therefore, the UPHGM is more realistic and effective than the PHGM for many applications to monitor multiobjects.
Compared with the PHGM, the UPHGM yields a new problem which needs to be solved. That is, how to forward Object-msgs to the sink node securely while providing location privacy to tag-nodes and reporter sources under a global adversary. Prior work only considered the location privacy of reporter sources and ignored the location privacy of tag-nodes. Although reporter sources can use the established pairwise keys to communicate with common nodes securely, due to tag-nodes being of moving characteristic and their resource constraints, the tag-nodes cannot firstly establish pairwise keys with all common nodes in the network and then use the corresponding keys to communicate with the corresponding nodes securely. Therefore, secure and effective protocols have to be designed to implement the secure communications between tag-nodes and reporter sources while providing their location privacy.
4.4. Formal Model
The problem Ω for protecting the source location privacy against a global adversary in WSNs can be represented by an eight-tuple (O, O is the set of monitored objects. We assume that the size of O is M. Every monitored object can move around in the deployment area. D is the set of defense strategies to protect the source location privacy. A is the set of attack strategies to infer the locations of monitored objects. b is the level of privacy in terms of bits. It is defined as [9, 10]
Given the level of privacy b, our goal is to achieve it with minimum defense overhead
5. Grid-Based Pull (GBP) Scheme under the UPHGM
As we have pointed out in Section 4, the UPHGM is more realistic than the PHGM and is suitable to monitor multiobjects accurately. However, there are still more challenges. In this section, we will propose a grid-based pull scheme to protect the DSLP under the UPHGM by combining a light-weight security object collection scheme with an effective grid partition method. It includes selecting communication scheme and determining grid size. And its implementation is then presented.
5.1. Selecting Communication Scheme
The first main challenge is to effectively authenticate and communicate between a mobile tag-node and each potential communication node in the network. There are two kinds of communication schemes: push scheme and pull scheme. For push scheme, each tag-node broadcasts Object-msg periodically. As the tag-nodes are mobile, every node in the network has to be able to authenticate each tag-node. For pull scheme, the query nodes broadcast query messages periodically. In this case, each tag-node must be able to authenticate every node in the network.
Compared with the push scheme, the pull scheme is more secure to solve our problem. For the push scheme, if any node is compromised by the adversary, he or she can obtain the secret information such as secure keys stored in a compromised node and then upload the obtained secrete information to every eavesdropping node. As a result, when any tag-node broadcasts an Object-msg, eavesdropping nodes can authenticate the message and recognize the monitored object. For pull scheme, if any node is compromised by the adversary, to launch the stealthy attacks, he or she shall not broadcast query message using the obtained secure information. If he or she does so, then it is very probably to expose the eavesdropping nodes to the obj-WSN and to trigger alarms. Only in this situation, when a monitored object lies in the communication range of the compromised node and the compromised node is just the query node, the location of the monitored object is exposed to the adversary without triggering alarms. Therefore, as shown in Table 1, considering security, we should select the pull scheme.
Comparison of communication schemes.

However, due to resource constrains, for example, the storage resource, in order to let a tag-node be able to authenticate every node in the network, obviously, we cannot select symmetric approaches, which require the tag-node store a large number of pairwise keys. Hence, for storage efficiency, we should adopt an asymmetric authentication approach. Considering the asymmetric feature between tag-nodes and common nodes in the obj-WSN, we design an authentication approach based on the identity-based cryptography (IBC), which will be described in Section 5.3.
5.2. Determining Grid Size
The second problem we consider is how to reduce the number of query nodes as largely as possible while keeping the high quality tracing of the monitored objects. To reduce the number of query nodes, we divide the whole network area into a number of virtual grids. And in each grid a node, called duty node, is selected to collect information of the monitored objects. To balance energy load among nodes, each node can be responsible for collecting the information for a certain time interval in turn as duty node. Hence, the second problem can be translated into the problem that how to determine the size of the virtual grid to satisfy both query requirement and connectivity requirement. The query requirement means that no matter where a tag-node is in the network, its relevant information can be detected by at least one query node. The connectivity requirement means that nodes in a grid are capable of communicating with those nodes in an adjacent grid.
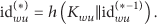
On the one hand, to meet the query requirement, there should be at least one full grid in the circle with the tag-node as the center and with the communication radius r of the tag-node as the radius, just as illustrated in Figure 3. Obviously, the smaller the size of the gird is, the more full grids are in the circle. To reduce the number of query nodes as largely as possible, we need to determine the maximum size of the grid. We have derived the theoretical maximum size of the grid and have the following theorem.

Example of query requirement in the communication range of the tag-node containing at least a full grid.
Theorem 1.
To ensure that no matter where a tag-node is in the network, there is at least one full grid in the circle
Proof.
Firstly, we prove that there is at least one full grid in the circle
Secondly, we prove that the a is the maximum length. We assume that the length

Example of one tag-node at the common vertex of four grids.
On the other hand, according to [31], to satisfy the connectivity requirement, the length a of the grid should satisfy

Example of connectivity requirement according to [31].
As the communication radius of the common node is usually not less than that of the tag-node, we assume that 
That is, m and n are the number of grids according to the above two dividing methods, respectively. Then, we have the following conclusions.
If If If
5.3. Implementation of the Grid-Based Pull Scheme
In this subsection, we introduce the implementation of the grid-based pull scheme, including predeployment phase, grid formation phase, and report collection phase.
5.3.1. Predeployment Phase
Before deploying the obj-WSN, we assume that a trusted authority (TA) does the following operations.
Generate system parameters (p, q, Choose two hash functions: Select a random element Calculate the Randomly select L common nodes as token nodes and preload each of them with a unique token ID.
Each common node u is preloaded with the pubic system parameters (p, q,
5.3.2. Grid Formation Phase
After deploying the obj-WSN, we assume that every common node can obtain its own location information using some localization methods such as [33, 34]. Also we assume that every common node can obtain the location information (
To form virtual grids, in network initialization phase, each common node i broadcasts a hello message (hello-msg), as follows:

Upon receiving the hello-msg from node i, the node u first calculates the grid identifier
To avoid additional communication overhead caused by the duty node role rotation, we can stipulate the rotation order, for example, in descending (or increasing) order of ID number, in each grid. Thus, each grid will have a duty node when the network initialization finishes and also each node will rotate as duty node in a stipulated order.
5.3.3. Report Collection Phase
We assume that in network initialization phase an effective key-based mechanism is adopted, such as [35–37]. That is, an infrastructure for secure communication has been established. To achieve anonymity, nodes may need to use pseudonyms to communicate with each other according to the requirement. We adopt the method in [29] to generate pseudonyms. Assuming two nodes u and v with a shared key 

(1) Broadcast Query Message. After network initialization, every duty node u periodically broadcasts query message (query-msg), as follows:
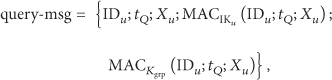
( 2) Reply Query Message
(i) For Tag-Node. We assume that tag-nodes and common nodes are loosely synchronized. Every tag-node periodically monitors the query-msg for a specific time interval Calculate the Check the first MAC in (9): calculate Send a reply message (reply-msg). The tag-node v selects a node in its candidate reply-list to reply. We assume that query node u is the candidate node; then tag-node v sends a reply-msg to node u, as follows:
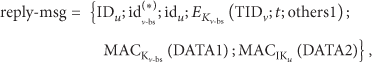




(ii) For Token Node. In the same manner as tag-nodes, when a token node w receives a query-msg from a duty node u, which, we assume, is the candidate node to reply, it sends a reply-msg to node u. Note that token nodes do not perform the operations (I) and (II) as tag-node does do. A token node just checks the second MAC in (9) with the corresponding shared group key. Token node w sends the following reply-msg to node u:



As the reply-msg sent from token node w contains the pseudonym shared between w and nextTkNode, hence, nextTkNode also receives the reply-msg. When receiving this message, it first checks the corresponding MAC using the pairwise key shared between w and itself. If the corresponding MAC is verified, it updates the pseudonym shared between w and itself using (8), decrypts the corresponding encrypted field, obtains the token-ID, and sets itself as the next round's token node.
(3) Generate and Forward Event Report Message. Due to the different schemes used by tag-nodes and token nodes to generate pseudonyms, as shown in (11) and (8), a query node which receives a reply-msg can know whether the message is sent from a tag-node or a token node. Therefore, the query node can check the MAC using the corresponding key. Upon receiving a reply-msg from a tag-node v or a token node w, a query node u first checks the corresponding MAC. If the corresponding MAC is verified, it generates an event report (rpt-msg) and forwards the rpt-msg to the duty node closest to the sink node in its communication range.
Query node u forwards the following real rpt-msg to the chosen next hop node (nextHop) if it receives a verified reply-msg from tag-node v:

If query node u receives a verified reply-msg from token node w, it forwards the following fake rpt-msg to the chosen next hop node (nextHop):


When a relay-node receives a rpt-msg, it checks the MAC. If the MAC is verified, the relay-node regenerates a MAC using the pairwise key shared with the next hop node. Then it forwards the rpt-msg to the next hop node as quickly as possible whenever the channel is free. In this way, the rpt-msg will evenly reach the sink node.
When the sink node receives a verified rpt-msg generated from a reporter source u, it first obtains the collectInfo field via decrypting the encrypted part using the key shared between u and itself with the help of the
5.3.4. Security Analysis
The GBP scheme provides the following security services.
(1) Confidentiality Service. The confidentiality service provided by the GBP scheme is shown in two aspects. On the one hand, the GBP scheme achieves the confidentiality of identifications of the tag-nodes and the token nodes at the reply query message phase via the pseudonym technique, as shown in (10) and (15). In other words, when receiving a reply-msg, the adversary cannot know whether the message is sent by a tag-node or a token node from the pseudonym fields, that is, from 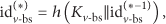

However, using the pseudonym technique we have to solve the influence of pseudonym collision; that is, more than one node has the same pseudonym, because the hash function may generate same outputs from different inputs. The birthday paradox implies that the pseudonym collision probability is
On the other hand, the GBP scheme guarantees confidentiality of the contents of messages via encrypting their contents using secret pairwise keys
(2) Authentication Service. The authentication service of the GBP scheme is provided via checking MACs and pseudonyms. For example, in (9), tag-nodes and token nodes can authenticate duty nodes via using corresponding keys such as 

(3) Integrity Service. The integrity service of the GBP scheme is provided via checking MACs similar to the analysis for the authentication service, such as in (9), (10), and (15).
(4) Freshness Service. The freshness service of the GBP scheme can be provided via the timestamp in (9), (18), and (20). For example, if a tag-node receives a query-msg, it can compare the timestamp field 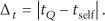
(5) Privacy Service. As both the adversary and the defender have similar knowledge about the behavior of real objects, we assume that any candidate trace created by the token nodes in the network will be considered as a valid candidate trace by the adversary as [9, 10]. On the one hand, as the confidentiality service is provided by the GBP scheme, hence, the adversary cannot distinguish between tag-nodes and token nodes based on the contents of messages in the network. On the other hand, as the communication schemes of tag-nodes and token nodes are the same and indistinguishable for the adversary, hence, the adversary cannot distinguish between tag-nodes and token nodes based on the communication schemes. That is, the adversary cannot use the content information and the contextual information to distinguish tag-nodes from token nodes. In other words, L token nodes create L valid candidate traces. Therefore, we can see that the set of candidate locations includes an average of 
Let us have a look at the following example where we have one monitored object,
6. Evaluations
In this section, we first give the communication and computation overhead of both our schemes and the SS scheme in [9, 10]. Then, we present performance results of them in terms of communication overhead.
6.1. Numerical Discussion
In this subsection, we provide mathematical analysis to get the numerical results of both our methods and the SS scheme in [9, 10], in terms of communication overhead and computation overhead.
6.1.1. Packet Format and Length
In order to analyze the communication cost accurately, in this section, we provide the packet format and length for each type of messages. According to IEEE 802.15.4 frame format [39], each packet includes 9 bytes constant information, which consists of the 4-byte preamble sequence, the 1-byte start of frame delimiter, the 1-byte frame length, the 2-byte frame control field, and the 1-byte data sequence number. That is to say, each type of messages in both our schemes and SS includes the 9 bytes constant information.
In GBP, a query-msg carries a 2-byte source address, which is denoted by the identification of the broadcasting node, a 4-byte timestamp, a 64-byte X coordinate of the broadcasting node on the elliptic curve
In GBP, a reply-msg consists of the 9-byte constant information, two 8-byte pseudonym fields, an encrypted field, and two 4-byte MACs fields. We assume that the encrypted function is implemented using the AES-128 with a 16-byte output. Then, the byte length of the reply-msg
In GBP, a rpt-msg carries three 2-byte ID fields, a 4-byte timestamp, an encrypted field, and a 4-byte MAC field in addition to the 9-byte constant information. As shown in (12) and (14), since the byte length of the encrypted information collectInfo is 28, including an 8-byte pseudonym, a 16-byte encrypted field, and a 4-byte MAC, the byte length of the encrypted field of the rpt-msg is 32 using the AES-128 with two 16-byte outputs. Therefore, the byte length of the rpt-msg
In both ISS and SS, we assume that an event-trigger-signal carries a 4-byte timestamp and a 4-byte MAC in addition to the 9-byte constant information. Thus, the byte length of the event-trigger-signal
In ISS, a token-pass-msg consists of the 9-byte constant information, a 2-byte ID field, a 4-byte timestamp, two encrypted fields, and two 4-byte MACs fields. Similar to the encrypted field of the reply-msg in GBP, the byte length of the encrypted field of the token-pass-msg in ISS is 16. Therefore, the byte length of the token-pass-msg
In SS, a token-pass-msg carries a 2-byte ID field, a 4-byte timestamp, a 16-byte encrypted field, and a 4-byte MACs field in addition to the 9-byte constant information. Thus, the byte length of the token-pass-msg
In both ISS and SS, similar to in GBP, a rpt-msg consists of the 9-byte constant information, three 2-byte ID fields, a 4-byte timestamp, a 16-byte encrypted field, and a 4-byte MAC field. Therefore, the byte length of the rpt-msg
6.1.2. Communication Overhead
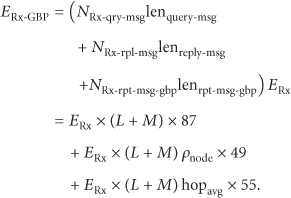
In GBP, the communication overhead includes broadcasting and receiving query-msg overhead, replying and receiving query-msg overhead, and sending and receiving event report message (rpt-msg) overhead. (1) In the broadcasting query-msg phase, duty-nodes broadcast query-msgs, and tag-nodes and token nodes listen on the chosen channel. Note that in order to reduce the interinfluence caused by broadcasting query-msg and replying query-msg, we can transmit them on two different channels. Therefore, the number of query-msg broadcast, 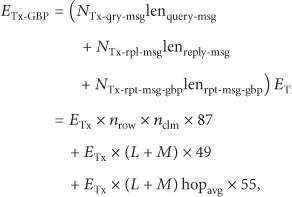
Total number of messages transmitted and received of each type in the GBP scheme.

In ISS, communication overhead includes broadcasting and receiving event-trigger-signal overhead, transmitting and receiving token-pass-msg overhead, and sending and receiving event report message (rpt-msg) overhead. (1) In the transmitting event-trigger-signal phase, tag-nodes and token nodes send event-trigger-signals and their neighbor nodes receive event-trigger-signals, which is similar to the replying query-msg phase in GBP. Thus, the number of event-trigger-signals transmitted, 

Total number of messages transmitted and received of each type in the ISS scheme.

In SS, communication overhead includes broadcasting and receiving event-trigger-signal overhead, sending and receiving event report message (rpt-msg) overhead, and transmitting and receiving token-pass-msg overhead. In both transmitting event-trigger-signal phase and sending token-pass-msg phase, it is similar to the corresponding phases in the ISS scheme. In the sending rpt-msgs phase, since every node which receives the event-trigger-signal generates a rpt-msg and delivers it toward the sink node, the number of token-pass-msgs transmitted 

Total number of messages transmitted and received of each type in the SS scheme.

According to (29), (31), and (33), we can derive
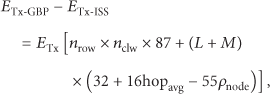


Since WSNs are usually densely deployed,
Similarly, according to (30), (32), and (34), we can derive
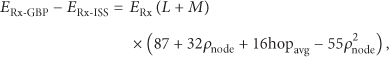

In (38), if
In (39), if

In (40), if

6.1.3. Computation Overhead
Compared with the SS scheme and the ISS scheme, the most time-consuming task for computation in the GBP scheme is the scalar point multiplication operation. Similar to [9, 10, 41, 42], we ignore conventional hash operations and symmetric-key encryption/decryption operations as they consume much less energy than scalar point multiplications and transmitting/receiving operations. According to [43, 44], the energy consumption of the ECC-160 scalar point multiplication on TelosB sensor nodes with the 16-bit MSP430 microcontroller running at 4 MHz is approximately 17 mJ. As reported in [44], a CC2420 transceiver with a claimed data rate of 250 kbps used in TelosB nodes consumes 5.76 and 6.48 μJ to transmit and receive one byte, respectively. As mentioned above, the byte length of a query-msg and a reply-msg in GBP are 87 and 49 bytes, respectively. Thus, the energy cost for receiving a query-msg and replying a reply-msg by a tag-node is approximately 0.846 mJ. Let
6.2. Simulation Results
In this section, we present the simulation results of our methods and the SS method in terms of communication overhead. For the convenience of comparison, we assume that the event-trigger-signals emitted by token nodes and tag-nodes are distinguishable for reporter sources in SS.
6.2.1. Simulation Setup
The simulation is based on the Castalia simulator [46]. In the simulation, 6000 sensor nodes are randomly generated and distributed in a 1000 m × 1000 m area. The sink node is located at the center of the field. During the simulation, we assume that there is only one monitored object in the network as [9, 10]; that is, there is only one tag-node in the network. Multiple fake monitored objects, that is, token nodes, are randomly chosen from the sensor nodes and simulated in the field. For each node, including the tag-node, the transmission range is 50 m. Thus, on average, each node has 47 neighbors. As [9, 10], we focus our simulation evaluation on how much communication cost we have to pay to achieve a given level of location privacy. For each experiment, there is only one event generated by each tag-node or by each token node. We repeated the experiment 20 times with different network topologies and all the results were obtained by computing the average of all corresponding results.
6.2.2. Simulation Results
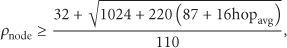
Figures 6 and 7 show the communication costs for transmitting and receiving messages of the network at different privacy levels, respectively. Figure 8 shows the total communication costs in the network at different privacy levels.

Communication cost for transmitting messages of the network at different privacy levels.

Communication cost for receiving messages of the network at different privacy levels.
Total communication cost of the network at different privacy levels.
Figure 6 shows that, (1) with the privacy level increasing, the energy consumed to transmit messages in GBP is less than that in both ISS and SS; (2) the energy consumed to transmit messages in ISS is less than that in SS, which are in accord with the analysis in Section 6.1.2. Figure 7 shows that (1) the energy consumed to receive messages in GBP is less than that in both ISS and SS. (2) the energy consumed to receive messages in SS is less than that in ISS. The reason is that
From Figure 6 to Figure 8, we also see that in the three schemes the communication overhead increases with the privacy requirement. However, the communication overhead of GBP demonstrates a relatively slower increase compared to the SS scheme and the ISS scheme. Note that when we also consider the computation overhead, as mentioned earlier, we only need to add the additional computation overhead of GBP to our results (i.e., 17 mJ, the scalar point multiplication operation of the tag-nodes). However, from Figure 6 to Figure 8, we can see that it would not have much influence on the results.
In summary, both the ISS method and the GBP method are good choices to provide the data source location privacy service. Moreover, the GBP scheme is the better choice with lower energy cost.
7. Conclusions
Prior work on protecting the DSLP against a global eavesdropper was based on the panda-hunter game model (PHGM) and rarely considered the communication between data sources and reporter sources, which restricts their applications and even causes their methods to fail. Only the SS method considered the event trigger process from monitored objects. However, the SS method still has two limitations. First, the reporter source cannot generate effective event reports as the event-trigger-signals emitted by token nodes and tag-nodes are indistinguishable, which was ignored in SS. Second, it is unsuitable to track multiobjects accurately. In order to solve the first problem of SS, an improved source simulation (ISS) method was proposed by adjusting the event report strategy under the PHGM. To overcome the disadvantage of the PHGM, we proposed an updated-panda-hunter game model (UPHGM) and gave the formal model of the DSLP issues. And an energy-efficient grid-based pull (GBP) scheme was presented to protect the DSLP under the UPHGM as well as to provide security services including confidentiality, authentication, integrity, and freshness.
The ISS scheme uses the token pass message to distinguish different events and only one node will generate event report message for each event-trigger-signal; hence, its communication overhead for transmitting messages is lower than that of SS, which causes the neighbor nodes of each event-trigger-signal to generate event reports. Although the total communication cost of ISS is higher than that of SS, the communication cost of ISS is comparable to that of SS under low privacy requirement and it allows a reporter source to generate effective event reports while the SS scheme cannot. The GBP scheme adopts the pull scheme, IBC-based technique, and pseudonym technique to provide the authentication service and to reduce storage overhead of key material. In order to reduce the communication overhead of GBP, we presented the optimal grid size to meet connectivity requirement and query requirement. Both the theoretical analysis and the simulation results show that GBP outperforms both ISS and SS in terms of energy cost on the whole.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work was supported by National Natural Science Foundation of China under Grant no. 60873199. The authors are grateful to the anonymous reviewers for their insightful comments.