Abstract
This paper introduces a hybrid and secure MAC protocol (PMAC) for WBAN. The PMAC protocol uses two contention access periods (CAPs) for accommodating normal and life-critical traffic and one contention-free period (CFP) for accommodating large amount of data packets. The priority-guaranteed CSMA/CA procedure is used in the CAP period, where different priorities are assigned to WBAN nodes by adjusting the backoff window size. In addition, a set of security keys is used to prevent illegal access to the network. Analytical expressions are derived to analyze the average delay, power consumption, throughput, and packet loss probability of the PMAC protocol. Results derived from these expressions are validated by computer simulations.
1. Introduction
Wireless body area networks (WBANs) are captivating significant attention from research and industrial communities. They provide unprecedented and limitless opportunities for medical and nonmedical applications [1, 2]. Medical applications employ implantable or wearable tiny devices in, on, or around the human body for continuous health monitoring such as predicting contingency abnormal condition and treatment of chronic diseases including diabetes and hypertension. Non-medical applications include interactive body computing, information exchange, social networking, monitoring forgotten things, entertainment, monitoring of athletes, education, or assessing soldier fatigue and battle readiness. Most of these applications require WBAN to stay operational for a longer period of time which necessitates power-efficient network operation. For example, a diabetic patient requires round-the-clock real-time glucose monitoring over a period of years to decades in order to avoid catastrophic consequences such as stroke or a heart attack that may result in death. This requires WBAN node to continuously monitor and report glucose level for timely action. Nodes of WBAN primarily rely on low power batteries that hinder their operation over longer period of time. Therefore, power-efficient network operation is extremely crucial for prolonging network lifetime.
Medium access control (MAC) protocols play a critical role in extending network lifetime by controlling the dominant sources of energy waste such as packet collisions, overhearing, idle listening, and control packet overhead. Most of the existing MAC protocols for WBAN are categorized into contention- and schedule-based MAC protocols. In contention-based MAC protocols, nodes compete for the channel to transmit the data; carrier sensor multiple access with collision avoidance (CSMA/CA) protocol is the best example of contention-based MAC protocols where the nodes contend for the channel using a random backoff period. These protocols are scalable and do not require establishing infrastructure. However, they are unable to handle emergency situations where multiple nodes (with the same priorities) are triggered to send life-critical data. Schedule-based MAC protocols divide the channel into multiple fixed or dynamic slots, which are used for data transmission. These protocols reduce idle listening and overhearing; however, they incur significant protocol overhead.
This paper proposes a hybrid and secure MAC protocol (PMAC) for WBAN. The PMAC protocol supports two contention access periods (CAPs) and one contention free period (CFP). In the CAPs, the operation is mainly based on a priority-guaranteed CSMA/CA procedure, where different WBAN nodes are assigned different priorities. These priorities are adjusted by tuning the contention window (CW) size. Depending on the application requirements, the CAPs may also employ the slotted-ALOHA protocol. The CFP is used to carry large amount of data packets to the coordinator. The PMAC protocol uses a set of security keys including master key (MK) and pairwise temporal key (PTK) in order to prevent adversaries from gaining resource allocation information and from corrupting the CFP slots. The performance of the PMAC protocol is analyzed using both analytical and simulation-based methods. The results are derived in terms of average delay, power consumption, throughput, packet loss probability, and number of corrupted CFP slots.
The rest of the paper is organized into the following sections. Section 2 presents the related work. Section 3 explains the basic operation of the PMAC protocol. Sections 4 and 5 present the analytical approximations and performance results. The final section concludes our work.
2. Related Work
Multiple research efforts are dedicated to the development of novel MAC protocols for WBANs. Some of these efforts analyzed existing technologies such as IEEE 802.15.4 [3], while others have proposed new techniques for power-efficient communication in WBANs. The authors of [4] investigated the suitability of IEEE 802.15.4 MAC protocol for WBANs; however, their analysis was confined to periodic and asymmetric traffic. In [5], the authors proposed a random access protocol that supports quality of service for multiuser mobile WBANs. This protocol addressed inter-WBAN interference and energy wastage problems caused by network mobility and provided support for latency and energy control. The authors of [6] proposed a reliable power-saving mechanism that strives to reduce collisions and idle listening. They also proposed a distributed queuing MAC protocol and evaluated its performance for different network loads [7, 8]. The performance of IEEE 802.15.6-based CSMA/CA procedure was investigated in [9] where the minimum delay and maximum throughput for different narrow band frequency bands were derived. The authors of [10, 11] developed an analytical model to evaluate the performance of contention-based WBANs. They developed a Markov chain to model backoff procedure of IEEE 802.15.6 under saturated and nonsaturated conditions. Their study also investigated the effectiveness of exclusive and random access phases. A similar study was conducted in [12] where the authors investigated the impact of different periods on the IEEE 802.15.6 superframe structure. They considered saturated and error prone channel and developed a Markov chain for analyzing different traffic loads on the IEEE 802.15.6 networks. In [13], the authors studied the integration of radio frequency identification (RFID) technology with WBANs and concluded that RFID-based wakeup methods can play a significant role in extending the network lifetime to years. A superframe-level time hopping scheme for WBAN with variable contention access period was presented in [14]. While maintaining the similar interference mitigation, the proposed scheme improved performance of WBAN in terms of energy dissipation, latency, and spectrum efficiency. The authors of [15] recently proposed an adaptive time division multiple access (TDMA) protocol based on periodic wake up schedules, which efficiently handles overhearing and idle listening problems in WBANs. Another study presented in [16] proposed a traffic-aware dynamic MAC protocol that dynamically adjusts wakeup intervals based on traffic status register bank. The dynamic wakeup intervals save extra power consumed by idle listening, overhearing, collisions, and unnecessary beacon transmission. A priority-based TDMA protocol is presented in [17], where the transmission schedules are based on priorities of data packets. This protocol dynamically adjusts the superframe structure according to the traffic load, thereby minimizing power consumption of the network.
3. PMAC Protocol
The following sections discuss the general description, priority-guaranteed resource allocation, and security support of PMAC protocol.
3.1. General Description
The PMAC protocol operates in a beacon-enabled mode, where beacons are transmitted at the end of each superframe. The superframe consists of a beacon, two contention access periods (CAP1 and CAP2), and one contention-free period (CFP) as given in Figure 1. The beacon is used for resource allocation information. It also carries security codes in order to allocate resources to legitimate users. The CAP1 considers a priority-guaranteed CSMA/CA procedure for data transmission. The operation of the priority-guaranteed CSMA/CA is partially based on IEEE 802.15.6 standard [18]. The CAP1 has an optional period for slotted-ALOHA protocol (this is not considered in our analysis). Depending on the application requirements, the slotted-ALOHA protocol may be used to send short data and command frames. For example, for low-traffic situations, the slotted-ALOHA may be used to allocate resources to nodes in the CFP period. The CFP period consists of multiple TDMA slots and is used for a large amount of data packets including streaming data. The CAP2 is an optional period which is used to finish the pending transmission of CAP1. This period is also used to inform the coordinator of incomplete transmission in the previous CFP slots. In addition, the PMAC considers a one-hop star topology network with uplink traffic only. The entire operation of the network is controlled by the WBAN coordinator.

PMAC superframe structure.
3.2. Priority-Guaranteed Resource Allocation
For resource allocation, the coordinator continuously broadcasts beacons to all nodes, and only active nodes are able to receive the beacons. The PMAC protocol allows low duty cycle nodes to remain in sleep mode in order to save their energy (consumed by beacon overhearing). The nodes which have no data to send or receive do not need to wakeup and receive the beacons. The nodes requiring the allocation of TDMA slots send a request to the coordinator in the CAP period. Upon receiving the request, the coordinator allocates TDMA slots in the CFP period of the following superframe. Figure 2 shows the beacon format of PMAC protocol. The details of each field are present in [18].

PMAC beacon frame format.
In the CAP period, the PMAC protocol employs the priority-guaranteed CSMA/CA procedure. The procedure of this protocol is based on IEEE 802.15.6 standard [18] where the node sets the backoff counter to a random integer that is uniformly distributed over
CW bounds for priority-guaranteed CSMA/CA [18].

Nodes having high priorities will have a small

A priority-guaranteed CSMA/CA procedure.
3.3. Security Support
Since WBANs are mostly used for health applications, attacks on these networks may create serious circumstances for their users. Each WBAN must be able to support strong security protocols in order to enable secure communication on the channel. In addition, these protocols must also be able to address other security issues such as data confidentially, data authentication, data freshness, data availability, and secure management. The security mechanism of the PMAC protocol is based on IEEE 802.15.6 standard [18]. The protocol supports three security levels: (1) unsecured communication level, where the data is transmitted in unsecured frames, (2) authentication level, where the data is transmitted in secured authentication with no encryption, and (3) authentication and encryption, where the data is transmitted in authenticated and encrypted frames. The PMAC protocol uses a master key (MK) for establishing a secure communication. The MK is preshared between the nodes and the coordinator. Once the pre-shared MK is activated during association, the nodes generate a pairwise temporal key (PTK) for a single session upon mutual agreement. The frames are then authenticated and encrypted using the AES-128 counter. The secure MK and PTK keys prevent adversaries from penetrating into the network and from manipulating different active and passive attacks including backoff manipulation and replay attacks.
4. Analytical Approximations of PMAC
Let 
The probability σ is that the channel is busy or there is an ongoing transmission during a slot time is given by

The transmission probability 
The probability that the data is successfully transmitted after jth retry is 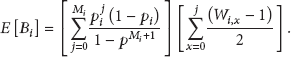
The probability
4.1. Average Delay
The average delay 
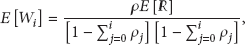
4.2. Average Power Consumption
The average power consumption 
4.3. Throughput
The saturated throughput 

For PMAC, the expressions for 
5. Performance Results
The basic operation of the PMAC protocol is simulated in an independent C++ simulator. The nodes generate uplink Poisson traffic in a star topology network. Initially, we consider two priority classes (class 0 and class 1) for performance analysis; however, the analysis is valid for all types of priority classes. The
Simulation parameters (the symbol rate is calculated based on [18]).

(i) Average Delay. This is the average delay of a packet in the queuing, backoff, and transmit states for a priority class i.
(ii) Average Power Consumption. This is the average power consumed in the backoff, transmit, and receive states for a priority class i.
(iii) Throughput. This is the saturation throughput of WBAN.
(iv) Packet Loss Probability. The packet loss probability
(v) Number of Corrupted CFP Slots. This is the total number of CFP slots that are corrupted by an attacker. The attacker first listens to the beacon in the beginning of the superframe period and grabs knowledge about the slot boundaries of CFP period. Once the CFP slots are known, the attacker creates interference in these slots.
Figure 4 shows the average delay as a function of number of nodes in priority class 0 and class 1. Because class 0 has longer waiting and queuing delays, its average delay is comparatively more than that of class 1. In addition, when the number of nodes increases, the average delay increases; this is because of increase in packet loss and collision probabilities. In addition, the average power consumption for class 0 is more than that of class 1 for a few number of nodes as illustrated in Figure 5. However, when the number of nodes in a high priority class is increased (for a fixed

Average delay of PMAC for priority class 0 and class 1.

Average power consumption of PMAC for priority class 0 and class 1.

Saturation throughput of PMAC for priority class 0, class 1, and class 2.

Packet loss probability

Number of corrupted CFP slots.
6. Conclusion
This paper introduced a hybrid and secure MAC protocol which prioritizes the nodes by using a priority-guaranteed CSMA/CA procedure in the CAP period. The priorities are adjusted according to the
Footnotes
Conflict of Interests
The authors declare that they have no conflict of interests.
Acknowledgment
This work was supported by the Research Center of College of Computer and Information Sciences, King Saud University, Riyadh, Saudi Arabia, through the Research Project no. RC121244.
