Abstract
Various errors and failures occur every day in the plant field. However these errors have been managed manually by field inspector. In this paper, we present a design and implementation of a field inspection management system based on wireless sensor networks. This system works on a portable embedded device. To develop the field inspection management system, we analyzed work tasks and process in the plant field. In addition, we propose security measures for preventing information stealing and alteration in the embedded system. Through this system, we can manage effectively error information collected in the field.
1. Introduction
Recently the prevalence of portable devices such as smartphone or tablet PC has increased rapidly. These portable devices are called embedded systems and designed to serve specific tasks. Almost all embedded systems come with compact size, so users are able to use them as additional parts of other devices or construct specific applications with them [1–5]. However, due to increasing the processing speed of microprocessors and the amount of flash memory or SDRAM, embedded systems can accomplish more complex program. Also due to the advent of database management systems for embedded system, embedded system is able to install database management system and play the role of secondary server [6–8]. Meanwhile, the new and rapid development of ubiquitous technology is expected not to be confined in specific area but to spread to every part of human life and initiate changes. In ubiquitous environment, various sensors are spread out around us and these sensors collect environmental information such as temperature, humidity, and illumination. Also, a person's current location can be estimated using ZigBee wireless communication [9–11].
In the plant field, various errors and failures occur every day. These are described manually and record process has several problems. So, this paper analyzes work tasks and process in the plant field and develops a field inspection management system based on sensor network.
2. Background
In this section, we briefly describe some of the background and related work necessary for the rest of the paper.
2.1. The Analysis of Work Environment and Process
To develop the field inspection management system, we analyzed work tasks and processes in the plant field. Various errors and failures occur every day in the plant field. In general, these errors and failures can be verified through field inspection and are recorded in the handbook. After the field inspection, come back to the office and access to the information system through login. And then enter information such as the errors, edit a report using word processor, and finally print a report. Figure 1 shows the flow of actual work in the field. Figure 2 shows a flowchart through the analysis of the fieldwork.

Work process.

The flowchart of field work.
2.2. Problems of Current Work Process
Problems that can occur in this process are as follows.
First, the status information of a particular location cannot be verified in real time. This status information includes temperature, humidity, and environmental information of device or location. Second, the error in the field cannot be entered immediately. Third, after returning to the office, the content information recorded in handbook must be entered in the system again.
In this paper, in order to improve these problems, we focus on the following points and develop the system.
First, the status information of a particular location is identified in real time.
Second, the portable device is used to enter the error immediately at the field.
Third, the information entered at the field is passed directly to the system.
To do this, we use portable embedded device and develop a field inspection management system, which can collect status information using wireless sensor networks technology and manage error information.
3. Management System
There are many types of equipment in the power plant, the equipment is in operation 24 hours, and a large or small problem is occurring. These problems are discovered through field inspection and by solving these problems the power plant can operate safely. In this paper, to facilitate the existing record process in the power plant, we develop a field inspection management system based on embedded systems and wireless sensor networks. Embedded devices have the advantage of being easy to carry. As a result of this characteristic, these devices are not to be used in restricted areas, so critical data stored on the devices may be stolen or altered by external or unauthorized people. In addition, we propose security measures for preventing information stealing and alteration in the embedded system.
The architecture of the proposed system is illustrated in Figure 3. We install embedded Linux in flash memory because a hard disk does not exist in the embedded system. Embedded Linux is compact and slim. Also SQLite is installed to store and manage status and error data as DBMS. A field inspection management system is developed using Qt graphics library to operate on TFT/LCD. A field inspection management system consists of information management module, status information collection module, error input module, and security module.
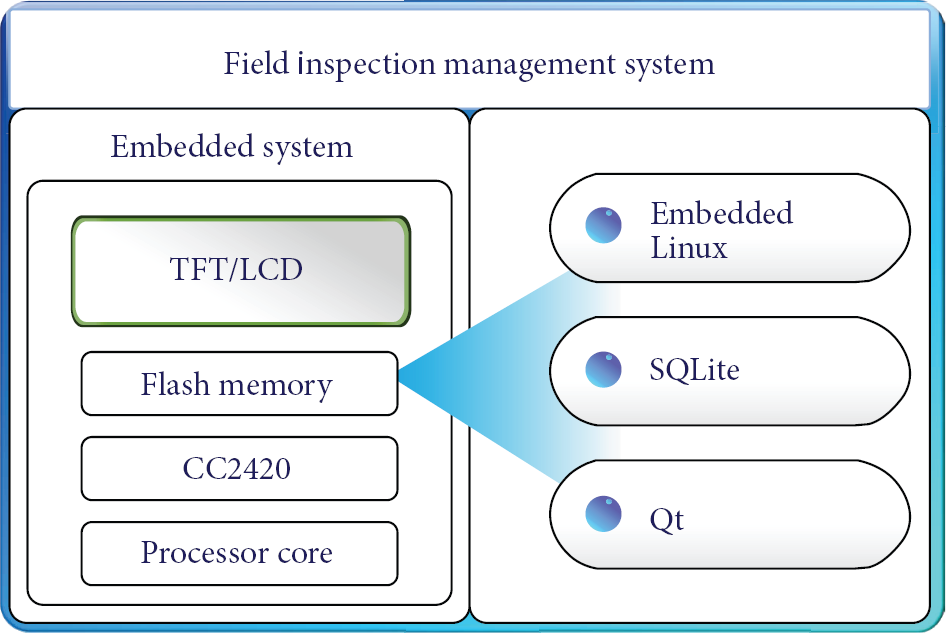
System architecture.
3.1. Information Management Module
This module manages effectively information gathered from the field. To achieve this, it creates a database to store status information. In this paper, we use a SQLite, which is a database engine suitable for embedded systems such as handheld and small devices [12]. Through this module, we can easily manage without network connection or firewall.
Through analysis of fieldwork in Section 3.1, database construction works as follows.
3.1.1. Draw an ERD
The first step in creating a database is to draw an ERD (entity relationship diagram), which presents error information. This diagram consists of six attributes as in Figure 4. The number of errors is a primary key. There are five field numbers, five location positions, fourteen error types, three emergency levels, and three process types.

ERD about error information.
3.1.2. Build a Table
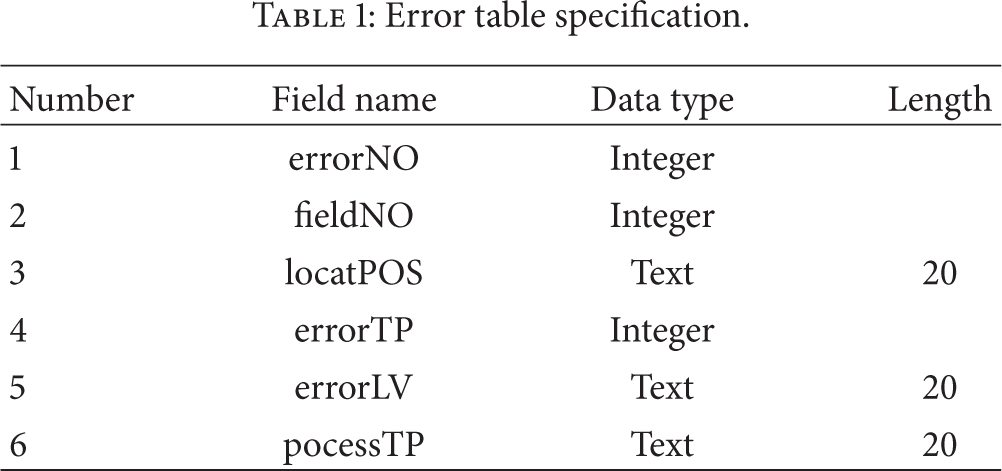
The second step works based on the ERD. That is, convert the entity into a table, set up a relationship to the reference key, and then set the data type for each field in a table. Error information table consists of six fields (refer to Table 1).
Error table specification.
3.1.3. Construct a DB
The third step creates the table in the physical database file. In this paper, we construct a database using SQLite suitable for handheld devices. SQLite is an embedded SQL database engine. Figure 5 shows the received error data. These data are collected in the field. For example, the first record in Figure 5 shows that one error occurred in 74th area, type of error was 1, error level was easy, and the request was necessary to work.

Collected error data.
3.2. Status Information Collection Module
Status information collection module is transmitted status information such as temperature and humidity from the sensor node attached to the field. In addition, location information is collected using ZigBee wireless communication. Through this module, we can collect status information easily unlike the existing method. In this paper, we use location estimation method which informs of the inspector's location and path check. This method uses tree routing proposed in the ZigBee standard. In other words, status information is transmitted wirelessly by mote which is installed in the field and then embedded system receives this data in the CC2420 chip and displays status information on TFT/LCD screen.
3.3. Display Module
Display module shows error and status information collected through field inspection on TFT/LCD screen. In this paper, we develop display module using Qt. Qt is a cross-platform application and UI framework for writing web-enabled applications for desktop, mobile, and embedded operating systems. Qt also is a C++ GUI toolkit and has the rich GUI toolkit widgets and high portability and easy layout. Figure 6 shows the screenshot of a field inspection management system implemented using Qt. As shown in Figure 6, inspector is able to manage error and status information easily.

User interface of management system.
3.4. Security Module
Embedded devices are portable. In other words, these devices may be exposed to the outside and critical data stored on these devices may be stolen or altered by external or unauthorized people [13, 14]. Therefore, security module is added to prevent information stealing and alteration in the embedded system.
Attacks on embedded systems from outside can be classified into three types: direct attack, short-distance attacks, and long-distance attack. The flowchart of a security module is shown in Figure 7.
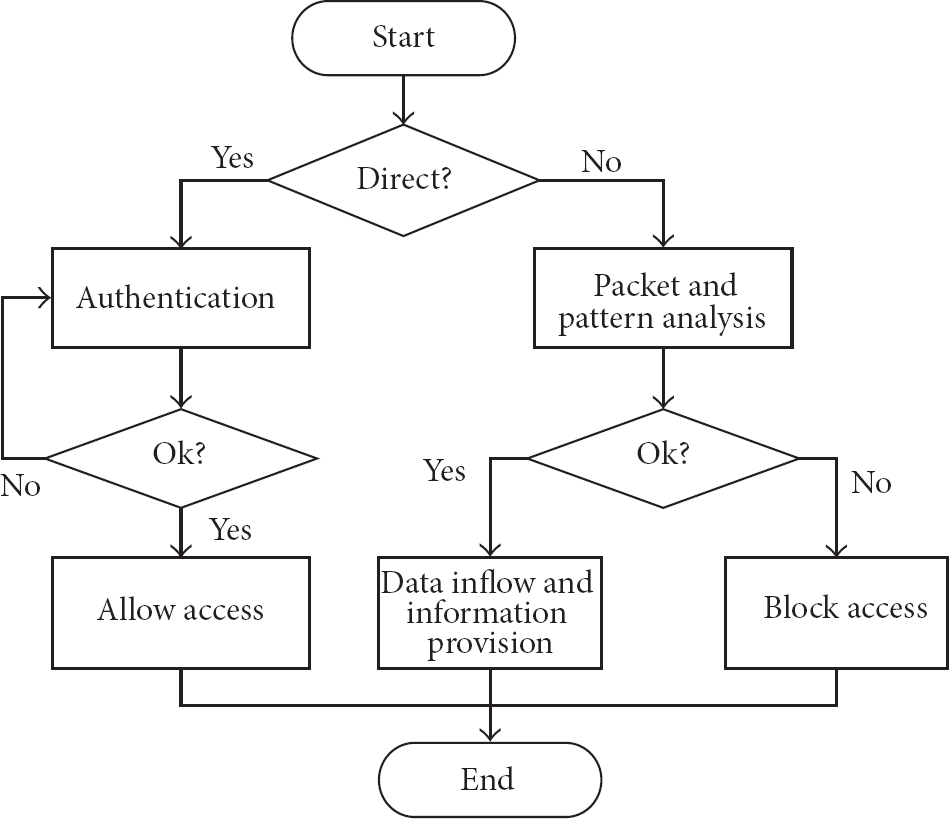
The flowchart of a security module.
Direct approach for embedded systems is to access through touch screen or keypad. If number of login exceeds limit or adversary access without administrator permission, embedded systems are automatically locked. Short-distance approach and long-distance approach are indirect approaches. Indirect approach for embedded systems is to access through LAN port or wireless LAN port. In this stage, a security module analyzes packets received from two ports and compares with normal packet patterns. If abnormal patterns are detected, block access to embedded systems.
4. Conclusion
In the plant field, various errors and failures occur every day. These errors and failures can be verified through field inspection and are generally recorded manually. However, this method cannot verify the status information in real time and enter error immediately. In this paper, in order to improve these problems, we analyzed work tasks and process in the plant field and then suggested a field inspection management method through this analysis. That is, we present a design and implementation of a field inspection management system based on embedded system and wireless sensor networks. In addition, we propose the security method for embedded system. Through this system, we can manage effectively error information collected in the field.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
