Abstract
PRINTcipher-48/96 are 48/96-bit block ciphers proposed in CHES 2010 which support the 80/160-bit secret keys, respectively. In this paper, we propose related-key cryptanalysis of PRINTcipher. To recover the 80-bit secret key of PRINTcipher-48, our attack requires 247 related-key chosen plaintexts with a computational complexity of
1. Introduction
Recently, the security of constrained hardware environments such as RFID tags and sensor nodes is major topic in cryptography [1, 2]. The research on lightweight block ciphers suitable for the efficient implementation in constrained hardware environments such as RFID tags and sensor nodes has been studied. As a result, PRESENT [3], LED [4], HIGHT [5], PRINTcipher [6], and Piccolo [7] were proposed.
PRINTcipher is a
Summary of cryptanalytic results on PRINTcipher.

CDLC: combined differential and linear cryptanalysis.
ISA: invariant subspace attack.
RKDC: related-key differential cryptanalysis.
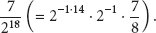
In this paper, we find weakness of PRINTcipher-48/96 on related-key attacks. To construct related-key differential characteristics, we focus on related keys that have different values in the part related to a key-dependent permutation. Thus, we can construct t-round related-key differential characteristics with a probability of
This paper is organized as follows. In Section 2, we describe briefly the structure of PRINTcipher. In Section 3, we explain how to construct related-key differential characteristics on PRINTcipher. Related-key attacks on PRINTcipher-48 and PRINTcipher-96 are proposed in Sections 4 and 5, respectively. Finally, we give our conclusion in Section 6.
2. Description of PRINTcipher
PRINTcipher-48/96 are
Figure 1 presents a single round of PRINTcipher-b, where
A b-bit plaintext
For
X is XORed with a b-bit round key

Consider
Consider
For
Consider that X is mixed by using

A single round of PRINTcipher-b.
With a bit permutation

In a key-dependent permutation
Key-dependent permutation

3. Construction of Related-Key Differential Characteristics on PRINTcipher
In this section, we present how to construct t-round related-key differential characteristics on PRINTcipher-48/96 by using properties of a key-dependent permutation
3.1. Related-Key Properties on Key-Dependent Permutation and S-Box
We consider a
In the above relations, if

In total, we can obtain the following six properties of
Property 1.
Consider
Property 2.
Consider
Property 3.
Consider
Property 4.
Consider
Property 5.
Consider
Property 6.
Consider
Furthermore, from the definition of S-box S, we can obtain the following property.
Property 7.
If
3.2. Related-Key Differential Characteristics on PRINTcipher-48
Among the above seven properties, we focus on Properties 1, 2 and 3. To apply these properties on the proposed attack, we first consider the following related-key pairs
Case 1 (l).
Consider the following:
Case 2 (l).
Consider the following:
Case 3 (l).
Consider the following:
We assume that the input difference of the target round is zero. If a related-key pair

Note that we cannot control the exact values of the related-key pair
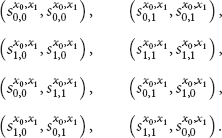
Consider
Consider
Consider
Consider
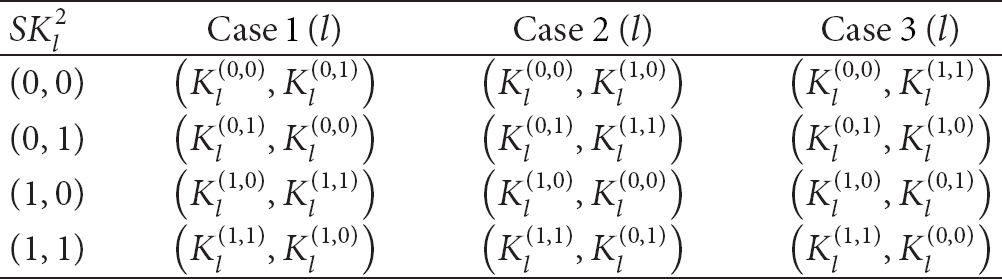
From these four related keys, we can combine six related-key pairs. For each value of
Consider
Consider
Consider
Consider
Recall that the condition of Case 1
The corresponding related-key pair according to the value of
If
3.3. Related-Key Differential Characteristics on PRINTcipher-96
In the case of PRINTcipher-96, we can construct
4. Related-Key Cryptanalysis on PRINTcipher-48
We are ready to propose related-key cryptanalysis on PRINTcipher-48. Recall that we can construct t-round related-key differential characteristics on PRINTcipher-
To solve this, we use 4 related keys
4.1. Basic Related-Key Attack on PRINTcipher-48
To attack the full PRINTcipher-
Our attack procedure mainly consists of the following steps. First, we consider plaintext structures which are composed of
4.1.1. Collection of Ciphertexts
First, we consider the following plaintext structures
Consider

Basic related-key differential attack on PRINTcipher-
Among all possible sixteen plaintext pairs for each plaintext structure, we consider only the following
Recall that
4.1.2. Filtering the Wrong Pairs
We discard the wrong ciphertext pairs by checking the difference between ciphertexts. For the right ciphertext pair, the output difference of round
In round
Since the filtering probability of this step is
4.1.3. Recovery of the Secret Key of PRINTcipher-48
For each ciphertext pair passing the above steps, we guess the following

Then we recover
First, we check
Until now, we introduced the attack procedure with a related-key pair
Select
Considering the related-key pair
Discard wrong pairs which do not satisfy
Guess 16-bit key
Considering the related-key pair
Discard wrong pairs which do not satisfy
Guess 16-bit key
Output the guessed key with the maximal count as the right key.
Do an exhaustive search for the remaining secret key by using trial encryption.
4.2. Complexities of Basic Related-Key Attack on PRINTcipher-48
This attack considers 4 related keys
A computational complexity of Step 1 is
4.3. Improved Related-Key Attack on PRINTcipher-48
In this subsection, we improve the basic related-key attack on the full PRINTcipher-48. To improve the basic attack, we consider
Select
Considering the related-key pair
Discard wrong pairs which do not satisfy
Guess
Guess
Considering the related-key pair
Discard wrong pairs which do not satisfy
Guess
Guess
Output the guessed key with the maximal count as the right key.
Do an exhaustive search for the remaining secret key using trial encryption.
4.4. Complexities of Improved Related-Key Attack on PRINTcipher-48
The improved attack uses 4 related keys
A computational complexity of Step 1 is
In Step 2(a) and Step 3(a), similar to the basic attack, we discard wrong ciphertext pairs by checking the following three checkPoints (see Figure 4).

Improved related-key differential attack on PRINTcipher-
The filtering probability of this step is computed as follows:
Thus,

For each remaining ciphertext pair, we guess total
In Step 2(b) and Step 3(b), we guess

Thus,
In Step 2(c) and Step 3(c), we guess
Since we can recover the

5. Related-Key Cryptanalysis on PRINTcipher-96
The overall attack procedure on the full PRINTcipher-96 is similar to that on the full PRINTcipher-48. Thus, we explain the attack procedure on the full PRINTcipher-96 briefly. In this attack, we consider

Related-key differential attack on PRINTcipher-
The attack procedure on the PRINTcipher-
Select
Considering the related-key pair
Discard wrong pairs which do not satisfy
Guess
Guess
Considering the related-key pair
Discard wrong pairs which do not satisfy
Guess
Guess
Output the guessed key with the maximal count as the right key.
Do an exhaustive search for the remaining secret key using trial encryption.
Since 4 related keys
6. Conclusion
In this paper, we proposed related-key cryptanalysis of PRINTcipher. Our attack results are summarized in Table 1. To recover the
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgment
This research was supported by the MSIP (Ministry of Science, ICT & Future Planning), Korea, under the C-ITRC (Convergence Information Technology Research Center) Support Program (NIPA-2013-H0301-13-3007).
