Abstract
Mobile roaming authentication scheme achieves the mutual authentication and session key establishment between the mobile user and the foreign agent. In 2013, Xie et al. pointed out that Chen et al.'s scheme is vulnerable to offline password attack, and does not achieve fair session key generation, user untraceability, user friendliness, and perfect forward secrecy, and then they proposed an improved scheme. In this paper, we propose an improvement of Xie et al.'s scheme, since the foreign agent may confuse the mobile users when multiple mobile users simultaneously access the foreign agent in Xie et al.'s scheme. Further, we prove the formal security of the proposed scheme, and present the performance comparison between our scheme and some related schemes. The proposed scheme is more efficient and secure than other related schemes and is suitable for using in the global mobility network.
1. Introduction
With the rapid development of mobile technology such as 3G and 4G wireless networks, more and more mobile users can access services in global mobility networks. A typical mobile roaming authentication scheme includes three parties: a mobile user, a foreign agent, and a home agent; both the mobile user and the foreign agent should authenticate each other before establishing the session key. Privacy-preserving is usually referred to as user anonymity and user untraceability. It is important to protect the user's privacy, such as what the users did or where the users accessed, from the attacker even if he accesses to user's records. Strong anonymous mobile roaming authentication means that only the home agent can know the mobile user's identity, but adversary or foreign agent cannot. Since wireless network is more vulnerable to several attacks and mobile terminals' computational power is limited, therefore, how to design the secure and efficient authentication scheme for roaming service with strong anonymity in global mobility networks is brought into much attention.
In 2004, Zhu and Ma [1] proposed a first anonymous authentication scheme for wireless communications. Lee et al. [2] showed that their scheme is vulnerable to forgery attacks and does not provide perfect backward secrecy and mutual authentication and proposed an improved scheme. Later, Chang et al. [3], Wu et al. [4], and Xu et al. [5] pointed out that Lee et al.'s scheme cannot achieve privacy-preserving and proposed an improved scheme, respectively. However, Youn et al. [6] showed that Chang et al.'s improved scheme does not achieve user anonymity and provide secure key establishing service, and Mun et al. [7] showed that Wu et al.'s scheme does not achieve anonymity and perfect forward secrecy. In 2011, He et al. [8] proposed a two-factor user authentication scheme for wireless communications. But Li and Lee [9] demonstrated that He et al.'s scheme has several weaknesses such as lacks of user friendliness, user anonymity, and fairness of key agreement, and then they proposed an improvement of He et al.'s scheme. However, Hu et al. [10] showed that Li et al.'s improved scheme cannot resist the foreign agent's impersonation attacks and proposed an improved scheme. In 2011, Chen et al. [11] proposed a lightweight anonymous user authentication for roaming in the global mobility network, but Xie et al. [12] showed that their scheme is vulnerable to offline password attack and does not achieve fair session key generation, user untraceability, user friendliness, and perfect forward secrecy; then they proposed an improved scheme to overcome the weaknesses of Chen et al.'s scheme. Very recently, Chen et al. [13] and Xie et al. [14] proposed some other anonymous authentication schemes for roaming service in global mobility networks.
In this paper, we first propose a strong anonymous mobile roaming authentication scheme in the global mobility network, which is a modified version of [12], the preliminary version of our work. In [12], there is no formal model and no formal proof of the proposed scheme and no performance comparison between the proposed scheme and some related schemes. On the other hand, the scheme in [12] may be impractical; the reason is that the foreign agent does not confirm who is authenticated by the home agent; when multiple mobile users simultaneously access the foreign agent, the foreign agent may confuse the mobile users. Moreover, an adversary can know the
The rest of this paper is organized as follows. Section 2 introduces the security model. The proposed scheme and security proof are given in Sections 3 and 4, respectively. After that, we present the performance comparison between the related schemes and ours in Section 5. Finally, we conclude the paper in Section 6.
2. Security Model
In this section, we recall the security model based on [15, 16].
2.1. Participants
In an authenticated key exchange (AKE) protocol, there are three different participants: a mobile user
2.2. Queries
The adversary's capabilities are captured by the following oracle queries.
If If
2.3. Freshness
The freshness of a session key is that the adversary does not trivially know the key. We say an instance I is fresh if (1) instance I has accepted; (2) no
2.4. Semantic Security
Finally, the adversary outputs a bit
3. The Proposed Scheme
In this section, we demonstrate a practical scheme which is a modified version of our preliminary scheme in [12]. Some notations which will be used in this paper are defined as follows:
E: an elliptic curve defined over a finite field with large order n, G: a generator on E with large order n, N: a secret value of
3.1. Registration
When a mobile user
Step 1.
The mobile user
Step 2.
Upon receiving the message from
Step 3.
The
The login and authentication phase of the proposed scheme is shown in Algorithm 1.
MU FA HA
The session key:
3.2. Login
When
Step 1.
It chooses a random number
Step 2.
It sends the login request
3.3. Authentication
Step 1.
The
Step 2.
The
Step 3.
The
Step 4.
The
Then the
Step 5.
On receiving the message
3.4. Password Change
When mobile user
4. Security Analysis
Theorem 1.
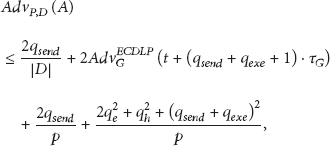
Let G and D be an elliptic curve group and a uniformly distributed password dictionary, respectively. Let P be our scheme, and let A be an adversary. Then, one has
Proof.
We define a sequence of experiments starting at the real attack experiment
Experiment Exp
0
. In the random oracle model, this experiment is the real attack. By definition, we have
Experiment Exp
1
. In this experiment, we simulate hash oracles and the encryption/decryption oracles (see Algorithm 2).
Experiment Exp
2
. In this experiment, we simulate all oracles as in the experiment Exp
1
except that we cancel all executions in which some collisions occur in the transcript
Experiment Exp
3
. In this experiment, we cancel the executions wherein the adversary may be lucky in guessing the authentication values
Experiment Exp
4
. In this experiment, we use random value (
Experiment Exp
5
. In this experiment, we introduce a random self-reducibility of the ECDL problem into the executions, given one ECDLP instance
If the
Therefore, Theorem 1 is concluded.
(i) On a hash query Otherwise, choose an element (ii) On a query Otherwise, choose an element C, add the record (iii) On a query Otherwise, choose an element M, add the record
(i) On a query as login algorithm. Then the query is answered with (ii) On a query proposed as login algorithm and authentication Step 1 algorithm. Finally, the query is answered with (iii) On a query correct state, we proposed as authentication Step 2 and Step 3 algorithm. At last, the query is answered with (iv) On a query as authentication Step 4 algorithm. The query is answered with
(i) On a query If the instance (ii) On a query The query is answered with the transcript (iii) On a query Get the session key return the session key, otherwise we return a random value with the same length.
5. Performance Comparison
Since Chen et al.'s [11] scheme is more efficient than other schemes without perfect forward secrecy, to the best of our knowledge, only Mun et al. [7], Li and Lee [9], Hu et al. [10], Xie et al. [12], Chen et al. [13], and Xie et al. [14] schemes can provide perfect forward secrecy. Therefore, we will present performance comparison between our scheme and these related schemes. Table 1 is performance comparison of login and key agreement phase, as we know that login and key agreement is the main body of an authentication scheme, and registration phase only performs one time before authentication.
Performance comparison.

Let
According to Table 1, we can conclude that Chen et al.'s [11] and Mun et al.'s [7] schemes are more efficient than others since Chen et al.'s scheme is completely based on hash and symmetric encryption/decryption operations but does not provide perfect forward secrecy and Mun et al.'s scheme is vulnerable to several attacks such as impersonation attack, replay attack, man-in-the-middle attack, and verification table stolen attack. And our scheme only needs 0.44 seconds in login and key agreement which keeps low performance cost.
6. Conclusions
In this paper, we proposed a modified scheme of our preliminary work, which was presented in ISBAST 2013. Compared with the preliminary work, the modified scheme can eliminate the weaknesses of the previous version. Further, we proved the security of the modified scheme and showed that the proposed scheme is efficient according to the performance comparison between our scheme and some related schemes. Therefore, the proposed scheme is secure and efficient and is suitable for using in the global mobility network.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This research was supported by the Major State Basic Research Development (973) Program of China (no. 2013CB834205), the National Natural Science Foundation of China (no. 61070153), the Natural Science Foundation of Zhejiang Province (nos. LZ12F02005, LY12F02006), and a Grant from the RGC of the HKSAR, China (no. CityU 121512).