Abstract
In wireless sensor networks (WSN), two major challenges are how to conserve the battery power and a series of security challenges. The power conservation and security are important for reliability and longevity of a WSN. This paper proposes an approach called “priority based approach (PBA)” which empowers the node to choose the most important packet based on the priority and the current energy status of the forwarding node. Thus we can minimize the average delay and energy spent and maximize the throughput and packet delivery ratio (PDR) when compared to game theory approach.
1. Introduction
A wireless sensor network consists of many wireless sensors that collect data like temperature, light, humidity, vibration, and other physical environmental conditions. The information is processed and sent to the sink. Each node has a battery with limited capacity which is very difficult to recharge and change due to the environment in which it is deployed [1].
So, one of the major constraints is to minimize power consumption. Also, WSN imposes a series of security challenges to network designers. Among these security problems, denial of service (DOS) attack eliminates the network capacity to perform its expected function. The DoS attack is defined as vulnerability by arbitrarily neglecting to route some messages [2].
The attacker node still participates in the network and may even acknowledge reception of data packets to the sender, as it drops messages randomly. Such a node should be neglectful by giving low priority value to it. Otherwise, the urgent messages are also hacked and dropped by the attacker.
We use “priority based approach” to extend a sensor's battery life and also improve security [3]. We accomplish this by giving priority to each packet as which is most important and which is less important by priority assignment which will be discussed later.
The rest of this paper is organized as follows. Section 2 discusses cluster scenario. In Section 3, we present related work. Section 4 presents priority based approach, while Section 5 shows and discusses simulation and results. Section 6 discusses all the protocols. Finally, we conclude our work in Section 7.
2. Cluster Scenario
We form four clusters, that is, C1, C2, C3, and C4, respectively. Each cluster is having one cluster head (CH), that is, CH1, CH2, CH3, and CH4, respectively, and many sensor nodes. Finally, the network should have one base station (BS). Here an attacker is present, that is, DoS attack.
To conserve power and enhance security, we should give less priority to attacker node according to their impact severity [4]. This supports the network designers to decide that the urgent data packets should be forwarded to the destination node and should not be sent to the attacker node.
The cluster formation scenario is shown in Figure 1.

Cluster formation scenario.
Every sensor node periodically senses whether the urgent messages are coming or not. Otherwise, normal prioritized packets are communicated. And also, the sensor senses whether the attacker node is arriving near to it, but already we configured the attacker node with lower priority, so the sensor does not send the packets to the attacker node.
If the sensor node received any urgent messages (namely, theft or fire) from the associated cluster and sends the information report to the associated cluster head (CH) node, the latter computes whether the urgent messages are received and then delivers first to the base station [5].
3. Related Work
There are many techniques that have been proposed to extend battery lifetime in recent years. One of the most popular cluster based routing protocols in WSN is “LEACH” [6]. The operation of LEACH is divided into rounds. Each round is started with a set up phase, and it is followed by a steady state phase when data are transmitted from the sensor nodes to the CH and to the BS. LEACH randomly selects a few nodes as CHs and balances power dissipation of the sensor nodes [7].
Anastasi et al. proposed an approach called “duty cycling.” In duty cycling, we turn off the radio transceiver on sleep mode whenever the communication is not needed. But also this is the most effective way to reduce the energy consumption. Moreover a sleep/wakeup scheduling algorithm is required and energy saving is obtained at the expense of an increased node complexity and network latency [8].
Fasolo et al. proposed “in-network aggregation” technique. It is intended to merge routing and data aggregation techniques. To improve robustness of data aggregation, multipath routing algorithms together with erasure codes can be employed. But most commonly used erasure codes are not suitable for WSN [9].
Asadi et al. proposed “game theory” for the purpose of extending a sensor's battery life. They accomplished this by helping the sensors optimize their decision making process about whether to forward any data packets or not that they may receive. On one hand, if a node decides to never forward packets, it conserves battery power, but no communication takes place. On the other hand, if a node forwards any packets, then it demonstrates its reliability and traffic flows through the network but the node will run out of battery power [10].
By using game theory, we attempt to find an optimum configuration that will extend a node's battery life while still allowing the sensor node to forward an acceptable amount of packets through the network. Implementing game theory is beneficial by helping reduce the amount of power consumption throughput WSN. By adding a decision making process of when to send and not to send the data packets, the sensors conserve the power as well as detect the attacker node.
4. Priority Based Approach
The limitations of the game theory are as follows: the assumption that players (sensors) have the knowledge about their own payoffs and payoffs of other sensors is not practical. The techniques of solving games involving mixed strategies particularly in case of large payoff matrix are very complicated, so decision making is also complicated.
To overcome the decision making problem, we are giving priority value to each packet. To improve the power conservation and security in WSN, “priority based approach” (PBA) is implemented. The PBA approach can be done by assigning “priority assignment” table.
4.1. Priority Assignment
The priority value should be given to all the data packets in a sensor node, depending upon the importance of the message and fastness to reach the sink node. The priority assigned by the source node should be stored in a field, namely, “priority,” of the data packet's header and it should remain in part of the header, till it reaches the sink node [11].
According to the urgency level of the data packet, the source node should assign priority value by “priority assignment” table as shown in Table 1.
Priority assignment.

4.2. Assigning Less Priority to the Attacker Node
The attacker is detected by using “reputation method.” The base station (BS) always tracks the reputation of each node in the network. The BS decides whether a node is acting as an attacker node or not based upon its throughput. The BS takes the current reputation of each node and calculates its average and standard deviation (SD). If a node's reputation is lower than the average minus SD, that node is considered to be an attacker node. Then we assign a less priority to that attacker node [10]
4.3. To Find the Energy Level of the Node
All the data packets are always possess a header field of “priority” in a sensor node. The path node can read the packet's priority field and, depending upon the priority, it takes the appropriate forwarding decisions. Along with the priority, the forwarding node must also know the current status of the energy level, so as to decide whether the current status of the energy level allows forwarding the given priority packet or not [12].
4.4. Energy Level Reporting Technique
The current status of energy level in a sensor node can be calculated by a technique called “power status reporting” technique. For example, if node 1 forwards a packet to node 2, then first it should know whether node 2 is energy optimized by taking a packet forwarding decision based on node 2's energy level. Then according to power status reporting by node 2 to its neighbor node, node reports its powers, whenever it reaches above, below, or exact energy level of the critical energy level of 75%, 50%, and 25% of the total sensor node energy.
Initially all the nodes are having 100% power. Whenever transmission takes place, the energy level of each node depletes to start. According to the power status reporting scheme, node 2 should inform node 1 about its power status as soon as its power level starts to deplete at 75%, 50%, and 25%. So, a node always knows which of its neighbor nodes has what energy level and according to that it makes the choice of the best forwarding node for a particular priority packet.
4.5. Restoration of Power
The node forwards a packet first which are the highest priority (P1) packets. So, the energy level gets depleted. When it becomes below the critical level, that is, 25%, its workload gets automatically decreased, so it does not forward the rest of the prioritized packets like P2, P3, and P4. So, we have to refill the energy level by using its solar cells. As its power level increases above its critical level, it informs all its neighbor nodes by using power status reporting scheme and its workload also increases [13].
If we use sleep mode scheme when the power is in low state (<25%), then the nodes switch to sleep state. Here, we can conserve the power of the node because there is no transmission taking place. In sleep mode scheme, the power is only sustained. But when we use solar cells, the power level is increased above the critical level (25%). Our goal is to transmit prioritized packets without fail. So, the node refills its energy level; by using its solar cells the energy level is increased above 25% and it can transmit the rest of the prioritized packets. But in sleep mode scheme, the energy level is only sustained. So, if transmission takes place then the low state node becomes dead soon [14].
4.6. Algorithm
Step 1. Start.
Step 2. Initialize P.
Step 3. Switch.
Case 1. Find suitable neighbor node for packet forwarding; exit switch.
Case 2. Find neighbor node with above 75% energy level; exit switch.
Case 3. Find neighbor node with above 50% energy level; exit switch.
Case 4. Find neighbor node with above 25% energy level; exit switch.
Step 4. Request retransmission of packet from previous node.
Step 5. Exit switch.
Step 6. End.
4.7. Flowchart
See Figure 2.

5. Simulation Result
This section presents simulation result of “priority based approach” when compared with normal AODV, DoS attack, and game theory (Table 7). It is implemented in NS2 software. NS2 is an object oriented, discrete event driven network simulator developed at UC Berkeley, written in C+ and OTcl. NS2 is useful for simulating local and wide area networks. The NS2 simulation parameters are shown in Table 2.
NS 2 parameters.

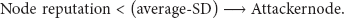
5.1. Average Delay
Figure 3 represents average delay that has been calculated using different protocols such as normal AODV, DoS attack, game theory, and PBA. AODV protocol [15] is normal protocol and the delay is also normal but it is slightly higher than PBA (Table 3). In DoS attack, due to the presence of an attacker, the delay is always high. In game theory GTFA, the delay is slightly higher because of decision making. In our proposed PBA approach, already we assign priority to the packets so the delay is very less compared to all the three protocols.
Average delay calculation.

Average delay graph.
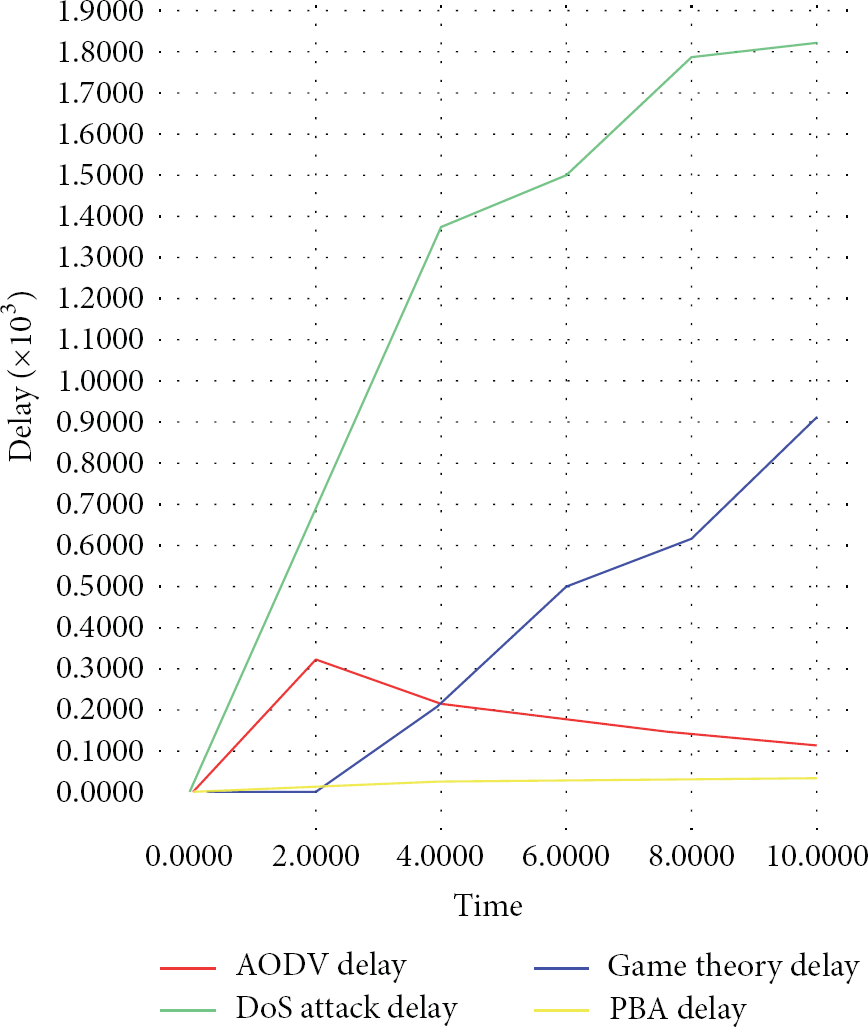
5.2. Energy Spent
Figure 4 represents the energy spent of a sensor node. To conserve battery power, we should minimize energy spent [16]. In DoS attack, due to the presence of an attacker there is no successful transmission. Due to that, energy spent is the highest (Table 4). In AODV, when link breakage happens, rerouting will take place. Due to rerouting energy spent is higher. In GTFA, every time it takes a decision when to send a packet and not to send a packet. Here, energy spent is comparatively less but due to the decision making the energy spent is comparatively high. In PBA, due to the preassigned priority the energy spent is very less. Thus, we minimized energy a lot in priority based approach (PBA).
Energy spent calculation.

Energy spent graph.
5.3. Throughput
Figure 5 represents throughput, that is, total number of packets sent from sender and how many packets are received to the receiver [17]. In DoS, all the packets are received by the attacker, so the throughput is the highest. In AODV and GTFA, the packet loss is high, so throughput is low. In PBA, the packet loss is very less, so throughput is higher. Thus, we maximized the throughput compared to game theory, AODV, and DoS attack (Table 5).
Throughput calculation.


Throughput graph.
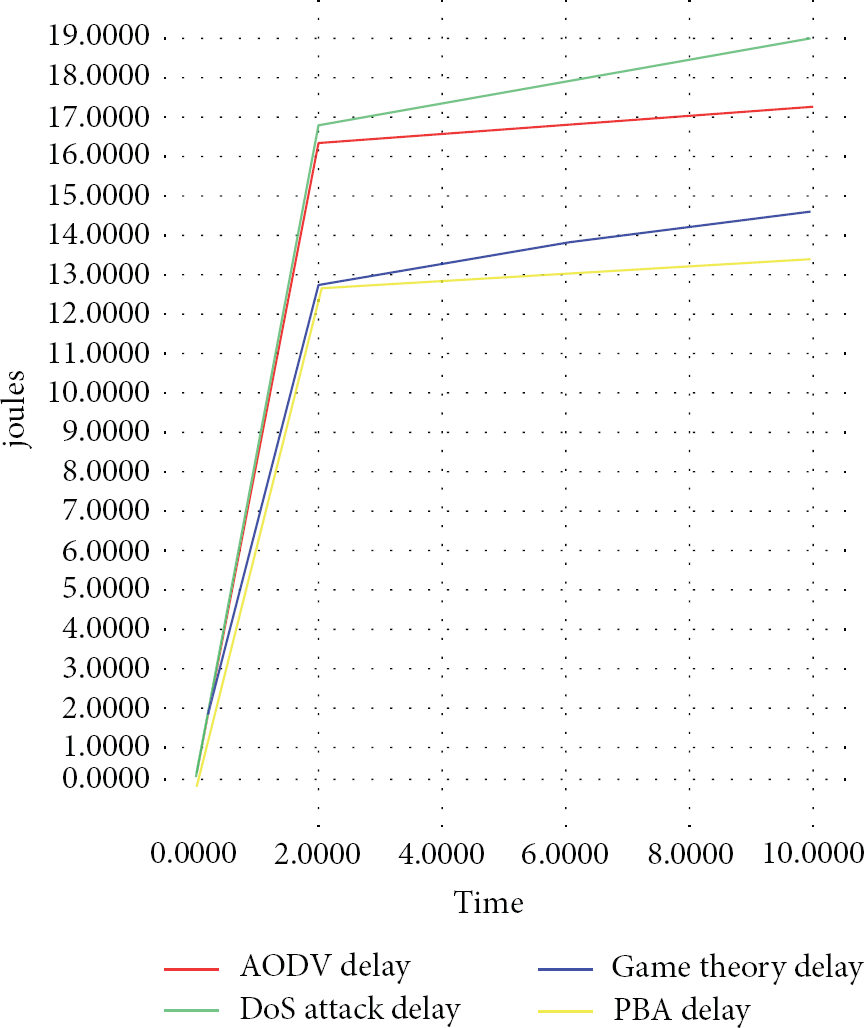
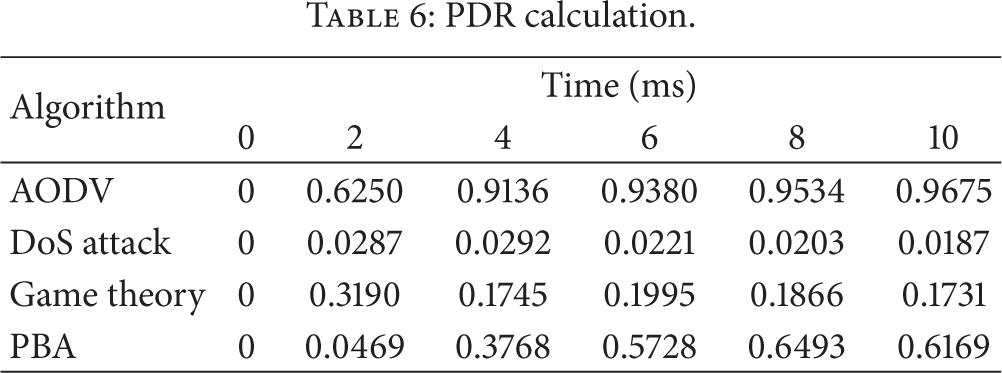
5.4. Packet Delivery Ratio (PDR)
Figure 6 represents packet delivery ratio (PDR), that is, the total average of delivered data packets [18]. In AODV, all the packets are delivered successfully. In PBA, due to less packet loss PDR is higher. In GTFA and DoS attack, the packets are lost heavily. So, the packet delivery ratio is very less.
PDR graph.
6. Discussion
The wireless sensor network has many constraints such as average delay, energy spent, and security. It is indeed necessary to consider these constraints before designing any sensor networks. Nodes communication and data transmission take much power and consume more energy. So, PBA approach technique is proposed to consume less energy and also enhance high security compared to normal AODV protocol, DoS attack presence protocol, and game theory approach.
6.1. AODV Protocol
The AODV protocol is only used when two endpoints do not have a valid active route to each other. When link breaks, rerouting will take place by AODV protocol [19]. It is done by the operation of nodes that can keep track of connectivity to neighbors using available data link or network layer mechanisms. In every pause time, 2 ms, 4 ms, 6 ms, 8 ms, and 10 ms, the average delay and energy spent are less. Throughput and PDR are high.
6.2. DOS Attack
It is a type of which is designed to bring the network to its knees by flooding it with useless traffic. Many DoS attacks, such as the ping of death and teardrop attacks, exploit limitations in the TCP/IP protocols. For all known DoS attacks, there are software fixes that system administrators can install to limit the damage caused by the attacks [20]. But, like viruses, new DoS attacks are constantly being dreamed up by hackers. Due to the presence of attacker, the delay and energy spent are high.
6.3. Game Theoretic Approach
In game theory, the basic assumption is that the decision makers pursue some well-defined objectives and take into account their knowledge or experience of the other decision makers' behavior. In this paper, the game theory pursued well-defined decision making and also improves high security, throughput, and PDR. It also minimizes the average delay and energy spent during communication [21].
6.4. Priority Based Approach
To overcome all the shortcomings of above protocols, we are giving priority to the data packets depending upon the importance of the messages. So, it reaches rapidly the destination even though attacker is present. So, this PBA approach is effective compared to all the above protocols. Here the delay and energy spent are very less. The throughput and PDR are very high. The discussion is shown in Table 6.
PDR calculation.
Comparison of AODV, DoS attack, GTFA, and PBA.

7. Conclusion
Power conservation and security are the major challenges in WSN. In this paper, we proposed an approach called “priority based approach (PBA)” and established a relationship between packet priority and current energy status of a sensor node which decides the most urgent message to forward first according to its priority and also its energy level. By giving less priority to the attacker node, we then improved the security of a network. Also, the proposed priority based approach emphasizes reducing the workload on some nodes depending upon the energy level and gives time to refill their energy. Therefore PBA ensures a real time communication in WSN with minimizing the delay and energy spent and maximizing the PDR and throughput which further maximizes the lifetime of the network.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
