Abstract
The authors first review the recently proposed Das's biometric-based remote user authentication scheme, and then show that Das's scheme is still insecure against some attacks and has some problems in password change phase. In order to overcome the design flaws in Das's scheme, an improvement of the scheme is further proposed. Cryptanalysis shows that our scheme is more efficient and secure against most of attacks; moreover, our scheme can provide strong mutual authentication by using verifying biometric, password as well as random nonces generated by the user and server.
1. Introduction
In a client/server system, the validity of remote user is necessary to assure the security of the system. Traditional remote identity-based authentication schemes [1–9] are based on passwords only. However, simple passwords are always easy to break by using simple dictionary attacks since they have low entropy. To overcome this problem, cryptographic secret keys and passwords are used in the remote user authentication schemes. But the long and random cryptographic keys are difficult to memorize and hence they must be stored somewhere [10]; it is expensive to maintain the long cryptographic keys. Furthermore, both passwords and cryptographic keys are unable to provide nonrepudiation because they can be forgotten or lost or when they are shared with other people, there is no-way to know who the actual user is [11]. A biometric system operates by acquiring biometric data from an individual, extracting a feature set from the acquired data and comparing this feature set against the template set in the database [12–14]. In [3], the authors propose an online Biometric keys cannot be lost or forgotten. Biometric keys are very difficult to copy or share. Biometric keys are extremely hard to forge or distribute. Biometric keys cannot be guessed easily. Someone's biometrics is not easier to break than others.
As a result, biometric-based remote user authentications are inherently more reliable and secure than usual traditional password-based remote user authentication schemes.
In this paper, we propose an improvement of Das's biometric-based remote user authentication scheme using smart cards in order to withstand his design flaws. The remainder of this paper is organized as follows. In Section 2, we briefly review the Das's biometric-based remote user authentication scheme using smart cards [21]. In Section 3, we analyze the design flaws in Das's scheme. In Section 4, we propose an improvement of the scheme in order to eliminate the design flaws discussed in Section 3. Security analysis of our scheme and performance comparison with other related schemes are implemented in Section 5. Finally, we conclude the paper in Section 6.
2. Review of DAS's Biometric-Based Remote User Authentication Scheme
In this section, we review in brief Das's biometric-based remote user authentication scheme [21]. For describing the Das's scheme [21], we use the notations shown in Table 1. Das's scheme consists of the following four phases, namely, registration phase, login phase, authentication phase, and change password phase. Details of each phase are given in the following subsections.
Notations used in the proposed scheme.

2.1. Registration Phase
In order to login to the system, the remote user
(1) (2) Computes (3)
Step
1. The user inputs his/her personal biometric
Step
2. The registration center
Step
3. Finally, the registration center
2.2. Login Phase
In this phase, if a user
(1) Inserts the smart card and (2) Verifies whether (3) If it holds, then (4) Computes (5) Checks if (6) If it holds, the smart card computes the following: (7)
Step
1.
Step
2. Next, the user's personal biometric template
Step
3. If the above verification does not hold, then
Step
4. The smart card computes
Step
5. If
Step
6. Finally,
2.3. Authentication Phase
After receiving the login request message
(1) Checks whether the format of If above holds, (2) Verifies whether If it holds, then computes (3) (4)Verifies whether (5) If above holds,
Verifies whether If it does not hold, Otherwise, if it holds, then computes
(6) (7) Verifies whether (8) If it holds, (9) Otherwise,
Step
1.
Step
2. If the above format is valid,
Step
3.
Step
4. After receiving the message in Step 3,
Step
5. After receiving
Step
6. If the abovementioned does not hold,
Step
7. In case the verification is successful, then only
2.4. Password Change
The password change phase of Das's scheme [21] has the following steps.
Step
1. It inserts the smart card into the card reader and offers
Step
2. It verifies whether the user's personal biometric template
Step
3. If
Step
4. The smart card then computes
Step
5. Finally, replace
3. Cryptanalysis of Das's Scheme
This section demonstrates that Das's scheme [21] has some drawbacks: denial-of-service attack, user impersonation attack, replay attack, and password change problem.
3.1. Denial-of-Service Attack
One of fundamental properties of a secure one-way hash function is that its outputs are very sensitive to small perturbations in their inputs. The cryptographic hash function cannot be applied straightforwardly when the input data are with noise such as biometrics [22]. Then the predetermined threshold for biometric verification cannot be used to measure outputs of hash functions. In the registration phase of Das's scheme, the register center
3.2. User Impersonation Attack
We see from the login and authentication phase of Das's scheme that an attacker can impersonate a legal user to access to the server. In the login phase of Das's scheme, since the user
When an attack denoted as
3.3. Replay Attack
In Das's scheme, the replay and man-in-the-middle attack is withstood by checking whether
3.4. Password Change
In password change procedure of Das's scheme, if remote user
4. Proposed Scheme
In this section, we propose an improvement of the Das's biometric-based remote user authentication scheme [21] using smart cards in order to withstand the flaws discussed in Section 3. For convenience, we use the same notations used as in Das's scheme shown in Table 1.
4.1. Registration Phase
In order to login to the system, the remote user
(1) (2) computes (3)
Step
1. The user
Step
2. The registration center
Step
3. Finally, the registration center
4.2. Login Phase
In order to login to the system, the remote user
(1) Inserts the smart card and inputs (2) Verifies whether (3) If it holds, then (4) Computes (5) If it holds, the smart card computes (6)
Step
1.
Step
2. The smart card computes
Step
3. Finally, the user
4.3. Authentication Phase
When the remote server
(1) When receiving (2) (3) (4) When receiving at computes (5) then (6) When receiving then computes If it holds,
Step
1. Verify T. If
Step
2.
Step
3.
Step
4. After receiving the message
Step
5.
Step
6. When
4.4. Password Change
In our scheme, user
Step
1.
Step
2. If it holds,
Step
3. Smart card performs
Step
4. If it holds, the smart card computes
Step
5. Finally, replace
5. Security Analysis and Performance of the Proposed Scheme
5.1. Security Analysis
If a legal user lost his/her smart card, it is extremely hard for an adversary to derive the user's sensitive information such as user's identity, password, and biometrics because the extraction of parameters from the smart card is quite difficult. Furthermore, the adversary cannot change the password because he/she cannot pass the biometric verification.
5.1.1. Denial-of-Service Attack
In our proposed protocol, we take into account hash function's sensitivity to small perturbations in its inputs. In the login phase, user's biometric verification is performed by checking
5.1.2. Stolen-Verifier Attack
Our scheme can resist stolen-verifier attack because the scheme is free from the verifier/password table. In our protocol, the remote server
5.1.3. Many Logged-In Users Attack
Most systems, which maintain the password table to verify user login, are vulnerable to this kind of threat. Our scheme can resist the threat since our scheme requires on-card computation for login to the remote server
5.1.4. Guessing Attack
Our protocol can resist guessing attack, which is a critical concern in password-based systems, since the password in our protocol is transmitted as a digest of some other secret information. The attacker cannot guess the user's password from the digest because of the one-way characteristic of the hash function, even if the attacker may get the digest which contains the password.
5.1.5. Replay Attack
Replaying an intercepted message can be prevented in our proposed protocol. If an attacker intercepts
5.1.6. User Impersonation Attack
In the login phase of our scheme, the message sent to remote server
5.1.7. Server Masquerading Attack
If an attack
5.1.8. Insider Attack
In the registration phase, if the user's password
5.1.9. Mutual Authentication
As described above, our scheme can withstand the user impersonation attack and server masquerading attack; consequently our scheme can provide mutual authentication between the user
5.1.10. Man-in-the-Middle Attack
Man-in-the-middle attack means that an active attacker intercepts the communication line between a legal user and the server and uses some means to successfully masquerade as both the server to the user and the user to the server. Then, the user will believe that he is talking to the intended server and vice versa. In our scheme, when a user
5.2. Performance of the Proposed Scheme
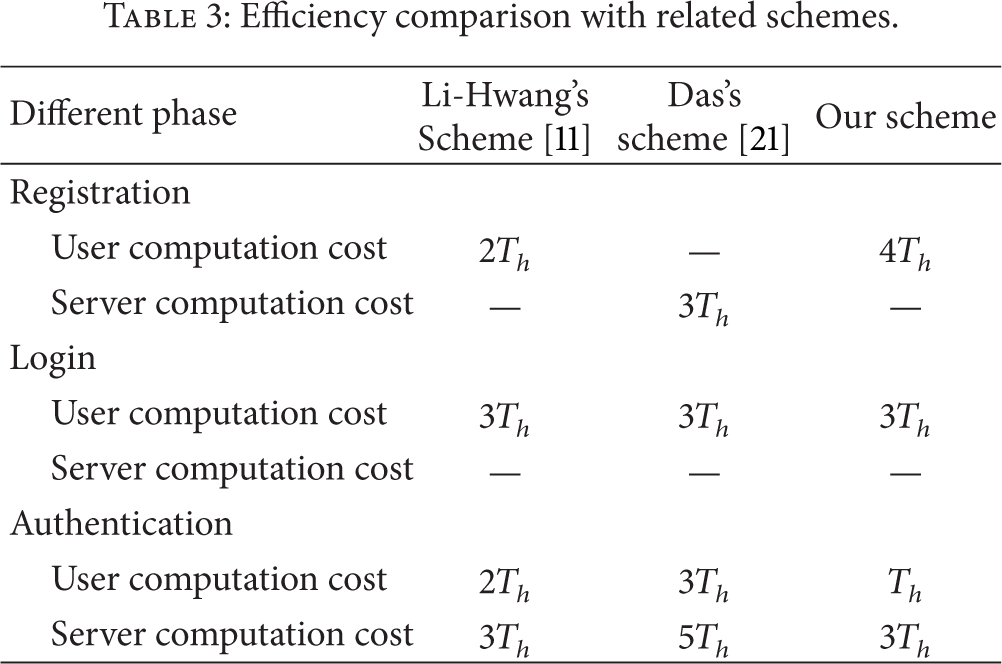
In this subsection, we compare the performances of our improved scheme with those for Li-Hwang's scheme [11] and Das's scheme [21]. It is worth recalling that the protocol of Li-Hwang's scheme [11] has security weaknesses against denial-of-service attack, replay attack, user impersonation attack, and man-in-the-middle attack. It is noted that Das's scheme [21] has security weaknesses against denial-of-service attack, user impersonation attack, replay attack, server masquerading attack, and insider attack. The security comparisons between our scheme and the schemes proposed by Li and Hwang [11] and Das [21] are summarized in Table 2. For the convenience of evaluating the efficiency of related scheme, we define the notation
Security comparisons among related protocols.

Efficiency comparison with related schemes.
6. Conclusion
This paper presents a biometric-based user authentication scheme for client/server system. The method employs biometric keys and resists the threats of stolen-verifier, of which many are logged-in users with the same login identity, denial-of-service attack, guessing attack, insider attack, replay attack, user impersonation attack, server masquerading attack, and man-in-the-middle attack. Moreover, the improved scheme can realize mutual authentication between the user and remote server. The proposed scheme uses only hash function and XOR operation, which is efficient compared with that of related protocols. In addition, the user's password can be changed freely using the proposed scheme. Our proposed scheme provides strong authentication with the help of verifying biometrics, passwords, and random nonces generated by the user and server as compared to that of related schemes.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
The authors would like to thank the valuable comments and suggestions of the reviewers. This work is supported in part by National Natural Science Foundation of China (no. 61370223) and by Science Research Project of Hubei Provincial Department of Education (XD2012374 and B2013024).
