Abstract
Fault tolerance and reliable transmission are hot issues in wireless sensor networks. For the problems that the fault of nodes or links will affect the transmission stability and reliability of the network, a gradient based multipath reliable transmission strategy with fault tolerance is presented for wireless sensor networks. Firstly nonuniform clustering topology is established in nonequal clustering probability based on twice K-means algorithm. Then it calculates the comprehensive measurements (CM) of cluster heads by the quality evaluation function and establishes the contour lines. Finally gradient based multiple disjoint transmission paths are established by the mechanisms of load balance and linear erasure coding. It also establishes the transmission mathematical model to analyze the performance of the network. Simulation shows that this strategy has good performance of fault tolerance. It improves the transmission reliability of the network and energy efficiency.
1. Introduction
The reliability of data transmission is an important index to evaluate the performance of wireless sensor networks (WSNs). The stable topology routing is established to realize the effective and reliable data transmission giving the consideration to the balance of energy consumption, low transmission delay, and so forth [1]. However, owing to the characteristics of the network itself, such as ad hoc network with no center, dynamic topology changes, source restriction of the computing, transmission, and energy consumption, as well as the unpredictability of the working scenario especially brought by vibration and electromagnetic interference, failures of nodes or links often occurred which lead to data loss or retransmission. This seriously affects the data receiving rate, accuracy rate, and the average transmission delay. Finally it lowers the transmission stability and reliability, weakens the reservation function, and brings great challenges to the existing network technologies [2].
A network with good performance has characteristics of reliable data transmission, efficient energy consumption, and low transmission delay. When the malfunction occurs, the network can adaptively adopt the reasonable fault-tolerant control scheme to deal with the failure and continue to provide highly credible computational service. So fault tolerance becomes the key technology to improve the transmission stability and reliability of the network. Now it attracts much attention and becomes one of the hot issues in wireless sensor networks [3].
The reliable transmission strategy with fault tolerance mainly contains multipath transmission routing, network coding, packets retransmission, and so forth [1, 4–11]. Unquestionably, the network has better performance when it adopts the optimal combination of some methods or combined control optimization with other layers [4, 11]. Therefore, the core of reliable transmission with fault tolerance is to establish an effective topology and data coding based multipath transmission mechanism. Multipath routing transmission technology with fault tolerance is to establish multiple transmission paths between the source node and the destination node to improve the load balance and transmission bandwidth. Network coding based redundancy transmission mechanism is to transmit the coded packets along multiple paths and to decode and to reconstruct the certain number of coded packets received at the destination node into the source data. Network coding should be combined with multipath transmission and load balance mechanism. Therefore, it is essential to establish the multipath data coding transmission based on an effective topology.
This paper mainly studies the issues that the node failure or link quality affects the stability and reliability of data transmission in network layer and presents a gradient based reliable multipath transmission strategy with fault tolerance. It mainly includes the establishment of the network topology by twice K-means nonuniform clustering algorithm and the establishment of gradient based multipath transmission mechanism according to nodes’ CM (comprehensive measurement). By adopting the mechanism of erasure coding and load balance, it decodes the received packets and reconstructs them into source data at the destination node to improve the reliable transmission and fault tolerance.
Our work makes the following new contributions. (1) Twice K-means algorithm is adopted to do the nonuniform cluster splitting to establish and optimize the hierarchical clustering topology. By this way, it can realize the load balance, improve the efficiency of energy consumption, and avoid the hot issue. (2) Contour lines are established according to the nodes’ CM to establish the gradient based multiple disjoint transmission paths between the adjacent hierarchical nodes. Combining with mechanism of erasure coding and load balance, complexity of the establishment of multipath routing is reduced and the performance of fault tolerance is improved. (3) Load balance mechanism based mathematical model is established to do the theoretical analysis on the performance of the network. Simulations are done to evaluate the performance of reliability and fault tolerance.
The rest of this paper is organized as follows: related work is in Section 2. Section 3 presents the network topology by twice K-means nonuniform clustering algorithm. Section 4 presents the establishment of multipath gradient routing according to nodes’ CM; furthermore, it establishes the mathematical model and does the theory analysis and proof on the network's performance. Section 5 is the simulations and analysis. The conclusion is in Section 6.
2. Related Works
2.1. Coding Based Multipath Transmission Technology
Coding based multipath transmission technology for fault tolerance is to transmit the encoding packets along multiple paths established between the source node and the destination node. Certain amount of encoded fragments received at the destination node is reconstructed into the source data. By the mechanism of redundant routing and network coding, load balance and transmission bandwidth are improved to realize fault tolerance and transmission reliability.
Energy efficient reliable multipath routing using network coding (NC-EERMR) [4] is to establish the multipath routing in a distributed way through multiple hops. Sub-Branch Multi-Path Routing Protocol (SMRP) [5], based on Secure and Efficient Intrusion-Fault Tolerant Protocol (SEIF) which is DM model, improves the fault tolerance and credibility by the mechanism of multiple routing selection in the distributed authentication way. Self-selecting reliable path routing (SRP) [6] which is based on SSR (self-selecting routing) and SHR (self-healing routing) has the transmission fault tolerance by establishing the multiple paths. Mixed multipath mechanism H-SPREAD [7] is based on the hybrid multipath data acquisition mechanism and adopts the key sharing and backup path for any node to improve security and reliability of data transmission. Network coding based multipath reliable transmission route (NC-RMR) [1] adopts BM mode to establish the logical backup for any path. DD (directed diffusion) [12] establishes the multipath transmission mode to deal with the node failure and topology changes through three phases: flooding the interests, establishing the gradient, and dynamically optimizing transmission routing. DD based multipath routing algorithm [8] strengthens the multiple paths with high quality and low transmission delay and [9] presents the DM based distributed multipath routing algorithm with high energy efficiency and scalable characteristic which can adjust data flow by the load balance mechanism. VR (distance vector routing) [10] that combines the coding algorithm and multipath transmission mechanism establishes paths by the light-weight flooding only when needing transmitting the data [11]. However, it is difficult to obtain the accurate amount of the paths.
2.2. Gradient Based Transmission Routing
Nodes in the network are divided into different hierarchies according to gradient values defined by the distance or hops to the destination node, nodes’ energy level, and transmission delay so as to establish the gradient based transmission routing by a certain strategy.
The energy balance nonuniform clustering gradient based routing (EBCAG) [13] transmits the data packets along the gradient descent direction to the destination node according to the gradient value decided by the minimum hops between the source node and the destination node. GBR (gradient-based routing) [14], which contains competitive algorithm GBR-C and adaptive GBR-C, is to establish two forward hops to minimize the probability of data retransmission. In gradient broadcast algorithm (U-GRAB) [15], the transmission decision depends on the node's practical degree and it preferentially selects the noncrowded channel and energy-efficient nodes for transmission. GBR (gradient-based routing) [16], based on DD protocol, transmits the data along the path with maximum gradient value determined by minimal hop to the destination node. FGS (fine-grain gradient sinking) [17, 18] introduces average weighted mechanism based on the HGS (hop gradient sinking) model and converts hop count information into fine gradient information as the reference to establish data transmission strategy. Data aggregating ring (DAR) [19] classifies the nodes by the hop counts, the data packets are not always transmitted along the gradient direction to the destination node through multiple hops, and the data with other gradient values can be directly forwarded to the destination node through only one hop by the load balance mechanism. In [20], the nodes are distributed in the different hierarchical circle areas based on the nodes’ nonuniform distribution strategy, it establishes the shortest transmission path also among different hierarchical circle areas. Gradient based routing MR2-GRADE [21] presents the greedy algorithm based GRADE-GF and lighted flooding algorithm based GRADE-RF. Reference [22] studies the gradient model based network's upper and lower bounds of the survival time. Gradient broadcast (GRAB) [23] allows nodes with low gradient values to forward data simultaneously to form the multipath routing. However, it lowers the transmission reliability owing to the conflicts of twice forwarding.
3. Topology Establishment for Multipath Transmission
3.1. Network Topology
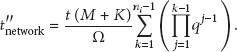
For large scale of wireless sensor networks, multipath reliable transmission mechanism which is based on nonuniform clustering topology by twice K-means clustering algorithm has good performance of fault tolerance. The nodes are uniformly distributed in the rectangular area and the destination node is located on the right. Nodes closer to the destination node are clustered by larger probability, so smaller scale and more quantity of clusters are formed near the destination node. The clustering topology is as shown in Figure 1.

Clustering topology.
3.2. Twice K-Means Based Nonuniform Clustering Algorithm
k objects are randomly selected as the initial clustering center and the clusters which the object belongs to are adjusted after many rounds iterations by the principle of minimum distance. Clustering topology is finally established until the clustering results are no longer changing. K-means based iterations through random selection of cluster heads can establish the optimized clustering topology with good performance of compactness within clusters and alienation among clusters. Hops that is from a cluster head to the destination node are calculated by the interest packets flooded among cluster heads. Cluster heads are divided into n hierarchical areas; clusters are split in larger clustering probability when n is smaller. Through twice K-means clustering optimization, smaller scale and more quantity of clusters are formed which are nearer to the destination node. This clustering topology can avoid the hot issue in the energy consumption. The algorithm is described as follows.
Step 1.
Set the parameters
Step 2.
Divide each object to the nearest clusters with the center
Step 3.
Calculate new center
Step 4.
Judge
Step 5.
Flood the interest packets among cluster heads and learn minimum hops from each cluster head to the destination node.
Step 6.
Judge the number of nodes in each subcluster
Step 7.
Randomly select the cluster heads in the nth hierarchical area and repeat Steps 2–4 to do the twice K-means based cluster splitting until the clustering optimization for all nodes in n hierarchical areas has been finished.
3.3. Characteristics of Twice K-Means Nonuniform Clustering Algorithm
K-means based nonuniform clustering method selects the cluster heads by the probability p which is determined by the scale of the network and quantity of cluster heads. Twice K-means based clustering algorithm is applied in the whole network. n hierarchical areas are divided according to the hops from the cluster heads to the destination node. Existing clusters will be split into a number of subclusters by certain rules. K-means clustering algorithm is used for locally twice optimization in each area so that the nonhierarchical topology is formed. It has good characteristics as follows. (1) The complexity of K-means based nonuniform clustering algorithm is
3.4. Realization of Twice K-Means Nonuniform Clustering Algorithm
The following pseudocode shows the detailed process of realization of twice K-means nonuniform clustering algorithm. It contains two parts: k-means clustering algorithm and clusters’ splitting. First k-means clustering algorithm is carried out among the initial clusters until the optimum cluster topology is established. Then clusters’ splitting is done by the setting threshold values and finally k-means clustering algorithm is carried out again to optimize the clustering. The pseudocode is as Pseudocode 1.
(1) set the parameters (2) randomly select k nodes by the probability p as the initial clusters (3) for (4) for (5) calculate the (6) if min (7) if (8) node i→cluster j (9) m++ (10) endif (11) endif (12) endfor (13) endfor (14) for (15) for (16) calculate (17) if (18) (19) endfor (20) endfor (21) interests flooding (22) get the minimum hops to destination node (23) for (24) for (25) if (26) cluster q→ (27) endif (28) endfor (29) recycle Step (2) to (18) (30) endfor
Pseudocode 1
4. Establishment of Gradient Based Multipath Transmission Routing
4.1. Calculate Nodes’ CM and Establish the Contour Lines
4.1.1. Calculate Cluster Heads’ CM
Packets will be lost or retransmitted due to path's poor quality. This will cause more local energy consumption and serious congestion. Path quality has direct influence on the reliability of packets forwarding. The residual energy determines the survival time of the network. Therefore, the way only using hops as a criterion to evaluate the quality of routing has failed to meet the requirements of the network service quality. By selecting the hops to the destination node, residual energy and transmission delay to comprehensively evaluate the nodes’ quality, the preferred cluster heads are selected to establish the optimal transmission path. This has great significance to improve the transmission reliability.
Definition 1.
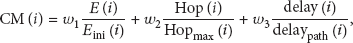
Comprehensive measurement (CM) of a node is defined to set the appropriate weighting factor to calculate CM for each cluster head according to parameters of hops to the destination nodes, residual energy, and transmission delay. The node's comprehensive measurement function is defined as
4.1.2. CM Based Contour Line among Clustering Heads
Definition 2.
All nodes’ CM values are hierarchically divided, the nodes with equal hierarchy values have similar CM values, and the connection line among the cluster heads with the same hierarchy value is defined as CM based contour line.
Each cluster head's CM is calculated by formula (1). Nodes are divided into n hierarchies
Contour lines on cluster heads.
4.2. Establishment of Multipath Gradient Routing
4.2.1. Multipath Gradient Routing
Gradient based multipath routing is an on-demand distributed routing presented to solve the issue of blind broadcasting, directed transmission, and quick establishment of multiple paths. Gradient value is used to restrict the direction of interest packets’ broadcasting and data transmission. When data are being needed to transmit, n global optimal paths are distributed established from the source node to the destination node according to the cluster heads’ CM. This strategy mainly includes the phases of topology establishment, nodes’ CM calculation, multipath routing establishment, routing maintenance, and so forth.
When the source node has packets to be transmitted, it firstly reports to its cluster head. The cluster head selects the node with the minimum distance on the next contour lines along the gradient direction as the next hop within the transmission power coverage to establish the first optimal transmission path. Then the cluster head selects one node as the next hop which is with the minimum distance on the next contour lines and within the transmission power coverage but not belonging to the established transmission paths to establish the suboptimal path. Finally multiple paths are established from the source node to the destination node as shown in Figure 3.

Gradient based multipath routing.
The detailed steps are as follows.
Step 1.
To initialize the parameters [
Step 2.
To establish the first optimal path, the cluster head selects the nearest cluster head on the contour line with
Step 3.
To establish the second suboptimal path, the cluster head selects the second nearest nodes on the contour line with
Step 4.
After establishing the necessary paths, the destination node will forward the paths’ information back to the source node along the established multiple paths and it includes nodes’ energy information, transmission delay, success rate of the data transmission, and so forth. Source node then encodes the packet by the linear erasure coding algorithm and allocates the coded fragments into multiple paths by load balance mechanism.
Step 5.
In the time interval
4.2.2. Maintenance of the Multipath Gradient Routing
After the establishment of multiple transmission paths and packets transmission, the node will go into a dormant state and wait for the next event trigger by the MAC layer protocol control. Maintenance of the multipath gradient routing includes two main parts: error reporting and routing repair. Routing error report means that the node sends the error report to the source node and requests a repair when a fault node or invalid link is detected in the routing. If the former node of the fault node or link decides to make a repair, it will launch the routing repair process. The node firstly stores the received packets and then selects the node on the next contour line and not belonging to other routing as the next hop to reestablish the routing. Furthermore, it sends the routing requests message to the destination node. The repair work finished when the destination node receives and replies to the request. Finally, the packets in the cache queue are forwarded along this newly established path.
Multipath gradient routing has the performance of fault tolerance. For example,
4.2.3. Characteristics of the Gradient Multipath Routing
( 1) High Transmission Reliability and Fault Tolerance. Multipath gradient routing, established in a dynamic distributed way, forwards the coded fragments along multiple paths so that it can avoid data loss caused by failures of a node or link. Decoding transmission mechanism can tolerate a certain amount of data loss. By allocating more fragments to the optimal path for transmission, load balance mechanism can reduce packet loss rate and improve the receiving rate of coded fragments at the destination node and the success rate of the source packet transmission.
(2) Load Balance and High Efficiency of Energy Consumption. Parameters of node's hops, energy consumption, and transmission delay are comprehensively considered when establishing the multipath gradient routing. All nodes in a cluster are repeatedly selected as the cluster head when the energy consumption reaches a certain threshold. The coded fragments are to be allocated to multiple disjoint paths. When the data is finished transmitting to the destination node along multipaths or the residual energy of any cluster head reaches the set threshold, the network will calculate the nodes’ CM and establish the contour lines and the multiple transmission paths to the destination again. With this optimization it can prolong the network lifetime.
(3) Low Complexity and Low Transmission Delay. The multipath gradient routing with load balance mechanism has lower computational complexity. Each node only stores neighbor nodes’ CM and it can establish multipath routing in a distributed way, not needing to store the global information of the nodes or paths. Computational complexity mainly reflects in establishing the topology and multipath gradient routing. The computation of K-means based nonuniform hierarchical clustering routing is lower owing to its establishment according to CM in a distributed way. Multipath routing with load balance mechanism can lower the transmission delay. During the time
4.2.4. Realization of Multipath Gradient Routing Algorithm
The following pseudocode shows the establishment process of multipath gradient routing. It is based on the clustering topology. In the algorithm, it firstly calculates the CM of cluster head and establishes the contour lines. Then it establishes multiple gradient transmission paths according to the multipath establishing rules. After this, it sends the interest packets, evaluates the quality of paths, and establishes the maintenance mechanism of multipath gradient routing. The pseudocode is as Pseudocode 2.
(1) set the parameters (2) for (3) calculate CM by the formula (1) (4) calculate (5) endfor (6) if packets (node i)→destination (7) for (8) for (9) if node (10) if G(node m) = (11) establish path( (12) endif (13) endif (14) endfor (15) endfor (16) interests(Source→Destination) (17) evaluate the quality of paths by (18) packets(Destination→Source)
Pseudocode 2
4.3. Mathematical Model and Performance Analysis
4.3.1. Mechanism of Linear Erasure Coding
Assume that

Multipath transmission model.
Figure 4 shows the multipath transmission model.
4.3.2. Success Rate of Packet Transmission
Transmission reliability of network can be evaluated by the success rate of data transmission. In the model it is defined as rate of coded fragments received at the destination node and all coded fragments needed being transmitted at the source node.
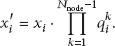
Success rate of data transmission for the jth link on
For the above definition of success rate of data transmission, success rate of data transmission for the ith path from the source node to the destination node can be deduced as follows:
Quantity of received coded fragments at the destination node for
According to (5), for calculating the success rate of data transmission, quantity of coded fragments received at the destination node should be gotten. For the whole network, quantity of total received coded fragments at the destination node is
Success rate of data transmission in the model is
If the received packets can be reconstructed into source packets, it has
4.3.3. Load Balance Mechanism
Due to the restrained resources of calculation and transmission, all encoded fragments at the source node should not be transmitted on each established path. If not, this will lead to a large number of redundant packets transmission in the network and consume more energy. Transmission delay will occur due to packets collision. Furthermore, it does not need too much redundant packets to reconstruct the source data at the destination node. Too much redundant packets will also cause great resources waste of decoding calculation and the storage of destination node. Therefore, multipath based load balance mechanism should be adopted. Different quantity of encoded fragments at the destination node is allocated to paths with different quality to transmit.
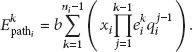
Firstly, it is to normalize each path's success rate of data transmission
The quantity of coded fragments received at the destination node is
Lemma 3.
The quantity of coded fragments received at the destination node by the load balance mechanism is equal to or greater than it, not by the load balance mechanism; namely,
Proof.
When When
let
If and only if
and when
4.3.4. Efficiency of Energy Consumption
Assume that energy consumption is
Energy consumption vector of the unit byte is
Packet loss exists during the transmission by load balance mechanism. The energy consumption of data transmission of the kth link on
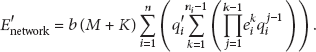
Energy consumption of transmitting
Energy consumption of transmitting
Energy consumption of data transmission of the kth link on
Energy consumption of transmitting
Energy consumption of transmitting
Therefore, energy consumption of successful transmitted fragments, respectively, by load balance mechanism and not by it is defined as
Lemma 4.
The energy efficiency of the network by load balance mechanism is higher than not by it; namely
Proof.
Suppose energy consumption of unit byte's transmission of each link on one path is equal; namely,
4.3.5. Transmission Delay
The delay usually refers to the time interval from the moment that the source packet is begun to send the at the source node to the moment that it is received successfully at the destination node; it mainly includes producing delay, queuing delay, transmitting delay, and sending delay; namely,
Assume that the time interval t is needed at each node when unit packet Ω is transmitted; thus the transmission delay of the allocated packets on the ith path is
Thus the transmission delay of the whole network is
The transmission delay of the same quantity of packets in single-path transmission mode is
5. Simulation and Analysis
Assumptions. (1) Network node is static and each node's location is known; (2) the initial state of the nodes is equal; each has the same parameters and initial energy; (3) the network node is in full duplex work mode; (4) the nodes are randomly and uniformly distributed in the rectangular area.
The simulation is based on PC with processor i3-2100 and 4G RAM as well as Matlab simulation scenario. In the simulation, 150 nodes are randomly deployed in the area
5.1. Network Topology
The clustering topology, nodes’ comprehensive measurement, and contour lines are simulated in this section.
Figure 5 shows the random distribution of the nodes. 150 nodes are randomly deployed in the area

Random distribution of the network nodes.

Clustering mode based on once K-means algorithm.
Figure 7 shows the clustering mode based on twice K-means cluster splitting and optimization. In order to form the hierarchical clustering topology, it does the cluster division on the clusters which has higher CM and does the second round K-means algorithm based clustering after the first round clustering. Simulation shows that cluster splitting is carried out on the clusters which are near to the destination node. Finally smaller scale and larger quantity of clusters are formed in this area. As a result, clusters being near to the destination node have fewer nodes. The clusters which are far from the destination node have more quantity of nodes.

Clustering mode based on twice K-means clustering.
Figure 8 shows the contour lines which are established among the cluster heads. After calculations of cluster heads’ CM, all nodes’ CM values are hierarchically divided. The nodes with equal hierarchy values have similar CM values according the rules presented above. Now hierarchies of all cluster heads’ CM (comprehensive measurements) are determined. CM based contour lines are established to connect the cluster heads with the same hierarchy values which are marked in red color. From Figure 8, it finally forms 10 contour lines. These contour lines have different hierarchical values and prepare for establishing the multiple transmission paths.

Contour lines among cluster heads.
5.2. Characteristics of the Data Transmission
Packet reception rate and accuracy are adopted to reflect the characteristics of data transmission. This is closely related to the link quality and performance of fault tolerance. Packet reception rate and accuracy can reflect the link quality and performance of fault tolerance. Packet receiving rate is defined as the quantity ratio of received packets and source packets. The higher the packet receiving rate is, the lower the packets lose in the transmission process and the better the quality of the links is. Simulation of the packet receiving rate is shown in Figure 9.

Comparison of the receiving rate of transmission packets.
Figure 9 shows comparison of the receiving rate of transmission packets. Now it gives the ratio of the received packets and all source packets when the network runs at 1000–2000 times. The presented algorithm in the study and FGS keep a high data receiving rate in
Data accuracy is defined as the quantity ratio of the received packet that can be reconstructed into source data and the source packets. It reflects the accuracy of data decoding and reconstruction, the simulation is shown in Figure 10.

Comparison of the accuracy rate of transmission data.
Figure 10 shows the comparison of the packets accuracy rate in the packets transmission among the presented algorithm, FGS and DD routing. It shows that data accuracy rate is higher than the data receiving rate at the same network operation times, because the data decoding transmission mechanism allows certain coded packets loss and does not affect the reconstruction into the source packet. This means that it still has higher data accuracy rate even if some coded packets are lost. The accuracy rate of the transmission data varies steadily and keeps within [0.95, 1] along with the network operation. The accuracy rate of the presented method and FGS keeps higher which is within [0.98, 1] when the network runs at 1000–2000 times. The presented algorithm has superior performance in data accuracy.
5.3. Performance of Energy Consumption and Load Balance
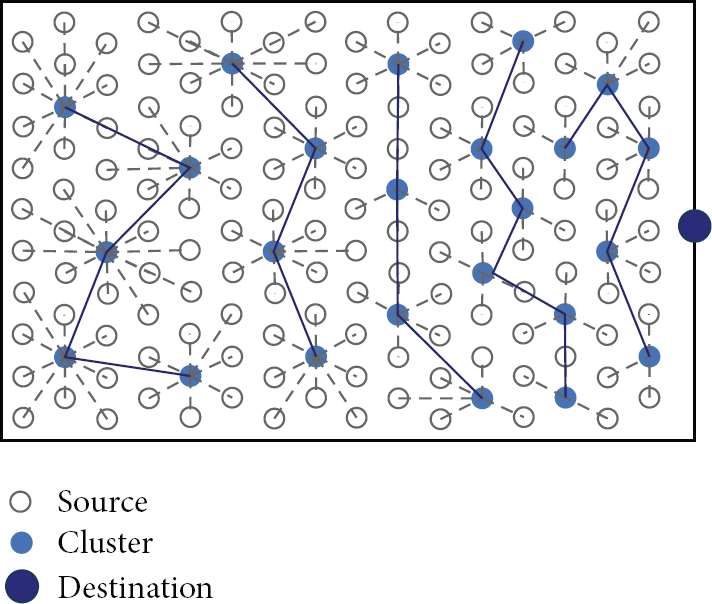
Energy consumption model of data transmission is adopted from [24, 25]. The balance of energy consumption refers to that the residual energy keeps at the similar level during each operation time.
In Figure 11, the part in red, green, and blue, respectively, presents the residual energy when network runs at 600, 1000, and 1400 times. It can be concluded that the residual energy keeps at the similar level during three randomly selected times. For example, the residual energy varies within

Residual energy when the network is running at 600, 1000, and 1400 times.
Figure 12 shows comparison of average residual energy of all the nodes, including the cluster heads and cluster members, on the contour lines 1, 4, and 7 which are selected randomly when the network runs at 1000–2000 times. From Figure 12, the average residual energy of the nodes on three contour lines is almost the same. When the network runs at 1800 times, the residual energy on contour line 1 declines obviously. From this point, it reflects good performance in the balance of nodes’ energy consumption.
Comparison of average residual energy of three randomly selected contour lines.
6. Conclusions
The stability and reliability of transmission are much important to the performance of wireless sensor networks. The failures of nodes or links will lower the transmission reliability and increase the transmission delay and energy consumption. The multipath gradient based reliable transmission strategy with fault tolerance presented in this study mainly includes establishing the nonuniform clustering topology based on twice K-means algorithm, calculating the cluster heads’ CM and contour lines, and establishing multiple gradient based disjoint transmission paths. The balance mechanism based on the multipath transmission is also studied so that the encoded fragments are allocated and forwarded along multiple paths. The encoded fragments are decoded and reconstructed into the source data to realize fault tolerance in transmission. Mathematical model is established to analyze and evaluate the performance of the network. Simulations show that the gradient based multipath routing with load balance mechanism has fast effective clustering topology and distributed multipath establishment. Gradient based routing can lower the complexity of the multipath routing establishment and energy consumption. The algorithm improves the success rate of the coded fragments, the accuracy of the source packet, and efficiency of the energy consumption. Finally it improves performance of fault tolerance and reliability of data transmission.
Footnotes
Conflict of Interests
The authors state that they ensure the scientificalness and independence of the study in the forms of paper which has no conflict of interests with other teams or schemes. Authors in the paper have no conflict of interests among them. Activities related to the paper including reviewing and evaluating will not be affected by the factors such as interpersonal relationships, economic interests, and professional preferences.
Acknowledgments
This work was supported by National Science and Technology Major Projects of China (no. 2009ZX07528-003-09 and no. 2011BAJ03B13), Specialized Research Fund for the Doctoral Program of Higher Education of China (no. 20100191110037), Chongqing Key Project of Science and Technology of China (no. CSCT2010AA2036 and no. cstc2012gg-yyjs40008), Science and Technology Project of Chongqing City Board of Education Committee (KJ131117), Wanzhou Science and Technology Planning Projects of China (no. 201203037 and