Abstract
We propose forwarding-function (
1. Background
Underwater acoustic sensor networks (UASNs), as a subclass of wireless sensor networks (WSNs), are specifically used for monitoring purposes in aqueous environment. The acoustic wireless sensors along with sink(s), distributed under water, constitute the basic body of UASN, where acoustic sensors gather the information of interest and then following a routing strategy forward these data to the end station. WHOI Micro-Modem [1] and Crossbow Mica2 [2] are among the commercially available sensors for underwater environments. Sink is generally supposed to have no power constraint, whereas the acoustic sensors are equipped with limited battery power. These networks provide diversified range of applications like pollution monitoring, ocean current detection, submarine discovery, deep sea explorations, and seabed management.
Due to the nature of aqueous environment, improving energy efficiency at routing layer is a challenging task. Moreover, as there are major differences between terrestrial and underwater conditions, hence the basic concepts of terrestrial routing can not be implemented in UWSNs. To tackle these problems, researchers exercise the role of low speed acoustic signals for aqueous communication and sea navigation systems, leading to high propagation delay and transmission losses. High shipping activity, thermal noise, and turbulent noise also increase the error rate. Authors in [3] design the underwater acoustic channel to descriptively analyze the total noise density and path loss. On the other hand [4], it investigates diverse routing architectures for 2-dimensional and 3-dimensional UWSNs. Fundamental analyses of aqueous conditions show that reactive routing is more challenging than the proactive one. Battery replacement and efficient routing are among the solutions to overcome the power constrained problem of acoustic sensors; however, the leading solution is not practical; thereby, we focus on the lagging one.
The two major categories of underwater routing protocols are localization-based and localization-free. The fundamental difference between these two is the awareness of location by the sensor nodes. Localization-free protocols are also termed as flooding based schemes, where nodes are only aware about their depth. On the other hand, location-based protocols assume that the sensor nodes are location aware. In literature, both localization-based and localization-free schemes are available: QELAR [5], R-ERP2R [6], EEDBR [7], and MPT [8]. These protocols attempt to tackle high transmission delay, path loss, and receiving energy consumption. However, deficiencies do exist. Depth Based Routing (DBR) protocol [9] is based on depth of sensor nodes as the trivial parameter in flooding-based forwarding schemes. EEDBR [7] improves the deficiencies of DBR by considering residual energy while selecting data forwarder(s). R-ERP2R [6] is another magnificent depth-based routing scheme, which implements “ETX” routing metric for improving energy efficiency. QELAR [5] designs routing architecture and cross-layer approach on the basis of Q-machine learning, thereby improving localization-based routing. MPT [8] employs power-controlled and source-initiated transmission by examining the deficiencies at the physical layer in UASNs, specifically to deal with on-demand applications. H2-DAB [10] achieves the minimum delay and higher network lifetime by using hop count as routing metric. It also employs courier nodes to provide adaptability for time-critical and data-sensitive applications.
There is always a need of less complex and highly reliable communication scheme in WSNs and UWSNs. Liu et al. [11] improve reliability in transmissions by proposing a network coding based cooperative communications scheme (NCCC). It provides a scalable implementation of NCCC by selecting coding vectors from finite field. Localization schemes for sensor nodes are not so accurate in UWSN, as in WSN. In WSN, mobile beacon assisted localization is used.
In [12], the authors propose Z-curve, which is a path planing mechanism for mobile beacons to localize the sensor nodes. Zou et al. [13] develop a generic algorithm to control the movement of autonomous underwater vehicles (AUVs) in UWSN by gathering network information from sensor nodes. Limited residual energy is one of the main challenges for sensor nodes in UWSN. High numbers of (re)transmissions and collisions cause consumption of energy. In [14], the authors tackle the issue by proposing contention-free multichannel MAC protocol for UWSNs.
Another technique has been proposed by [15] in which authors design spatially fair MAC (SFMAC) protocol for UWSNs. It avoids the collisions with postponing clear-to-send (CTS) for a specific duration as calculated by the receiver node. Mobility of the target object is always an issue for WSN. Furthermore, it is very difficult to update the location information of the target object by sensor nodes. In [16]; the authors suggest an accurate target tracking scheme for WSNs. They achieve energy efficiency in the scheme by minimizing the missing rate of an object.
MUAP in [17] examines the acoustic channel as well as its losses and then proposes an energy model for the computation of channel losses in aqueous environment. Stojanovic [18] carefully examines the association between transmission distance and channel capacity in underwater communication. CEDC [19] uses doppler compensation model to improve the scrutinizing of acoustic signals and present a high data-rate communication model. In dense underwater conditions, PULRP [20] provides a cross-layer model as well as a descriptive algorithm to maximize network's throughput. This model is localization-free technique with efficient energy consumption model. AMCTD [21] exploits the adaptive mobility of courier nodes to maximize the network lifetime. It computes the holding time on the basis of weight function to cope with the problems of high transmission loss and low network lifetime. The work presented in this paper is the extension of [21].
2. Motivation and Contribution
By examining the flooding as well as depth-based routing protocols, we compensate for the deficiencies in these schemes. In DBR and EEDBR, stability period quickly ends due to unnecessary data forwarding and high load on low-depth nodes. Another main deficiency of these protocols is a sharp instability period due to the quick energy consumption of medium-depth nodes. In AMCTD, the high transmission loss is due to distant transmissions of medium-depth nodes. AMCTD is not suitable for data-sensitive applications, especially during instability period due to the mobility pattern of courier nodes. The consideration of only two parameters, depth and residual energy, is not sufficient for global load balancing throughout the network lifetime.
We investigate the problems of medium-depth nodes in the earlier rounds like high end-to-end delay and transmission loss, low stability period, and fast energy consumption. Based on these, we optimize the movement of courier nodes in sparse conditions for load balancing. Although AMCTD's performance is better than DBR and EEDBR, respectively; however, deficiencies do exist. We try to overcome the deficiencies as follows.
In iAMCTD, the efficient movement of courier nodes minimizes end-to-end delay and decreases the energy consumption of low-depth nodes in sparse conditions. The Implementation of threshold-optimized data forwarding is resourceful process for on-demand routing and removes forwarding of unnecessary data in the network. Optimized mobility pattern of sink, in later rounds, maintains end-to-end delay of the network, especially for delay-sensitive applications even in sparse conditions. We examine nodes' depth and control overhead at physical layer as well as network layer and propose a model which caters for the major acoustic problems.
We consider arbitrary deployment of nodes in 3D aqueous environment. The network consists of sensor nodes, courier nodes, multiple sinks, and onshore data centers. Sensor nodes and courier nodes communicate with low-range acoustic modems, whereas sinks (equipped with both RF and acoustic modems) communicate with onshore data centers and sensor nodes. Upon the detection of physical environmental attributes, the sensor nodes transmit the sensed data to either of the in-range node or sink. Courier nodes are equipped with mechanical modules for movement control; however, these can only relay the network data towards sink. After collecting threshold-based data, sensor nodes transfer the data to sink, as soon as possible, either by direct transmission or through courier nodes; otherwise they broadcast the data towards their neighbors. Nodes communicate with each other using low-range commercial acoustic modems. In flooding-based techniques, control packets' transmission is the requirement of network in order to achieve better management with the varying network density. The multiple-sink model is proficient at balancing the network load and it has been analyzed in [22–24].
3. The Proposed iAMCTD
We divide operation of the proposed iAMCTD into the following four phases:
network initialization and underwater channel model, implementation of on-demand data routing, data forwarding phase, adaptive mobility patterns of courier nodes.
The first phase deals with nodes' deployment, network initialization, and thorp's model [18] for path loss and noise density calculation in aqueous environment. Second phase discusses implementation of on-demand data routing to facilitate the time-sensitive and critical-data applications. Third phase expresses the data forwarding along with the variations in depth thresholds for sensor nodes to cope with varying network density. We develop efficient forwarding functions for optimal data forwarding in aqueous environment. We also discuss the data packet structure and the tradeoff between control overhead and network lifetime. On the basis of control packets, sink identifies the network density and manages the network specifications and mobility of courier nodes. Last phase uses mixed integer linear programming (MILP) to analyze adaptive mobility patterns of courier nodes and their multiple cases.
3.1. Network Initialization and Underwater Channel Model
We assume that sensor nodes broadcast the data using flooding-based approach. As each neighbor of the node receives data of the sender node, courier nodes devise their sojourn tour at the start of the network and then start collecting data from the source nodes. These also report the network density information to sinks in order to devise mobility patterns and depth-threshold variations. During knowledge acquisition, nodes share the depth and residual energy information among themselves. As the network initiates, courier nodes remain at equal horizontal distances from each other and these start vertical movement towards the bottom.
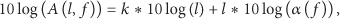
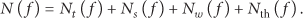
Given below channel model is used to calculate spreading loss and total noise loss in underwater acoustics. We calculate the total attenuation of signal on the bases of spreading loss [3] and thorps model for signal absorption loss. At a given frequency f, the channel model calculates absorption loss
Accordingly, all tunable parameters are given in
The flooding-based approaches employ receiver-based data forwarding due to un-awareness of location. Each node shares depth information with other nodes and the eligible neighbors for forwarding are decided on the basis of depth threshold. The neighbor nodes compute the forwarding functions by considering channel losses, residual energy, and depth differences.
3.2. Implementation of On-Demand Data Routing
The proposed protocol performs on-demand data routing as the nodes react immediately to sudden and drastic changes considering the value of sensed attribute. Figure 1 depicts the transmission algorithm for threshold-based data.

Routing of on-demand data.
Where V is the current sensed value,
3.3. Data Forwarding Phase
The sensor nodes send sensed data to in-range courier node(s). Upon reception, the courier node(s) acknowledge the sender node(s) to reduce further flooding. In the absence of courier nodes, sensor node sends data towards their neighbor nodes. Each sensor node calculates holding time for received packet on the basis of forwarding function. In order to avoid packet collisions, all nodes maintain a timer to send threshold-based sensitive data. Nodes sense packets buffer and maintain priority queue to avoid transmission of same data and to forward packets on the basis of holding time. Thus, the end-to-end delay of critical data decreases, increasing network's feasibility for time sensitive applications. The sensor nodes, after every 100 rounds, transmit control packets for the computation of network density at the sink, which is further utilized to manage the variation in the mobility patterns of courier nodes and depth-thresholds. The data packet format of our technique is shown in Figure 2 which consists of sender ID, packet sequence number, depth information, and payload.
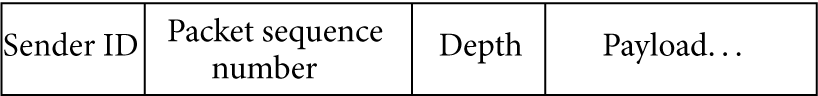
Data packet format.
The trade-off between control overhead and network lifetime is a serious consideration in the design of flooding-based routing techniques, so we attempt to control this trade-off by employing minimal overhead.
3.3.1. Variation in Depth Threshold
In preceding depth-based schemes, nonvarying depth-threshold is another key reason of flooding in dense situations. It is also due to the absence of eligible neighbors in sparse conditions specifically during instability period, which causes the loss of critical data. Therefore, we implement variations in depth-threshold of nodes according to network density. The three optimal values for depth thresholds are

Variations in depth threshold.
With a network of 225 nodes and each nodes' range 100 m, we assume the values of
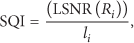
3.3.2. Forwarding Function Computation
In this section, we analytically model the optimal value selection for

Analytical model for data forwarding.
Where,
In medium-depth region, load on nodes is high due to frequent data forwarding, so the ECF grants the significance of residual energy of nodes to attain global load balancing in the network. In last region, we formulate DDF to accomplish distant forwarding and minimum flooding scenarios. The formulae for these functions and holding time
where

Mechanism of data transmission in iAMCTD.
In receiver-based forwarding, multiple nodes choose the optimal forwarder between themselves. It is also important to decrease the flooding mechanism during forwarding. Multiple transmissions of same data cause higher average energy consumption by the network than by other interferences. So, it is necessary to cope with it. A simple algorithm for data forwarding using
3.4. Adaptive Mobility Patterns of Courier Nodes
Courier nodes are highly resourceful in stabilizing network condition as these collect data from sensor nodes by their adaptive mobility. After network initialization, courier nodes start their movement towards the bottom of network along with collecting data from the nodes in their vicinity. Thus, reduce the load on medium-depth nodes by acting as a relay(s) and then receive data from high-depth nodes, an efficient approach for time-critical applications. Furthermore, courier nodes change the mobility pattern as network density (controlled by BS) varies. These nodes maintain the depth and vertical movement by using mechanical module [10].
3.4.1. Aggregate Traffic Model for Mobile Courier Nodes
We propose Aggregate-Traffic-Model (ATM) and formulate the objective functions to achieve higher throughput by utilizing adaptive mobility patterns of courier nodes.
In the proposed mobility pattern, we are interested in maximizing the total information flow towards the sink by all courier nodes, that is,
Equation ((11)) defines the objective function: maximize the total information flow towards the sink. Equation ((12)) ensures that the total information flow towards sink from courier node y will not surpass the sum of information flows of all couriers nodes towards sink. Equation ((13)) describes that

Adaptive mobility pattern in dense and sparse conditions.
Figure 6 illustrates the two specific mobility patterns of courier nodes. They also provide support to nodes with no neighbors in the later rounds, which efficiently deals with instability period. After receiving packets in each round, they broadcast the received packet sequence number(s) to reduce flooding.
Figure 6 shows that if the number of alive nodes is greater than
4. Performance Evaluation
To evaluate the performance of iAMCTD, we compare it with the selected existing schemes with the extensive simulations. Following multiple-sink model of conventional methods, we randomly deploy 225 nodes in the network field along with 4 courier nodes. We assume
The proposed and the existing protocols are evaluated in terms of the following performance metrics.
Network lifetime: duration between network initialization and complete energy exhaustion of all the nodes. Average energy consumption: it is the average energy consumption of all active nodes in one round. End-to-end delay: it is the duration for a packet to be transmitted from source to destination. Number of dead nodes: it shows the number of nodes having no energy. Transmission loss: it shows the average transmission loss (dB) between source node and sink in one round.
Figure 7 illustrates that our scheme improves the stability period of network by avoiding the forwarding of unnecessary data along with maintaining lower transmission loss. It reduces end-to-end delay by utilizing LSNR and DDF in extreme low-depth and high-depth regions, thus providing flexibility for delay-sensitive applications in UWSN. In iAMCTD, the instability period starts from almost 9000th round, after which the transmission loss (Figure 11) remains even; however, end-to-end delay (Figure 12) decreases very slowly.

Number of alive nodes in iAMCTD, AMCTD, EEDBR, and DBR.
Due to prioritization of SQI in the upper region, load balancing is achieved. Moreover, the load on medium-depth nodes is shared because of the adaptive movement of courier nodes. After the expiry of initial nodes, the network destabilizes due to diminution of eligible neighbors. In EEDBR, the stability period is greater than DBR; however, the network energy consumption is greater. In DBR, the stability period is lesser than the other techniques as it considers only depth of forwarding nodes as the ultimate determining factor; however, the instability period is much better than EEDBR as there is gradual increase in network energy consumption. When the network becomes sparse, number of neighbors decreases quickly causing network instability. In AMCTD, there are only two forwarding selection attributes; depth and residual energy. This consideration causes a trade-off between the network lifetime and transmission loss which is not suitable for reactive applications. The load on high-depth nodes becomes low due to the existence of courier nodes in stability period causing load balancing in AMCTD. During the instability period of AMCTD, network gradually becomes sparse causing load on high residual-energy nodes, whereas the number of neighbors is managed by variations in depth threshold. Lifetime of iAMCTD is increased due to lower throughput by responsive network. Moreover, it provides minimum transmission loss and delay which is specifically suitable for time-decisive applications such as pollution monitoring.
In our suggested scheme, employment of Thorp's energy model specifies the detailed channel losses, which are useful for selective data forwarding in responsive networks. Increase in stability period also confirms reduction in redundant transmissions.
Figure 8 shows the comparison of dead nodes in iAMCTD, AMCTD, EEDBR, and DBR. The confidence interval of results verifies that iAMCTD has almost 5000 more rounds of stability period than AMCTD due to better

Number of dead nodes in iAMCTD, AMCTD, EEDBR, and DBR.
To balance load on nodes, iAMCTD selects forwarders on the bases of SNR, depth, and depth differences. Thus, preventing the creation of coverage holes which is to converse the previous techniques. Main reason behind better stability period is the implementation of efficient
Figure 9 shows that iAMCTD consumes almost constant energy throughout the network lifetime as compared to the selected protocols. This is due to the implementation of well organized

Total energy consumption in iAMCTD, AMCTD, EEDBR, and DBR.
Figure 10 portrays throughput comparison of iAMCTD, AMCTD, EEDBR, and DBR. The throughput of iAMCTD demonstrates the amount of threshold-optimized data for responsive networks, as the proposed protocol avoids unnecessary data transmission, thereby leading to lower throughput. However, it ensures minimal transmission loss and end-to-end delay while delivering data. Previous schemes send unnecessary data along with high propagation losses; the throughput decreases sharply due to quick fall in network density. In our protocol, throughput steadily decreases due to maintenance of network density and low energy consumption.

Comparison of network throughput in iAMCTD, AMCTD, EEDBR, and DBR.
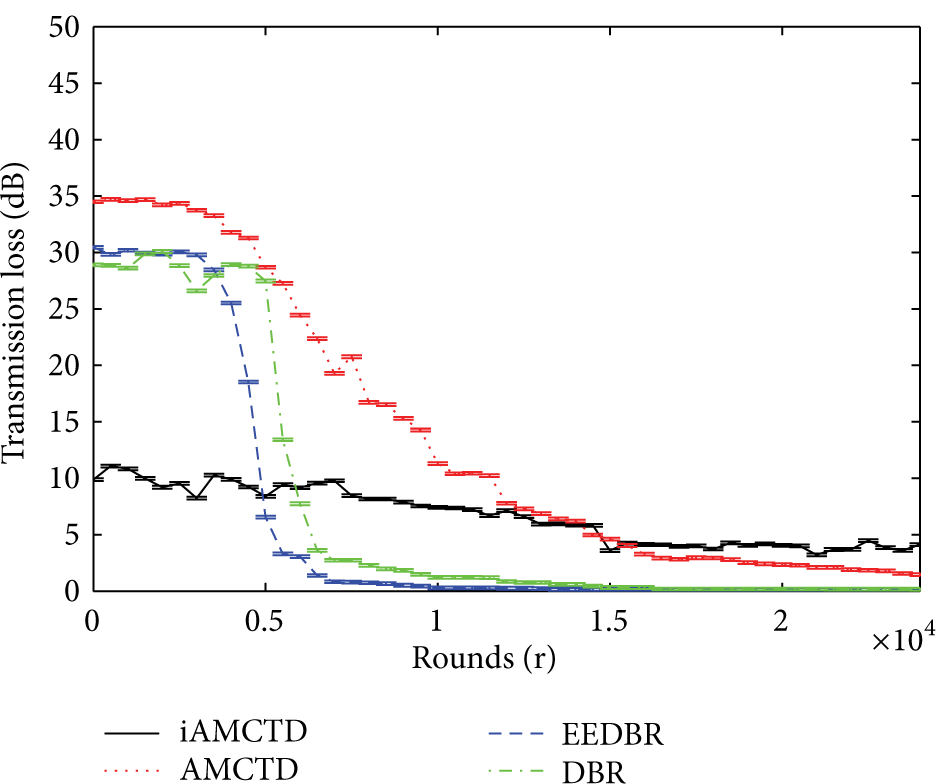
Comparison of transmission loss (dB) in iAMCTD, AMCTD, EEDBR, and DBR.

End-to-end delay in iAMCTD, AMCTD, EEDBR, and DBR.
The throughput of DBR and EEDBR declines very quickly, which is unsuitable for both delay-tolerant and delay-sensitive applications. AMCTD performs better than the previous schemes in instability period, but our scheme outperforms AMCTD due to less time lag in data delivery, thus validating its better performance in flooding-based protocols.
Figure 11 shows that transmission loss of the network in iAMCTD is much less than the previous techniques due to prioritization of SNR in calculations of
In our proposed scheme, transmission loss is one of the key factors concerning the significance of data-sensitive responsive networks. The
Figure 12 shows that end-to-end delay of network in iAMCTD is less than the previous techniques due to minimum forwarding distances between the nodes in both dense and sparse conditions. The delay in DBR suddenly increases because of sharp energy depletion of medium-depth nodes. However, in EEDBR higher delay is caused due to prioritization of residual energy. In DBR, delay is much higher in initial rounds due to distant data forwarding. It decreases gradually with the sparseness of the network, after about 5000 rounds. In EEDBR, delay increases whenever the network becomes scattered causing data forwarding at minimum distance. End-to-end delay in AMCTD is better than previous techniques as both threshold variations and weight functions perform global load balancing. In our technique, there is a minimum possible time lag due to consideration of signal quality and depth differences between sender and receiver nodes. It is more suitable for delay-sensitive applications specifically in on-demand routing.
5. Conclusion and Future Work
In this paper, we have proposed iAMCTD routing protocol to maximize the lifetime of reactive UWSNs. Amendments in
As for future directions, we intend to design mathematical analysis of courier nodes' mobility. We are also interested in performing detailed analysis of the acoustic channel model to devise further routing metrics for optimal data forwarding.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.