Abstract
The mobile wireless sensor network (MWSN) is a new style WSN with mobile sinks or sensors in the network. MWSN has advantages over static WSN in the aspect of better energy efficiency, improved coverage, and superior channel capacity. However, mobile nodes also bring some security problems. For example, it is difficult to ensure secure communications among the mobile nodes and static nodes. In this paper, we design a lightweight mobile reauthentication protocol for mobile nodes. The designed protocol provides forward secure pairwise key for the mobile node when it moves from one cluster to another. Thus, the mobile sensor node can be authenticated by the new cluster head, and the privacy of his origin area is protected. In addition, the security and performance analysis shows that our scheme meets the need of lower communication and computation overhead, while achieving security requirement for mobile sensor node application in MWSN.
1. Introduction
WSN has become more and more prospective in human life with the development of hardware and communication technologies. However, due to the static network style, there are some natural limitations of WSN, such as network connectivity and network lifetime [1–4]. Furthermore, more and more researches find that the mobility in WSN not only improves the overall network lifetime and the data capacity of the network, but also addresses delay and latency problems [5–9]. There are many researches on how to realize better energy efficiency, improve coverage, enhance target tracking, and cause superior channel capacity for MWSN. However, limited researches consider the issue caused by the mobile sensor nodes, such as credibility with low consumption overhead and secure communication in MWSN. While more and more application scenarios require mobile sensors in WSN, such as traffic detection, animal observation E-Health, and battlefield. Furthermore, some present researches begin to consider the mobile adversary [10], which brings new security problems. Therefore, we should pay attention to realize the mutual authentication between the mobile node and the cluster efficiently, generate the new pairwise key, and make sure of the security of data transmission.
The framework of MWNS is given as in Figure 1.
The network considers four types of entities: base station—as usual, the base station is assumed to be absolutely secure, which has
plenty bandwidth, energy, storage space, and computation capability; cluster head—cluster head is assumed to have more storage space, energy, communication
range, and computation capability than sensor node, and notice that, in general, the communication
range of cluster head is also larger than the sensor node; static sensor node—we consider static sensor nodes in our network model, since they can
work for the cluster head, and relay for mobile sensor node which has smaller communication range
than cluster head, and in general, we assume that it has limited storage space, energy, and
communication range; mobile sensor node—the mobility is the only difference between the mobile sensor node and
the static sensor node, and the mobile sensor node roams from one cluster to another cluster and
communicates with the nodes in the cluster.

The framework of MWSN.
Based on the framework of MWSN, some security problems are brought by the mobility of mobile
sensor node. One problem is the identity authentication of mobile sensor node in the new cluster.
The other is the new session key generated between mobile sensor node and new cluster to ensure
security communication. Moreover, we should protect the privacy of the mobile sensor node which
means attackers cannot track it. Therefore, the security requirements of MWSN are given as follows:
the authentication of identity—making sure that the identities of both parties who
generate the key are trusted; data integrity—ensuring that only authorized person can modify the transmission of
information; message privacy—transferring data can only be read by authorized parties; key freshness: ensuring that the existing session key is only used at current stage; node Resiliency—the network recovers when some nodes are captured by malicious
attackers; privacy-preserving—since the mobile sensor node roams in WSN, attackers cannot track the
mobile sensor node; scalability—allowing revoking and joining nodes. With the expanding of the network scale,
it has little effect on the storage space of nodes and communication consumption.
In this paper, we focus on the security requirements caused by mobile sensor nodes. For the mobile sensor node in MWSN, we present an efficient node reauthentication and key generation scheme for mobile sensor nodes which consumes less communication and computation overhead and protects the privacy of the mobile sensor node. The security and performance analysis shows that our re-authentication scheme for mobile sensor node cannot only efficiently realize the secure requirements for MWSN, but also suit for the limited resource WSN.
The rest of this paper is organized as follows. In Section 2, we introduce the related work. We present our protocol in Section 3. Section 4 gives the security analysis of re-authentication protocol. Section 5 gives the performance analysis and simulation. Finally, we conclude the paper in Section 6.
2. Related Work
We introduce our related work from three aspects: the lightweight authentication schemes for WSN, the research of mobile sink in MWSN, and the re-authentication schemes for the mobile sensor node in MWSN.
The demand of lightweight is mostly considered in sensor network. All nodes in sensor network are
considered to be static initially. For example, Perrig et al. [11] proposed a typical authentication scheme named
μTESLA (Timed Efficient Stream Loss-Tolerant Authentication) by using the
one-way hash chain. The protocol publishes the authentication key
The advantages of mobile sink in MWSN have attracted much attention. Zhang et al. [14] proposed several efficient schemes to restrict the privilege of a mobile sink without impeding its capability of carrying out authorized operations for an assigned task. To prevent the authenticator from revealing information due to mobile sink compromises, the privileges of the authenticator are restricted by adding parameters, such as the starting time and the ending time of a task, the type of a task, and ID of the mobile sink. Vieira et al. [15] proposed a bioinspired location service named Phero-Trail location service protocol. In Phero-Trail, location information is stored in a 2D upper hull of a Sensor Equipped Aquatic Swarm, and a mobile sink uses its trajectory projected to the 2D hull to maintain location information. This enables mobile sensors to efficiently locate a mobile sink. The results show that Phero-Trail performs better than existing approaches. Agrawal et al. [16] proposed a key update protocol which securely updates the session key between a pair of nodes with the help of random inputs in mobile sensor networks. The security analysis shows that the proposed protocol resists known-key, impersonation, replay, worm, and sink hole attacks, while also provides forward secrecy, key freshness, and key control.
Recently the security of mobile sensor nodes in WSN has been paid more and more attention. Han and Kim [17] proposed the re-authentication issue concerning mobile nodes moving among sink nodes. The scheme considers the sink in the home cluster as a trusted third party. It prestores authentication information in all surrounding neighbor clusters and transfers the credible information to the new sink. The communication and computation overhead of re-authentication is reduced through credible trust. Qiu et al. [18] considered a sensor node roaming within a very large and distributed wireless sensor network, such as the application of healthcare field, in which the sensor nodes are deployed in the patient's body. When a dynamic sensor node moves to new area and wants to attack a router or a cluster head in this area, it first sends a request message to the base station. After verifying validity of the request message, the base station generates the session key for mobile node and the router and sends it to the router, and then the router sends the material of session key to the mobile node to generate the session key. Qiu also improves the E-G scheme to guarantee that two sensor nodes share at least one key with probability 1 with less storage and energy overhead. The disadvantages of Han's scheme are as follows. First, it only takes the mobile node, sink node, and base station into consideration. Then, the communication overhead of the program mostly concentrates on the mobile node, so it has influence on the lifetime of the mobile node. Lastly, the re-authentication material is prestored in the neighbor clusters, which exists unnecessary communication overhead and information leak. In Qiu's scheme, the base-station is always online and provides the full utilities. The re-authentication also depends on the base station which incurs large communication overhead.
3. The Proposed Protocol
With the mobility of MWSN, the mobile sensor nodes may move from one cluster to another. If we repeat the new nodes addition process proposed in [4], the scheme will degrade to the E-G [19] scheme. Besides, some predistribution schemes need to interrupt the operation of network and implemented by man, which is unrealistic for the running wireless network. Therefore, the roaming behavior of mobile sensor nodes must consider how to get trust from the new cluster and generate the pair-wise key to achieve security communication. Considering the security requirements caused by mobile sensor nodes in the MWSN, we design our re-authentication protocol as follows. For convenience, we assume that after the static WSN generated the communication keys for the entities, the mobile sensor nodes join the network from some clusters.
As Figure 2 shows, the whole process can be
divided into two phrases. Phrase 1 the mobile sensor node
Notation.


The re-authentication of mobile sensor node.
3.1. Predistribution for Mobile Sensor Node
Before roaming in the network,
3.2. Mobile Sensor Node Reauthentication
After registering at the base station and trusted joining When When Upon Receiving the message 2, the home cluster After receiving the message 3, Upon receiving the message 4 from
After generating the session key, 
1: Verify 2: 3: Compute 4: 5: Compute 6: 7: Compute 8: 9: 10:
1: Verify 2: 3: Compute 4: 5: Extract 6: Generate random number as formula (1). 7: Compute 8: Compute 9: 10:
1: Verify 2: 3: Compute 4: Compute 5: Compute 6: 7: 8: 9:

Re-authentication of mobile sensor nodes.
For convenience, the role of home cluster is acted by the foreign cluster node through which the
mobile sensor nodes have completed the re-authentication process. That means that after
Taking the issue of tracking and protecting the privacy of 
Notice that since
4. Protocol Security Analysis
4.1. The Protocol Satisfies Forward Security
Suppose that the attacker gets the session key
4.2. Mutual Identity Authentication
In our scheme, as there is no shared information between
4.3. Prevent Man-in-the-Middle Attack
From the analysis of our scheme, an attacker can track or intercept message 1 to
act the mobile sensor node
4.4. Prevent Replay Attack
When the mobile node
4.5. Protect the Privacy of the Mobile Node
Since the communication of mobile sensor node uses the pseudonyms, attackers and other entities
cannot distinguish them which protects the privacy of the mobile sensor node. But to the base
station and cluster heads, they can track the mobile sensor node. After the mobile node joins the
foreign cluster, the cluster head sends the
5. Protocol Performance Analysis
We give the performance analysis of our scheme in this section in terms of communication pass, message size, and computation overhead. We also give the simulation of our scheme on the NS2 simulation platform and use the time delay to reflect the efficiency of our scheme.
5.1. Communication Pass
We compared the required number of communication passes with Han's [17] and Qiu's [18] schemes, since both of them propose the reauthentication protocols for mobile sensor
nodes in WSN. Table 2 shows the comparison of
communication passes for mobile node reauthentication, where n denotes the number
of hops from
The required number of communication passes.

Since Han's and our schemes use the relation among cluster heads to realize
re-authentication for mobile sensor node, which do not need communication with the base station, in
Qiu's scheme, when the node joins a new sink, it first sends the requirement message to the
base station. Actually, the message is first sent to the foreign cluster head (n
hops) and then to the base station via the foreign cluster (l hops) which incurs
large communication overhead. The hole communication passes are (
Although the re-authentication of Han's scheme does not need communication with the base station, he pre-stores the authentication information in all surrounding neighbor cluster heads which are related with the number of neighbor cluster (m hops), while our scheme realizes the re-authentication by the tradition tripartite authentication, which results in less communication pass.
5.2. Message Size
The message size during the re-authentication process is quantified by the byte which is to show the communication overhead. We compare the message size with Han's. We use the base parameter setting of message as Han's [17] in Table 3.
The base parameter setting of message.
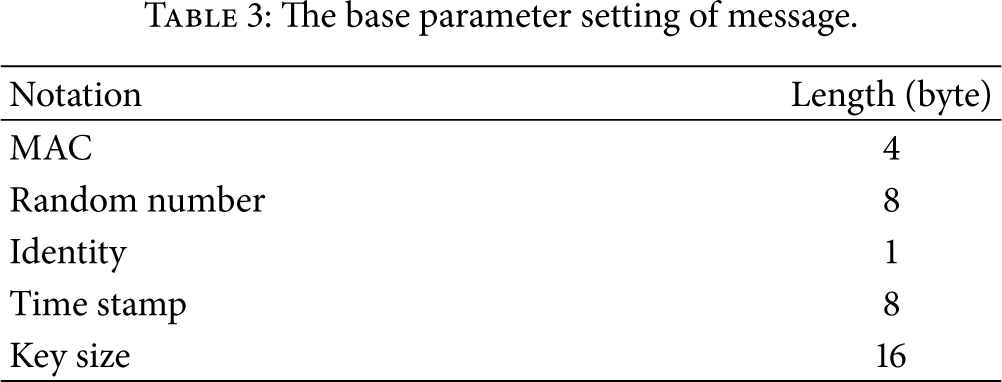
From Table 4, we can see that our scheme has less message size of the whole re-authentication process. Notice that Han pre-stores authentication information in all surrounding neighbor clusters and we only consider that the number of authentication material of transmission size is 36 bytes, while the actual number may be more than 36.
The required message size for re-authentication (byte).
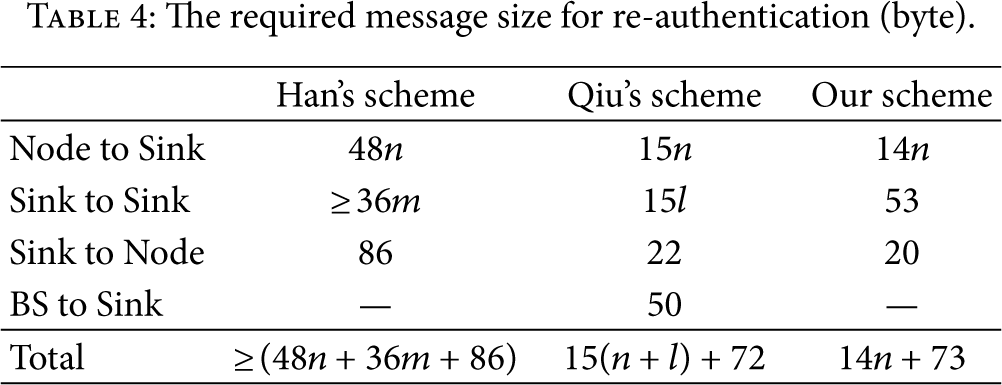
During re-authentication for mobile sensor node, we reduce the message length transmission among the entities since the data transmission consumes much more energy than computation in WSN.
5.3. Computation Overhead
Computation overhead is quantified by the number of execution encryption algorithm. As Table 5 shows, the total number of encryption/decryption of our scheme is the same as Han's, both more than Qiu's scheme. Since the re-authentication of Qiu's scheme is based on the base station, our scheme and Han's scheme are based on the relation among clusters.
The required message size for re-authentication.

5.4. Protocol Simulation
We use NS2.29 to simulate our scheme and Han’ scheme [17], since both of them realize mobile node re-authentication without requiring communication with the base station. We use the transmission delay to quantify the message size, which can reveal the availability and efficiency of our scheme. The simulation uses the mesh network topology, MAC layer uses the 802.15.4 protocol written by Zheng and Lee [22] for NS2, the routing layer uses the AODV routing protocol which has the shortest hops, the transportation layer uses the UDP protocol, and the application layer transmits the CBR packet. The message size is set as Table 4. The data transmission speed is 250 KB/S, which adopts the recommended beacon mode standard setting in reference [22].
Supposing the communication radius of the mobile sensor node and the common sensor nodes within the cluster to be 20 m, the communication radius of cluster head is 100 m. The computation delay of message 1 and message 4 in mobile sensor node is 6 ms and 3 ms [23], respectively, while the computation delay of message 2 and message 3 node is 1 ms for cluster head.
To reflect the comparison of Table 4, we design two groups of simulation for our scheme and Han's scheme [17]. The number of each group simulation is 100 times.
In Figure 4,
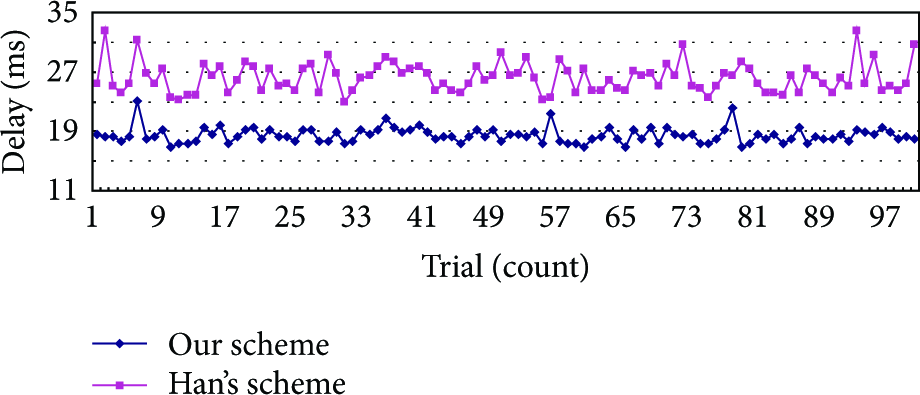
The time delay for
In Figure 5,
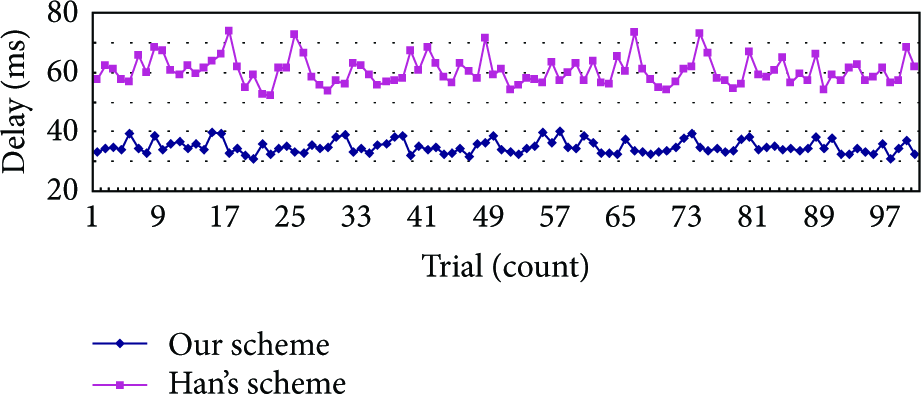
The time delay for
6. Conclusion
The security problem brought by the mobile sensors in MWSN attracts more and more attention of researchers. In this paper, we propose a re-authentication protocol for the mobile node roaming among clusters. Our protocol can transfer the credibility among the clusters which can efficiently achieve the requirements of secure identity authentication and establish the forward secure pairwise key. Meanwhile, the base station can track the mobile trajectory and protect the privacy of the mobile sensor node. We also give performance analysis and simulation for our re-authentication protocol. The results and comparison show that our protocol achieves better security and has better performance on communication overhead, message size, and computation cost.
Footnotes
Acknowledgments
This work was supported by the National Natural Science Foundation of China under Grant 61202474 and the Natural Science Foundation of Jiangsu Province under Grant BK2011464.
