Abstract
Body area network (BAN) is an emerging branch of wireless sensor networks for personalized applications in many fields, such as health monitoring. The services in BAN usually have a high requirement on security, especially for the medical diagnosis, which involves private information. With limitations of power and computation capabilities, one of the main challenges to ensure security in BAN is how to generate or distribute a shared key between nodes for lightweight symmetric cryptography. The current research almost exploits the randomness and distinctiveness (characteristics) of physiological signals to solve the key generation problem. However, it needs the help of additional hardware support and has the constraint on positions deployment, to acquire vital signals, which will bring the high cost and hardness to implementation of real system. To avoid the above problems, this paper presents a novel key generation scheme and a key distribution protocol, both of which are only based on wireless modules equipped on sensors. By exploiting the high correlation of received signal strength index (RSSI) between peer-to-peer communications, our scheme can provide a shared symmetric cryptographic key under the presence of an eavesdropper. We conduct experiments on the real Telosb nodes, and the results demonstrate that our proposed methods have a good performance on security.
1. Introduction
With the aged tendency of global population, people pay more attention to the healthcare requirements. Due to the advances of wireless communication and medical sensing technologies, many researchers focus on the applications of body area network (BAN), which can provide individual healthcare services. BANs consist of small and intelligent wireless medical sensors, worn or implanted in the human bodies, to sample vital physiological signals and send the records to a basestation (usually a portable device such as PDA or mobile phone) for real-time analysis or remote diagnosis. When a disaster or ailment comes up, BANs could offer an emergency response. Recently, some BAN platforms have been put into market. Fujitsu has developed inductively powered ring sensor [1], which works in conjunction with Fujitsu's developing sensor network system to tie into a healthcare monitoring of patients application for Apple's iPhone. Shimmer [2] has designed a wearable sensor platform to monitor a subject's EMG, ECG, and GSR. Due to the strong privacy and liability concerns of health data, these devices and communications between them need to be secured. “Lack of adequate security features may not only lead to a breach of patient privacy, but also potentially allow adversaries to compromise patient safety by modifying actual data resulting in wrong diagnosis and treatment [3].”
Given limited power and computation capabilities of BAN, asymmetric cryptography is not suitable. The only left option is symmetric encryption, which however has a significant challenge in dynamically sharing a secret key between devices (both sensors and base station). There are two traditional approaches to address the problem: predeployment or a key management infrastructure (a trusted third party), written in IEEE 802.15.6 standard for body area networks [4]. As to predeployment, if the initial key is preconfigured in hardware by manufactures, sensors from different companies could not work together. When using something like SD card or USB stick instead, stick may be cracked. Some predeployment techniques for key distribution such as [5] will lead to network reconfiguration when new nodes join. Towards key management infrastructure, a trusted third party which stores the keys is seldom present in BAN scenarios. Even though a trusted third party exists, it still carries the risk of compromise and associated liability. In some instances, Diffie-Hellman (DH) and its variants [6] such as ECDH (Elliptic Curve Diffie-Hellman) have been used for key exchange. However, based on computational security, they are not cost effective for resource-constrained sensors [7].
In order to overcome the limitations mentioned above, an information-theoretical secure solution has been developed, which is based upon the distinct subjective property from environment that nodes can observe. Since the environment around human body is dynamic and complex, physiological signals are quite unique at a given time. Therefore, the idea using physiological signals for securing intersensor communications was first introduced by Cherukuri et al. [8]. Motivated by this initial idea, [9–12] exploited interpulse interval (IPI) to generate cryptographic keys. Though physiological signals measured from different areas of the body have high correlation, these signals do not possess the exact same values [3]. Consequently, when symbols in the keys get reordered, different values could be produced by translational and rotational errors [13]. To avoid the errors, [3] used physiological signals to facilitate key agreement instead of generating keys. Nevertheless, nodes in the same BAN need to measure the same physiological signals, which unavoidably lead to an additional hardware cost and restrained deployed positions (ECG needs to be measured near cardiovascular).
The above difficulties are real challenges faced by researchers attempting to find another subjective property. Recent works such as [14, 15] have indicated that wireless channel could be the next common property to share a secret. In wireless environment, multipath is a basic character, which brings in a rapid decorrelation with distance. Therefore, the wireless channel between two nodes, Alice and Bob, can produce a special mapping between transmitted and received signals for a shared secret key agreement. Based on the dependence from position and motion, the channel can not be inferred by an eavesdropper, Eve, who is more than half of wavelength away from both Alice and Bob. Obviously, BAN could easily satisfy the condition of location and movement because of human activity. Considering resource-constrained condition, BAN requires periodic reasonably key renewal with a minimum hardware and software overhead. Exiting channel property based key-sharing solutions are established to extract secret keys at a high rate with high bit mismatch rate or generate secret keys at a low rate with acceptable bit mismatch rate. The former needs reconciliation phase to exchange the mismatch information, which consumes resources. The latter is not time effective. It is challenging to optimize two metrics at the same time and balance the trade-off between them.
In this paper, we propose wavelet-transform trend-based key extraction (WTKE) scheme and fuzzy vault based key distribution (FVKD) protocol, which use the received signal strength (RSS) variations for a pairwise key agreement to secure BAN communications. WTKE exploits wavelet transform for more accurate trend to achieve a lower bit mismatch rate than previous work, and it also has an acceptable secret key rate. FVKD, which combines channel property features and fuzzy vault [13] together, could distribute a secret key derived by one end of communication link to the other end. Through experiments, we validate its cost is less than that of DH and ECDH.
The rest of the paper is organized as follows. Section 2 briefly introduces some fundamentals of our paper. Section 3 is devoted to the basic aspects of our key generation scheme WTKE, experimental results, and analysis. Section 4 elaborates on fuzzy vault based key distribution protocol FVKD and further analyses security and performance. Section 5 generally introduces the related work. In Section 6, we come to the conclusion and discuss some possible future directions.
2. Preliminary
In this section, we will introduce channel models in BAN, the fundamentals of key agreement based on channel property, wavelet transform, and fuzzy vault.
2.1. Channel Model in Body Area Network
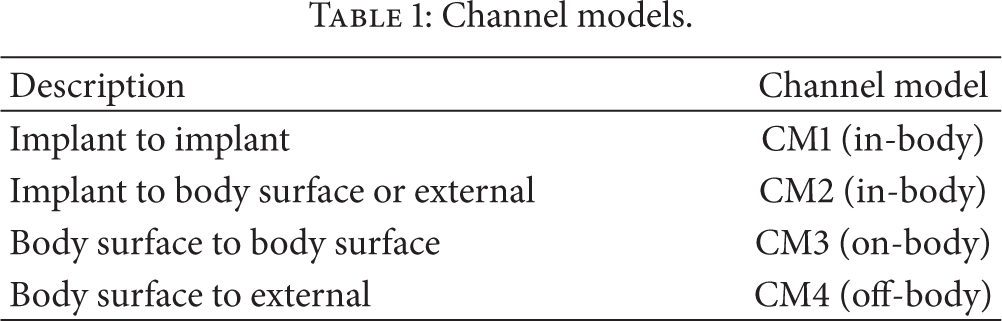
As sensors' positions are on or inside the body, the BAN channel models need to consider the impact of human body and activities. In [16], IEEE 802.15.6 group defines 3 types of nodes as follows: (1) implant node: a node that is placed inside the human body; (2) Body surface node: a node that is placed on the surface of the human skin or at most 2 centimeters away; (3) external node: a node that is not in contact with human skin. Based on the different node types, [16] gives 4 channel models (CM) shown in Table 1. In this paper, with the hardware constraints, we focus on the latter two channel models (on-body and off-body).
Channel models.
2.2. Key Generation Based on Channel Property
There are three reasons why channel is regarded as secret information.
Reciprocity of electromagnetic propagation: as wireless channel is symmetric, the multipath characters of the radio channel (gains, phase shifts, polarisation distortions, and delays), which Alice and Bob can get from the received signal, are identical. Temporal variations in the radio channel: The motion by either Alice, Bob, or other objects in the environment near the link would make the channel change over time. Evidently, the security mechanism can reap the full benefit of the randomness resulting from channel variations. Spatial variations: the radio channel depends on the location of Alice and Bob. Only if another node Eve is more than half a wavelength away from both of them, she will get a different channel.
Therefore, we can take the wireless channel as a time- and space-varying filter. The combination of channel properties (gains, phase shifts, polarisation distortions, and delays) can represent different channels uniquely. Among those channel properties, received signal strength (RSS), which can be measured by most of the off-the-shelf wireless cards, is widely used. According to [17], the on-body BAN wireless channel exhibits reciprocity. From [15], we can infer that the off-body BAN wireless channel will reveal reciprocity if mobility is brought in.
When Alice and Bob are sampling the channel with Eve locating more than half a wavelength away, the valid samples are limited by the rate of time variation. And this variation can be approximately analyzed by using the level-crossing rate (LCR): for a Rayleigh fading process, 
In (1), v is a measure of the effects of dynamic change by sensors and environment, but, as opposed to other dynamic changes, sensors' motion mostly plays a dominant role in BAN. Thus, we use relative movement velocity between two nodes to signify dynamic change here. And λ is the wavelength of the carrier wave, which can be easily gotten from (2): 
2.3. Wavelet Transform
Wavelet transform is the representation of a function by wavelets, which is mathematical functions used to divide a given function or continuous-time signal into different scale components. Wavelet transforms are classified into discrete wavelet transform (DWT) and continuous wavelet transform (CWT). Take CWT to illustrate the definition: for a given signal 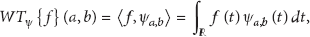
The wavelet transform is often compared with the Fourier transform, in which signals are represented as a sum of sinusoids. The main difference is that wavelets are localized in both time and frequency whereas the standard Fourier transform is only localized in frequency. In other words, wavelet transforms have advantages over traditional Fourier transforms for representing functions that have discontinuities and sharp peaks, and for accurately deconstructing and reconstructing finite, nonperiodic, and/or nonstationary signals. And the discrete wavelet transform is also less computationally complex, taking
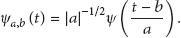
2.4. Fuzzy Vault
The fuzzy vault was first presented by [13] as a cryptographic construction where one can hide a secret (S) in a vault by using the set A. Others can get the secret only when the vault is unlocked on the condition that their set B is closed to set A (B has enough number of values in common with A). The procedure of locking is as follows. (1) Create a v degree polynomial p over the variable x; (2) Use set A as the values of x to compute the values of p and create a set
(1) (2) (3) (4) (5) (6) (7) (8) (9) (10) (11) (12)
To unlock the above vault, others use their set B to recall the specified point of set A in R. If B gets more than
(1) (2) (3) (4) (5) (6)
FVKD can map this scheme through setting the channel property obtained at the sender to set A, those obtained at the receiver to set B, and the secret key that needs to be shared to polynomial coefficients.
3. Wavelet-Transform Trend-Based Key Extraction
In this section, we will propose basic idea of wavelet-transform trend-based key extraction, analyze the security of the scheme, and evaluate the performance of the scheme using real collected data.
3.1. Scheme Description
As shown in Figure 1, the complete process is divided into the following steps.

Flow chart of key extraction.
3.1.1. Sampling
First, both Alice and Bob should obtain common information based on RSS value. Alice sends a probe message periodically for Bob to get RSS values, and after Bob receives message, he sends back probe message as soon as possible for Alice to sample the channel. As a result, Alice and Bob get related almost-exact values, respectively. The sample process lasts for a fixed duration at a specific rate to get enough samples, and all of samples must be obtained on the condition that channel is changing to keep the reciprocity as described in Section 2.
3.1.2. Wavelet Analysis
As a number of factors such as random noise, asymmetrical interference, transceiver differences, and half-duplex communication bring in some mismatches between the original RSS readings of both sides, but they have the same fading trend. In order to accurately evaluate the trend, we use wavelet transform. Through wavelet transform, signal is decomposed into multiresolution levels; thus the corresponding detail and approximation signals are obtained. At the same level, approximation signal represents the low frequency part, and detail signal shows the high frequency part. Clearly, we can use approximation signal to get the same trend. There are many mother wavelet functions for different purposes or signals. Here we use Haar wavelet because of its advantage for the analysis of signals with sudden transitions. In addition, we choose 4-level wavelet transform, and the reasons are given in the following experiments and performance evaluation.
3.1.3. Quantization
Through Haar wavelet transform, signal will have sudden changes. We can therefore detect those changes and make binary quantization. For an RSS measurement 
3.2. Experiments
We conduct our experiments in typical indoor environments. Our experiments were divided into two parts. In scenario 1, we verify our scheme through on-body channel by using two sensors in the same BAN. In this situation, sensors provide real time service, so sensors need to probe the channel frequently. In scenario 2, we exploit sensor-to-basestation communications to test our scheme on off-body channel, and sensors on the body keep a low-data-rate communication with basestation. For this reason, we can use the scheduled communication to measure RSS value.
In the existing hardware system, the RSS values are reported as integers through wireless card, but different products from different companies calculate RSS values with deviations. “For example, Atheros devices report RSS values from −35 dBm to −95 dBm, Symbol de-vices report RSS values from −50 dBm to −100 dBm, in 10 dB steps, and Cisco devices report RSS values in the range −10 dBm to −113 dBm [15].” To avoid the impact of different manufactures, we use products from the same corporation.
Our experiments used Telosb nodes running TinyOS and operating in the 2.4 GHz band. With logarithmic units, their radio antennas (CC2420) can measure signal power and output a received signal strength indicator (RSSI). Our setup is listed in Table 2. For scenario 1, Alice and Bob are mounted on the body (here we take them in hand), shown in Figure 2(a). And Alice transmits a probe packet every 40 ms, and Bob sends message back once he receives the packet. For scenario 2, Alice is still a body-worn node, but the probe interval is changed to 80 milliseconds. The basestation 1 (Bob, shown in Figure 2(b)) still replies an acknowledgement immediately after he receives the packet. The settings above allow the two endpoints of the communication link to sample the channel alternately in quick succession to ensure the high reciprocity between their measurements.
Experimental setup.

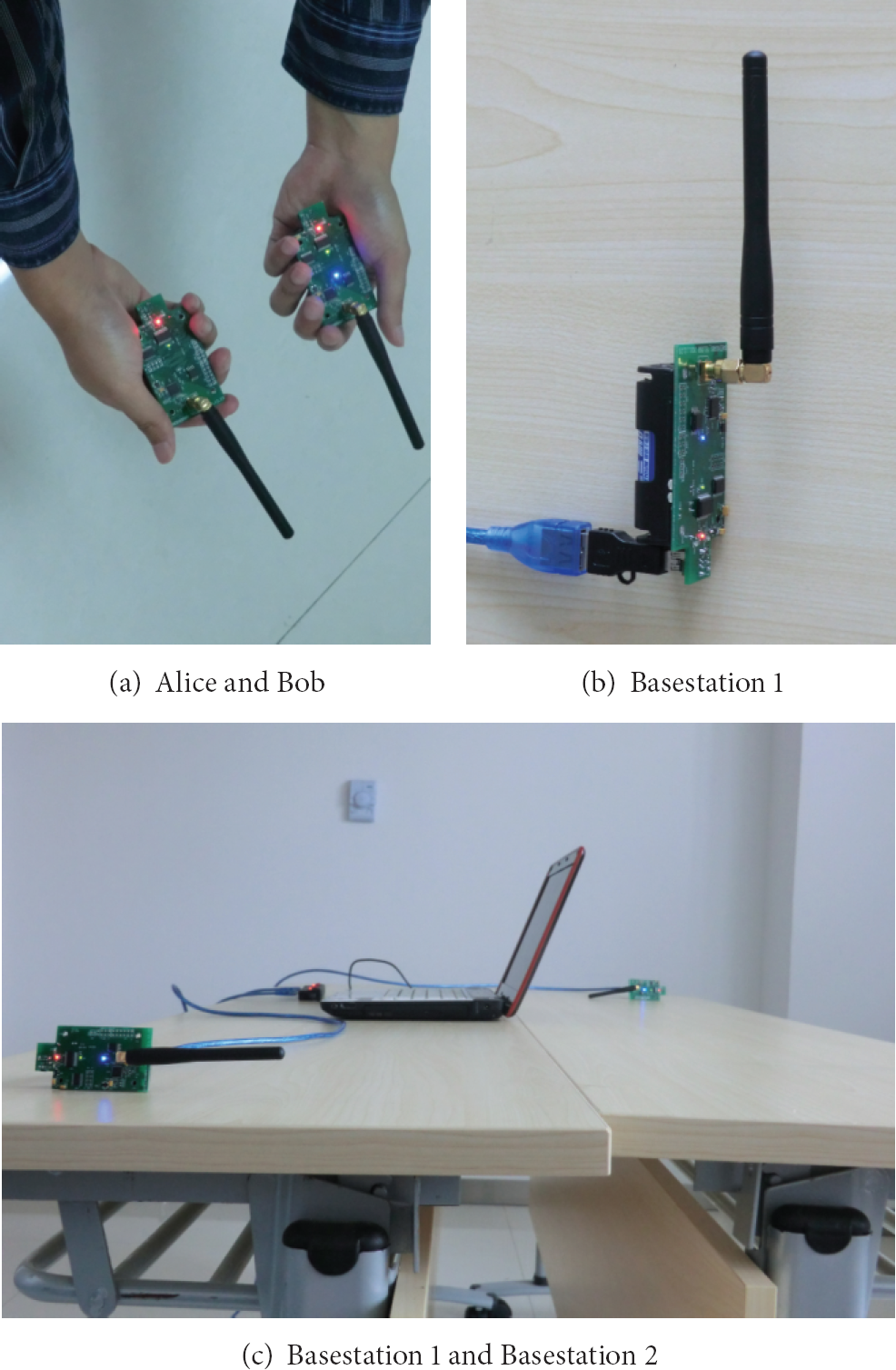
Mobile node and basestations.
The layout of our indoor environment experiments is depicted in Figure 3 showing the location of the basestations (as shown in Figure 2(c)). The room is covered by multiple WiFi networks, which may result in interference. The subject walked around the table to ensure that the channel between two parties of the link varies. In scenario 1, the on-body channel varies with arm swinging. In scenario 2, it is obvious that movement of the subject can bring in changes to the off-body channel between Alice and Bob (basestation 1). In both experiments, the subject walked and waved just as we normally do in real life.

Experimental layout for indoor environment.
For scenario 1, we show the signal strengths measured by Alice, Bob, and Eve in Figure 4. It can be obviously observed that the eavesdroppers are not able accurately to replicate the channel measurements between Alice and Bob, and it can also be noticed that Alice's and Bob's RSS values have a similar trend. As a result, the RSS measurements are the distinct information shared between Alice and Bob to generate secret key or channel features. However, we find that even though Alice' RSS values are close to Bob's, their values are not exactly the same and discrepancies may result in mismatches of secret key extraction (our channel feature generation). The discrepancies between channel properties measurements are similar to deviation between the physiological signal measurements, which reminds us of using trend- and fuzzy-based methods. The result of experiment in scenario 2 is shown in Figure 5, which seems similar to that of scenario 1. As the channel between Bob (basestation 1) and Eve (basestation 2) is almost steady, the RSS trace of Eve from Bob is not painted.
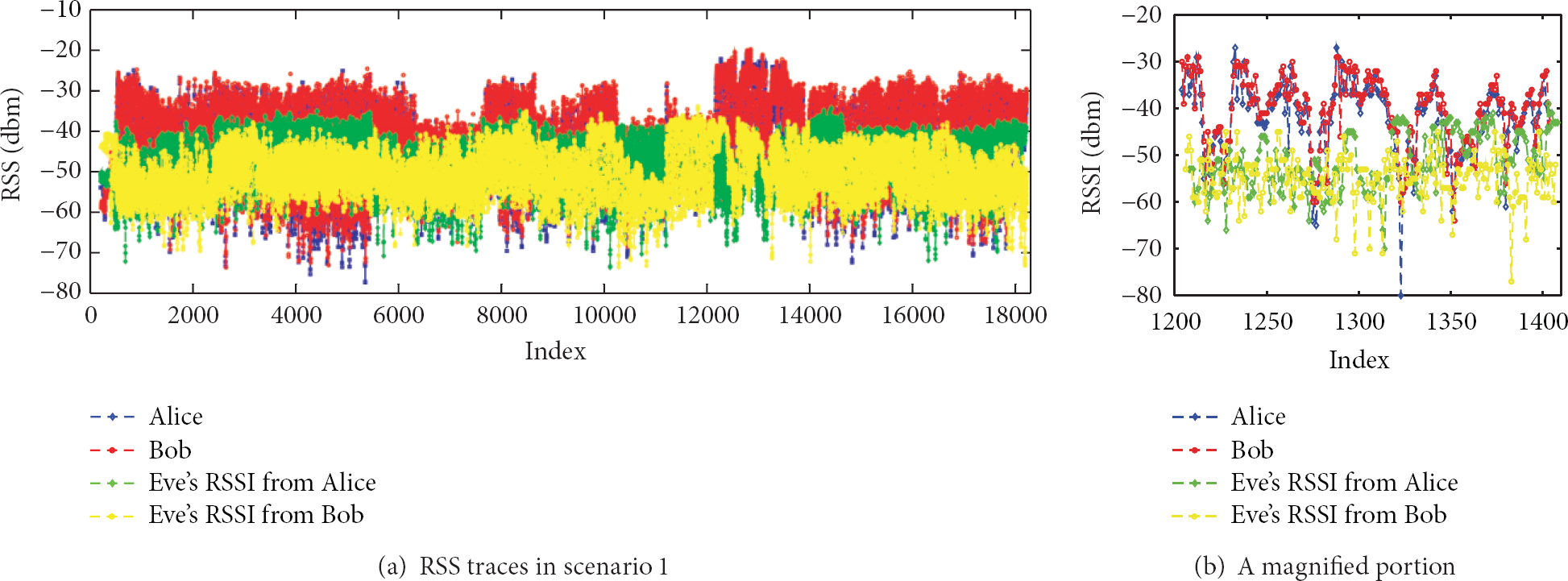
Experiments results in scenario 1.

Experiments results in scenario 2.
Figure 6 shows the autocorrelation coefficients for Alice and Bob in two scenarios. As the definition is mentioned in Section 2, the channel coherence time is about 140 ms in scenario 1 (on-body channel) and 50 ms in scenario 2 (off-body channel) based on the observations of Figures 6(a) and 6(b). We denote the link Alice to Bob as

Autocorrelation for Alice and Bob in two scenarios.

Channel gain scatter plot

Histogram of channel gain

Parts of approximation signals from Haar wavelet transform in scenario 1.
3.3. Security Analysis
For our threat model, our first assumption is the adversary Eve own unlimited computation capability. Eve can eavesdrop all the traffic between Alice and Bob and can also sample the channel at the same time when Alice and Bob measure the channel, but she only gets information about the channels between herself and either Alice or Bob. Another assumption is that Eve knows the algorithm and settings. However, Eve cannot be less than half of wavelength close to either Alice or Bob. This assumption is reasonable in BAN as human can easily detect the illegal node a few centimeters away. We do not concern the issue about authentication, for it is another distinct problem, and it should be done in the start-up phase. There are many solutions such as [24–26] to authentication. Those solutions can be used in conjunction with our scheme. Based on the measurements of our experiments, all devices generate keys by using WTKE, and the results of bit mismatch rate are shown in Figure 10. The bit mismatch rate between Eve and legitimate devices is nearly 0.5, much higher than that between legitimate devices themselves. Obviously, our key extraction scheme, fading trend-based wavelet key extraction, has the high security to generate secret key through channel properties measurements.

Bit mismatch rate for legitimate devices and Eve under different scenarios.
3.4. Performance Evaluation
It is important to ensure the randomness of a secret key. Therefore, we test our keys generated from two scenarios in the NIST test suite [27]. Because of limitation of the bit length, we only run some tests, and the results are listed in Table 3. To pass a test, the value for that test must be greater than 0.01, and our results meet the requirement.
NIST statistical test suite results.

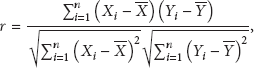
We compare our method with typical amplitude quantization scheme [14] and previous trend quantization work [28] through three performance metrics: (1) secret bit rate: the average number of secret bits extracted per second; (2) bit mismatch rate: the ratio of the number of bits that do not match between Alice and Bob (3) entropy: The entropy of a random variable X is defined as 
In [14], Mathur et al. construct a quantizer, which calculates two thresholds 
Here, μ and σ are mean and standard deviation, and α is a parameter which can be configured dynamically on the condition of
In [28], Liu et al.'s scheme contains both trend and amplitude multilevel quantization. Since WTKE is a single bit extraction scheme, we only take fading trend estimation from Liu et al.'s scheme into account. Fading trend estimation runs as follows For an RSS measurement
The performances of all three schemes in two scenarios are exhibited in Figures 11, 12, and 13. Though Liu et al.'s scheme has the highest secret bit rate, they get the highest bit mismatch rate. Our WTKE scheme is better than Mathur et al.'s scheme in both aspects of secret bit rate and bit mismatch. All the schemes produce bit streams with nearly the same high entropy. In a word, both trend-based methods are better than Mathur's amplitude-based methods. Compared to Liu's scheme, our method accurately gets the trend through wavelet analysis, which also reduces the frequency of wave change.
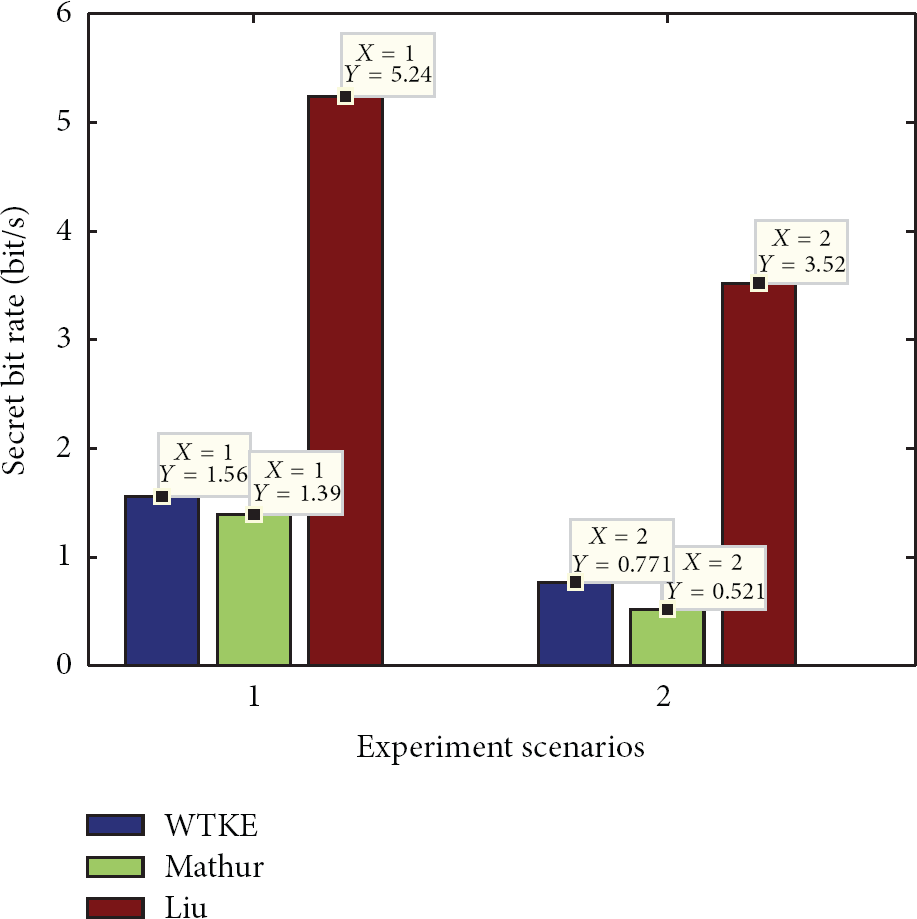
Secret bit rate comparison.

Bit mismatch rate comparison.

Entropy comparison.
Here, we present another reason why we choose 4-level Haar wavelet transform. As shown in Figure 14, the curve of secret bit rate goes down with the curve of bit mismatch. The curve of bit mismatch falls faster before 5 Level, and the curve of secret bit rate falls faster after 5 Level. In a word, it is worth sacrificing secret bit rate to reduce mismatch before 5 level.
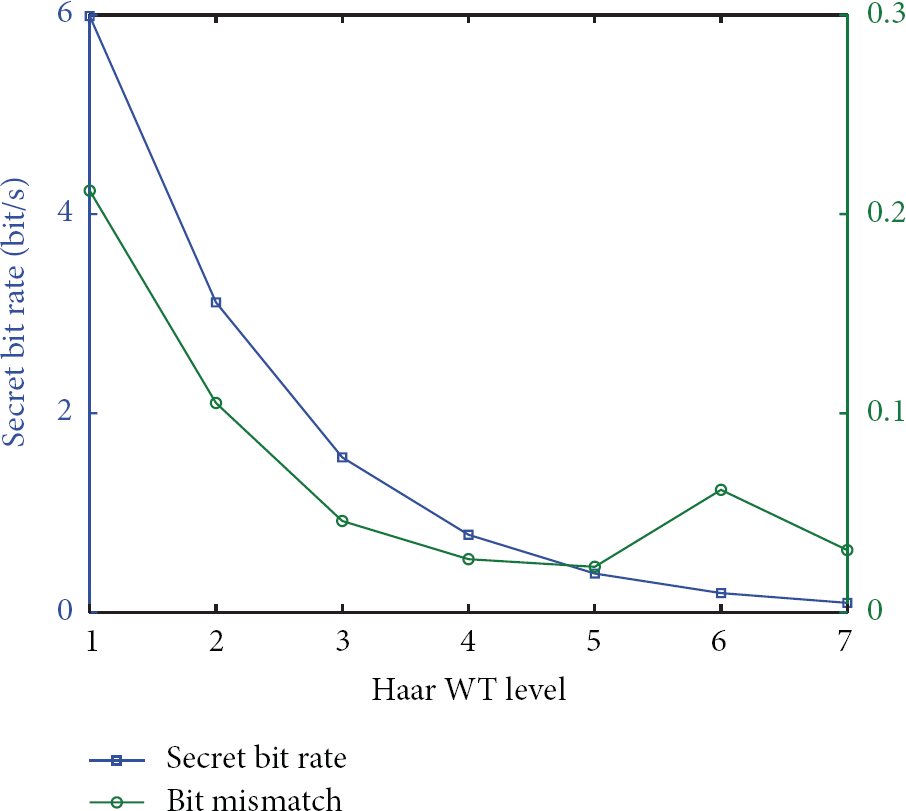
Secret key rate versus bit mismatch rate in scenario 2.
4. Fuzzy Vault Based Key Distribution
In this section, we first describe our novel key distribution protocol based on fuzzy vault. Then, we give analysis on its security and efficiency.
4.1. Protocol Description
Our key distribution protocol uses fuzzy vault to facilitate a pairwise symmetric key agreement between Alice and Bob through measuring RSS values. The protocol is as follows.
4.1.1. Channel Feature Generation
First, both Alice and Bob should obtain common information based on RSS value. Next, every 128 samples form a window, and neighboring windows have 32 overlapping samples. Using WTKE mentioned in Section 3 to process each window, we will get 8-bit binary. In order to increase the range of chaff points, 4-level Daubechies 5 wavelet transform is used to search for the fourth level detail signal's maximum point, whose position in 128 samples will be converted into 7-bit binary. For example, as shown in Figure 15, if the window contains 128 samples from index 500 to 627, the maximum points of Alice and Bob in 128 samples are both at index 518. So the position of maximum points in the window is 19 and could be converted into 0010011. Finally, the first 6 bits generated by WTKE and all 7 bits extracted by maximum point form a channel feature. A group of channel features generates a feature vector

4th level db5 detail signal.

Flow chart of channel feature generation.
4.1.2. Polynomial Choice
Alice uses a random generator to produce random numbers which is the secret key she wants to share with Bob. The length of the key is set as 128 bits here, and it could also easily be set longer. To create a vth order polynomial of the form
4.1.3. Vault Creation
Since the polynomial and feature vectors are now available, fuzzy vault is then created by computing the set
4.1.4. Vault Locking
Alice builds the vault
4.1.5. Vault Exchange
Alice then sends the vault R to Bob using the following message: Alice → Bob: IDs, Nonce, R, Par, MAC (Key,
4.1.6. Vault Unlocking
Once Bob receives the vault R, he makes parity check using Par and drops the part which does not match
4.1.7. Vault Acknowledgment
If unlocking is successful, Bob sends a message back to Alice to inform the successful unlocking. The message is described as follows: Bob → Alice: MAC (Key, Nonce|IDs|IDr). The meanings of Key, Nonce, and IDs are described in the paragraph of Vault Exchange, and IDr means the ID of Bob. After verifying the acknowledgement sent by Bob, Alice knows the key has been shared successfully. Since Bob measures the similar distinct RSS values to the measurements of Alice, only Bob can unlock the vault.
Figure 17 shows the key distribution process. This protocol provides a one-hop security by channel property, and this protocol can be easily extended to multihop end-to-end communication, where the estimates of shared channel property could be delivered as proposed in [28]. Considering the latency problem in BAN, sensors can initialize a secret key by only executing the protocol one time and then derive keys from this initialized key for ensuring the security of more communications.

Fuzzy vault based key distribution protocol.
4.2. Security Analysis
With the use of fuzzy vault, FVKD ensures that the two ends of the communication link can share a secret key though they do not have all the same features. The security of the FVKD scheme depends on the difficulty of polynomial reconstruction. We can hide the legitimate feature points among a mass of the spurious chaff points, whose values fluctuate in the same range as that of legitimate ones. An adversary, without knowledge of legitimate points, has to try out each of the

Security of the vault.
It is also hard for adversaries to know the key in the vault exchange and acknowledge phases. As mentioned in Section 3, Alice and Bob could authenticate each other by using methods in [24–26]. It is a reasonable assumption that Alice and Bob have been device paired. For this reason, the existence of ID (IDs and IDr) could be used to control access. The Nonce provides the freshness of the protocol, and the MAC is used to prevent man-in-the-middle attack.
4.3. Performance Evaluation
4.3.1. Distinctiveness
The channel properties depend on the location and relative motion of two endpoints in the link. Half wavelength (e.g., 6.25 cm of 2.4 GHz carrier frequency) is close enough for the BAN user to detect adversaries. We also conduct a series of theoretical analysis here. As to WTKE, after 4-level Haar transform, the bit mismatch probability (
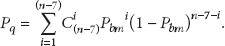
Here C is combinatorial computing. Therefore, the probability that receiver can unlock the vault is shown in Figure 19. With consideration of the time effectiveness, we set N, the size of feature vector, below 15. It means if response time of sensor is between 20 to 40 ms, the sample time is 29.44 to 58.88 s. To balance security and efficiency, we set polynomial order as 7 and the size of feature vector as 11. As shown in Figure 10, Eve's

Unlock probability.
4.3.2. Length and Randomness
The key shared between Alice and Bob is generated by Alice using a random number generator. Thus, the length and randomness of the key can ensure communication security.
4.3.3. Temporal Variance
As mentioned above, the variation of channel is quantified by the maximum Doppler frequency, and the variation follows Gaussian distribution. It can be concluded that even though adversaries know the previous values, they cannot infer the value of channel properties.
4.4. Implementation
We prototype FVKD by using Verilog HDL to evaluate its cost and performance in hardware. The Xilinx ISE software tool is used for emulating a Virtex V platform (http://www.xilinx.com). The metrics used for the evaluation are CPU clock cycles and memory footprint. Table 4 shows the details.
Computational cost and memory footprint of our prototype implementation.

Though the computational cost is composed of many tasks, only three kinds of them (feature generation, key hiding, and key unhiding) are crucial. Both sender and receiver have feature generation step. Only sender has the task of key hiding, and receiver is just responsible for key unhiding task. As key unhiding needs more computations than key hiding, receiver runs more cycles. We set a 25 MHz clock, so it would only take a few milliseconds to execute our protocol. And the cost could be amortized in the sampling phase. Since other than generating features, the sampling phases can computerize and transmit some chaff points in the meantime. The memory foot print values are primarily determined by chaff points (2000, 13-bit x-values, and 23-bit y-values), features (13-bit values), and polynomial projections (23-bit values). Compared to our protocol, DH takes more than 320,000 cycles and its variant ECDH takes more than 100,000 cycles, though they consume less memory footprint.
5. Related Work
There has been increasing research on utilizing wireless channel properties to extract secret keys. This approach is based on the theory of [14, 31, 32], and it suggests that a secret key agreement is possible for two parties to achieve through using correlated random variables of channel in the presence of an eavesdropper. Till now, several channel properties such as signal phase, time delay, angle of arrival, and received signal strength (RSS) have been proposed, among which phase difference is firstly proposed in [31]. It measures differential phase of two-tone signal to generate secret keys. Further research is done by using phase difference to improve the efficiency of key establishment in [33]. The impulse response of a wireless channel is estimated from WiFi signals in [14]. And in [22], statistics of the angle-of-arrival (AOA) is used on the condition that AP needs a programmable phased array antenna.
RSS is widely used due to the fact that it can be easily collected through most off-the-shelf radio devices. As to RSS-based methods, some works focus on temporal and spatial variations such as [14, 15, 34, 35]. In [36–38], some other factors like multiple antenna diversity and multiple frequencies are also taken into account. In [14], the authors develop a lossy quantization to extract key bits from a statistical Gaussian channel. And they supply theoretical certification and validate this mechanism in indoor environment. In [15], Jana et al. extend this approach to measure RSS over a single channel in various environments using laptops. And a multibit quantization method is also proposed to improve secret bit rate with privacy amplification. In [35], the authors use a transform to decorrelate secret key bits for a very high bit generation rate (40 bits/s).
Although BAN is a newly emerging wireless sensor network, there is still research already done on this topic. In [39], the authors examine the near-body radio channel for key generation based on simulation modeling. Body-worn scenarios such as patient mobility, different placement of devices on the body, and different modes of motion are considered in [40]. To avoid reconciliation phase in key generation, the authors analyze the reasons of measurement asymmetries and then use Savitzky Golay filter to improve signal correlation [21]. In [38], channel hopping is used to solve the problem of little dynamic channel change that exists, which means the channel coherence time period is too large.
Different from the above works, we use waveform trend and feature to promote key agreement by using wavelet transform and fuzzy vault.
6. Conclusion
This paper presents two main research findings: a key extraction scheme and a secure key distribution protocol for BAN. On the basis of the high correlation in RSS measurements between two communication parties, wavelet analysis and fuzzy vault are utilized in this paper. With the assumption of enough motions in BAN, a secret key can be shared between two sensors, and the key can also be shared between a sensor and a basestation, even though an eavesdropper is present. This paper analyzes the security and performance of the scheme and protocol, and it turns out that WTKE provides a secure key with low mismatch rate, high entropy and acceptable secret key rate. FVKD meets the requirements of key agreement (randomness, distinctiveness, and temporal variance).
There are some problems this paper does not fully explore. For instance, the channel coherence time period lasts longer than node's response time. We would take measures to adjust the channel coherence time in our future research.
Footnotes
Acknowledgments
This research was supported by National Basic Research Program of China (973 Program) under Grant no. 2011CB302702 and National 863 Program of China under Grant no. 2011AA010305.
