Abstract
Secret sharing is an important aspect of key management in wireless ad hoc and sensor networks. In this paper, we define a new secure model of secret sharing, use the Lagrange interpolation and the bilinear cyclic groups to construct an efficient publicly verifiable secret sharing scheme on the basis of this model, and show that this scheme is provably secure against adaptively chosen secret attacks (CSAs) based on the decisional bilinear Diffie-Hellman (DBDH) problem. We find that this scheme has the following properties: (a) point-to-point secure channels are not required in both the secret distribution phase and the secret reconstruction phase; (b) it is a noninteractive secret sharing system in that the participants need not communicate with each other during subshadow verification; and (c) each participant is able to share many secrets with other participants despite holding only one shadow.
1. Introduction
A secret sharing scheme [1–8] allows the splitting of a secret into different pieces, called shares or shadows, which are given to a group of participants (or shareholders). Only a certain specified subset of the participants can reconstruct the secret easily by providing their shadows, while any unqualified subsets cannot obtain any knowledge about the secret. Secret sharing is useful for any important action whose initiation requires the collective decision of several designated participants, such as the launch of a missile, opening of a bank vault, or opening of a safety deposit box. Research on secret sharing is important for the key distribution of wireless ad hoc and sensor networks [9], both in theory and in practice.
In 1979, two basic secret sharing schemes were independently proposed by Shamir [1] and Blakley [10]. They used two different methods to construct threshold secret sharing schemes. In Shamir's scheme, a secret s is divided into n shadows by a dealer and shared among n participants in such a way that it is possible to reconstruct the secret with any t or more shadows but impossible to reconstruct the secret with fewer than t shadows. This scheme is called a
Verifiable secret sharing (VSS) was proposed in [11] to solve the problem of dishonest participants who want to deceive other honest participants or the problem of a dishonest dealer who distributes incorrect shadows to some participants. VSS has been an important area of cryptography research for the last two decades [5, 7, 8, 12–15]. Feldman [12] proposed a very practical VSS scheme in which the security is based on a discrete logarithm problem. In this scheme, a deterministic function of the secret is published; hence, it achieves only one-way security. Pedersen [13] proposed a VSS scheme that can withstand an unbounded passive adversary.
Stadler [16] proposed a publicly verifiable secret sharing (PVSS) scheme in which the validity of the shadows can be verified by anyone without knowledge of the shadows. In some PVSS schemes [5, 14], the verification procedure involves interactive proofs of knowledge. If these proofs are made noninteractive by means of the Fiat-Shamir technique [17], the security of the verification process would only be carried out in the random oracle model (ROM) [18]. Transferring security analysis of cryptographical primitives from the random oracle model to the standard model (SM) [19] has always been a theoretically important task.
1.1. Related Work
In 2005, Ruiz and Villar [15] proposed a new PVSS scheme that has a higher level of secrecy, called indistinguishability (IND) of secrets based on the decisional composite residuosity assumption. In 2009, Heidarvand and Villar [3] gave two new secure definitions of publicly verifiable secret sharing, which capture the notion of indistinguishability of shared secrets. Then they proposed a non-interactive PVSS scheme against the attacks of indistinguishability of secrets in the standard model based on the decisional bilinear square assumption (DBS) which is a natural variant of the standard decisional bilinear Diffie-Hellman (DBDH) assumption. In 2010, Jhanwar [20] proposed a PVSS scheme whose level of security is called semantic security based on the
Another important aspect of secret sharing is the problem of making the size of shadows of each participant as small as of making the size of shadows of each. A secret sharing scheme is ideal if the length of every shadow is the same as the length of the secret. This is the best possible situation. However, we would like to emphasize that it is also very important to reduce the number of secure channels used in a secret sharing scheme, especially in wireless ad hoc and sensor networks.
A secret sharing scheme contains at least two essential phases: a share distribution phase and a secret reconstruction phase. In the share distribution phase, a dealer chooses a secret, executes a secret distribution algorithm to generate shadows, and then sends the generated shadows to the participants through point-to-point secure channels. In the secret reconstruction phase, the participants belonging to a qualified subset of participants exchange shadows amongst themselves through point-to-point secure channels to reconstruct the secret. In a
1.2. Our Contributions
In this paper, we use the Lagrange interpolation and bilinear cyclic groups to construct a Public Verifiability: a dishonest dealer or participant is detected unconditionally. Security: the scheme has provable security against an IND-CSA (see the security model present in this paper) adversary in the standard model. The security relies on the hardness of the decisional bilinear Diffie-Hellman (DBDH) problem. Needless security channels: in both the setup and share distribution phases, these are no secure point-to-point communication channels between the dealer and the participants. Moreover, no secure point-to-point communication channels are used in the reconstruction phase of the extended scheme. Noninteractivity: the participants need not talk to each other during the secret reconstruction phase.
An overview comparison of the major technique differences and the corresponding security level those of WT11's [2] and HV09's [3] PVSS schemes is given in Table 1.
Major technique differences and corresponding security level.

1.3. Paper Organization
This paper is organized as follows. In Section 2, we describe the definition of bilinear maps and the decisional bilinear Diffie-Hellman problem. In Section 3, we describe the model of our PVSS scheme and the security model. In Section 4, we present our pairing-based PVSS scheme, and in Section 5, we prove its security. In Section 6, we analyze the performance of our scheme. In Section 7, we present an extended scheme that allows reconstruction of the secret through publicle channels. Finally, we give a conclusion in Section 8.
2. Preliminaries
If S is a set,
2.1. Bilinear Map
Let 𝔾 and Bilinearity: Nondegeneracy: Computability: there is an efficient algorithm to compute
The algorithm
2.2. Decisional Bilinear Diffie-Hellman Assumption
Given a tuple 
2.3. Lagrange Interpolation
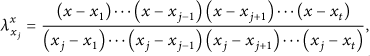
Let 
3. Definitions
This section is dedicated to the definition of a
3.1. Threshold PVSS Scheme without Secure Channels
Let
A PVSS scheme is described by the following algorithms.
Setup
The dealer generates all public parameters of the scheme. Furthermore, every participant selects its channel protection key The dealer randomly picks a number as the main secret of the system and uses For each Secret distribution: the dealer randomly selects a secret S that will be distributed to the participants. It calculates and publishes the secret commitment value (SCV) Verification Reconstruction: this algorithm is composed of three subalgorithms.
Subshadow generation Sub-shadow verification Combine
3.2. Security Model
The PVSS scheme described above must satisfy the following properties.
Correctness: if the dealer and the participants act honestly, any t or more participants can reconstruct the secret correctly during the execution of the reconstruction algorithm. Verifiability: a successful verification of the SCV and SDV of a secret implies that the SCV and SDV are consistent. Privacy: the basic requirement is that it is impossible for any collusion of less than t participants to obtain any information about a secret. Init. 𝒞 executes Setup (λ) to obtain the public parameters and sends the public parameters to 𝒜 along with all of the shadow verification keys SVK. Phase 1. The adversary adaptively selects a secret and generates Sub-shadow query. On being input a participant Challenge. The adversary 𝒜 outputs a target set of participants Phase 2. The adversary continues to adaptively issue the subshadow query as in phase 1, but with the constraint that Guess. Finally, the adversary 𝒜 outputs a guess
Hereafter, we will use the notion of a CSA to define the security of the PVSS scheme. We mostly follow the notation from [19, 23], using a game between an adversary 𝒜 and a challenger 𝒞.
Definition 1 (IND-CSA security).
A 
4. Construction
In this section, we present a concrete
Setup
The dealer obtains the group parameters
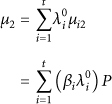
Having received all the The dealer selects a random number The dealer computes The dealer selects a collision-resistant hash function The dealer sets the The dealer randomly selects
Finally, the dealer sends
Secret Distribution
The dealer wants to share a secret, which is a random element in 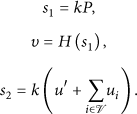
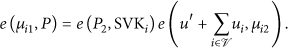
Verification
Given 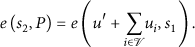
Without loss of generality, let us assume that Sub-shadow generation Sub-shadow verification Combine
At this point, every participant in Γ uses 


5. Security and Correctness
5.1. Correctness
If the dealer and the participants are honest, any t or more participants can reconstruct the secret during the execution of the reconstruction algorithm. The correctness of equalities (6), (9), and (10) is as follows.


5.2. Security
Theorem 2 (IND-CSA of PVSS).
Suppose the hash function H is a universal collision-resistant one-way family. Then, the proposed PVSS scheme is secure against adaptive CSA under the intractability assumption of the DBDH problem. More specifically, if there is an adversary that can break the PVSS scheme within time 𝒯 with probability at least ϵ, then there exists an algorithm that can solve the DBDH problem within time 
Proof.
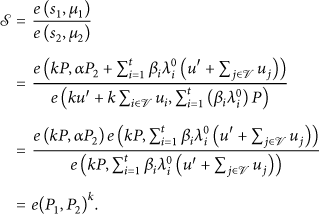
Suppose an adversary 𝒜 breaks the PVSS scheme with advantage
Init. Algorithm ℛ does the following.
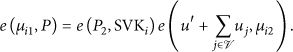
Algorithm ℛ chooses a set 𝕌 containing Algorithm ℛ selects a collision-resistant hash function Algorithm ℛ selects Algorithm ℛ constructs the shadow verification key SVK as follows.
If If Algorithm ℛ follows Waters' [24] method to simulate it as follows.
For v, it lets It sets an integer It chooses a random vector It lets It chooses a random integer It sets It defines Algorithm ℛ sends

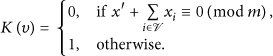
Phase 1. The adversary 𝒜 adaptively selects a secret The algorithm ℛ computes Otherwise, ℛ continues to check whether Otherwise, there are two different cases as follows.
If If
where


We claim that 
Challenge. Once the adversary 𝒜 has completed phase 1, and sent a challenge set 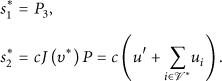
Algorithm ℛ computes the sub-shadow of each If If
where 

At this point, algorithm ℛ randomly selects a bit
Claim 1. Our simulation does not abort with probability greater than 3/4.
Proof. Without loss of generality, let us assume that the adversary 𝒜 makes the maximum number q of sub-shadow queries. For any sub-shadow query of a participant and the 
Phase 2. The adversary 𝒜 continues to issue queries about a sub-shadow of the form
Guess. Eventually, 𝒜 outputs a guess bit If Otherwise, ℛ answers 0, meaning that T is a random element of
If the input 
6. Comparison
Now, let us compare our scheme to
As is well known, the time taken to execute
Computational cost and security.

Communication cost.

From the comparison in Tables 2 and 3, one can see that our scheme achieves a higher level of security without significantly increasing the overall computational complexity and the communication cost.
7. Extension Scheme
In the basic scheme described previously, the secret reconstruction requires the presence of point-to-point secure channels among the participants. In this section, we remove this limitation without sacrificing any good property of the scheme.
Suppose that a participant 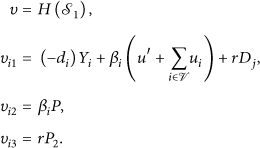


Having collected t valid sub-shadows,
8. Conclusion
In this paper, we proposed a
Footnotes
Acknowledgments
This work is supported by the National Natural Science Foundation of China (NSFC) Programs (nos. 61070251, 61003285, 61103198, and 61272534), the NSFC A3 Foresight Program (no. 61161140320), and the JSPS KAKENHI program (23500031).
