Abstract
The design and analysis of routing algorithm is an important issue in wireless sensor networks (WSNs). Most traditional geographical routing algorithms cannot achieve good performance in duty-cycled networks. In this paper, we propose a k-connected overlapping clustering approach with energy awareness, namely, k-OCHE, for routing in WSNs. The basic idea of this approach is to select a cluster head by energy availability (EA) status. The k-OCHE scheme adopts a sleep scheduling strategy of CKN, where neighbors will remain awake to keep it k connected, so that it can balance energy distributions well. Compared with traditional routing algorithms, the proposed k-OCHE approach obtains a balanced load distribution, consequently a longer network lifetime, and a quicker routing recovery time.
1. Introduction
Studying the behavior of dynamic sensor networks becomes a hot topic. Movements of nodes make the wireless sensor networks (WSNs) [1] a dynamic one. These nodes can communicate with each other in wireless communication radius without any static network interactions. An important issue in dynamic geographical networks is the design and analysis of routing algorithms. Due to the limited communication range of the wireless transceivers, mobile nodes cannot communicate with other nodes unless they are within each other's geographical regions [2, 3]. Thus, it may be necessary for a mobile node to require aids of other nodes after checking their geographical routing information in forwarding data packets to its destination.
It will be much more uncertain when we consider the routing issue in a duty-cycled network, since the duty-cycle scheduling aims to prolong the network lifetime [4, 5] by making some nodes sleep and wake up when packets transmission occurs. Studies on adopting conventional routing protocols in wireless sensor network in a dynamic convention have been generally discussed [3, 6]. Our interest in the routing problem in a duty-cycled network falls into the following two aspects: (1) existing routing algorithm could place a heavy load on a newly joined node due to routing table updates and (2) the wireless network connectivity.
Conventional routing algorithms concentrate on finding the shortest path, without much concern about critical issues such as energy efficiency and network lifetime. The problem we discuss here is how to route efficiently in a duty-cycled sensor network. The basic idea behind the algorithms is to divide the network into a number of overlapping clusters. A node's sleep scheduling leads to a change in the network topology, then the membership of cluster changes as well. We propose a cluster formation scheme called k-OCHE, which selects cluster heads considering energy availability firstly, and then the cluster heads recruit cluster members. This cluster creation scheme can well be adopted in different routing circumstances.
The rest of this paper is organized as follows. Section 2, we survey related work. Section 3 defines network model, sleeping scheduling model, energy consumption model, and some notations. In Sections 4 and 5, we further detail the k-OCHE scheme and routing algorithm. We present specifics of simulation experiments which validate the correctness of the proposed algorithm in Section 6. Finally, Section 7 concludes the paper.
2. Related Work
Similar to other networks, overload balance, prolonging lifetime, and scalability are the major design concerns of wireless sensor networks. In conventional multihop communications in WSNs, sensors close to the sink are often overloaded, resulting in increased latency and reduced network life span. Such overload might cause latency in communication and reduce life span of network. In addition, the original architecture is not scalable for larger set of sensors covering a wider area of interest. To allow the network to cope with additional load and to be able to afford a large area of interest, clustering routing has been pursued. The main aim of clustering routing is to efficiently maintain the energy consumption of sensor nodes by involving them in multihop communication with a particular cluster and by performing data aggregation and fusion to reduce the number of transmitted messages to sink.
2.1. Routing Protocols
Many routing protocols [7–11] have been studied in the field of wireless sensor networks. Karp and Kung present greedy perimeter stateless routing (GPSR) [7], a novel routing protocol for wireless datagram networks that uses the positions of routers and a packet's destination to make packet forwarding decisions. GPSR makes greedy forwarding decisions using only information about a router's immediate neighbors in the network topology. When a packet reaches a region where greedy forwarding is impossible, the algorithm recovers by routing around the perimeter of the region. By keeping state only about the local topology, GPSR scales better in perrouter state than shortest-path and ad-hoc routing protocols as the number of network destinations increases. Under mobility's frequent topology changes, GPSR can use local topology information to find correct new routes quickly.
Shu et al. propose an efficient two-phase geographic greedy forwarding (TPGF) [8] routing algorithm for WMSNs. TPGF takes into account both the requirements of real-time multimedia transmission and the realistic characteristics of WMSNs. It finds one shortest (near shortest) path per execution and can be executed repeatedly to find more on-demand shortest (near shortest) node-disjoint routing paths. TPGF supports three features: (1) hole bypassing, (2) the shortest path transmission, and (3) multipath transmission, at the same time. TPGF is a pure geographic greedy forwarding routing algorithm, which does not include the face routing, for example, right/left hand rules and does not use planarization algorithms, for example, GG or RNG. This point allows more links to be available for TPGF to explore more routing paths and enables TPGF to be different from many existing geographic routing algorithms.
However, these traditional routing algorithm will overload relay nodes with the increase in sensor density. Besides, convergence characteristics of these algorithm are not good enough to meet the need of dynamic networks, such as duty-cycled networks.
2.2. Cluster-Based Approach for Routing
In the last few years, many algorithms have been proposed for clustering routing in wireless sensor networks [12–24].
In [14], Heinzelman et al. have proposed a distributed algorithm for wireless sensor networks (LEACH) in which sensors randomly select themselves as cluster heads with some probability and broadcast their decisions. The remaining sensors join the cluster of the cluster head that requires minimum communication energy. LEACH is one of the most popular clustering routing algorithms for sensor networks and is completely distributed. However, LEACH uses single-hop routing where each node can transmit directly to the cluster head and the sink. Besides, there are a number of clustering algorithms constructing clusters not more than 1-hop away from a cluster head, such as DCA [15] and DMAC [17]. Similar to these, Baker and Ephremides [13] propose overlapping cluster with
In addition, the TEEN [16] and APTEEN [18] are hierarchical protocols designed to be responsive to sudden changes in the sensed attributes such as temperature. Younis et al. [19] have proposed a different hierarchical routing algorithm based on a threetier architecture.
To the best of our knowledge, there is only one clustering algorithm that specifically controls overlapping in the formation of clusters, that is, KOCA [20]. Goal of KOCA is to ensure that the entire network is covered with connected overlapping clusters considering a specific average overlapping degree. KOCA is still a static clustering in which the cluster formation is not changed all the time. This condition causes an unbalance load among all nodes. A node that roles as cluster head (CH) will get more load than a non-CH and so that it will die faster. The death of CHs will break the whole network because the link between nodes and center will be broken. Therefore, KOCA cannot be applied in actual situation commendably. Rotating the CH role distributes this higher burden among the nodes, thereby preventing the CH from dying prematurely. To overcome this problem, we propose k-OCHE which allows a node to go to sleep while keeping its neighbors k connected, thus the role of CH can be rotated and the load of CH can be balanced. The most important is that k-OCHE is the first approach to combine the interior cluster routing with exterior cluster routing which achieves balanced load distribution, longer network lifetime, and quicker routing.
3. Assumptions and Notations
3.1. Network Model
We consider a multihop wireless sensor network where all nodes are alike. We assume that each node has a unique id. The locations of sensor nodes can be obtained by GPS. All sensors transmit at the same power level and hence have the same transmission range
All communications are over a single shared wireless channel. A wireless link can be established between a pair of nodes only if they are within wireless range of each other. The k-OCHE algorithm only considers bidirectional links. It is assumed that MAC layer will mask unidirectional links and pass bidirectional links to k-OCHE. We refer to any two nodes that have a wireless link as 1-hop or immediate neighbors. Nodes can identify neighbors using beacons.
3.2. Sleeping Scheduling Model
To ensure the network connectivity and prolong its lifetime, we assume that all nodes operate under CKN-based [27] sleep/awake duty cycling. Time is divided into epochs, and each epoch is T. On each epoch, nodes run CKN, shown in Algorithm 2, to decide whether to be awake. A node can go to sleep assuming that at least k of its neighbors remain awake to keep it k connected. And nodes reach a consensus to take turns to sleep, while the whole network is globally connected. Therefore, by changing the value of k, the network can manipulate the sleep rate s, so that it can proceed with further work with clustering.
3.3. Energy Consumption Model
We use the same radio model defined in [28]. The amount of energy required to transmit an L-bit message over a distance x is
The energy consumed by receiving this packet is
3.4. Notations
(1) Network size (n): the number of nodes in the network. Sensor nodes are deployed randomly in a square area with side length of l.
(2) Energy consumption rate (EC): for each node,
(3) Energy availability (EA):
(4) Minimum number of awake neighbors in an epoch for each node (k): through varying the value of k, we can keep the network k connected and optimize the geographic routing performance.
(5) Average node degree (d): the average degree of a node u is the number of its neighbor nodes. The relation between the average node degree (d) and the radio range (r) of a node is given by
4. The k-OCHE Algorithm
4.1. The Proposed Algorithm
In k-OCHE, shown in Algorithm 1, a node can go to sleep assuming that at least k of its neighbors remain awake to keep it k connected. Given a k, we can obtain a new network topology within the range of awake nodes in each cycle. Each node can have three possible states: cluster heads (CHs), boundary nodes (BNs), and normal nodes. A cluster head possesses information about not only its own cluster (such as member nodes' IDs) but also adjacent clusters (such as boundary node and adjacent clusters' members). A boundary node belongs to multiple overlapping clusters connecting different clusters to transfer and forward data, and it improves the network robustness effectively. Normal nodes are internal nodes that belong only to one cluster.
(*Run the following at each node u*) (1) Get the information of current remaining energy EA. (2) Set (3) (4) status = CH; (5) Broadcast (6) (7) (8) status = NORMAL; (9) (10) (11) Receive (12) (13) Add (14) (15) Broadcast (16) (17) (18) status = NORMAL; (19) Receive a message. (20) (21) status = CH; (22) (23) (24) Add (25) (26) (27) Send (28) (29) HC=HC+1; (30) Broadcast (31) (32) (33) (34) Send the (35) (36) (37) Update its (38) (39) (40) (41) (42) Status = Boundary; (43) Add (44) Send its (45) (46) Receive (47) (48)
(*For each node (1) Pick a random rank (2) Broadcast (3) Broadcast (4) If Return. (5) Compute (6) Go to sleep if both the following conditions hold. Remain awake otherwise. (i) Any two nodes in 2-hop neighbors that have (ii) Any node in (7) Return.
In this section, we present the description of the cluster head's selection process as well as the clusters' generation; we then give an example to illustrate a cluster generated by k-OCHE.
4.2. Cluster Head Selection Procedure
In k-OCHE approach, the important operation is to select a set of cluster heads (CHs) among the nodes in the network and recruit the normal nodes as these CHs' members. The k-OCHE approach adopts EA to select CHs, and EA is defined as the battery residual energy after certain consumption during a certain period. At the beginning of each cycle, each node compares its EA to the threshold (the threshold is an empirical value, which is used to control the number of CHs in the network. The optimal threshold is obtained when the CH nodes take
However, if a CH u receives a recruit from another CH v, and v has the higher EA, then u gives up being a CH and joins v's cluster. Since the
4.3. Cluster Generation
Each node maintains a table,
The k-OCHE algorithm avoids the fixed cluster head scheme, with periodic replacement done by sleep scheduling mechanism to balance the node energy consumption. All cluster members send the current state information to cluster head, and k-OCHE chooses the node with the highest EA to be the new head. When the new cluster head gets cluster head's notification, it broadcasts recruitment message and the new cluster forming phase triggers. The process can reduce the energy consumption of broadcast of temporary head.
Note that k-OCHE stops in
4.4. An Illustrative Example
We demonstrate our algorithm with Figure 1, which is selected from the simulation results optionally, and we add some necessary information to make it more comprehensible.

An example of overlapping clusters in a network with 38 nodes. After executing k-OCHE, the network selects three cluster heads, and each cluster contains 9 normal nodes. Clusters can communicate with each other through boundary nodes.

Single hop clustering. Each node in the network is not more than 1-hop away from a cluster head.
In Figure 1, there are three clusters with three corresponding cluster heads A, B, and C, and nodes with black frame in the overlapping area are boundary nodes. Note that two cluster heads are not immediate neighbors. Since boundary nodes belong to multiple clusters, their tables contain CHs of those clusters. A, B, and C can communicate with each other through their common boundary nodes in their neighbor cluster head tables.
5. Routing Algorithm
We first discuss the necessary data structures to be maintained at each node for the routing algorithm, as shown in Table 7. We then explain the routing construction and recovery procedures in the network. The routing construction can be divided into two phases: interior cluster routing and exterior cluster routing.
During the interior and exterior routing phase, routes are constructed between all pairs of nodes. The routing recovery phase takes care of maintaining routing table considering sleep schedule and recovering from an individual node failure.
5.1. Interior Cluster Routing
After cluster head selection and cluster generation procedure, each node completes the construction of two tables: when when when when
Let us illustrate it with an example. Tables 1, 2, 3, 4, 5, and 6 are
CH table of A.

CH table of

CH table of H.
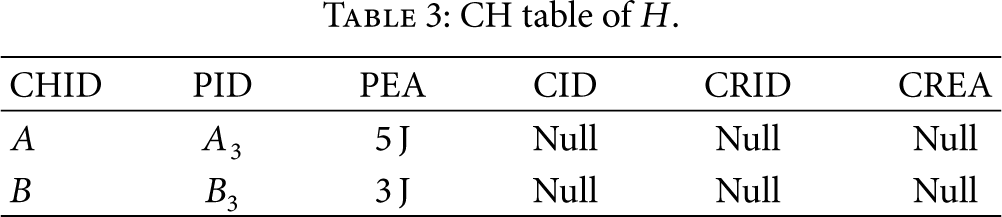
NCH table of A.

NCH table of

NCH table of H.
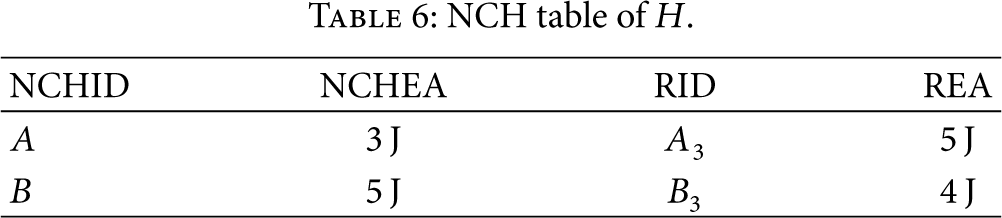
Data structures table.

In the routing table of A, when destinations are
In the routing table of
In the routing table of H, when destinations are in neighbor cluster, H will check
Routing table of A.

Routing table of

Routing table of H.

5.2. Exterior Cluster Routing Construction
We consider each cluster as a node in exterior cluster routing phase. Each CH node takes the responsibility of each cluster. An original routing algorithm (e.g., GPSR and TPGF algorithms) is running exterior clusters. As shown in Figure 3, each hexagon presents a cluster and the black nodes are CH nodes. The normal nodes are ignored except source and sink. When source node s sends a packet to sink node d, s node will run interior cluster routing and then packet will be relayed to CH node A. At that time, A will run exterior cluster routing to decide which neighbor cluster to be the relay cluster and then run interior cluster routing to the CH node of relay cluster. In general, as shown in Figure 3, the routing path of GPSR is straight while k-OCHE's path is sinuous and adaptive to nodes' energy availability which can obtain a balanced load distribution and consequently a longer network lifetime.

Exterior cluster routing. Nodes s and d are source and sink, respectively.
5.3. Routing Maintenance
This phase begins when nodes' status change due to duty-cycle scheduling. The route maintenance in our approach basically boils down to cluster maintenance. After a change in topology, all the nodes have the complete cluster information in the form of
The new cluster information will be propagated throughout the network. Among exterior neighbor clusters, it should be noted that only the boundary nodes are responsible for broadcasting and rebroadcasting any new information. This helps in quick dissemination of information across the network. Thus, the convergence of the cluster-based protocols is very quick. When a node of a cluster stops working, after a certain time, all its neighbors will detect this event. In interior cluster, only its parent node will update the information of
Let us illustrate it with an example, as shown in Figures 4 and 5. Let node D disappear. This event will be detected by nodes C, E, L, K, and J and CH node. Since nodes C, E, L, K, and J are not parent nodes, they will just update

Each cluster can be transformed into a spanning tree.

Routing recovery. When node D disappears, k finds its new parent J and L finds its new parent E.
6. Performance Evaluation
6.1. Experiment Setup
To verify the correctness and effectiveness of the proposed k-OCHE algorithm, we conduct a detailed simulation using the NetTopo [29]. In our simulation, the studied WSN has the topology: 400 * 400
Simulation parameters.

In this section, we evaluate traditional GPSR and GPSR in k-OCHE approach in terms of energy consumption, network lifetime, and recovery time.
6.2. Energy Consumption
First we compare energy consumption of each sensor in traditional GPSR and k-OCHE-based GPSR, which can reflect lifetime of network. Figure 6 reports energy consumption of sensors in two protocols after 600 routing queries have been processed, where x-axis and y-axis together decide the location of each sensor node and z-axis represents the value of energy consumption. Figure 6(a) shows that some sensors in traditional GPSR consume a lot of energy, especially those located along the two edges and diagonal line of the sensor field to which the data sink belongs. So these sensors are energy hungry ones which consume all 5 joules, while sensors located outside this region just consume as little as 0.1 joules after 600 queries. Obviously, the energy consumption in traditional GPSR is very unbalanced. On the contrary, the load in k-OCHE-based GPSR balances very well, as shown in Figure 6(b), where no energy intensive nodes exist. In k-OCHE-based GPSR the maximum energy consumption is 3 J and the minimum energy consumption is 0.04 J. In other words, in the k-OCHE-based GPSR, by consuming 5 J, the sensor network can process routing at least 1000 times.

Comparison of energy consumption in traditional GPSR and in k-OCEH-based GPSR.
6.3. Network Lifetime
Finally, we compare network lifetime, which is more attractive to application scientists and system designers. We set the value of θ (the threshold determines the ratio of active nodes) 90%. The comparison between traditional GPSR and k-OCHE protocols is reported in Figure 7, where x-axis is the initial energy of each sensor and y-axis is the value of network lifetime. From the figure, it can be easily seen that network lifetime in the traditional GPSR is about 1/6 of that in k-OCHE. Additionally, if we decrease the value of θ, the gap between the traditional GPSR and k-OCHE-based GPSR will become much wider. Thus we conclude that k-OCHE indeed extends network lifetime much more than that of traditional GPSR.
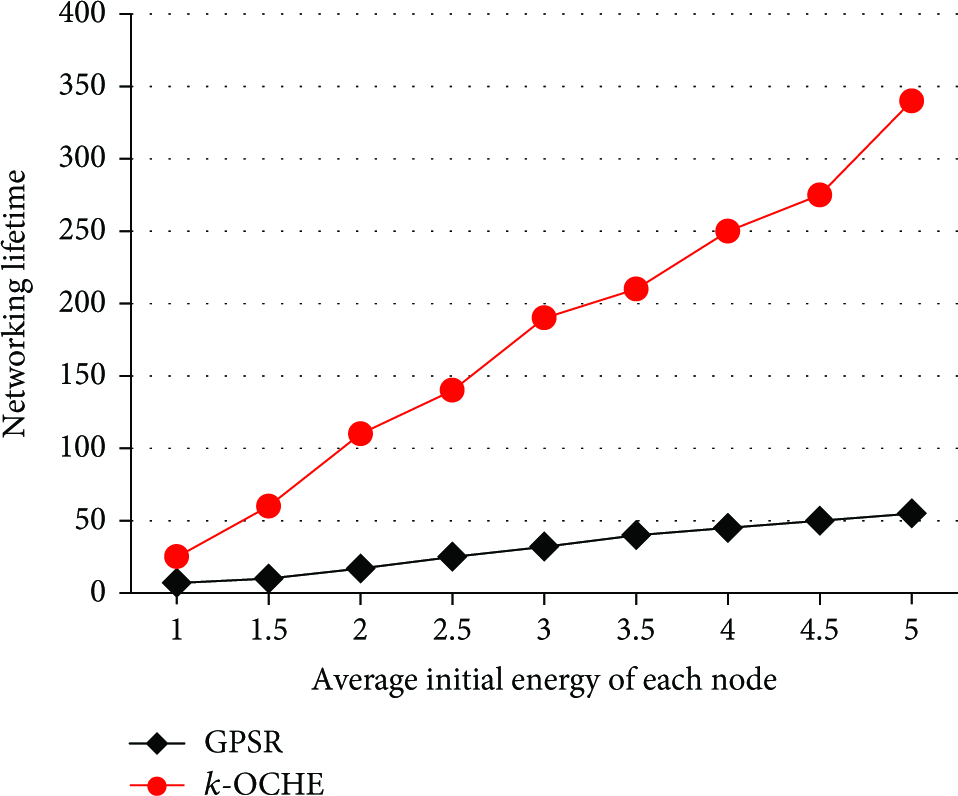
Comparison of network lifetime by using traditional GPSR and k-OCHE-based GPSR.
6.4. Recovery Time
Figure 8 shows the impact of the network size (node density) on the time to repair from an individual node failure for GPSR and k-OCHE, respectively. The x-axis is the network size and the y-axis is the value of recovery time. It is obvious that the recovery time of k-OCHE is much more better than that of GPSR, especially at high values of network size. For low values of network size, that is network size <30, k-OCHE will consume a little bit more recovery time due to the maintenance of clusters. For high values of network size, the recovery time of GPSR increases with network size linearly, while the recovery time of k-OCHE increases very slowly.

Comparison of routing recovery time by using traditional GPSR and k-OCHE-based GPSR.

Demonstration of k-OCHE for different number of nodes n when
7. Conclusion
In this paper, we propose a k-connected overlapping clustering approach with energy availability for routing and topology information maintenance in WSNs. We compare k-OCHE with the classical GPSR, and simulation results show that k-OCHE balances the load to extend the lifetime of sensor network. What is more, k-OCHE achieves shorter recovery time than GPSR, especially with large network size.
Footnotes
Appendix
We present the pseudo code of k-OCHE and review Connected K-Neighborhood (CKN) algorithm in [27] in this appendix.
Acknowledgment
This work is supported by the Natural Science Foundation of China under Grants no. 61070181, no. 61272524, and no. 61202442.






