Abstract
The unattended nature of wireless sensor networks makes them very vulnerable to an adversary's malicious attack. In this paper, we propose to apply game theory into solving the network security problem of wireless network. We explore game theory algorithms to model situation for wireless network with malicious nodes and investigate the attack and detection problem by modeling it as pairwise simultaneous game and spatial structured game. We consider the relationship between the nodes in a wireless sensor network to formulate the game and give the game theory algorithms in detail. We also evaluate the approach with a simulation experiment and analyze the simulation results in detail. We argue that the approach is able to support secure end-to-end communication in wireless sensor networks.
1. Introduction
The unattended nature of wireless sensor networks (WSNs) makes them very vulnerable to an adversary's malicious attacks. An adversary can physically compromise a subset of nodes in a WSN to eavesdrop information. The compromised nodes (or malicious nodes) become black holes [1] in the network. Those black holes in a WSN raise hidden-action attacks [2] to reduce the performance of the network or even destroy the network. Therefore, network security is an important issue for WSNs. In a WSN with malicious nodes, there are obvious conflicts between malicious nodes and normal nodes. As a branch of applied mathematics, game theory is concerned with how rational entities make decisions in a situation of conflict, which has been used primarily in economics. Game theory aims to model situations in which decision makers have to make specific actions that have mutual—possibly conflicting—consequences [3]. In the context of WSNs, game theory may be used to form cooperation schemes among entities in a competitive environment, for example, power control, routing, and resource allocation. Game theory can be applied to model the situation where there are malicious nodes in a WSN.
In this paper, we try to explore game theory to model situation for wireless network with malicious nodes and solve the problem of secure wireless communications by using a game-based approach. The main contributions of this paper are summarized as follows: (1) a formal representation model for simulating a WSN with malicious nodes and hidden-action attacks by using game theory is given; (2) several efficient game-based algorithms are proposed to support reliable and secure wireless communications against the attacks of malicious nodes in the WSN. The remaining of the paper is organized as follows. In Section 2, we first illustrate the system model including the network model as well as the problem statement. In Section 3, we present the game theoretic formulation for a WSN with malicious nodes. Game theory is used to solve the problem of reliable and secure wireless communications against the active attacks of malicious nodes in WSN. Moreover, we present the game theory algorithms in Section 4. In Section 5, we also evaluate the approach with a simulation experiment and analyze the simulation results in detail. Section 6 gives an overview of the related works. Section 7 concludes the paper with an outlook on future research directions.
2. Network Model and Problem Statement
2.1. Network Model
In this paper, we consider a relatively simple WSN. Consider
Forward means a node sends a data packet to another node in the network.
Receive means a node receives a data packet from another node in the network.
Detect means a node receives a data packet from another node in the network and analyzes the pattern of the packet to find out any abnormality.
Sleep means a node turns off its antenna and does not take any other actions.

A wireless sensor network with malicious nodes.
Each action (except sleep) of a node will consume certain of energy. Therefore, either a normal node or a malicious node intends to sleep periodically, in order to save energy. An adversary is able to compromise a node or even physically capture a node. Therefore, there are a number of malicious nodes in the network. Assume the number of the malicious nodes is
Forward.
Receive.
Jam means a malicious node sends an abnormal data packet to another node in the network, in order to block the channel of the node.
Sleep.
Normal nodes do not have knowledge of the instantaneous channel state information (CSI) of malicious nodes, but they know their distribution, and vice versa. Moreover, we assume that the number of the malicious nodes is much smaller than the number of the sensor nodes in the network; that is,
2.2. Problem Statement
The major task of a normal node in the network is to transmit data to other nodes by routing. However, there is an additional task for normal nodes in a WSN with malicious nodes, that is, to detect the abnormal behaviors of malicious nodes. The major task of a malicious node is to block as many data packets of normal nodes as possible by attacking. A malicious node has two kinds of attack methods, passive methods like eavesdropping and active methods like jamming and DoS attack. In WSN, passive attacks of malicious nodes are hard to be detected, while active attacks have a risk of being detected. In this work, we mainly focus on the positive ones. Malicious nodes, in order to allay suspicions or save energy, only take attacks intermittently.
Moreover, we assume that detecting malicious nodes is an accumulative process to a normal node. Every detecting action of a normal node may gain a piece of evidence. When a normal node allocates enough evidence, it could then perform intrusion detection [4, 5] and locate malicious nodes.
3. Game Theoretic Formulation
In this section, we investigate the attack and detection problem by modeling it as a simultaneous game. In this game, we consider the relationship between every pair of nodes in the network. We try to formulate different cases for this game in detail.
3.1. Pairwise Simultaneous Game
Let us consider a WSN with two nodes, a normal node n and a malicious node m. It is a pairwise simultaneous game between the two nodes, where both players move simultaneously. Each player has four strategies (see Table 1). Here γ is the direct income for a node to send out a data packet successfully; that is, the packet is received by another node.
The result of two nodes’ game (one normal node versus one malicious node).

We formulate the energy consumption in the game by some constants.
As we have mentioned before, nodes do not know the identity of each other in our network model. Even a malicious node is not able to confirm one of its neighbor nodes as its ally. Therefore, there is also a game between two malicious nodes,
The result of two nodes’ game (one malicious node versus one malicious node).

Similarly, there is a game between two normal nodes,
The result of two nodes’ game (one normal node versus one normal node).

3.2. Spatial Structured Game
Let us consider a more complex situation. There are a number of subgames between different pairs of nodes (either normal or malicious) in the whole network. We could reduce the complete game into a number of two nodes’ games. For each two nodes’ game, we could get a result by the formulation in Section 2.2 and then synthesize the result of the complete game by the result of all the subgames. Considering a part of a WSN with three nodes

Different patterns for local subgames.
The strategy set of a normal node is
Assume that
In pattern (a) and pattern (b), both neighbors of
In these patterns, we have the following exception rules to the game result in Table 3.
If
If
If
If
In pattern (c) and pattern (d),
In pattern (c), we have the following exception rules to the game results in Tables 1 and 3.
Rule 1.
Rule 2.
If
If
If
In pattern (d), we have one more exception rule.
If
In pattern (e) and pattern (f), both neighbors of
In pattern (e), we have the following exception rules to the game results in Table 2.
Rule 1.
Rule 2.
If
If
In pattern (f), we have one more exception rule.
If
If we take the whole network as an undirected graph, each edge denotes a subgame between two nodes. We could compute the game result of each edge in the graph by traversing the graph with a certain traversal algorithm (e.g., BFS or DFS).
4. Game Theory Algorithms
We could formulate the game for a WSN given in Section 3 by the following algorithms. First, let us consider the case for one specific wireless node (either normal node or malicious node). Algorithm 1 is proposed to compute the payoff of a specific wireless node.
in
The algorithm is trivial. The payoff of a specific node is impacted by the roles of its neighbors. In order to compute the payoff of a specific node, we have to consider the relationship between the node and each of its neighbors.
Then we could compute the payoffs of the whole network based on Algorithm 1. The algorithm for computing global payoffs is given as follows.
Algorithm 2 is also easy to be understood. The process of computing global payoffs is reduced to traversing an undirected graph by BFS. For each node, we just perform a single-node payoff computation, and then we get the information for the whole network. To a given WSN, we shall perform a series of computations to reach convergence.
collection of malicious nodes
5. Simulation and Evaluation
5.1. Simulation Setting
In this section, we construct simulation to evaluate the performance of the proposed approach. We consider a WSN with N players (wireless nodes). Player i is represented as a vertex
The BA scale-free network [6] is adopted to represent the population structure of our WSN, which is constructed according to the “growth” and “preferential attachment” mechanisms. Starting from
Let
The game process is the same as the standard evolutionary game. At each step, all nodes are synchronously updated according to a strategy update rule. Note that in realistic WSNs, there may be environmental noise, which influences individuals' decisions (e.g., strategy mutation). Therefore, we adopt the Fermi updating rule, which considers environmental noise. When player i updates its strategy, it will first select a neighbor j out from all its
Here, κ characterizes the environmental noise, including bounded rationality, individual trials, and errors in decision;
Finally, Tables 1–3 describe the payoffs of normal nodes and malicious nodes; Figure 2 depicts all the six exception rules in the network.
5.2. Experiment Results
In the following simulations, we study the effect of
5.2.1. Action Cost Effect
Figure 3 shows the relationship between network action (
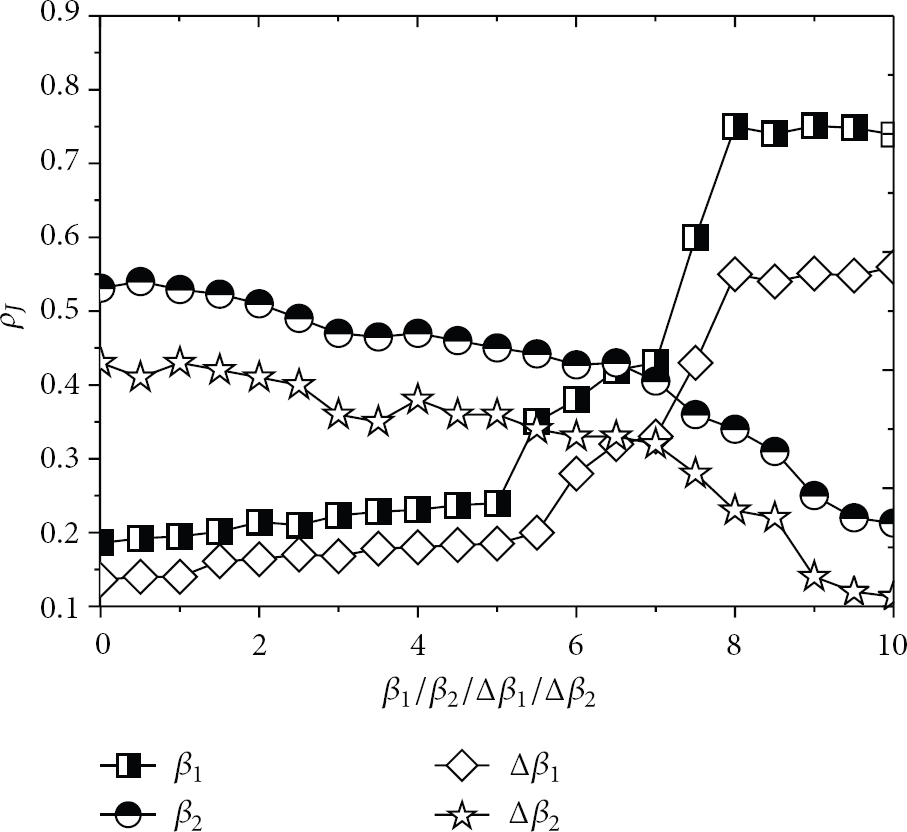
Effect of package-receiving cost, package forwarding cost, jamming detecting cost, and jamming cost on the proportion of malicious jamming nodes.
5.2.2. Coaction Effect
To further explore the effect of network action cost, we jointly study the coaction of forwarding and receiving. The result is shown in Figure 4. The value of

Coaction effect of forwarding and receiving on the proportion of malicious jamming nodes.
5.2.3. Stimulation and Punishment Effect
Next, we explore the impacts of detecting stimulation s and jamming punishment p on

Effect of detecting stimulation and jamming punishment on the proportion of malicious jamming nodes.
Similarly, we also study the joint effect of s and p on the proportion of malicious nodes that take jamming action. The result is given in Figure 6. According to the result of Figure 5, a large
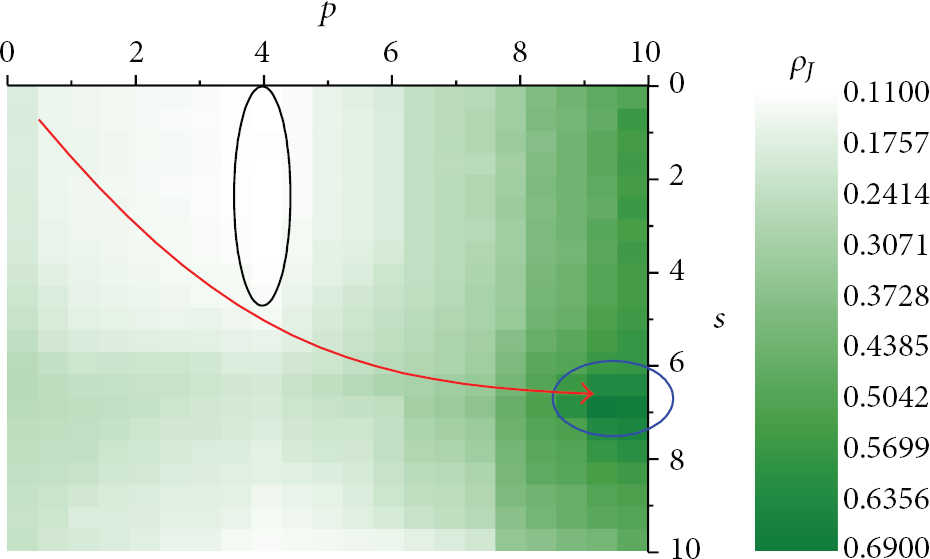
Joint effect of detecting stimulation and jamming punishment on the proportion of malicious nodes taking the jamming action.
6. Related Works
Applying game theory into improvement the QoS of WSN or wireless network is a new research direction, especially the games for the security in WSN or wireless network. There have been a few research efforts in this field. However, there are still many issues worthy of further exploration.
Kodialam and Lakshman in [8] model a zero-sum game between the intruder and service provider of the network. The objective of the intruder is to inject a malicious packet in the network at some node with node t as the target. The intrusion is successful when the packet reaches the target and unsuccessful when it does not. To protect the nodes from the attack, the service provider is allowed to sample the packets flowing through the links on the network. The optimal solution for this game is the min.-max. optimal solution, which is the Nash equilibrium for a zero-sum game. Agah et al. in [9] study a game formulation at the routing layer of a wireless network between malicious nodes that do not forward incoming packets and an intrusion detector residing at the base station. They model this scenario as a repeated game, where the IDS uses the history of nodes’ collaboration to determine paths comprising malicious nodes. The proposed protocol for the repeated game shows a correlation between network size and successful intrusion detection, where detection success rate increases with higher percentage of malicious nodes. Kamhoua et al. in [10] investigate a situation that it is cost effective to freely participate in the security mechanism or protect its privacy depending for each node on the fact that if that node believes or trusts that all other nodes or at least a minimum number of other nodes will do the same. They model a trustable dilemma for autonomous multihop networks by using the mathematical framework of game theory and evolutionary game theory. The well-known stag hunt game is used as their basic game model. They present the interconnection between cooperation, trust, privacy, and security in a network. However, they only consider the game for normal nodes in the network rather than the game between normal nodes and malicious nodes.
Khouzani et al. in [11] develop a zero-sum dynamic game model and investigate the structural properties of the saddle-point strategies. They consider a game with two players (normal nodes and malicious nodes) and three different states with normal nodes. Their research efforts show that saddle-point strategies are simple threshold-based policies, and hence a robust dynamic defense is practicable. They assume there is no competition among normal nodes or malicious nodes in the network, which is not feasible to many situations in WSNs. Sagduyu et al. in [12] present a class of jamming games played at the MAC layer of wireless network among a set of transmitters and jammers. They address the incomplete information or uncertainty in games compared with existing works. The equilibrium strategies resulting from the jamming games characterize the expected performance under DoS attacks and motivate robust network protocol design to support secure wireless communications. Although they consider the conflicts among malicious nodes to be incomplete information, they have not taken the conflicts of normal nodes into consideration. Jaramillo and Srikantin [13] discuss the problem that packet collisions and interference may make cooperative nodes appear selfish sometimes, generating unnecessary and unwanted punishments in wireless ad hoc networks. They present a robust mechanism to imperfect measurements, which is collusion resistant and can achieve cooperation among nodes. However, their method does not satisfy the situation where there are malicious nodes in the network. Yan et al. in [14] proposed a penalizing mechanism to prevent the noncooperative selfish behavior of decreasing the contention window without permission based on repeated game theory for WSNs. A Contention Window Select Game is defined, and in this game each sensor node selects its own contention window to control the access probability.
Moreover, there are some research efforts about using other evolutionary algorithms rather than game theory to sovle the security problem in WSNs or wireless networks. For example, Alrajeh et al. in [15] present an adaptive secure routing protocol based on bioinspired technique termed as ant colonization for WSNs. Their approach is able to select optimal paths from source to destination by ensuring adaptability, robustness, and security. However, their approach cannot suppress hidden-action attacks in WSNs. Hortos in [16] presents a cross-layer approach to WSN protocol design by applying a bioinspired evolutionary computational method to the functions of each protocol layer to improve the intrusion detection identification (IDID) performance. Genetic algorithms and ant colony optimization are used to solve the problem in the proposed approach.
Although many existing approaches have taken game theory to solve the security problem in WSNs or wireless networks, compared with existing works in this field, our approach considers the relationship between nodes in a WSN and gives a formal theoretic model for the game. We discuss different patterns in this game and represent them as rules to generate a more complete game model. We argue that such a representation model is relatively lacking in existing research efforts. Moreover, the algorithms proposed in this paper are not very complex and easy to be implemented in resource-constrained WSNs, compared to the existing approaches. In general, our approach is able to support secure wireless communication in WSNs with malicious nodes.
7. Conclusion
In this paper, we mainly present an approach to apply game theory into solving the network security problem of WSN. We try to explore game theory algorithms to model the situation for WSN with malicious nodes, in order to support reliable and secure wireless communications against the attacks of malicious nodes in the network. We consider the relationship between the nodes in a WSN to formulate the game and illustrate the game theory algorithms in detail. In order to verify the proposed approach, we also evaluate it with a simulation experiment and analyze the simulation results in detail. We argue that the approach is able to support secure end-to-end communication in WSNs with malicious nodes.
Future works may include (1) improving the efficiency of the algorithms to support different kinds of attacks rather than jamming, (2) evaluating the cost of the game theory algorithm for WSN, and (3) considering a more complex WSN model to evaluate the approach.
Footnotes
Acknowledgments
This work is partially supported by Grants from the NSFC Program (no. NSFC61003309), the Science and Technology Department of Zhejiang Province Program (no. 2010C13005, 2011C14024 and 2011C13006-1), the Key Science and Technology Innovation Team of Zhejiang Province Program (no. 2010R50041-03), the ZJNSF Program (no. LR12F02002). This work is also partially supported by the National Development and Reform Commission, China under Special Grants “The Operation System of Multimedia Cloud Based on the Integration of Telecommunications Networks, Cable TV Networks and the Internet”.
