Abstract
A smart grid is a data communications network integrated with an electrical grid that collects and analyzes near-real-time data on power transmission, distribution, and consumption. Currently, smart grid systems are considered to be necessary for improving the monitoring and control of a power distribution infrastructure. Using distributed measurement architecture, it is possible to gather information about the smart grid status for monitoring and controlling the overall infrastructure, including remote units. This architecture can control the use of electricity. In particular, users can monitor and regulate the electricity consumption of each home appliance in real time. Likewise, power companies can monitor and control electricity consumption for stabilizing electricity supply. However, serious problems can arise in case of data leakage. For example, if malicious attackers can sniff and analyze data, they can obtain the usage pattern of a house and ascertain when it is empty. They could then burgle the house. We propose a privacy-enhanced secure data transaction protocol that can protect private data by encrypting them. The encrypted data include the user's ID, home appliance serial number, and electricity consumption. Thus, attackers cannot obtain important data from the encrypted data. In addition, unauthorized power companies cannot access this information too.
1. Introduction
Recently, environmental issues such as global warming have become more serious because of industrial emissions. Many studies on low-carbon green growth are being carried out around the world to address them. The objective of aiming for low-carbon green growth is the abatement of carbon dioxide emissions and the efficient use of environmentally friendly resources. Thus, many researchers are studying application methods for these problems in various industries. In particular, interest in the use of smart grids for the effective use of electricity is increasing [1, 2].
A smart grid is a digitally enabled electrical grid that gathers, distributes, and acts on information about the behavior of all participants (suppliers and consumers) in order to improve the efficiency, reliability, economics, and sustainability of electricity services [3].
A key feature of smart grids is their ability to transmit information between the user and the electricity company in real time. In other words, users can check the electricity consumption of home appliances in real time, and electricity companies can generate only the electricity they need by analyzing usage patterns. The control of electricity production can help reduce carbon dioxide emissions. Interaction between users and power companies requires many types of sensitive information, such as user and home appliance information and smart sensor meter information. This information should be transmitted securely [4, 5]. Otherwise, a malicious attacker could gather data on the electricity consumption of home appliances in order to determine a user's routine and could plan a burglary when no one is at home.
We propose a privacy protection-based data transaction protocol for smart sensor meter in a smart grid. This protocol has two phases: a transmission phase and a check phase.
The remainder of this paper is organized as follows. In Section 2, we briefly provide basic information about smart grids. In Section 3, we discuss problems regarding the security of private information in smart grids, while in Section 4, we describe our proposed protocol. We present an analysis of the proposed protocol in Section 5, and finally, we summarize our research in Section 6.
2. Related Work
2.1. Smart Grid
A smart grid is a digitally enabled electrical grid that gathers, distributes, and acts on information about the behavior of all participants (suppliers and consumers) in order to improve the efficiency, reliability, economics, and sustainability of electricity services [1] (see Figure 1).

Smart grid system.
A smart grid communication network will comprise several different subsystems—it is truly a network of networks. These networks include a supervisory control and data acquisition (SCADA) system; a land mobile radio (LMR) system; cellular, microwave, fiber optic, dedicated, or switched wirelines; RS-232/RS-485 serial links; wired and wireless local area networks (LAN), and so on [6, 7].
2.1.1. SCADA
An important component required for the monitoring and control of a substation is the SCADA system. It is utilized for distribution automation (DA) and computerized remote control of medium voltage (MV) substations and power grids, and it helps electricity utilities increase the reliability of power supply and reduce operating and maintenance costs. In the past, sectionalizer switchgear, ring main units, reclosers, and capacitor banks were designed for local operation with limited remote control capability. Today, using a SCADA system over reliable wireless communication links, remote terminal units (RTUs) provide powerful integrated solutions for upgrading remotely installed electrical equipment. In a Distribution Management System (DMS), RTUs seamlessly interface via a SCADA system with a wide range of high-performance control centers supplied by leading vendors worldwide. Connection to these Enterprise Management Systems (EMS) and DA/DMS control centers is typically provided via a high-performance IP Gateway or similar nodes [2, 8].
2.1.2. Wireless Networks
Different areas of the smart grid network require different wireless networking solutions. Advanced metering infrastructure (AMI) solutions can be meshed or point-to-point, with local coverage or long-range communication. Options for backhaul solutions are fiber, wireless broadband, or broadband over powerline, to name a few. Workforce mobility solutions include WiMax, WLAN, Cellular, and LMR, depending on the reliability, throughput, and coverage desired by the utility. Wireless communication solutions can be either licensed or unlicensed, again depending on the needs of the utility. For achieving the highest reliability, a licensed solution should be chosen. Each of the above options has advantages and disadvantages, but what is consistently true of all of them is the necessity of a scalable security solution [2, 9].
2.1.3. Security
Smart grid deployments must meet stringent security requirements. Strong authentication is necessary for all users and devices that may affect the operation of the grid. With the large number of users and devices affected, scalable key and trust management systems, customized to the specific needs of the energy service provider, are essential.
The deployment and operation of large, secure network communication systems over many years has taught us that the effort required to provision symmetric keys into thousands of devices can be too expensive or insecure. The development of key and trust management systems for large network deployments is required; these systems can be adopted from other industries, for example, LMR systems and Association of Public-Safety Communications Officials (APCO) radio systems. Several APCO-deployed systems provide statewide wireless coverage, with tens of thousands of secure devices. Trust management systems based on public key infrastructure (PKI) technology could be specifically customized for smart grid operators, easing the burden of providing security that adheres to accepted and guidelines that are known to be secure [10, 11].
2.2. Review of Ren et al.'s Scheme
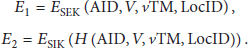
In this section, we present an analysis of Ren et al.'s scheme [12] (see Table 1). These researchers proposed lightweight privacy-aware yet accountable secure communication scheme (PASS) between SM sensors and a Smart Grid Control Center (SGCC). PASS has five components: Attaching Data uploading: the customer uploads data messages Consider
Notation of Ren et al.'s scheme.
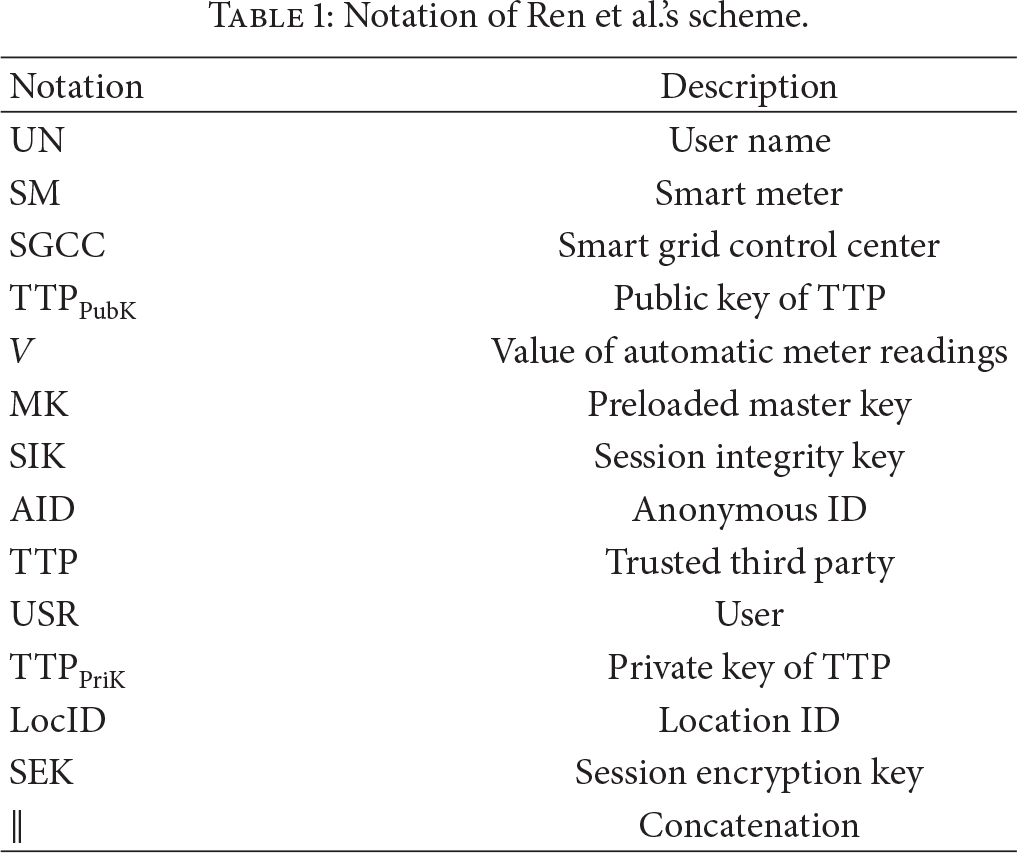
If it is satisfied, the
3. Security Problems in Smart Grid Systems
3.1. Privacy Problem
The security issues in smart grid have been widely discussed in recent years. The primary security issue is privacy because information transmitted over a smart grid contains electricity usage patterns of home appliances. This information could indicate not only the amount of energy consumed by each user, but also when they are at home, at work, or traveling [13]. Furthermore, it might be possible to infer what types of home appliances are present by compromising users' home area networks. The present smart grid system gathers user information in order to check and calculate the amount of electricity consumption.
Thus, if a criminal or malicious attacker can determine when a user is not at home, they may break into his/her house at such a time. Thus, energy-related information could support burglars or provide business intelligence to competitors [14].
3.2. Electricity Consumption Loss
According to the report Smart Metering & Privacy: Existing Law and Competing Policies, researchers at MIT have developed a nonintrusive appliance load monitor (NALM) [15, 16].
If NALMs could be incorporated in the existing metering infrastructure to allow for real-time logging of electricity consumption, information concerning appliance use may be reconstructed from the overall load data; thereby removing the need to intrude residential space and install new equipment in the house. NALMs were designed as research tools, and they were set up to monitor only a small number of customers in order to facilitate load forecasting and management (see Figure 3). However, smart grids allow the collection and communication of highly detailed electricity usage information, in much the same way as the NALM [16]. Thus, the problem of privacy within a smart grid is the main concern.
3.3. Modification of Electricity Consumption
Existing power companies require only power lines to connect a house to a power source. Thus, individual customers cannot access the electrical grid through the Internet. This feature provides security from the risks associated with the Internet. However, smart grid architecture connects a house (smart sensor network) to not only an electrical grid but also the Internet. This means that a smart grid is exposed to additional risks, one of which is illegal modification of electricity consumption [17].
In a smart grid, users and electricity companies communicate with each other through a wired or wireless network. Information about electricity consumption and the user is transmitted via this network. Thus, if a malicious attacker modifies a user's electricity consumption, the user might have to pay a lot of money for electricity that has not actually been used. In addition, unscrupulous users could modify their electricity consumption in order to profit by paying less. There is a high likelihood of such instances [18].
4. Proposed Protocol
4.1. Basic Structure
In this section, we propose a data transaction protocol for privacy protection (see Figure 2). To solve the problems faced in existing smart grid systems, our scheme creates hash data from the information on home appliances. Thus, electricity companies or attackers cannot obtain any valuable information.

Protocol of Ren et al.'s scheme.

Household electricity demand profile recorded on a one minute time base.
This scheme has two steps: a transmission phase and a check phase. In the former, the user sends encrypted information, such as electricity consumption and serial numbers of home appliances, to the power company and the power company stores this information. In the check phase, the user requests his/her electricity consumption from the power company and can check the power consumption of each home appliance. Figure 4 shows an overview of the proposed scheme.

Overview of the proposed scheme.
4.2. Overview of Entire Scheme
Table 2 describes the notation used for discussing the proposed scheme. The notation is used throughout this paper.
Notation used for the proposed.

4.3. Registration Phase
In the registration phase, the user inputs his/her ID (

Registration phase.
The
When the user moves into a new house, he/she should register his/her 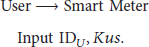
The 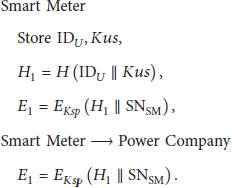
The 
4.4. Transmission Phase
In the transmission phase, information on home appliances (
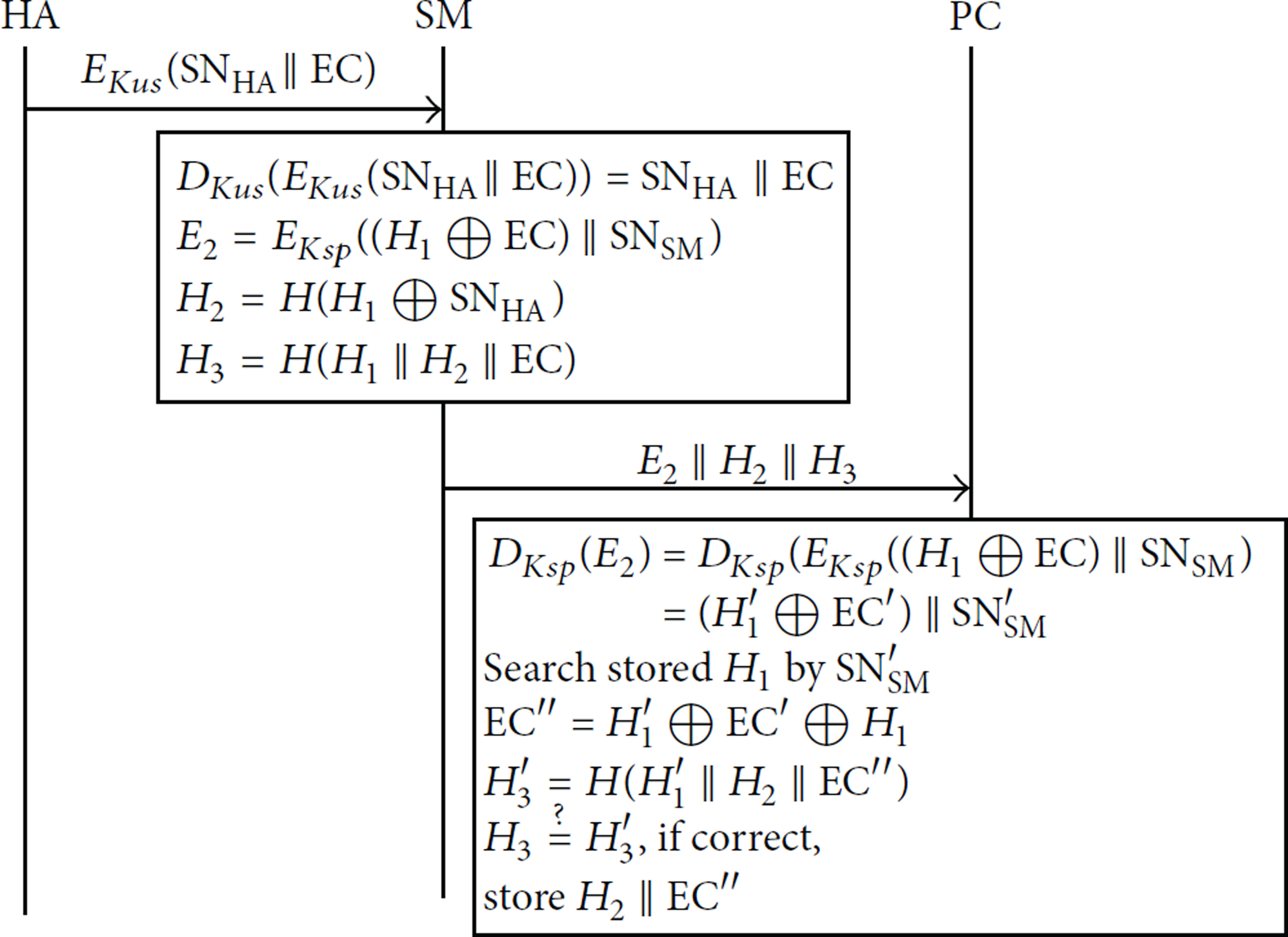
Transmission phase.
Each home appliance sends the home appliance serial number (
The 
The 
4.5. Check Phase
In this phase, the user requests the electricity consumption of one or more home appliances from the
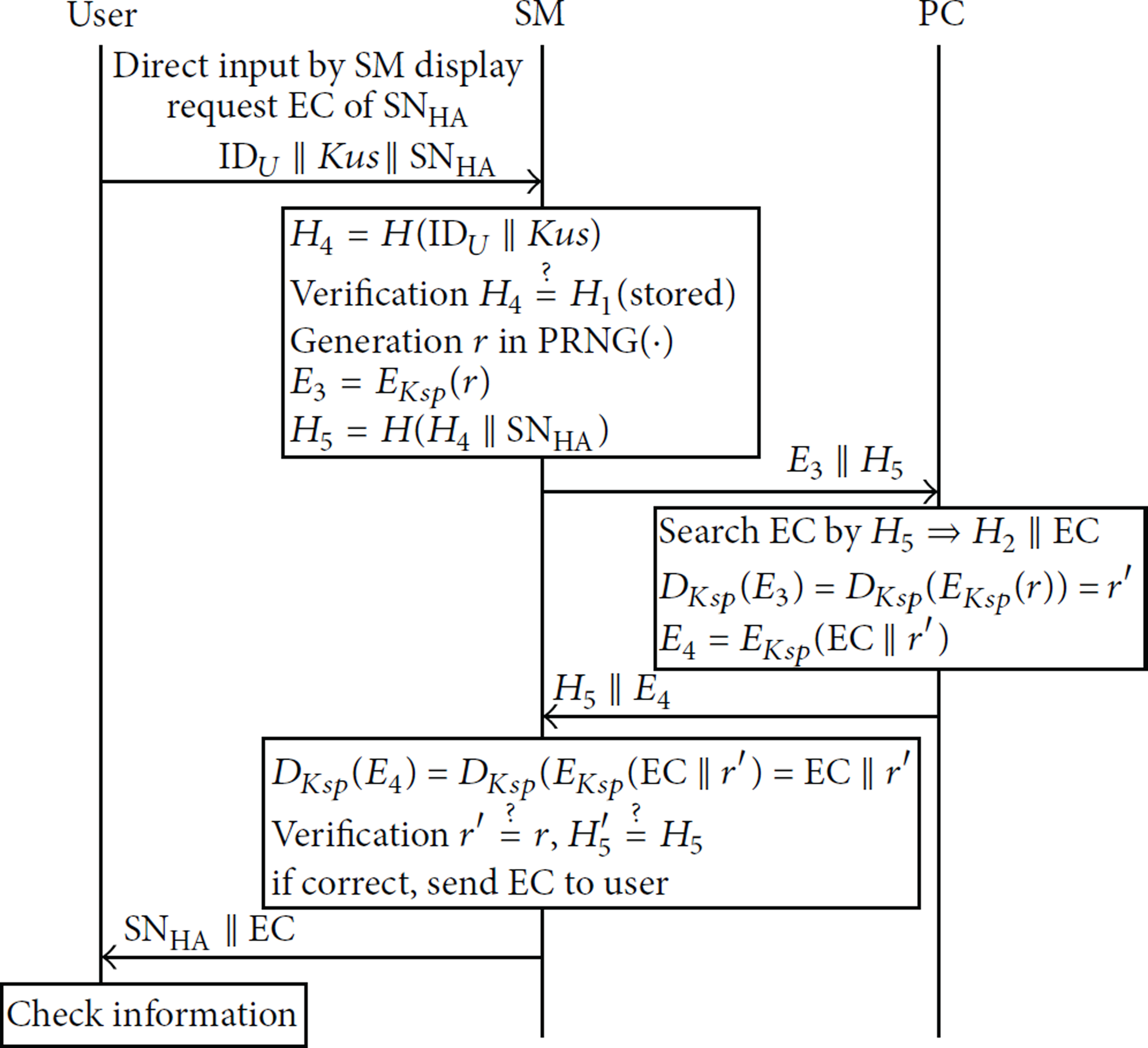
Check phase.
First, the user inputs the 
To verify that the request has come from an authorized user, the 

When 
Finally, the user can check the electricity consumption of his/her home appliances.
5. Analysis
5.1. Protection against Privacy Invasion
The proposed protocol protects against privacy invasion by using a user password (
However, the protocol proposed in this paper uses encrypted data. This contains the home appliance serial number and electricity consumption (
5.2. Protection against Electricity Consumption Loss
The proposed protocol protects against data leakage by using a user password (
In the transmission phase, we encrypt the home appliance serial number (
5.3. Protection against Modification of Electricity Consumption
If a malicious attacker modifies the electricity consumption data of a home appliance, the user may have to pay more money because of the modification. On the other hand, if unscrupulous users modify their electricity consumption in order to profit, the
Consider
Attacker cannot create The The The comparison result shows that the received data is incorrect. Therefore, the



5.4. Performance Analysis
In this section, we compare the performance of our proposed scheme with that of Ren et al.'s scheme. The proposed scheme has three phases: registration, transmission, and request. In contrast, Ren et al.'s scheme has only one phase, called PASS. PASS is similar to the transmission phase of the proposed scheme. Therefore, we compare PASS and the transmission phase.
Table 3 shows an analysis of the computational cost. The proposed scheme is computationally more efficient compared to Ren et al.'s scheme. Besides, in the former, asymmetric encryption is not used and the hash function is used less.
Analysis of computational cost.

Table 4 shows an analysis of the communication cost. As can be seen, our proposed scheme needs two handshakes in the transmission phase. On the other hand, Ren et al.'s scheme needs three handshakes in PASS. Thus, our proposed scheme is more efficient with regard to the communication cost.
Analysis of communication cost.
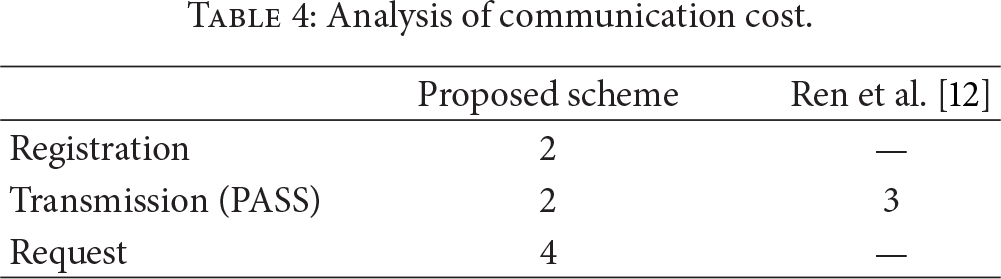
In order to compare the proposed scheme and Ren et al.'s scheme, we simplify the computational cost for carrying out a quantitative analysis. We assume that the computational cost of asymmetric encryption, symmetric encryption, and the hash function are 3, 2, and 1, respectively. Actually, asymmetric encryption involves higher computational cost compared to symmetric encryption and the hash function. Further, symmetric encryption involves higher computational cost compared to the hash function. Thus, the computational cost of the proposed scheme is 11 (4Sym + 3T (h) = 4 × 2 + 3 × 1 = 11), while that of Ren et al.'s scheme is 18 (2Asym + 4Sym + 4T (h) = 2 × 3 + 4 × 2 + 4 × 1 = 18).
Figure 8 shows the changes in the computational cost and communication cost with time. We calculate the costs for the case where data are transmitted at regular intervals. For example, if data are transmitted at 10 min intervals (144 = 1 day/10 min), the cost of the proposed scheme is 1584 (= 144 × 11), while that of Ren et al.'s scheme is 2592 (= 144 × 18).

Changes in computational and communication cost for data transmission at regular intervals.
6. Conclusion
In this paper, we have proposed a secure data transaction protocol for smart grids to protect private information. The proposed protocol has two phases: a transmission phase and a check phase. In the former, we encrypt the user ID, home appliance serial number, and electricity consumption to protect against attacks such as eavesdropping and modification. For the encryption, the user password, encryption/decryption key, and hash function are used. In the check phase, the user can request information about the electricity consumption of a home appliance. For this, he/she sends an encrypted user ID and home appliance serial number to the
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interest regarding the publication of this paper.
Acknowledgments
This research was supported by the Ministry of Knowledge Economy (MKE), Republic of Korea, under the Information Technology Research Center (ITRC) support program (NIPA-2012-H0301-12-3007) supervised by the National IT Industry Promotion Agency (NIPA). This work was supported by the Soonchunhyang University Research Fund.