Abstract
Being one of the main technologies for Internet of Things (IoT), wireless sensor network is absolutely critical and plays an increasingly important role in the development of Internet of Things. Wireless sensor network is mobile network composed of sensor nodes with limited resources, like computation capability, energy, memory storage, and communication capability. Its characteristic results in that the security of wireless sensor network faces a great challenge. Hence, the security of wireless sensor network is an important issue for the development of IoT and shall be focused on. In this paper, a novel authentication scheme is proposed for wireless sensor networks based on theory of quadratic residues. It is making the use of master key to achieve simple symmetric cryptographic primitives and authentication operation and reach the aims of great resistance against the attacks and low energy consumption. Then the proposed scheme is compared with other network-wide key management schemes, obtaining better results in the aspects of security, efficiency, and scalability.
1. Introduction
The future Internet, designed as “Internet of Things (IoT),” is foreseen to be a wide world network of interconnected objects which is uniquely addressable in various types of communication networks [1]. Internet of Things will lead to great influence and opportunities to change and improve people's lives and pushes the technologies in various areas developing rapidly. Playing an important role in the future developments of IoT, wireless sensor network can collect the information in the surrounding environments and process and transmit the data to the Internet. It is an important data resource for IoT and the development of IoT cannot be lack of wireless sensor network's support. Such a technology endows the WSN a new perspective and challenge. Therefore, wireless sensor network is more and more popular and important in technologies and applications of IoT. However, wireless sensor network is composed of small, lightweight, inexpensive sensor nodes. In the system, those sensor nodes have limited resources, like low computation capability, limited energy, limited memory storage, and narrow bandwidth [2, 3]. Meanwhile, it is usually deployed in untrusted and unsecure areas where communication is needed but there are no steady communication infrastructures or those infrastructures are absent. Therefore, we not only pay our attention to making wireless sensor networks useful, manageable, efficient, and feasible, but also focus on the improvement of security.
Security plays an important role in the wireless sensor networks' technologies [4–8], because sensor nodes are deployed mostly in hostile and tactical scenarios. Due to the nature of wireless sensor networks, they must face lots of great challenges about the security, such as limited resource of sensors, wireless transmission nature, and low resistance to attacks, which will result in that adversaries can easily eavesdrop the data transmission, impersonate other users, inject bogus data, and alter contents of legitimate messages. So the administrators must adopt effective measures to keep the security of WSNs, such as data confidentiality, data integrity, privacy, and authentication.
Therefore, authentication mechanisms need to be implemented to protect sensor nodes from various malicious attacks. While the WSN is running, when a user wants to join the WSN, it needs to be first authorized by the nodes in the WSN so that accessing the network illegally does not happen. Therefore, in recent years many researchers pay more attention to key management and authentication for WSN and make good achievements in the research field. A lot of novel, safe, and efficient authentication protocols are proposed in recent years, such as C. T. Li, M. S. Hwang and Y. P. Chu's scheme [9, 10], Das's schemes [11], and Dressler's scheme [12].
1.1. Threat Model
Due to the nature of wireless sensor network, it is vulnerable to resource consumption attacks and usually not resistant to those attacks, which facilitates physical manipulation and key material stealing. Few of the attacks are of the most concern for WSN [13] and are listed as follows.
(1) Physic Attack. Sensor nodes are usually deployed in hostile environment and exposed easily to physical intrusion with the adversary. Physic attack is gaining access to nodes' memory to extract the master key of legitimate sensor nodes in the network [14, 15].
(2) Node Capture Attack. In a WSN, an attacker can capture sensor nodes and extract desired information from nodes' memories or obtain access to the network. Once a set of sensor nodes is under the control of the attacker, this attacker has the capability of eavesdropping private information of the nodes and recovering cryptographic and authentication key [16–18].
(3) Denial-of-Service Attack. In a WSN, a denial-of-service attack (DoS attack) is an attempt to make a sensor node unavailable to its intended users [19–22]. The attackers will try to send external authentication requests to sensor nodes and want them to respond to those requests, such that it cannot respond to legitimate requests or responds so slowly as to be rendered effectively unavailable or use up the sensor nodes' energy and make authenticators cannot work normally. It prevents the sensor nodes from being authenticated by a legitimate authenticator and makes the authentication scheme not work.
(4) Reply Attack. An attacker can eavesdrop on the conversation between the claimant and the authenticator and retransmit the message to the legitimate authenticator as being authentic. It leads to legitimate access for the attackers into the network and no response to the claimant so that the authentication scheme cannot work normally.
(5) Impersonation Attack. Attackers can masquerade as legal nodes to be authenticated or authenticate others by intercepting and falsifying data and thereby gain illegal advantages.
1.2. Our Contributions
This paper aims to propose a novel authentication scheme based on quadratic residues for wireless sensor networks, which is utilizing the master key to calculate the authentication key chains. Our proposed scheme is to achieve simple key management and to provide an authentication operation for the user access to the network. It utilizes the master key to generate pairwise keys in initialization and key setup phase and then erases the master key from the memory and does not need master key during the normal operation of the network anymore. In addition, proposed authentication model has a good resistance to those attacks which are of the most concern for WSN. Therefore, a security analysis has been given to demonstrate that proposed scheme can withstand the previously mentioned attacks and have good scalability. Meanwhile, we make a simple summary and analysis of energy consumption and find it have better performance compared with other schemes.
1.3. Organization of Our Paper
The rest of the paper is organized as follows. In Section 2, we reviews and describes exiting related works. In Section 3, an improved authentication scheme is proposed based on quadratic residues. Security analysis and performance evaluation are provided in Section 4. Our conclusions are presented in Section 5.
2. Related Works
This section introduces two types of previously published work: master-key-based key management protocols and authentication schemes based on quadratic residue. Those protocols make important contributions in this area and have been discussed widely.
2.1. Master-Key-Based Key Management Protocols
SPINS is a suit of security protocols optimized for wireless sensor networks [8, 23]. It is presented to achieve data confidentiality, two-party data authentication, evidence of data freshness and authenticated broadcast for severely resource-constrained environments. In SPINS, it is assumed that there is a trusted third party in the network and each node shares its master key with this trusted third party. Thus, the trusted third party has the capability of achieving the authentication and generating pairwise keys for nodes. When two nodes want to establish a pairwise key to make a communication with each other, they must ask trusted third party to guarantee the legality of each other. BROSK is an energy efficient master-key-based key management protocol [24]. In the protocol each node establishes a pairwise key with its neighbors by broadcasting key negotiation messages instead of being authenticated through the trusted third party. Once one node receives a key negotiation message, it can construct the shared pairwise key with who broadcasts this message by generating the MAC. Both protocols are proposed based on master key however, they do not take the security of master key into consideration, because it is vulnerable to physical attacks in two protocols. Once the attackers extract the master keys, they can obtain all the information of key management to compromise the whole network. Zhu et al. [25] proposed the Localized Encryption and Authentication Protocol (LEAP) which utilizes four types of keys for each sensor node. These are used for different purposes and ranges. (1) Individual key is shared between each node and base station. (2) Pairwise key is shared between a node and its neighbor node. (3) Group key is shared by all nodes in the network. (4) Cluster key is a key between a node and its all neighbor nodes. Among four types of keys, pairwise key is more important and its security guarantees the security of LEAP. However, Kim et al. [26] pointed out that in LEAP, the entire network will suffer a severe loss if the initial master key is exposed to an attacker during key setup. So they propose a quick key establishment to improve the security of LEAP. Our proposed scheme will avoid this drawback and be perfectly resistant to those attacks.
2.2. Authentication Scheme Based on Quadratic Residue
Recently Chen et al.'s scheme [27] is proposed to achieve mutual authentication based on hash function and quadratic residues assumption for RFID system. The scheme is utilizing direct indexing for each tag's authentication and avoiding servers' brute search. In condition, Chen et al.'s scheme has the capability of having good resistance to those attacks and resolution to security problems, like TID anonymity, individual location privacy, replay attack, mutual authentication and DOS attack. Soon after Chen et al.'s scheme is proposed, Yeh et al. [28] demonstrate the weaknesses of that scheme in their work and present an improved scheme to avoid those already existing problems. According to the description of Yeh et al.'s work, Chen et al.'s authentication scheme is vulnerable to impersonation attack. In condition, Chen et al.'s scheme cannot effectively resist location privacy and replay attack. So Yeh et al.'s scheme makes an additional supplement of Chen et al.'s scheme and utilizes the number generated by the tags to add in the session between the tags and the server. The solution obtains a good effect in the authentication scheme and makes it invulnerable to impersonation attack.
Two schemes described previously are proposed based on quadratic residue however, they are both specific to RFID system and not suitable for WSN system. RFID system does not take the security of master key into consideration. And the common attacks in two systems are different so that we need to improve the authentication scheme invulnerable to those common attacks in WSN system. On the other hand, the relationship between the server and the tags in RFID system is one-to-many; in other words, the tags must be authenticated by one server. However, that is different in WSN system and each legal and authenticated sensor node should have the capability of authenticating the new nodes who want to join the network. Our proposed scheme will consider those drawbacks in detail and solve those problems.
3. Proposed Authentication Scheme
In the system, it is assumed that there is not a trusted server and each sensor node directly negotiates a session key with neighboring nodes and uses the master key to authenticate itself with its neighbors. And there are three phases in this paper: key predistribution phase, network deployment phase, and authentication phase. While the authentication protocol is operating, there are authentication messages exchanged among the nodes to be used for pairwise key generation and new node authentication. That message packets format used within the network is shown in Figure 1. The meanings of those acronyms in the Figure 1 are as follows: SRC, source address; DST, destination address; LEN, message length; MT, message type; AM, authentication message. When a node broadcasts its randomly selected number or begins the authentication operation, it will send the message packet to other neighboring nodes.

Message packet structure of our authentication protocol.
On the clarity and conveniences of this paper, the representations are listed in the following.
Then a detailed description for those phases is shown in the following.
3.1. Key Predistribution Phase
Key predistribution phase is carried out before the nodes deployed in the network, because a network-wide symmetric master key
The symbol
The authentication key is changed with the cycle increasing and the authenticator set in current cycle is removed after new authenticator set in next cycle is generated by the node.
3.2. Authenticator Update
In this section, the process to update authentication key and authenticator set for ith tuple of jth cycle is introduced in the following.
Update current authentication key to a new one with hash functions, getting
Calculate new authenticator for ith tuple of next cycle with newly updated authentication key Obtain the new key:
3.3. Network Deployment Phase
The nodes in the network are deployed randomly in the environment during the beginning of this phase. The network structure of WSN is shown in Figure 2. The nodes in the WSN are divided into various clusters. Then the nodes will find their neighboring nodes in their cluster and exchange session messages with neighboring nodes to initialize the network after the deployment. The details are listed in the following.

The network structure of WSN.
(1) Update session key: each node updates its session key from 0th cycle to 1st cycle of authenticator and generates the session key. Session key for each node is including authentication key and authenticator for current cycle. The session key shall be updated as authentication key in first cycle authenticator after the deployment. For example, session key of node A in ith tuple is
(2) Generate pairwise keys: after authentication key is updated, each node randomly selects a random number to generate pairwise keys with neighboring nodes based on master key. The generation is shown in Figure 3. In Figure 3, node A has 8 neighboring nodes and broadcasts the message
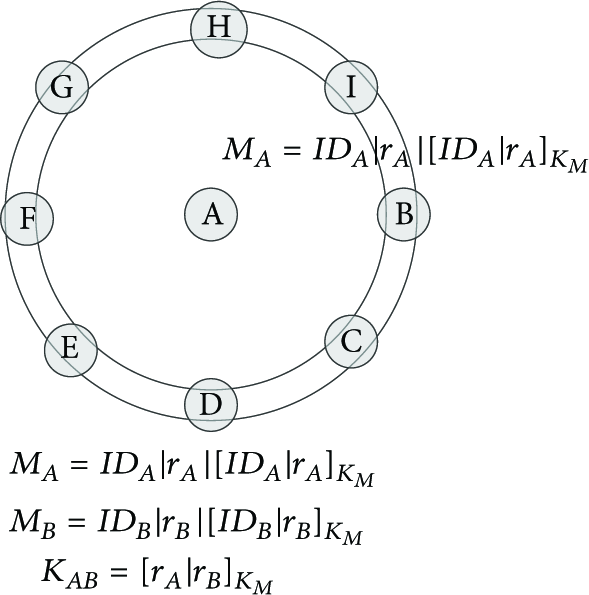
The generation of pairwise keys between nodes.
(3) After the deployment of the network, each node stores a series of keys, including its own encryption key, a list of pairwise keys of its neighboring nodes, its authentication key, and its session key in first cycle authenticator.
Following the previously steps, each node could begin to communicate with its neighboring nodes using pairwise key. In addition, each node is capable of authenticating new node that tries to join the network and confirming whether new node is a legal and permitted user.
3.4. Authentication Protocol Phase
During the authentication operation, node A is assumed as a new node that wants to join the network and stores network-wide master key, its 0th cycle authenticator. Node B is selected as a decision maker to confirm if node A is legal user. Node A must pass the authentication of node B, while node A shall also judge node B not to be a compromised and hostile user. The whole procession is a two-way authentication and they must authenticate each other.
(1) Node A randomly selects a number
Step 1.
Generate a pairwise key
Step 2.
Select a random number t and choose ith tuple random number
Step 3.
Calculate the values of
Step 4.
Compute the quadratic residue of x,
Step 5.
Send the message
(3) Node A receives the message
Step 1.
Update current cycle authenticator with this message and compute authentication key from current cycle to jth cycle with hash function:
Step 2.
Calculate x and t based on the parameters X and T in message
Step 3.
Determines the value of
Step 4.
Authenticate whether node B is a legal user. At first, calculate the authentication key of node B:
Step 5.
Generate a response message, showing
(4) Node B receives message
If all l tuples of random number in jth cycle authenticator run out, update j and authentication key
Then the whole authentication operation is shown in Figure 4.
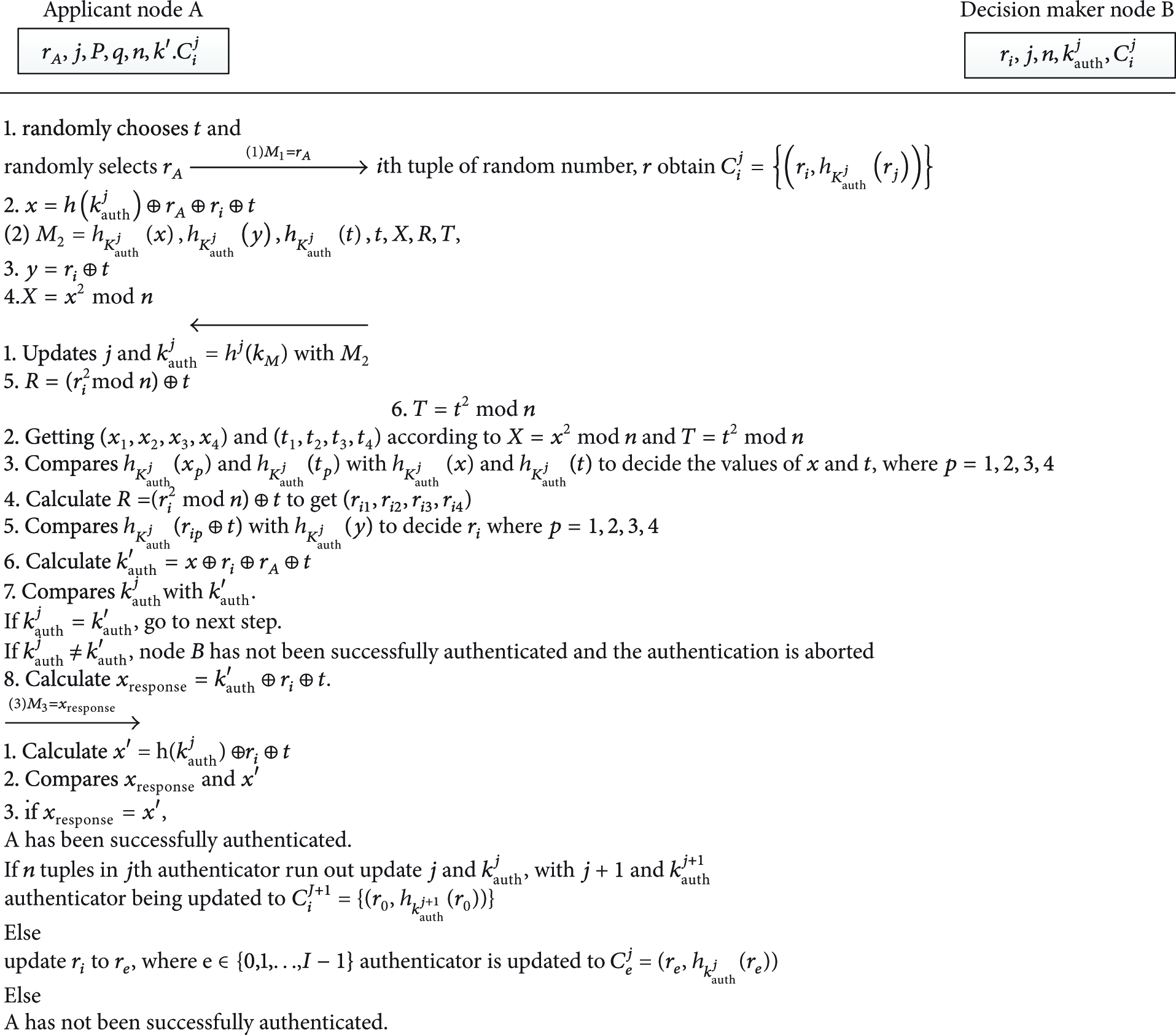
The authentication protocol.
4. Security Analysis and Performance Evaluation
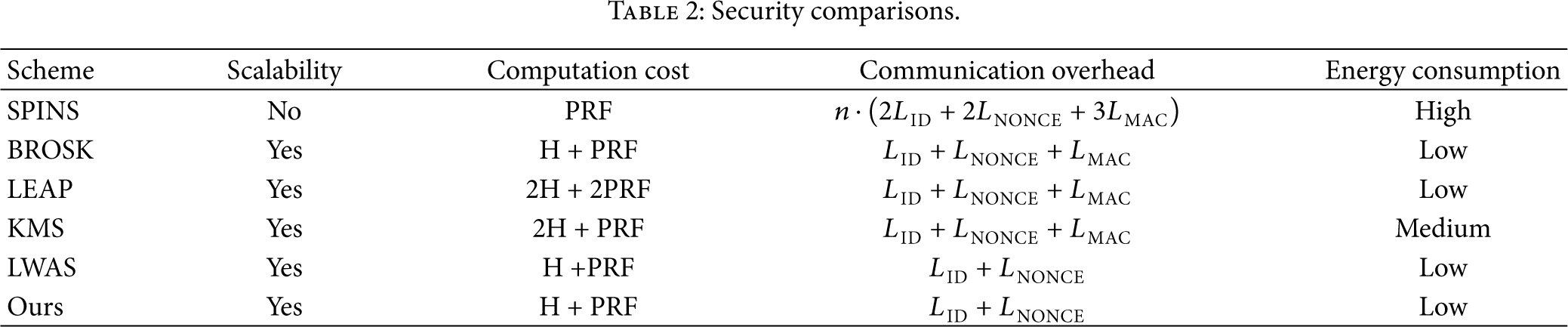
In this section we make the security analysis and performance evaluation of our scheme and compare it with other schemes, like SPINS [8, 23], BROSK [24, 30], LEAP [25], KMS [26], and LWAS [31]. The reason why we choose those schemes is that all the schemes are based on network-wide key. The comparisons of various security attributes among our scheme and other works are listed in Table 1, while the performance comparisons are revealed clearly in Table 2.
Security comparisons.

Security comparisons.
4.1. Security Analysis
As we all know for this area, there are a certain number of attacks [14, 15] and security issues to be ubiquitous and inevitable in wireless sensor networks. Then our proposed authentication scheme will be proved to be resistant to those most common attacks in Section 4.1.
Secrecy. Due to good protection for transmitted data, the resident data
Forward Secrecy. The data transmitted between applicant and decision maker is well protected so as to be obtained difficultly by the adversary from the transmission. To prove forward secrecy of our authentication scheme, we assume that the attacker compromises the decision maker and obtains the data in this decision maker. Let the decision maker's current data be
Resistance to Node Capture Attack. Sensor nodes in most applications are mostly deployed in public or hostile environment. Most nodes are low cost and not tamper resistant. Therefore, the adversary may have the capability of taking physical control of nodes undetectably and compromise the cryptographic keys. As a result, this type of attack [16–18, 30] is considered as the main threat and the resistance against node capture is regarded as an important criterion to protect the security of the network. The performance of the resistance toward node capture is evaluated in the work [30] by H. Chan, A. Perrig, and D. Song. They calculate the fraction of total network communications that are compromised by a capture of x nodes not including the communications in which the compromised nodes are directly involved. By utilizing this method, we could get the performance of our scheme's resistance against node capture. This metric shows our scheme's resistance against this attack is pretty good, because those nodes erase their master keys before the authentications begin and then the capture of nodes could not obtain any information, like mater keys and authentication keys of next cycle, about the links that are directly involved.
Resistance to Physical Attacks. In proposed scheme, nodes' master keys are erased after the deployment of the network. So there are no master keys in those nodes before the authentication phase. Sensor nodes deployed in public or hostile environment must be exposed easily to physical intrusion with the adversary. However, due to the erased master keys, those nodes are vulnerable to physical attacks [14, 15] and the information in them is unrelated to direct linked nodes.
Resistance to Replay Attack. In proposed scheme, both the decision-maker and applicant generate a random number during the authentication. The random number generated by node B is added to the session tokens
Resistance to Denial-of-Service Attack. This type of attack, which is described in works [19–22] in detail, is ubiquitous in wireless sensor network and proposed scheme has an effective resistance against this type of attack. The adversary will try to continue to send the request messages to the authenticators and receive the authenticators' response. But their goal of those actions is to use up the authenticators' energy and make the authenticators set cannot work normally. So those adversaries do not respond to the reply or supply the authenticators' incorrect replies after they request the authentication procession. If the authenticators could not have any measures to protect themselves and make the resistance to DoS attack, they will exhaust their energy and have no ability of working normally. The attack could be resistant by utilizing a timing controller to check the responding time. If an authenticator's reply has not be responded correctly in a certain time period, it is releasing this authentication procession, becoming a free authenticator again and available to other authentication claimants. The threshold of responding time could be updated according to the state of the in-progress attack. If the authenticator releases authentication procession to one claimant for a certain number of times, the claimant will be marked as untrusted user and could not be authenticated by the authenticators set in a future period.
Resistance to Impersonation Attack. The applicant node A and the decision maker B authenticate each other with the master key and authenticators. Only the legal applicant node A has master key and calculates the right authenticator and synchronizes its authenticator with node B. Meanwhile, only node A has the value of p and q and is able to obtain the correct x,
After the analysis is discussed, the comparisons in the security of our scheme are summarized with others in Table 1. It is concluded in Table 1 that security levels of our scheme and LWAS are highest, followed by LEAP and KMS. SPINS and BROSK schemes are in lowest security in the comparisons. In addition, our scheme has great resistance against impersonation attack and is more secure than LWAS scheme.
4.2. Performance Evaluation
The performance evaluation for wireless sensor network is very important due to sensor nodes' limited resource. So the analysis of energy consumption is key point in the performance evaluation for wireless sensor network.
As we all know, energy consumption of the security in wireless sensor network is mainly divided into two types: communication overhead and computation cost. However, it is concluded from previous and recent works that communication overhead plays a more important role in energy consumption than computation cost and accounts for a significantly larger part of energy consumption. For example, most of energy cost of adding SPINS protocol to wireless sensor network arises from communication and transmission overhead of extra data for security protocol rather than from computation cost. According to the work [8, 23], transmission cost is increased for SPINS protocol by 98%, while the MAC and encryption computation cost just only account for 2%. Thus, deceasing data transmission for security protocols and minimizing the communication overhead as soon as possible are one of the design goals for security protocols.
In this paper, the number of transmitted messages is utilized to make the evaluation of energy consumption, which is approximately equal to real energy consumption. We set the network in a certain area of 500 m × 500 m and deployed n sensors. Let us randomly select one node for analyzing the size of exchanged messages and estimating the communication overhead. At first, the lengths of different types of messages shall be defined:
Besides analyzing communication overhead of those protocols, computation cost is also a part of estimating energy consumption, which is listed in Table 2. From the result in Table 2, it is concluded that computation cost of SPINS protocol is lowest, followed by BROSK, LWAS, our proposal, and others because the nodes in SPINS protocol are just only needed to generate a nonce and other computations are done by a trusted third party. Summarizing the previously analysis, our proposal's energy consumption that is proportional to communication overhead is lower than others except LWAS protocol. In addition to lower energy consumption, guarantying the network scalable is also an important design goal. In SIPINS, pairwise keys are established by exchanging the messages with a trusted third party. Hence, the scale of the network in SPINS is not too large, or a lot of collisions will be generated in this network and the performance is degrading with the network running. Nodes in other protocols are only exchanging messages with neighboring nodes and are independent of network size. So proposed scheme scales very well with the size of the network and achieves good scalability for the network.
5. Conclusion
Being an important part of IoT, the security of wireless sensor networks should be focused on greatly. As wireless sensor networks are generally deployed in unsecured and untrusted areas, the transmitted data is vulnerable to all kinds of intrusions, like eavesdropping, interception, and modification. Those intrusions threaten the security and privacy of the users in the whole network and propose a great challenge for the development of wireless sensor network and IoT.
In this paper, our scheme is proposed to utilize the master key to achieve key management and the authentication operation based on quadratic residue for wireless sensor network, which is to provide the protection of the master key and offer the new users legal access to the network. It has a perfect resistance against those attacks which are of the most concern for WSN and achieves higher level of the security. Meanwhile, its energy consumption is in a lower position in comparison with other schemes. Therefore, it is concluded that our scheme achieves key management and node authentication, protects the node from a series of attacks which has reached a higher point in the security, and has very little increase in energy consumption.
Footnotes
Acknowledgments
This research is partly supported by National Natural Science Foundation of China under Grants 61071076, National High-Tech Research and Development Plans (863 Program) under Grants 2011AA010104-2, and the Academic Discipline and Postgraduate Education Project of Beijing Municipal Commission of Education.