Abstract
In the context of Internet of Things (IoT), multiple cooperative nodes in wireless sensor networks (WSNs) can be used to monitor an event, jointly generate a report and then send it to one or more Internet nodes for further processing. A primary security requirement in such applications is that every event data report be authenticated to intended Internet users and effectively filtered on its way to the Internet users to realize the security of data collection and transmission from the WSN. However, most present schemes developed for WSNs don't consider the Internet scenario while traditional mechanisms developed for the Internet are not suitable due to the resource constraint of sensor nodes. In this paper, we propose a scheme, which we refer to as Data Authentication and En-route Filtering (DAEF), for WSNs in the context of IoT. In DAEF, signature shares are generated and distributed based on verifiable secret sharing cryptography and an efficient ID-based signature algorithm. Our security analysis shows that DAEF can defend against node compromise attacks as well as denial of service (DoS) attacks in the form of report disruption and selective forwarding. We also analyze energy consumption to show the advantages of DAEF over some comparable schemes.
1. Introduction
To become an indispensable part of the Internet of Things (IoT), wireless sensor networks (WSNs) need to adopt IP technologies to create a seamless, global network infrastructure together with the Internet. To achieve this goal, many standardization organizations have been actively pursuing standardization work for creating a global sensor network infrastructure [1, 2]. In the context of the IoT, any IP-enabled node in the Internet shall be able to communicate directly with any remote sensor node in a WSN that is used to monitor specific events. Data transmission from any WSN node to any Internet node can be event-driven, whose scenarios include events that may be sensed sporadically by multiple cooperative sensor nodes when something happens, for example, when detecting fire or door-opening, or can be scheduled at predefined intervals, for example, reporting temperature every two hours. To monitor specific events of interest, more than one sensor node can be used to collect data and transmit it via multihop wireless paths to one or more Internet nodes to improve robustness, especially in an environment in which security threats resulting from internal and external attacks due to node compromises is a serious concern. Under such circumstances, it is still required that data report be sent to one or more of the intended Internet users as accurately as possible.
Since sensor nodes in a WSN may be deployed in an unattended environment, as shown in Figure 1, attackers can relatively easily compromise one or more sensor nodes so that they can be used to inject false event data (e.g., compromised node A can report false data for the event) or disrupt the transmission of legitimate event data (e.g., compromised node B can temper or even discard true data for the event within the multi-hop forwarding process). If undetected, such attacks can cause not only the generation of false alarms but also the depletion of limited energy in the sensor nodes. Moreover, Internet users may not be notified of a real event quickly and handle the event in time to avoid serious consequences. Therefore, it becomes imperative that security services such as data authenticity and availability be provided to resist such attacks.

Compromised nodes can inject false event data or disrupt the transmission of legitimate event data.
In many critical applications, the data that are collected by sensor nodes can also be sensitive. Therefore, it is important to ensure data authenticity to detect the report of false or nonexisting events. If a report for an event can be collectively endorsed by multiple sensor nodes, data authenticity can be ensured in the sense that a certain number of compromised nodes cannot collectively forge a report. That is, to forge a valid report for an event, a larger number of nodes have to be compromised.
Moreover, since denial of service (DoS) attacks can occur as the result of corrupted partial endorsements or discarded true data for the event, authentication alone may not be sufficient. It thus requires that data availability measures be employed in addition to those for authenticity to make the security measures highly resilient to DoS attacks. En-route filtering of false data is vital in saving scarce network resources and in prolonging the life of the network.
Consequently, to achieve security objectives, it is evident that authentication and efficient en-route filtering of data from WSN nodes to one or more Internet users be developed to detect false data injection and to fight against DoS attacks.
Traditional detection mechanisms developed for the Internet usually rely on infrastructure equipment (e.g., firewalls) to filter out distributed denial of service (DDoS) packets, which is deemed to be not adequate for WSNs due to the resource-constrained characteristics of sensor nodes as well as the lack of a comparable infrastructure in WSNs. Meanwhile, current detection mechanisms developed for WSNs rely primarily on the use of predistributed keys shared between sensor nodes and the sink node, which cannot be directly applied to the IoT scenario since the data of the event sensed by cooperative sensor nodes is sent only to one local sink rather than to one or more Internet users who are usually situated in different locations, even in different networks, and who may not be able to establish shared keys with every sensor node to authenticate the event data from a sensor node.
In this paper, we propose a data authentication and en-route filtering (DAEF) scheme to ensure the security of data collection and transmission from WSNs in the context of IoT. In DAEF, we make use of verifiable secret sharing cryptography to distribute the shares based on the most efficient ID-based signature scheme to multiple cooperative sensor nodes. In the case of a node compromise, with the tolerance of an adversary's compromising multiple neighboring nodes in the event area, the event report should be collectively generated, digitally signed, and forwarded to one or more of the intended Internet nodes through multipath routing. The main contributions of this paper are summarized as follows.
After identifying the security requirements on data collection and transmission from WSNs in the context of IoT, we propose a secure and efficient solution to deal with the security problems which have not been sufficiently dealt with in existing solutions.
We propose a data authentication and en-route filtering scheme, referred to as DAEF, without requiring the use of any preshared keys between the Internet users and the sensor nodes. Furthermore, not only can the scheme tolerate node compromise attacks, but it can also mitigate the impact of DoS attacks while minimizing energy consumption for the WSNs.
We analyze some exiting data en-route filtering mechanisms proposed for WSNs with respect to their characteristics and limitations and compare them with DAEF.
We illustrate how DAEF can be used as a secure and efficient mechanism to counter report disruption attacks to WSNs, a capability that we have not found so far in the literature.
We conduct performance comparison between DAEF and some comparable schemes to demonstrate DAEF's advantages over those schemes in terms of energy consumption, making DAEF suitable for WSNs.
The rest of this paper is organized as follows. In the next section, we review some related work on data authentication and en-route filtering. In Section 3, we present our proposed scheme, which includes assumptions, threat model and design goals, two preliminaries, and finally the procedure of the scheme. In Section 4, we analyze our proposed scheme in terms of security and performance and compare it to some comparable schemes. Finally, in Section 5, we conclude this paper in which we also discuss some future work.
2. Related Work
2.1. Authentication Frameworks for IoT
There are currently some authentication frameworks for data reports designed specifically for WSNs in the IoT scenario. Oliveira et al. proposed the Secure-TWS scheme to authenticate the communication from a single node to multiple users by using certificate-based signature in which the certification authority (CA) is part of the existing infrastructure in the Internet and, hence, is easy to provide since the Internet users only trust the CA and do not have to allow the CA to impersonate as themselves [3]. When the users receive a data report signed by a sensor node, they download the sensor node's public key and the corresponding certificate from the CA to authenticate the report using signature verification. Yasmin et al. proposed a framework for authenticated broadcast/multicast by the sensor node using the identity-based online/offline signature (IBOOS) scheme [4]. The offline phase performs most of the signature computations to calculate the partial signature which is stored on sensor nodes. Whenever a sensor node reports an event, it performs minor computations to obtain the final signature based on the partial signature stored on it.
The above two schemes can enable all sensor nodes in the WSNs to send messages to report critical situations and allow every node on the path from the sender node to the receiver users to verify and filter out false data as early as possible without using any shared keys. The computation overhead of the first scheme is lower than that of the second, but it requires higher communication cost due to the transmission of certificates.
However, these two schemes do not take into consideration of the existence of compromised nodes that may inject false event data as well as can disrupt the transmission of legitimate event data. Firstly, an event may be reported by a single sensor node which may have been compromised but not yet detected, the false report can get propagated to the users who may then mistakenly take incorrect measures. Secondly, should there be a compromised node in the routes to the Internet users, the users might be misled or might even not be able to receive any messages. Therefore, it is necessary to use multiple surrounding sensor nodes to collectively generate a legitimate data report which should also be forwarded to the Internet users via multipath routing.
2.2. Authentication Based on Symmetric Cryptography in WSNs
In WSNs, the problem of authenticating an event report collected by multiple sensors to the local sink node has attracted a great deal of attention in recent years [5–20]. Most of the schemes achieve the goals through using message authentication codes (MAC) based on symmetric keys. The basic idea is to attach MACs to the event reports and to ensure that a legitimate report must have a certain number of valid MACs. When the event report is forwarded to the sink along a routing path, intermediate nodes can detect and drop a forge report if it does not carry enough number of valid MACs. SEF [5] and IHA [6] are two such schemes for filtering injected false data in WSNs. SEF allows both the sink node and the en-route nodes to authenticate a report that has T MACs generated by a cluster attached to it with a certain probability by using the keys from different partitions in a global key pool. IHA verifies a report that has
2.3. Authentication Based on Asymmetric Cryptography in WSNs
Some asymmetric cryptographic schemes, such as CCEF [19], PDF [20], and LTE [22], that rely on signature approaches can enable any report, not just the report that is sent to the sink node, to be authenticated and en-route filtered. Moreover, they do not require any preshared keys. CCEF employs a commutative cipher based on public key cryptography filtering mechanism in which cluster nodes can establish a secret association with the sink on a per-session basis, while the en-route nodes are equipped with a witness key to be used to verify the authenticity of reports without knowing the original session key. PDF leverages Shamir's threshold cryptography and elliptic curve cryptography (ECC) to reject false data packets while LTE makes use of identity-based cryptography (IBC) based on bilinear pairing to bind the private key of each sensor node to both its identity and geographic location.
2.4. Critical Analysis and Comparison of Existing Schemes
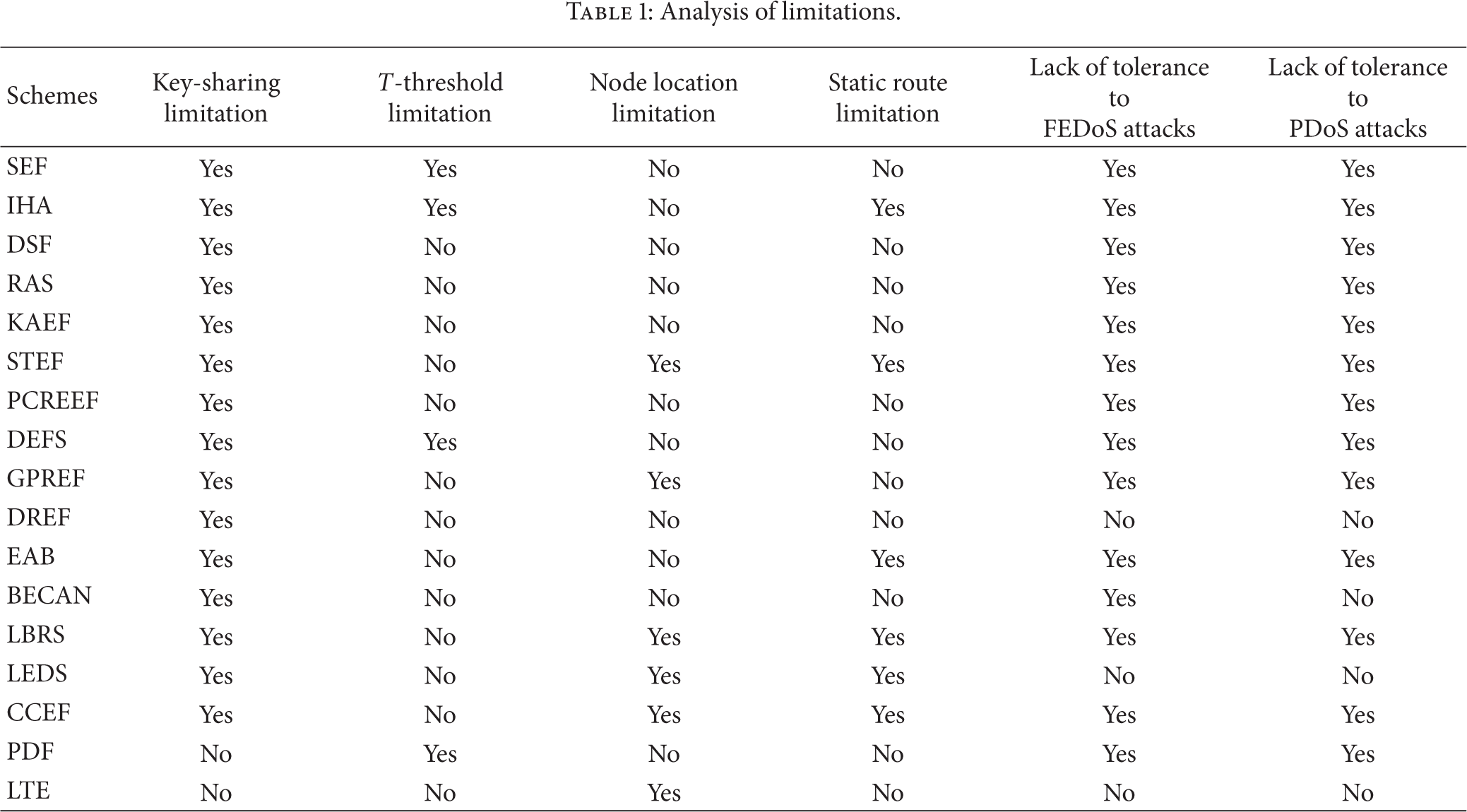
Although the existing schemes can effectively perform the functionality of authentication and false data report filtering, there are still some limitations in different aspects, such as key-sharing limitation, T-threshold limitation, node location limitation, static route limitation, lack of tolerance to report disruption attacks, lack of tolerance to selective forwarding attacks, to name a few. The notion of such limitations is discussed below.
Key-sharing limitation refers to the requirement that every node that generates a report must share key material with the sink.
T-threshold limitation refers to the situation in which the compromise of more than T-authentication partitions would put the whole WSN in danger. Such a limitation makes the network less resilient to the increase in the number of compromised nodes.
Node location limitation refers to the requirement that each node be equipped with GPS capability to locate itself since only rough estimation on the location can be achieved for sensor nodes that are not equipped with GPS.
Static route limitation refers to the reality in which reports get forwarded to a fixed sink along a preestablished path and each en-route node is associated with the source nodes in the event area.
Lack of tolerance to report disruption attacks refers to the situation in which intentional submission of corrupted partial MACs or signatures by compromised sensor nodes would disrupt the process of data filtering by some sensor nodes on the forwarding route, also called packet pollution attacks or false-endorsement based DoS (FEDoS) attacks [23].
Lack of tolerance to selective forwarding attacks refers to the situation in which one or more compromised forwarding sensor nodes can drop a legitimate report, also called path-based DoS (PDoS) attacks [24].
Table 1 provides an analysis on the limitations of some of the main existing schemes. We can see from the table that all symmetric key-based schemes exhibit the key-sharing limitation since it is practically infeasible for every remote user to establish a shared key with each and every one of the sensor nodes. Therefore, these symmetric keys based schemes are not suitable for WSNs in the context of IoT. A result, only PDF and LTE that are asymmetric cryptography-based signature schemes can be used for event data authentication and filtering in the IoT scenario. However, PDF suffers from the vulnerability of both report disruption attacks and selective forwarding attacks. Only DREF, LEDS, and LTE can resist report disruption attacks and selective forwarding attacks that result from node compromises in the event area and from the use of a single route from a sensor node to the sink node. The result of the analysis shows that only LTE is applicable to the IoT scenario and can provide some level of tolerance to both types of DoS attacks. Therefore, we will compare our proposed scheme in terms of performance only to LTE at the same security level.
Analysis of limitations.
2.5. Location-Based Threshold-Endorsement (LTE) Mechanism
Due to its functional capability as well as its applicability to the IoT scenario, we would like to elaborate a little more on the LTE scheme. In LTE, the sensor network is divided into
An event occurs in cell

If the check succeeds, AP considers node
AP then sends to the sink the final report along a multihop path discovered using a secure multipath routing protocol. Upon receiving a report

where
However, LTE is not always feasible because it requires that every sensor node be equipped with localization capability, which incurs extra communication overhead as well as latency. Moreover, the bilinear pairing utilized in LTE is too expensive for low energy sensor nodes. In LTE, a data report must be cosigned by t out of T nodes (
3. The Proposed Scheme
In this section, we describe the proposed DAEF, a data authentication and en-route filtering scheme, that can be used to ensure the security of data collection and transmission from WSNs in the context of IoT. In applications to which DAEF can be applied, we assume that a group of sensor nodes are used to monitor an event. In the proposed DAEF, a group ID-based signature is introduced for each event report so that any intermediate node and any Internet user with the identity of the group lead node can easily verify the event report, which easily removes the key-sharing and the T-threshold limitations, while realizing T-authentication to tolerate node compromise attacks without requiring static route and node localization technology. DAEF also employs the verifiable secret sharing algorithm to distribute and verify signature shares in order to defend against report disruption attacks. Last, but not the least, we employ the most efficient ID-based signature algorithm in DAEF to reduce computation overhead that results from signature generation and verification operations. Moreover, a multi-path routing protocol should be used in DAEF to resist selective forwarding attacks.
3.1. Assumptions
We assume that all the sensor nodes in WSNs are deployed uniformly and bootstrapped securely using the scheme proposed in [25] so that the one-hop neighboring sensor nodes can establish pairwise keys and trust relationships to form a network with multi-hop cluster-tree hierarchical topology. Each node establishes and stores a neighbor trust list as shown in Figure 2. We also assume that every event of interest can be detected by multiple, say

Neighbor trust list: neighbor ID is the ID of the node's neighbor; short address is the short address of the node's neighbor; shared key is the pairwise key shared between the node and its neighbor; relationship points that the neighbor is the node's father, child, sibling, and so on; hop count is the distance between the node and the edge route, trust value is the computed result making use of the utility value method in a multiple criteria decision making scheme.
Moreover, we assume that the Internet users are determined by the service provider (SP) based on the service provided by the sensor nodes. Take the smart home applications as an example, the detection of fire in a home should be reported to the family members, security guards of the community, and the fire department, while the temperature in the home may be reported to all family members every two hours. The corresponding software code can be preloaded in the sensor nodes prior to deployment. Furthermore, the code can be dynamically updated by using an end-to-end secure communication protocol (referring to [26]).
3.2. Threat Model and Design Goals
An adversary can eavesdrop on all traffic, inject packets, replay older packets, and take full control of the compromised nodes to launch false report injection attacks and DoS attacks. In our model, we assume that most T-
It should not require the establishment of preshared keys between Internet users and sensor nodes (to overcome the key-sharing limitation).
It should not depend on the localization technology to prevent compromised nodes from breaking the whole WSN (to overcome the T-threshold limitation).
It should tolerate node compromises in the WSNs even if the locations of the sensor nodes may not be known (to overcome the node location limitation).
It can mitigate the impact of DoS attacks including report disruption attacks and selective forwarding attacks (to overcome the FEDoS and PDoS attacks).
It should keep the overhead of communication and computation as low as possible in the WSNs.
3.3. Preliminaries
3.3.1. ID-Based Signature
As discussed above, ECC-based signature (i.e., ECDSA) requires one point multiplication operation to generate a signature and two point multiplication operations to verify a signature. Moreover, authentication of the public key of the signer also requires two point multiplication operations. For an ECC of 160 bites, ECDSA produces a 60-byte signature, resulting in more than a 160-byte message payload (including a 60-byte ECDSA signature and a certificate with at least 100 bytes). With the current state of the art technology, the most efficient ID-based signature (i.e., vBNN [27]) needs one point multiplication operation to sign a message and three point multiplication operations to verify the signature with the length of a signature being 83 bytes. Let us briefly describe the vBNN scheme below.
Given a sensor node
Given a message
Choose a random number
Compute
The signer then sends
Compute
Check the equation
3.3.2. Verifiable Secret Sharing
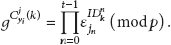
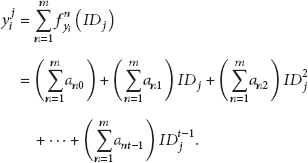
Sensor node
3.4. The Data Authentication and Filtering Scheme
3.4.1. Initialization
During the bootstrapping phase, the lead node in every group distributes the secret share of
3.4.2. Report Generation
When an event occurs, the lead node will prepare a report, say, E. To get an agreement on the event from other group nodes, the lead node

Note that the distribution of secret shares should be protected using the shared keys between the communicating peers. Therefore, each node will receive no less than
During the verification phase, a compromised group member may be detected. If
The secret random number

Each legitimate neighboring node
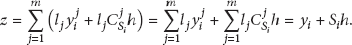
Finally,
for (each sensor for (each sensor for (each sensor
3.4.3. En-Route Filtering of Data Report
We denote

4. Analysis
4.1. Security Analysis
4.1.1. Resilience to Node Compromise Attacks
DAEF uses the threshold signature generation to sign any event report. The attacker must know the private key
4.1.2. Mitigation of Report Disruption Attacks
DAEF leverages verifiable Shamir's secret sharing cryptography described in Section 3.3.2 which has been shown to be secure [28]. In the report generation phase, at least t legitimate sensor nodes cooperatively generate the secret random number
4.1.3. Mitigation of Selective Forwarding Attacks
In DAEF, in order to mitigate selective forwarding attacks, the lead node and the intermediate nodes would forward the final report
4.2. Performance Analysis
In this section, we evaluate the performance of DAEF in terms of filtering efficiency, the number of hops that false data can travel, and the ratio of compromised area, which are the main metrics for the evaluation of en-routing filtering schemes [30]. We also analyze and compare DAEF to LTE in terms of computation, communication, and energy consumption. We conducted all experiments in the analysis, evaluation, and comparison by using MATLAB [31] plus some programming in VC++ whenever necessary.
4.2.1. General Analysis
First, let us analyze filtering efficiency
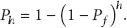
Clearly, the greater the value of
The filtering efficiency with different
The number of hops that false data can travel
The ratio of compromised area

Let
Therefore, the percentage of compromised nodes is

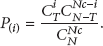
Figure 4 shows the resilience as the number of compromised nodes increases. We can observe that the percentage of compromised groups increases very slowly with an increasing number of compromised nodes when less than 20% of all the nodes are compromised. Even if the number of compromised nodes reaches 200, only 10% of groups are compromised in all the cases except (

The percentage of compromised groups with the increased number of compromised nodes when
4.2.2. Comparison Analysis
We analyze DAEF and LTE in terms of computation cost and communication overhead and then compare them in terms of energy consumption to show the advantages that DAEF has over LTE.
First, we perform the analysis on computation cost. In all the schemes, expensive operations are normally pairing (
For communication overhead, which is defined as the total number of messages generated in an event group, in DAEF, the T sensor nodes have to jointly generate a random number
Note that in the above analysis, we assume that there is no compromised node in any of the event groups. Let us now analyze and compare DAEF to LTE in terms of energy consumption for the whole WSN under the assumption that there is at least one compromised node in an event group at the time of reporting an event, for these two schemes offer a similar level of security and both can deal with report disruption attacks and selective forwarding attacks.
We employ the similar model to LTE when performing analysis and comparison on energy consumption which is determined by communication overhead as well as computation cost. We assume that the sensor nodes have the same capabilities as those of a standard Crossbow's MICA2 mote [32] which has 8-bit ATmegal 128L clocked at about 7.37 MHz microcontroller and complies with the IEEE 802.15.4 standards with data transmission rate of 12.4 kbps. According to [4], completing a 160-bit point multiplication operation of ECC, a pairing operation, and an exponentiation operation consumes 24.3 mJ, 62.73 mJ and 2.81 mJ, respectively. In addition, MICA2 consumes 52.2 μJ, and 19.4 μJ to transmit and to receive one byte, respectively. We assume that the length of the node's ID is 2 bytes, making the lengths of
In the analysis, we specify (
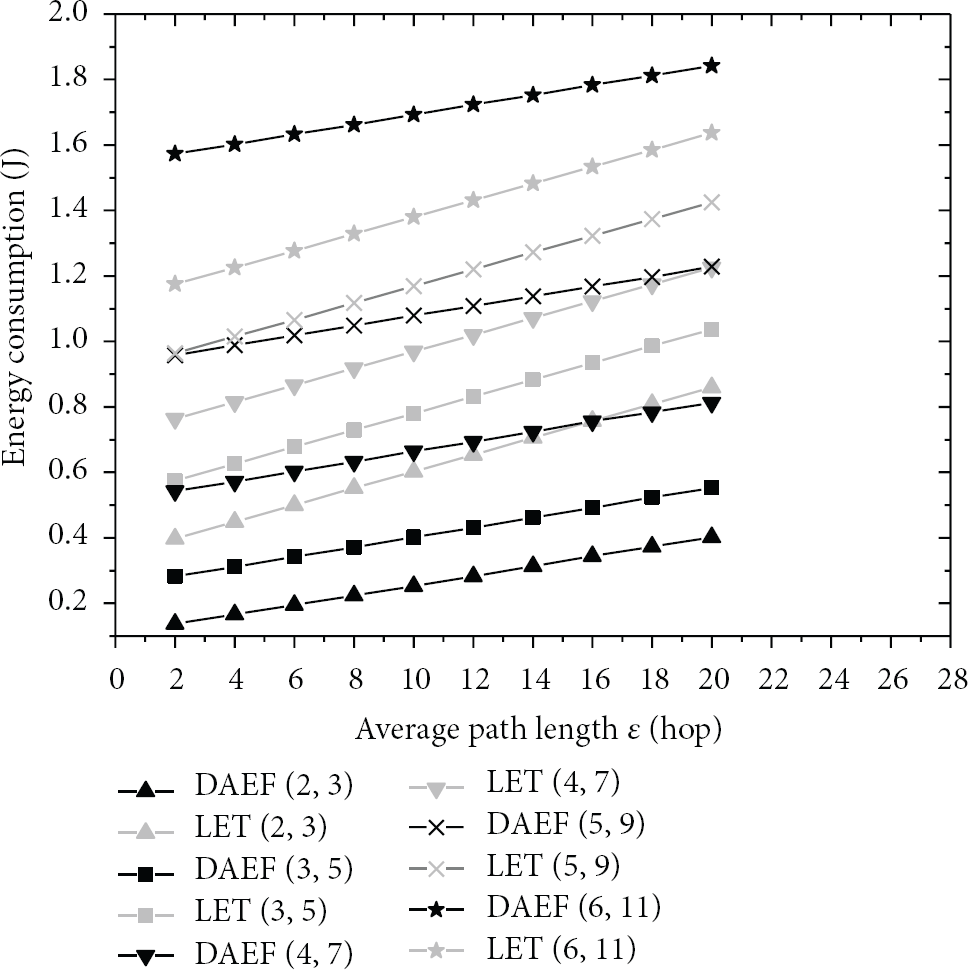
Energy consumption for various ε when
Figure 6 shows the energy consumption for various

Energy consumption for various
Figure 7 shows the energy consumption as the number of compromised nodes increases in an event group when

Energy consumption with an increasing number of compromised nodes for various (
Figure 8 shows the energy consumption for various parameter t when

Energy consumption for various t when
In conclusion, DAEF outperforms LTE for data authentication and en-route filtering when an event group has a smaller number of nodes and larger number of compromised nodes.
5. Conclusion
In this paper, we proposed DAEF, a new data authentication and filtering scheme, to ensure the security of data collection and transmission from WSNs in the context of IoT. In the scheme, the verifiable secret sharing cryptography is used for the distribution of the shares to multiple neighboring collective sensor nodes based on the most efficient ID-based signature scheme. As long as an adversary does not compromise more than
Footnotes
Acknowledgments
The work in this paper has been supported by funding from National Natural Science Foundation of China (61272500) and from Beijing Education Commission Science and Technology Fund (KM201010005027).
