Abstract
The eavesdropping attack is a serious security threat to a wireless sensor network (WSN) since the eavesdropping attack is a prerequisite for other attacks. Conventional WSNs consist of wireless nodes equipped with omnidirectional antennas, which broadcast radio signals in all directions and are consequently prone to the eavesdropping attacks. Different from omnidirectional antennas, directional antennas radiate radio signals on desired directions and potentially reduce the possibility of the eavesdropping attacks. In this paper, we propose a model to analyze the eavesdropping probability in both single-hop WSNs and multihop WSNs with omnidirectional antennas and directional antennas. We verify the correctness of our analytical model by conducting extensive simulations. We have found that using directional antennas in either single-hop WSNs or multihop WSNs can significantly reduce the eavesdropping probability. The reason of the improved security of WSNs with directional antennas lies in (i) the smaller exposure region of a directional antenna and (ii) the fewer hops to route a packet due to the longer transmission range of a directional antenna. Our results have also shown that the security improvement factor heavily depends on the node density, the antenna beamwidth, and the signal path loss factor.
1. Introduction
Recently, wireless sensor networks (WSNs) have received enormous interests from both industry and academia [1]. WSNs have been used in environmental monitoring, health care, surveillance security, farming, and so forth. Many studies assume that sensor nodes are deployed in random from an airplane. Those scatted sensor nodes self-organize to form an ad hoc network, in which data packets are transmitted through multihops from the source node to the destination node.
In WSNs, any wireless node residing in the transmission range of the transmitter can potentially decode the signal when both the transmitter and the receiver are unaware of the reconnaissance [2]. The reconnaissance, also named the eavesdropping activity, has attracted considerable attentions recently since many adversary attacks often follow the eavesdropping activity, for example, hear-and-fire attacks [3]. Specifically, there are two types of eavesdropping attacks in WSNs [4]: (i) Passive Eavesdropping, in which the malicious nodes detect the information by listening to the message transmission in the broadcasting wireless medium; (ii) Active Eavesdropping, where the malicious nodes actively grab the information via sending queries to transmitters by disguising themselves as friendly nodes. The study on the passive eavesdropping attacks is often more important than that on the active eavesdropping attacks since the malicious nodes must have the knowledge of the friendly nodes via conducting passive eavesdropping activities before they can actively attack the friendly nodes. Thus, we only consider the passive eavesdropping attacks in this paper.
Conventional WSNs typically consist of nodes equipped with omnidirectional antennas which broadcast radio signals uniformly in all directions. Only a portion of these signals can reach the destinations and most of them are lost. This property of radiating signals omnidirectionally inevitably leads to high interference and a short transmission range. Both these two factors severely limit the network performance of WSNs equipped with omnidirectional antennas. We call such networks as wireless omnidirectional sensor networks (WONs).
Compared with omnidirectional antennas, directional antennas can concentrate most of radio signals on desired directions. In other undesired directions, there are no radio signals or the weakened signals. Therefore, using directional antennas in WSNs can potentially reduce the interference [5]. Besides, the transmission range can be significantly extended compared with omnidirectional antennas. We call such networks as directional-antennas wireless sensor networks (DAWNs).
1.1. Contributions
In this paper, we only concentrate on the passive eavesdropping attack in WONs and DAWNs. We have found that using directional antennas in WSNs can significantly improve the network security in terms of reducing the eavesdropping probability in both single-hop networks and multihop networks. Our contributions are summarized as follows.
The first contribution of this paper is to formally establish the eavesdropping model in WSNs with consideration of omnidirectional antennas and directional antennas. In particular, we propose the exposure region to determine whether an adversary node can eavesdrop the transmission or not. We also define the eavesdropping condition, the single-hop eavesdropping probability, and the multihop eavesdropping probability.
Secondly, we analyze the eavesdropping attacks in both single-hop networks and multihop networks with both omnidirectional antennas and directional antennas. We have found that a DAWN has a much lower eavesdropping probability than a WON in either single-hop networks or multihop networks. The security improvement of directional antennas owes to the smaller exposure region and the fewer hops to route a packet.
Last, we conduct extensive simulations to verify the correctness of our analytical models. We show that the simulation results exactly agree with our analytical model in both single-hop WONs and single-hop DAWNs. We also show that both the simulation results and the analytical results in multihop networks keep the same trend in the eavesdropping probability although there exist quite small gaps between them. We have found the reasons behind this effect and pointed out the future direction.
The remainder of the paper is organized as follows. Section 2 presents the models and the definitions. In Section 3, we analyze the eavesdropping attack in single-hop networks. Section 4 presents the analytical results of the eavesdropping attach in multihop networks. We then discuss the simulation results in Section 5. Section 6 reviews the related work. Finally, we conclude the paper in Section 7.
2. Models and Notations
We adopt the notations shown in (Notation) throughout the paper. Sections 2.1 and 2.2 present the directional antenna model and the transmission model, respectively. In Section 2.3, we propose an eavesdropping model to analyze the eavesdropping attacks.
2.1. Antenna Model
In this paper, we consider a directional antenna model that was used in previous studies [6–11]. This model can simplify our analysis. The reasons why we choose the model are summarized as follows. Firstly, even in a more realistic model, the sidelobes and backlobes are so small that they can be ignored. For example, in a more realistic model (the cone-sphere model) [12] in which the sidelobes and backlobes are counted, the gain of the main lobe is more than 100 times of the gain of the sidelobes. Secondly, smart antennas often have null capability that can almost eliminate the sidelobes and backlobes.
We assume that a directional antenna gain

The antenna model.
The antenna gain of an omnidirectional antenna can be regarded as a special case in our model when the beamwidth
Note that a directional antenna generally has a beamwidth
2.2. Channel Model
We next describe the channel model. We denote the transmission power of node i by
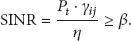
The transmission from node i can be successfully received by node j if and only if
where β is the minimum signal to interference and noise ratio and η is the environmental noise power level, which is assumed to be the same for all nodes.
Note that there are only one transmitter and one receiver in a single-hop network and all other nodes are adversary nodes, which are passive eavesdroppers and will not transmit actively. In a multihop network (see Section 4), there are N good nodes and M passive adversary nodes, which will not transmit actively. Besides, we also assume that only one of all the N good nodes can transmit at a time. Based on these assumptions on a single-hop network and a multihop network, we can concentrate our analysis on the eavesdropping attacks and ignore the interference from other nodes. Therefore, we have
In this paper, we consider the large-scale path loss in the channel model [13]. Thus, the channel gain is given by
where
Note that the channel model also holds for both the normal transmission and the eavesdropping attack. When the channel model is used for the normal transmission,
2.3. Eavesdropping Model
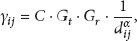
We next formally propose our eavesdropping model. First, we map WONs and DAWNs to the following two cases, which are summarized in Table 1.
Directional case and omnidirectional case.
In Case I (Omnidirectional), the transmitters, the receivers, and the adversary nodes use omnidirectional antennas (Omni for short). The Omnidirectional case corresponds to a WON. In Case
Second, we analyze the channel model for the eavesdropping attacks. If an adversary node can correctly decode the information from the transmitter, the SINR at the adversary node must satisfy the condition given in Inequality (4). After combining Inequality (4) and (5), we have

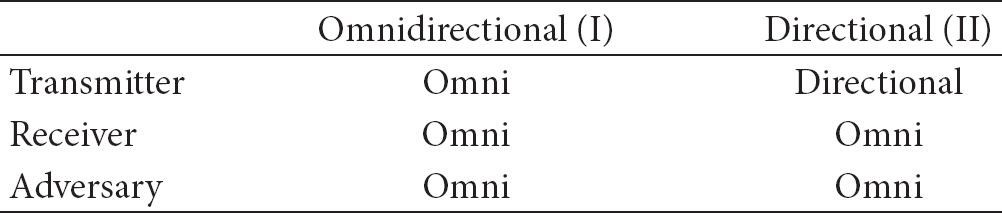
We denote the right-hand side (RHS) of (6) as
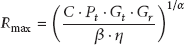
which is the maximum radius within which an adversary node can correctly eavesdrop the information from the transmitter.
We then define the exposure region as follows.
Definition 1 (exposure region).
The exposure region of a transmitter is an area that any adversary nodes within this area can potentially eavesdrop the transmission from the transmitter.
It is obvious that the area of the exposure region is determined by the geometric shape of the exposure region and the maximum radius
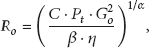
where
In Case

where
Note that both the receiver and the adversary nodes have the same minimum SINR (i.e., β) to decode the information to the transmitter. Figures 2 and 3 illustrate the exposure regions of a directional antenna and an omnidirectional antenna, respectively.
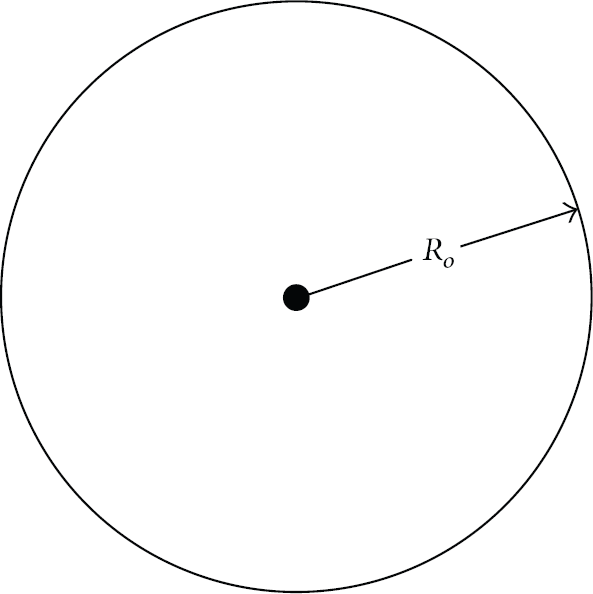
The exposure region of an omnidirectional antenna.
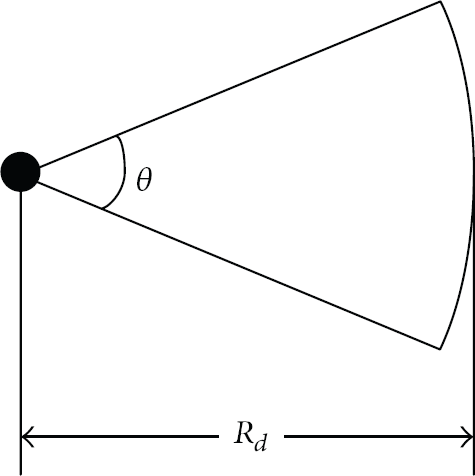
The exposure region of a directional antenna.
We then define the eavesdropping condition as follows.
Definition 2 (eavesdropping condition).
An adversary node can successfully eavesdrop the information from the transmitter if and only if the adversary node falls into the exposure region of the transmitter.
To evaluate the seriousness of eavesdropping attacks, we define the eavesdropping probability
Definition 3 (single-hop eavesdropping probability).
The eavesdropping probability
Definition 4 (multihop eavesdropping probability).
The eavesdropping probability of a multihop transmission is the probability that at least one-hop transmission is eavesdropped.
It is obvious that
Definition 5 (security improvement factor).
The security improvement factor
When
Finally, we describe the node distribution. In this paper, we consider that both the adversary nodes and the good nodes are distributed in a two-dimensional plane. We use a Poisson point process to model the distribution of the nodes [14]. In particular, the probability

where
3. Security Analysis on Single-Hop Networks
In this section, we analyze the eavesdropping probabilities of Omnidirectional case and Directional case in single-hop networks, in which all packets are transmitted through only one hop.
3.1. Eavesdropping Probability of WSNs
Generally, the eavesdropping probability of a single-hop WSN can be obtained by the following lemma.
Lemma 6.
The eavesdropping probability can be calculated by

Proof.
From the definition of the eavesdropping probability, that is, Definition 3, we have

where i denotes the number of adversary nodes falling into the exposure region of a transmitter.
Since the distribution of adversary nodes follows Poisson point process as defined in (10), we then have

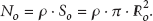
As shown in Lemma 6, to determine the eavesdropping probability, we need to calculate the area of the exposure region S first. We then calculate the exposure region S under the Omnidirectional case (WONs) and the Directional case (DAWNs), respectively.
In Omnidirectional case, the transmitter, the receiver, and the adversary nodes are equipped with omnidirectional antennas. The exposure region of an omnidirectional antenna is a circle with radius

where
In Directional case, the transmitter is equipped with a directional antenna while eavesdroppers are equipped with omnidirectional antennas. The exposure region of a directional antenna is a sector with radius

where
After replacing S in (11) by
Lemma 7.
The eavesdropping probability of the Omnidirectional case, denoted by

The eavesdropping probability of the Directional case, denoted by

3.2. Comparison between WONs and DAWNs under Single-Hop Networks
To simplify the analysis, we define the reference node density
We then have the following theorem to compare a WON with a DAWN in terms of the security improvement factor.
Theorem 8.
The security improvement factor of a WON over a DAWN is equal to

Proof.
From the definition of security improvement factor, that is, Definition 5, we have

where
Replacing

We then analyze the security improvement factor of a WON over a DAWN. In particular, we have the following.
Corollary 9.
DAWNs have the eavesdropping probability no higher than that of WONs under the same network settings. More precisely, one has the following.
When the pass loss factor When the pass loss factor
We then calculate the security improvement factor
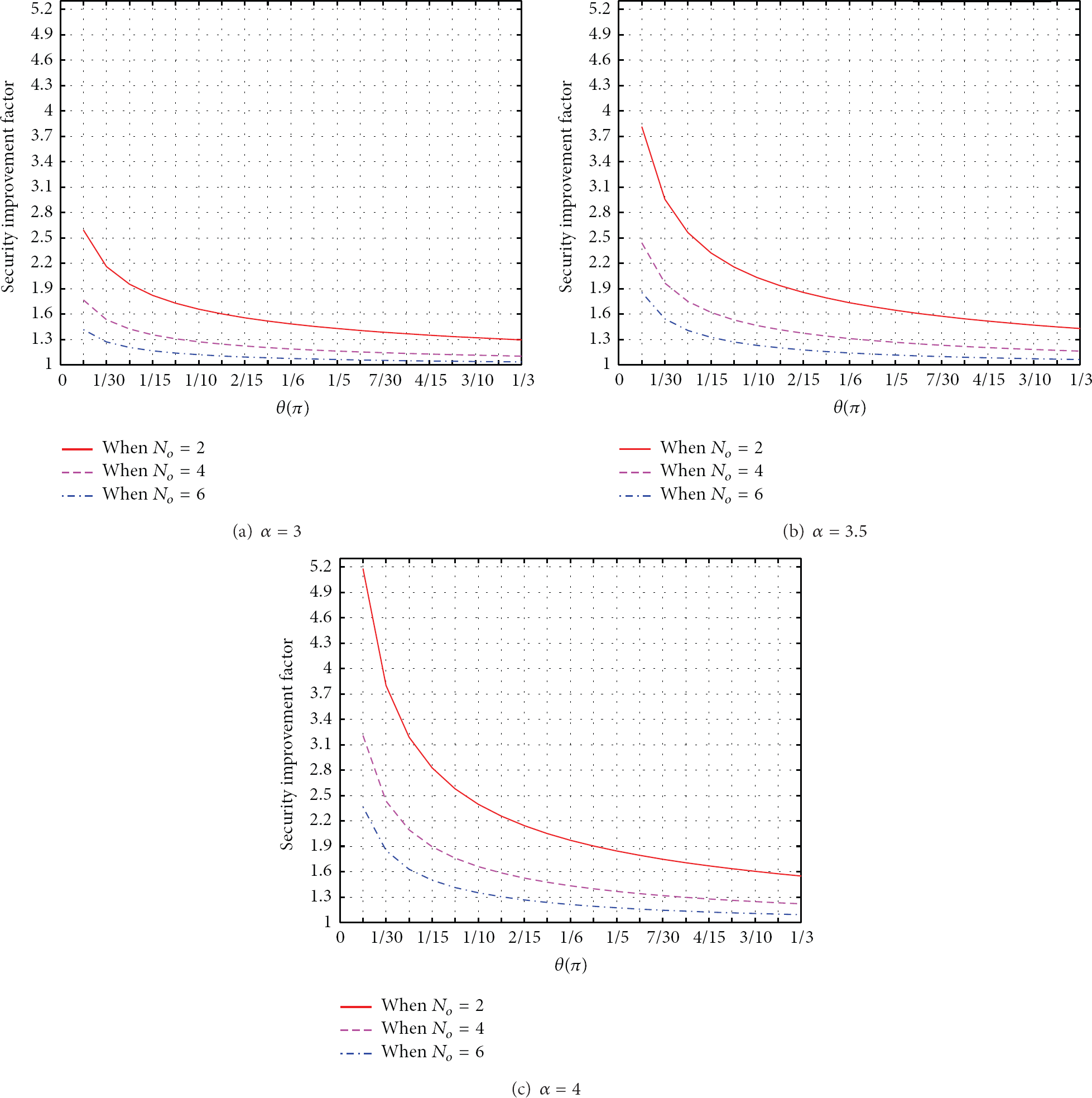
Security improvement factor of single-hop transmissions.
It is shown in Figures 4(a), 4(b), and 4(c) that the security improvement factor
Besides, it is also shown in Figure 4 that with the increased node density
Moreover, Figure 4 also shows that the security improvement factor
4. Security Analysis on Multihop Networks
In this section, we extend our analysis from single-hop networks to multihop networks. We first derive the eavesdropping probability of multihop transmissions. Then, we analyze the security improvement factor of WONs over DAWNs under multihop networks.
4.1. Routing Path in Multihop Networks
To analyze the eavesdropping probability of multihop transmissions, we construct a simple routing scheme that chooses a route with the shortest distance to forward data packets. We first introduce the Source-Destination (S-D) Line model [3, 15].
In the S-D Line model, we divide the unit-area plane into a lot of equal-sized square cells as shown in Figure 5. Each of them has an identical area of

The S-D Line model.
In this S-D Line model, we directly draw a line to connect a source node S and its destination node D. Then, node S will send data packets to its destination D by multihop forwarding those packets along the cells lying on its S-D line. Figure 5 shows an example of S-D lines, where the green line indicates a S-D Line. In the case of WONs, the packets are forwarded along the adjacent cells lying on the S-D line. For example, the red line as shown in Figure 5 denotes the routing path from S to D in a WON. However, the cells lying on the S-D line in a DAWN are not necessary to be adjacent since a directional antenna has a longer transmission range than an omnidirectional antenna. As shown in Figure 5, only 3 hops are needed from S to D, compared with the omnidirectional antenna case, which requires 7 hops from S to D. Therefore, using directional antennas can potentially reduce the number of hops.
We then calculate the number of hops required to route a packet from S to D. Since calculating the exact number of hops is difficult, we are only concerned about the number of hops H from S to D. In the S-D line model, the number of hops depends on both the length of the S-D line l and the transmission range of each hop, which is
We next calculate the number of hops

where
Similarly, the number of hops

where
4.2. Eavesdropping Probability of Multihop Networks
In general, the eavesdropping probability of a multihop WSN (either WON or DAWN) can be obtained by the following lemma.
Lemma 10.
The eavesdropping probability of multihop networks can be calculated by
where H is the number of hops and
Proof.
From the definition of the eavesdropping probability of multihop networks, that is, Definition 4, we have

Note that we assume that each hop has the same eavesdropping probability.
For a WON, since

For a DAWN, since

From (24), we have found that with the increased number of hops H, the multihop eavesdropping probability also significantly increases. Since directional antennas have a longer transmission range than omnidirectional antennas, that is,
4.3. Comparison between WONs and DAWNs under Multihop Networks
We then have the following theorem to compare a WON with a DAWN in terms of the security improvement factor under multihop networks.
Theorem 11.
The security improvement factor of a WON over a DAWN under multihop networks is equal to

Proof.
From the definition of security improvement factor, that is, Definition 5, we have

After replacing

Note that when
We then calculate

The security improvement factor of multihop transmissions.
Two factors contribute to the increment of the security improvement of multihop transmissions:
Moreover, it is also shown in Figure 6 that there is a higher multihop security improvement factor
In addition, different from the single-hop networks, the security improvement
5. Empirical Results
In this section, we conduct extensive simulations to evaluate the correctness and the accuracy of our proposed models in single-hop networks (Section 5.1) and multihop networks (Section 5.2). In the simulations, both adversary nodes and good nodes are randomly distributed on a plane of area
5.1. Single-Hop Networks
Figure 7 shows the eavesdropping probability versus node density when

Eavesdropping probability versus node density
As shown in Figures 7(a) and 7(b), the simulation results almost exactly match the analytical results in all cases. Besides, it is shown in Figures 7(a) and 7(b) that the eavesdropping probability increases when
Moreover, we can see in Figure 7 that a DAWN always has the lower eavesdropping probability than a WON in all cases, which further confirms our earlier observations in Section 3. In other words, using directional antennas in wireless networks can potentially improve the security. In addition, when α is fixed, we can see that the eavesdropping probability decreases with the increased beamwidth θ. It implies that a narrower-beam antenna can potentially reduce the eavesdropping probability and further improve the security of transmissions.
Furthermore, we can also see that the eavesdropping probability of a DAWN significantly drops with the increased path loss factor α (e.g., α increases from 3 in Figure 7(a) to 4 in Figure 7(b)) while α just slightly affects the eavesdropping probability of a WON. It is shown in [13] that the path loss factor α is generally greater than 3 in urban outdoor environments. Therefore, using directional antennas in such environments may bring more benefits on reducing the eavesdropping probability than using omnidirectional antennas.
5.2. Multihop Networks
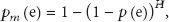
Tables 2 and 3 show the eavesdropping probabilities under multihop networks when
Eavesdropping probability versus node density
Eavesdropping probability versus node density

Both Tables 2 and 3 show that a WON has much higher eavesdropping probability than a DAWN when
As shown in Tables 2 and 3, the eavesdropping probability
Besides, Tables 2 and 3 also show that the narrower the beamwidth θ is, the smaller the eavesdropping probability
There exist quite small gaps between the analytical values and the simulation results as shown in Tables 2 and 3 though both of them have the same trend. More precisely, as shown in Tables 2 and 3 that the analytical values are always greater than the simulation results in a WON while the analytical values are always smaller than the simulation results in a DAWN. This effect may owe to two factors:
6. Related Work
Wireless Sensor Networks (WSNs) are prone to the malicious attacks due to the shared wireless medium, the multihop transmissions, and the decentralized control scheme [2, 18–20]. In a WSN, any wireless node residing in the transmission range of the transmitter can potentially decode the signal when both the transmitter and the receiver are unaware of the reconnaissance. Besides, it is also difficult to implement the centralized control mechanisms in WSNs. Furthermore, multihop communications are also suggested in WSNs to reduce the interference and to improve the network capacity [21]. However, the multihop communication is vulnerable to the malicious attacks.
One of the malicious attacks, namely, the eavesdropping attack, has attracted considerable attentions recently since many other malicious attacks often follow the eavesdropping activity. As summarized in [4, 18], there are two types of eavesdropping attacks in WSNs: passive eavesdropping and active eavesdropping. The study on the passive eavesdropping attacks is often more important than that on the active eavesdropping attacks since it is a prerequisite that the malicious nodes have the knowledge of the good nodes via conducting passive eavesdropping activities.
There are a number of studies on investigating the passive eavesdropping attack [2–4, 18]. But, most of them considered a WON, in which each node is equipped with an omnidirectional antenna, which radiates the radio signals in all directions and consequently is more prone to the eavesdropping attacks. Compared with omnidirectional antennas, directional antennas can concentrate radio signals on desired directions. In other undesired directions, there are no radio signals or weakened signals. Thus, using directional antennas in WSNs can potentially reduce the interference and consequently improve the network performance.
There are a number of studies on using directional antennas in wireless ad hoc networks. The first category of them mainly focuses on the theoretical analysis on the network performance, for example, the network capacity and the transmission delay. In particular, studies [6, 22, 23] derived the approximated network capacity of wireless networks with directional antennas, in which each node is equipped with only one directional antenna and only one channel is used. More specifically, Yi et al. [6] show that using directional antenna in arbitrary networks achieves a capacity gain of
Most of the above studies focus on improving the network performance by using directional antennas. However, there is little work on the security issue by using directional antennas. The study [38] is one of the earliest studies on exploring using directional antennas in wireless networks to improve the network security. It is shown in [38] that using directional antennas can significantly reduce the average detection probability compared with using omnidirectional antennas. However, their studies only analyze single-hop multihop transmission and do not consider other benefits of directional antennas, such as the longer transmission range, which may reduce the number of hops and consequently improve the security further.
7. Conclusion
In this paper, we have explored using directional antennas in wireless sensor networks to improve the network security in terms of reducing the eavesdropping probability. In particular, we analyzed the eavesdropping probability of single-hop networks and that of multihop networks. We have found that using directional antennas in either a single-hop network or a multihop network can significantly reduce the eavesdropping probability. The security improvements of using directional antennas owe to the smaller exposure region and the fewer hops due to the longer transmission range. Besides, we also derived the security improvement factors of single-hop transmissions and multihop transmissions. We have found that both the single-hop security improvement factor and the multihop security improvement factor heavily depend on the antenna beamwidth, the node density, and the path loss factor. It is shown that using a narrow beam antenna can significantly improve the network security by reducing the eavesdropping probability.
There are some interesting topics in the eavesdropping activities of DAWNs. For example, most of current studies always assume that the adversary nodes are uniformly and randomly distributed in the networks. What about the eavesdropping probability if the distribution of the adversary nodes is non-uniform and deliberate? Besides, does the power control schemes will affect the eavesdropping probability of a DAWN?
Footnotes
Notations
Acknowledgments
The work described in this paper was supported by Macao Science and Technology Development Fund under Grant no. 036/2011/A and Grant no. 081/2012/A3. The authors would like to thank Guodong Han and Qinglin Zhao for their valuable comments.