Abstract
We consider the collaborative use of amplify-and-forward relays to form a beamforming system and provide physical layer security for a wireless machine-to-machine (M2M) communication network. We investigate two objectives: (i) the achievable secrecy rate maximization subject to the relay power constraint and (ii) the relay transmit power minimization under a secrecy rate constraint. For the first objective, we propose a secrecy rate maximization (SRM) beamforming scheme. The secrecy rate maximization problem can be formed into a two-level optimization problem and we solve it using semidefinite relaxation (SDR) techniques. To reduce the complexity of the SRM beamforming scheme, a virtual eavesdropper-based SRM (VE-SRM) beamforming scheme is proposed, in which we hypothesize a virtual eavesdropper instead of all eavesdroppers and maximize the secrecy rate according to the virtual eavesdropper. In addition, for the second objective, we design a relay power minimization (RPM) beamforming scheme, in which an iterative algorithm combining the SDR technology and the gradient-based method is devised by studying the convexity of the RPM problem. By relaxing the constraints of the RPM beamforming scheme, we propose a virtual eavesdropper-based RPM (VERPM) beamforming scheme, which reduces the multivariate RPM problem to a problem of a single variable, and thus an analytical solution is obtained. Our proposed beamforming designs can work well even if the number of eavesdroppers is larger than that of relays, while the existing schemes, for example, the null-space beamforming schemes, cannot work under this condition. Simulation results are presented to demonstrate the significance of performance improvements with the SRM and RPM beamforming schemes. It is also shown that the virtual eavesdropper approaches significantly reduce the complexity with acceptable performance degradation.
1. Introduction
The demands of wireless personal communications drive the development of abundant advanced wireless technologies and systems such as the cognitive radio network (CRN) and Third Generation Partnership Project (3GPP) Long Term Evolution-Advanced (LTE-Advanced) [1]. In addition to human-to-human (H2H) communications, an emerging technology empowering full mechanical automation (e.g., the Internet of Things and the smart grid) that may change our living styles is vigorously being developed. Such communications among machine-type devices are known as M2M communications [2–4]. Due to the use of machine-type devices and the broadcast nature of wireless media, privacy and security issues play an important role in wireless M2M networks. Although security is typically addressed via cryptographic approaches, there have been several attempts at addressing security at the physical layer, following the pioneering work of Wyner [5]. Physical layer security can be considered to solve the security problem from the point of view of information theory. The basic principle of information-theoretic security calls for the combination of cryptographic schemes with channel coding techniques. Physical layer security exploits the randomness of communication channels to guarantee that the transmitted messages cannot be decoded by a third party maliciously eavesdropping on the wireless media. The following work by Leung-Yan-Cheong and Hellman characterized the secrecy capacity of scalar Gaussian wiretap channel [6]. Along the same lines, the Gaussian multiple-input-multiple-output (MIMO) wiretap channel was investigated and its secrecy capacity was established in terms of an optimization problem over all possible input covariance matrices [7–9]. There are some recent works focusing on secrecy rates based on partial channel state information (CSI) [10–12] and multiuser scenarios [13–15].
The secrecy rate based on single-antenna systems is hampered by channel conditions. When the channel condition between the source and the destination is worse than the source-to-eavesdropper channel, positive secrecy rate cannot be achieved unless multiple antennas are employed at the transmitter. Since the use of multiple antennas on a node involves a potentially significant hardware cost, node cooperation is an alternative low-cost scheme that enables single-antenna nodes to enjoy the benefits of multiple-antenna systems. In particular, node cooperation via relays can increase the achievable secrecy rate by exploiting/mitigating the channel effects [16–20]. There are mainly two relaying protocols for the cooperative secure transmission: decode-and-forward (DF) [16] and amplify-and-forward (AF) [17, 18]. Dong et al. [18] proposed a two-stage amplify-and-forward cooperative approach. In [18], the source and relays are located in the same cluster, while the destination and eavesdroppers are at far away locations outside this cluster. A system design was proposed to maximize the upper and lower bounds of secrecy capacity in the presence of a single eavesdropper. For the multiple eavesdroppers case, Dong et al. [19] proposed suboptimal and conservative null-space beamforming schemes for both the secrecy rate maximization problem subject to a power constraint and the relay power minimization problem subject to a secrecy rate constraint, which completely nulled out the signal leakage to all eavesdroppers in Stage 2. However, this kind of null-space beamforming scheme requires that the number of relays is larger than that of eavesdroppers. In addition, Yang et al. [20] obtained the secrecy rate maximization (SRM) weights design in the presence of multiple eavesdroppers, but they assumed that there are no direct links between the source and the destination, as well as the source and the eavesdroppers.
In this paper, we consider a more general case of multiple relays and multiple eavesdroppers, where there are possible direct links between the source and the destination as well as the source and the eavesdroppers. Global CSI is assumed to be available and even the eavesdroppers' channels are known. CSI on the eavesdroppers' channels can be obtained when the eavesdroppers are active in the network as their transmissions can be monitored. This is applicable particularly in wireless networks, in which terminals play dual roles as legitimate receivers for some signals and eavesdroppers for others [19]. We focus on the cooperative secure beamforming designs for both the secrecy rate maximization problem subject to a power constraint, and the relay power minimization problem subject to a secrecy rate constraint. The contributions of this paper can be summarized as follows.
For the first optimization problem, we propose an SRM beamforming scheme. Using the semidefinite relaxation (SDR) technique, we perform the two-level optimization SRM problem to a one-dimensional search problem. Its performance approaches that of the optimal beamforming scheme. From a practical point of view, it is necessary to design a more simplified solution. Null-space beamforming has low complexity to be implemented, while it is out of operation when the eavesdroppers outnumber the relays. In order to overcome the drawback of null-space beamforming scheme, we propose a virtual eavesdropper-based SRM (VE-SRM) beamforming scheme by hypothesizing a virtual eavesdropper instead of all the eavesdroppers and maximize the secrecy rate according to the virtual eavesdropper. For the second optimization problem, we propose a relay power minimization (RPM) beamforming scheme to minimize the relay power subject to a secrecy rate constraint. To solve the multivariate problem, an iterative algorithm combining SDR and gradient-based method is devised. To reduce the complexity of the RPM problem, we relax the eavesdropper constraint and propose a virtual eavesdropper-based RPM (VE-RPM) beamforming scheme, which reduces the multivariate RPM problem to a problem of a single variable, and thus an analytical solution is obtained.
Moreover, the beamforming schemes we proposed can work well even if the number of eavesdroppers is larger than that of relays.
The rest of this paper is organized as follows. In Section 2, an AF-based cooperative network with multiple eavesdroppers scenario is described and the corresponding secure beamforming problems are formulated. In Section 3, we propose an SRM beamforming scheme and a practical VE-SRM beamforming scheme for the SRM problem subject to a power constraint. In Section 4, we propose an RPM beamforming scheme and an analytical VE-RPM beamforming scheme for the RPM problem subject to a secrecy rate constraint. Simulation results are provided in Section 5 and the conclusions are drawn in Section 6.
2. System Model and Problem Formulation
2.1. Channel Model
In this paper, we consider a communication unit of wireless M2M network which consists of one source (Alice), N (

AF relay assisted wireless M2M network in the presence of eavesdroppers.
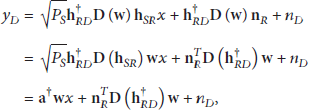
There are two stages in the AF protocol. In Stage 1, Alice broadcasts its n encoded symbols to its relays. For the purpose of evaluating the achievable secrecy rate, it is assumed that the codewords used at Alice are Gaussian inputs. In a time unit, let x be the transmitted symbol, and the average power of an symbol is normalized; that is,
In Stage 2, the N relays forward the signals that they received during Stage 1 to the destination. More specifically, each relay transmits a weighted version of the noisy signal that they received during Stage 1. Thus, the transmitted signals of all the relays are
The received signal at the destination is
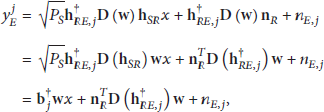
The received signal at the jth Eve is
2.2. Achievable Secrecy Rate
Recalling that
With the presence of J Eves, the achievable secrecy rate is given by [19]
Our beamforming design is based on amplify-and-forward cooperative scheme, and the optimization criterion is the maximization of the achievable secrecy rate subject to a relay power constraint or the minimization of the relay transmit power subject to a secrecy rate constraint. The specific problems addressed in this paper are as follows.
2.2.1. Maximize the Secrecy Rate under a Relay Power Constraint
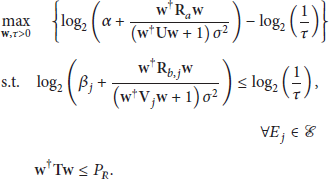
Given a source power
2.2.2. Minimize the Relay Transmit Power under a Secrecy Rate Constraint
Given a secrecy rate constraint
3. Secrecy Rate Maximization Beamforming Design under Relay Power Constraint
3.1. Existing Beamforming Scheme
In this subsection, we demonstrate the existing beamforming scheme under the relay power constraint. In [19], a simple null-space beamforming design was proposed when the number of relays is larger than that of eavesdroppers. Under the assumption of no signal leakage to all eavesdroppers in Stage 2, the associated SRM problem (7) can be simplified to
3.2. Secrecy Rate Maximization Beamforming
In order to maximize the secrecy rate under the total power constraint at relays, a SRM beamforming scheme is developed. By introducing a slack variable τ, problem (7) can be equivalently rewritten as
Since the logarithm function is monotonically increasing, we remove it and further obtain
To solve problem (11), following the idea of SDR [21], define
While problem (12) is still nonconvex due to the variable τ, one may check that, for a given τ, problem (12) changes into a quasiconvex problem [22]. By this observation, treat (12) as a two-level optimization problem—the inner level (problem (12) with a fixed τ) is a quasiconvex problem, and the outer level (optimization over τ) is a single-variable optimization problem.
Let us start with the inner-level optimization problem. Though this class of quasiconvex problems can be solved by using the bisection method [22], one usually needs to deal with many semidefinite programs (SDPs) during the bisection search [22]. Here, we adopt a more efficient approach by reformulating quasiconvex problem into a convex SDP through the Charnes-Cooper transformation [23]. For some
Problem (13) is an SDP whose optimal solution can be efficiently obtained by available solvers, for example, CVX. In the following, we turn our attention to the outer-level part, which is a single-variable optimization problem as follows:
The effective
The lower bound implies that, if
So far, we can cope with (12) through performing a one-dimensional search during which we solve a sequence of SDPs. We denote the solution of (12) by
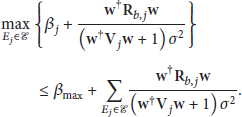
3.3. Virtual Eavesdropper-Based Secrecy Rate Maximization Beamforming
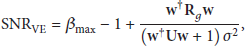
As mentioned above, the SRM beamforming is still difficult to implement due to the existence of multiple SDPs. To further reduce the complexity of the implementation, we propose a VE-SRM beamforming scheme. The SRM problem (7) can be rewritten as
Obviously, it is the two-level optimization that makes the SRM problem complicated to solve. The key to address problem (17) is to solve
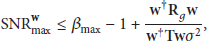
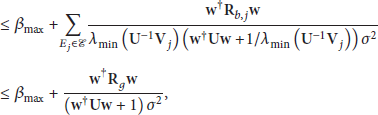
In order to drop the max expression in (18), we need to find an upper bound of the largest SNR (corresponding to the largest eavesdropping rate). Note that
According to the inequality in (21), the formula in (19) can be rewritten as
The VE-SRM beamforming scheme relaxes the constraint of selecting the Eve with the highest eavesdropping rate, while the null-space beamforming scheme introduces a strong constraint that nulls out all signals at Eves. Thus, the VE-SRM beamforming design is a better solution than the null-space beamforming scheme. Since the logarithm function is monotonically increasing, remove it and obtain
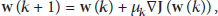
Considering the simple steepest gradient method [25], the equation for updating the weight vector regarding the function
As shown in Algorithm 1, we construct an iterative VE-SRM beamforming algorithm. The proposed algorithm requires an initial beamforming vector
(1) Initialize (2) (i) Clock index (ii) (a) Linear search. Choose step size search [22]. (b) Update. (c) Calculate. (d) Increase. clock index (iii) (3) Distribute the beamforming weights to the relays, and begin the secure data transmission.
4. Relay Power Minimization Beamforming Design under Secrecy Rate Constraint
4.1. Existing Beamforming Scheme
In this subsection, we demonstrate the existing beamforming scheme under the secrecy rate constraint. In [19], a simple null-space RPM beamforming design was proposed when there were more relays than eavesdroppers. Under the assumption of no information leakage to all eavesdroppers in Stage 2, the associated RPM problem (8) can be simplified to
Under the secrecy rate constraint, the null-space RPM problem was studied in [19], where a closed-form solution was derived.
4.2. Relay Power Minimization Beamforming
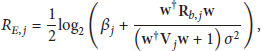
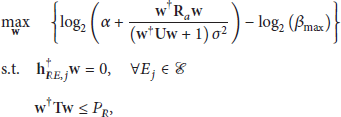
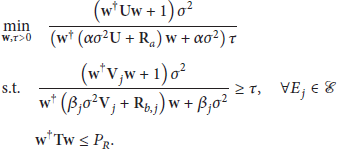
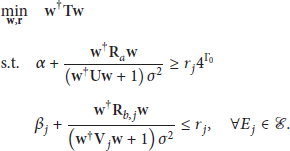
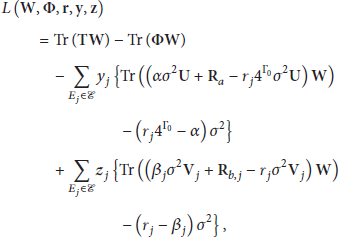
In order to minimize the transmit power at relays under the secrecy rate constraint, an RPM beamforming scheme is developed. Problem (8) can be reformulated into
Then we can further rewrite problem (31) as
The equivalence of the problems (33) and (31) can be shown as follows. Let
4.2.1. Optimization of w for Fixed r
Just as the SRM beamforming design, we introduce
The advantage of (36) is that it is an SDP problem and can be optimally solved [22]. Note that the obtained matrix
4.2.2. Optimization Over r
Denote the objective value of (36) as a function of
Theorem 1.
Proof.
The Lagrangian of problem (36) is
The Lagrange dual problem can be written as
Due to the strong duality between the primary problem (36) and the dual problem (38), the objective value of (38) is also
Since
The derivative of
The main iterative algorithm can be summarized as follows. For given
(1) Initialize α, (2) (i) Clock index (ii) (a) Calculate. calculate (b) Update. update (c) (iii) (3) Distribute the beamforming weights to the relays, and begin the secure data transmission.
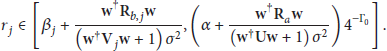
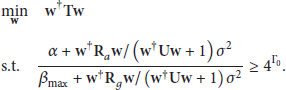
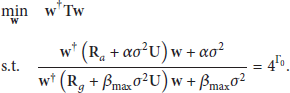
4.3. Virtual Eavesdropper-Based Relay Power Minimization Beamforming
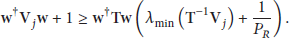
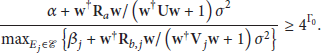
Similarly to the VE-SRM beamforming design, we propose a practical VE-RPM beamforming scheme to simplify the complexity of the RPM beamforming scheme. The eavesdroppers constraint in (31) can be relaxed as
Similar to (20),
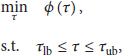
Note that the minimum relay power is achieved when the constraint in (45) is an equality; that is,
Defining
Note that if
Then minimizing
5. Simulation Results
In this section, we carry out some simulations to evaluate the secrecy rate performance of the proposed designs. For simplicity and without loss of generality, we consider a cooperative M2M network with N relays located in a (

Network scenario for simulations.
In Figure 3, we show the secrecy rates of different schemes versus the total transmit power budget when the number of relays is

Secrecy rate versus total power constraint.
Figure 4 illustrates the relationship between the secrecy rate and the number of Eves. The relay number N is

Secrecy rate versus number of Eves.
Figure 5 shows the results for the relay transmit power against the secrecy rate constraint. The relay number N is

Relay transmit power versus secrecy rate constraint.
In Figure 6, we illustrate the infeasibility probability against the number of Eves. We assume that there are N =

Infeasibility probability versus number of Eves.
6. Conclusion
In this paper, we have considered an AF-based cooperative protocol to improve the performance of secure wireless M2M communications in the presence of multiple eavesdroppers. The optimization criterion is the maximization of the achievable secrecy rate subject to a transmit power constraint or the minimization of the transmit power subject to a secrecy rate constraint. In previous works, the null-space beamforming schemes were imposed, at the expense of optimality, in order to obtain a simple solution. In our works, we propose beamforming schemes that do not rely on the null-space conditions, and thus our proposed beamforming designs can work well even if the number of eavesdroppers is larger than that of relays. Moreover, in the cooperative M2M network we have assumed that the global CSI is available, and even the eavesdroppers channels are known. System design of cooperative schemes that uses partial CSI or channel statistics will be considered in the future work.
Footnotes
Acknowledgments
This work has been supported by the Specialised Research Fund for the Doctoral Program of the Ministry of Education of China (Grant no. 20120001120125) and the National Natural Science Foundation of China (Grant nos. 61250001, 91338106, 61231011, and 61231013).