Abstract
The existing communication schemes are often unusable in natural disasters and public emergencies. But requirements of information collection and data transmission in emergency scenario are very imperative. Thus, sensor networks ad hoc networks are required in the emergency communication systems. For example, rescue vehicles equipped with wireless communication devices, sensors, and cameras are regularly used to collect and transmit the real-time information for the rescue action. The paper focuses on security solutions for the vehicular ad hoc networks (VANETs) in the emergency communication cases, in which the communication infrastructures are not always available. An expedite privacy-preserving emergency communication (EPEC) scheme is presented for the vehicles to securely connect with the others in the neighbor area even when the trusted infrastructures are destroyed by the disaster. EPEC satisfies conditional privacy preservation requirements, in which both lightweight signature and batch verification are employed to provide efficiency. We also show the proof of the security, feasibility, and efficiency of our EPEC by the theoretical and experimental analyses.
1. Introduction
Information perception, transmission, and processing are big problems in emergency rescues. The wireless sensor networks and ad hoc networks are expected to be used in these scenarios, but the network deployment and resource sharing face new problems of node connection, network security, and human privacy. As we know, vehicles are often used in disaster rescues, such as in Sichuan Earthquake [1] and Tōhoku Earthquake [2]. Then, we can equip rescue vehicles with sensors, cameras, and wireless communication devices, which combine wireless sensor networks with mobile ad hoc networks and will be more applicable in real-time data collection, transmission, and processing. Vehicle communication in rescue action should maintain the primary requirements of security, privacy, and efficiency, which contain mutual authentication, conditional privacy preservation, internal attacks prevention, and expedite authentication in emergency communication. The communication units of these rescue vehicles based networks are similar to typical vehicular ad hoc networks (VANETs), but the network structures are different because there are no road-side units (RSUs). Thus, the new networks are the same as traditional VANETs without the supports of RSUs, and we study the communication scheme for the emergency scenario where the vehicles cannot connect with an RSU.
VANETs mainly consist of mobile vehicles equipped with wireless communication devices and the road-side units. As shown in Figure 1, vehicles can communicate with one another (V2V) and with the RSUs (V2R) by means of the Dedicated Short-Range Communication protocol [3]. Figure 1 also shows that VANET is a subnet under the architecture of the Internet of Things, for VANET is connected with a trust authority (TA) and many Application Servers through the Internet. VANETs can provide drivers with traffic information to defend against dangers and traffic congestions [4], as well as entertainment information to improve the driving experience [5]. Privacy preservation [6] and expedite authentication [7] are two critical issues in VANETs communication, where privacy is conditional as TA is allowed to reveal any entity's real identity and revoke it from the network. It is because on one hand, drivers would not be willing to join VANETs if their private information could not be well preserved. And on the other hand, malicious vehicles should be removed from the network timely. In addition, expedite authentication can reduce packet loss and ensure smooth operations of VANETs. Many communication schemes have been proposed for conditional privacy preservation and expedite authentication in VANETs. But these reported schemes are not suitable for emergency communication in the rescue scenario we described earlier, because they take RSU as an important part of VANETs.

VANETs model.
We will present an expedite privacy-preserving emergency communication (EPEC) scheme for disaster rescues, where RSUs are unavailable. The remainder of this paper is organized as follows. Section 2 overviews the related works in VANETs. In Section 3, we describe the system model and give basic presuppositions used in the proposed scheme. The proposed EPEC is thoroughly described in Section 4. The security analysis of the proposed scheme is presented in Section 5. Performance evaluation is given in Section 6, followed by the conclusion in Section 7.
2. Related Works
Many related studies have been reported in VANETs based on different cryptographic systems, such as public key infrastructure (PKI) based signature, group signature, and identity-based signature. In terms of disaster rescue, the primary functional requirements of communication do not change, but these requirements should be realized without fixed infrastructures. Next, we analyze the related works in the aspects of EPEC's requirements aforementioned.
Mutual authentication is the primitive property required in VANETs communication, which can be achieved through digital signature. Raya and Hubaux proposed PKI-based schemes [16, 17] in 2005 and 2007, respectively to realize authenticity in VANETs. But PKI-based scheme is not suitable for VANETs because of the management overhead of certificates.
The commonly used techniques for conditional privacy preservation are group signature and Mix-zone pseudonym—changing pseudonym within specified region, that is, Mix-zone. Lin et al. [8] adopted short group signature [18], and TACK [9] and TARI [19] adopted group signature with verifier-local revocation [20], to realize conditional privacy preservation. For the shortcoming of the demand for group manager, ring signature [21] met conditional privacy preservation without group managers. However, what makes these schemes inapplicable to VANETs is that the verification cost for group/ring signature is very high. For authentication efficiency, Lu et al. [10] achieved conditional privacy preservation by pseudonym signature. Reference [22] aimed to establish Mix-zones at social points, allowing all vehicles in the Mix-zone to change pseudonyms at the same time. However, only when given a reasonable large number of vehicles in the Mix-zone, the privacy requirements can be well protected due to pseudonyms updating.
In aspect of internal attacks prevention, some existing schemes perform well while some fail to realize internal attacks prevention requirement. IBV [11] devised identity-based signature to realize unidirectional V2R authentication, which could not achieve internal attacks prevention or conditional privacy preservation requirements. Subsequently, TSVC [23] based on the TESLA [24] achieved fast authentication with internal attacks prevention using message authentication code (MAC). However, its drawback is that packet loss ratio increases with the speed of vehicles. ABAKA [12] was dedicated to entertainment services in VANETs, but internal attacks prevention requirement was not realized as users shared the same secret.
In addition to aforementioned requirements, verification efficiency, that is, expedite authentication, is another requisite in VANETs. One-by-one message verification is characterized by being simple to use. In RAISE [13], RSU verified messages one by one and broadcasted 128 bytes for each valid message, which caused severe inefficiency. Cooperative authentication is a method of raising verification efficiency. In COMET [13], verifiers verified message with probability of
Virtually, VANETs-based emergency communication system is a special kind of VANETs model without RSUs. But currently there is no related research. Overall, current works in VANETs cannot satisfy all the functional requirements in this scenario. And it is shown in Table 1, where “
Comparison of related works.

The proposed EPEC achieves the following five aspects of requirements. (1)
3. System Model and Preliminaries
In this section, we formalize the specific system model for VANETs-based emergency communication and the basic presuppositions used in the proposed scheme EPEC and identify the design objectives.
3.1. System Model
VANETs for disaster rescue are different from the regular vehicular network model in Figure 1. According to the accurate circumstance of disaster rescue, a two-layer network model is proposed, as shown in Figure 2. The upper layer comprises the trust authority TA and the Application Server, while the lower layer is composed of rescue vehicles including emergency communication cars and regular vehicles. TA is responsible for issuing real identification RID and public/private key pairs to all entities. Most importantly, TA is always trusted and can never be compromised. The Application Server is responsible for information analyses and feedbacks. The emergency communication cars contain ambulances, fire trucks, and so on, AMBs for short in EPEC. AMBs are allocated with powerful hardware facilities with longer communication range and stronger computation capability than regular vehicles. They are authorized by TA and can arrive at the target zone after the disaster, responsible for networking the regular vehicles.

System model.
In the framework we proposed, there are two different kinds of communication: the reregistration communication and the broadcast communication, where the broadcast communication can also be divided into vehicle to AMB communication and vehicle group communication. The leftmost group 1 in Figure 2 indicates vehicles reregistration with TA via AMB. Vehicles reregister themselves with the TA via AMB and get the exclusive secret key used to generate pseudonyms. Groups 2 and 3 show the communication with and without AMB available, respectively. EPEC does not require AMBs to cover the entire network. They may move to another place after networking the vehicles in some place. The dashed line indicates the group communication range, within which the vehicles communicate with each other by the wireless communication standard IEEE 802.11p. AMBs communicate securely with TA and the Application Server by satellite communications.
3.2. Basic Presuppositions
An elliptic curve is a cubic equation of the form
Definition 1 (Elliptic Curve Discrete Logarithm Problem (ECDLP) ).
Given two points
Definition 2 (Computational Diffie-Hellman Problem (CDHP) ).
Given three points
3.3. Design Objectives
In terms of emergency communication, the VANETs system needs to satisfy all requirements in the condition of no fixed infrastructures. The precise functional requirements are presented as following.
4. EPEC: Expedite Privacy-Preserving Emergency Communication
In this section, we detail the expedite privacy-preserving emergency communication EPEC scheme for VANETs-based disaster rescue. EPEC presents expedite authentication for two communication patterns: EPEC1 for vehicle networking with AMB and EPEC2 for vehicle group communication without AMB. When AMB enters the disaster area, it regularly broadcasts beacon of its own identification. Vehicles receiving the beacon verify its authenticity and, if valid, reregister with TA via AMB. Specific to the requirement of conditional privacy preservation, a secure key agreement protocol is proposed to establish an exclusive secret key between the vehicle and TA during the reregistration phase. Then, vehicles self-generate pseudonyms for subsequent broadcast communication. In both vehicle to AMB communication and vehicle group communication, point multiplications instead of bilinear pairings are conducted for authentication, thus saving computational overhead. Besides, signatures can be verified in batch. The prime notations in EPEC are defined in Table 2.
Notations.

4.1. System Initialization
Before AMBs enter the disaster area, TA initializes the system to establish the public parameters. It is reasonable to assume that TA bootstraps the whole system, as a single authority VANETs model is under consideration in Figure 2. Specifically, in this phase, TA generates a cyclic additive group
4.2. EPEC1: Networking with AMB
AMBs enter the disaster area after the system initialization for dynamic vehicle reregistration, after which vehicles generate pseudonyms by themselves and conduct communication with AMB according to EPEC1.
4.2.1. Dynamic Reregistration
In the reregistration procedure, a secure protocol with secret key agreement is presented to establish a shared secret key between vehicle and TA via AMB. The protocol is secured with signature and encryption to prevent the intermediate intrusion attacks. The precise process is shown in Figure 3.

EPEC1: Vehicle reregistration protocol.
AMB periodically broadcasts its own identity information when entering some area with the following beacon message:


As AMB's communication range is much larger than regular vehicles, In regard to replay attack,

If (4) holds, the beacon is accepted and
First, vehicle 
Receiving the first message RM1 from vehicle 
TA decrypts the message and verifies the real identity 
AMB stores the 
The vehicle verifies the TA's signature and, if valid, sends its own signature on 
TA authenticates the vehicle
The secret key agreement protocol adopts ECDSA signature and ECIES encryption to prevent the intermediate intrusion attacks. Under the assumption of computational Diffie-Hellman problem, the adversary cannot calculate any information about the secret key
4.2.2. Pseudonym Self-Generation
In the identity-based cryptography, the entity's public key can be generated based on the real identity. Different pseudonyms are used to sign messages to protect the vehicles from being tracked or associated.
The pseudonym 

In the end, the vehicle
4.2.3. Vehicle to AMB Communication


EPEC1: Vehicle to AMB communication.
AMB first checks the pseudonym life period For freshness, AMB checks the transmission delay. Assuming that AMB receives the message at AMB calculates the vehicle's corresponding private key according to (11), Verify all the signatures by
If (13) holds, all the signatures are valid in the batch; otherwise, there is at least one invalid signature, which calls for invalid signature detection algorithm to find the invalid ones.
Note that AMB needs to find out the verification key of
4.3. EPEC2: Vehicle Group Communication without AMB
As we do not assume that AMBs cover the whole network, they may forward to another place after networking the vehicles. So, vehicle group communication scheme is requisite for vehicle communication without AMBs.
4.3.1. Vehicle Group Formation
In this subsection, we present how to form a vehicle group with the help of AMB. The establishment of a group is divided into four stages as shown in Figure 5. Concretely, the specific procedure of group formation is detailed as the following.
First of all, AMB generates the group request message Vehicles receiving the message verify AMB's signature first and, if valid, check for their own pseudonym Receiving all the agreed messages, AMB verifies all the signatures in batch. If the batch verification fails, AMB suspends the protocol and broadcasts new group formation request. Otherwise, AMB sends group key request message GKR to TA applying for the group key. Consider
Upon receiving the group key request message GKR, TA verifies AMB's signature. If valid, they choose random number




EPEC2: Group formation protocol.
4.3.2. Vehicle Group Communication without AMB
After group formation, vehicles can conduct mutual authentication within the group for real-time communication without AMB. With the pregenerated pseudonym 

EPEC2: Vehicle group communication.
Receiving the message, the verifier 
Note that the batch verification is also applicable to group communication, providing a much smaller computational overhead of two point multiplication operations. Thus EPEC2 provides much smaller authentication delay than other schemes, which will be detailed in Section 6.
4.4. Invalid Signature Detection
Invalid signature detection algorithm is essential for batch verification scheme. This is because invalid signatures could come from a variety of reasons, such as malicious vehicles, legitimate vehicle failure, or wireless channel interference. The batch verification will fail when there is one invalid signature in the batch. IBV [11] may suffer from severe inefficiency as it does not pay attention to invalid signatures. Once an invalid signature frustrates the batch verification, all the valid ones in the batch will be discarded. Therefore, invalid signature detection mechanism is necessary. ABAKA [12] adopted the binary search method for invalid signature detection. When the batch verification fails, messages in the batch are bisected, and verified, respectively until only one message left or valid. But it is inefficient to retest the messages for 
5. Security Analysis
We analyze the security performance of the proposed scheme EPEC in this section. According to the security objectives aforementioned, EPEC is evaluated in the following four aspects: dynamic reregistration without fixed RSUs, mutual authentication, conditional privacy preservation, and internal attacks prevention. And the efficiency of EPEC is analyzed in Section 6 in three different aspects. The security of EPEC is analyzed as follows.

6. Performance Evaluation
In this section, the effectiveness of EPEC is evaluated in terms of message verification delay, transmission overhead, and verification delay with invalid signatures. In the evaluation, EPEC is compared with four related typical schemes: IBV [11], ABAKA [12], ECDSA [13], and CPAS [15]. IBV is a typical batch verification scheme for unidirectional authentication based on bilinear pairing operations. ABAKA is a point multiplication based signature scheme with batch verification. Reference [13] presents a key establishment and authentication protocol RAISE based on ECDSA signature in the IEEE standard 1609.2. It is referred to as ECDSA in the evaluation. CPAS is a typical mutual authentication scheme with batch verification based on bilinear pairing operations.
6.1. Message Verification Delay
To evaluate and compare the schemes' verification delay, we first define the time complexity of the main cryptographic operations required in our EPEC and other schemes. Let
Computational overhead.

Notice that IBV is an authentication scheme without mutual authentication and key agreement. So, for fairness, the schemes are compared in unidirectional authentication case without key agreement. The mutual authentication function of EPEC is analyzed in Section 5. And for EPEC, the broadcast authentication cost equals on the two sides. From the comparison in Table 3, we can see that the proposed scheme EPEC achieves the least computational overhead. ECDSA verifies
The computational overhead increases with the number of messages for all these schemes. The message verification delay ratio of these schemes is shown in Figure 7. It is apparent that EPEC is superior to all the other typical schemes, because EPEC adopts lightweight point multiplication to verify messages. Figure 7(a) indicates the relationship between EPEC1 and other schemes. It is obvious that the delay ratio between EPEC1 and ABAKA is always less than 0.50 regardless of the number of messages; the delay ratio between EPEC1 and ECDSA is approximately 0.25 when the number of messages is larger than 60. From Figure 7(b), we can see that the delay ratio between EPEC2 and other schemes approaches zero with the traffic density increasing, which is because the batch verification overhead has nothing to do with the number of messages for EPEC2.

Verification delay ratio with different traffic density.
6.2. Transmission Overhead
We consider the transmission overhead in terms of the signature and the certificate appended to the original message, while the message itself is not counted. The comparison of all the schemes is shown in Table 4. ECDSA signature is 42 bytes in length, but a certificate of 125 bytes must be transmitted along with each message, resulting in the total transmission overhead of 167 bytes. For IBV, the length of signature is 21 bytes, while pseudonym is 42 bytes. In ABAKA, the 20 bytes verification message and the 20 bytes material message all are authentication materials, resulting in a signature of 40 bytes. CPAS has 60 bytes signature, 41 bytes pseudonym, and 4 bytes message type information.
Transmission overhead.

The transmission overhead of ECDSA is the largest among the five schemes, while IBV has the smallest. Since IBV adopts bilinear pairing cryptographic operations for signature, which is short in length but costly in verification. The overhead of ABAKA is a bit less than EPEC, which is because 2 bytes life period
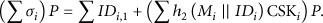
6.3. Verification Delay with Invalid Signatures
Batch verification can save computational overhead and provide low verification delay. However, the expense of the batch verification is that invalid signature may cause verification failure and re-batch verification is needed. As aforementioned, GBS is the most efficient invalid signature detection scheme when the number of invalid signatures is not very great. We adopt GBS, while the IBV and ABAKA use binary search algorithm to check the invalid signatures. Table 5 shows the computational overhead for first batch verification and one time re-batch verification. ABAKA and EPEC only need point multiplications for re-batch verification, while IBV and CPAS need three bilinear pairing operations.
Computational overhead with invalid signatures.
The verification delay 

Figure 8 gives the verification delay ratio with the number of invalid signatures. In the experiment, the messages number

Verification delay ratio with invalid signatures.
7. Conclusion
In this paper, we propose an expedite privacy-preserving emergency communication (EPEC) scheme for VANETs-based disaster rescue. EPEC fulfils two communication patterns: EPEC1 for vehicle networking with AMB and EPEC2 for vehicle group communication without AMB, respectively. By the theoretical and experimental analyses, we show that the proposed scheme has the following advantages. (1)
Footnotes
Acknowledgments
This work is supported by the Natural Science Foundation of China under Grant no. 61272074, the Natural Science Foundation of Jiangsu Province under Grant no. BK2011464, and the project of the Key Laboratory of Intelligent Computing & Signal Processing, Ministry of Education. And the author L. Wang is supported by the Disguised Researcher Program of Jiangsu Province of China (2012-wlw-020) as well as academic leader supported by Qinglan Project of Jiangsu Province of China.
