Abstract
Dynamic service composition provides us with a promising approach to cooperate different sensor nodes in WSN to build complex applications based on their basic functions. Usually multiple nodes located in different regions provide data with different security levels, and it is critical to ensure the security of the information flow in the composite services. However, the energy-limited nature of sensor nodes in WSN poses a significant challenge for the centralized information flow verification with which the verification node needs to consume lots of computation and network resources. In this paper, we specify the security constraints for each service participant to secure the information flow in a service chain based in the lattice model and then present a distributed verification framework that cooperates different service participants to verify their information flow policies distributively. The evaluation results show a significant decrease on the verification cost of the single verification node, which provides a better load balance in each sensor node.
1. Introduction
WSN is the key enablers for the development of the Internet of Things (IoT), which is responsible for collecting surrounding context and environment information. In a service-oriented WSN [1, 2], multiple sensor nodes with different basic services, for example, data aggregation, data processing, and decoding, can cooperate with each other to develop new applications rapidly. However, because of the variety and regional characteristics of WSN, the data provided by the sensor nodes have different security levels. When services are composed together, data are transmitted among these nodes, respectively, where an operation in a node assigning high-level data to a low-level object would cause the information leakage with a serious impact on the public safety or personal privacy.
For example, a personal-health helper service can be provided for the healthy advice according to the body status and environments data. Most of the former work, mainly focus on the access control of the individual services [3, 4]. But in a service chain, data may be computed from its prior services which can result in the undesired information leakage. When the collection service is completed, the data collected by the wearable sensors and environmental sensors are delivered to the data processing node, such as mobile phone. Healthy information may leak to untrusted third party through the illegal operations during data processing. So the information flow security is one of the major concerns about the service composition in sensor network environments.
One issue in information flow security of the composite service is the dynamic dependence among various objects in different service participants. Accorsi and Wonnemann [5] use Petri nets to represent the workflow and detect information leaks in workflow descriptions based on static information flow analysis. But this work can only validate the information flow in fixed workflow with static input and output dependences. In service-oriented WSN, there are several candidate services with same functions where the dependences between input and output are different from each other. It is necessary for user to select appropriate service for the secure composition of the service chain. She et al. [6, 7] define transformation factors to measure how likely the output depends on the input data in different candidate services. But it is hard to define the LR, MR, and HR transformation factors. Therefore, a suitable dependence model is required for the analysis of the information flow in different candidate services.
Another major issue for the information flow verification in WSN is the energy cost of the verification node. Zorgati and Abdellatif [8] and She et al. [9] propose the centralized verification approach against the information flow control policies to ensure an end-to-end security in wired network. However, in WSN, the sensor node is energy limited, and the centralized way consumes lots of energy of the verification node. Yildiz and Godart [10] propose an decentralized service composition approach considering the information flow policies in an inexpensive manner, but its policies are static. Based on the information flow type system, Hutter and Volkamer [11] specify the composition rules to control the security of dynamically computed data and their proliferation to other web services. But it costs extra energy of the sensor node to compile the service code again before the service execution.
In this paper, we present a distributed information flow verification approach applied on the composition of the service chain in wireless sensor network. Our contributions include the following. (1) For the dynamic dependences in service chain, we define the intra and inter dependences among different objects in composite service based on the PDG. (2) We specify the security constraints for each service participant based on the dependences and lattice model. (3) We propose a decentralized information flow verification approach to execute the verification process distributively to provide a better load balance of the sensor nodes in WSN.
The rest of the paper is structured as follows. Section 2 presents the basic definitions of the wireless sensor service system. Section 3 specifies the security constraints for each service participants based on the analysis of the information flow in the service chain. In Section 4, we propose the distributed information flow verification framework based on the secure information flow model. Section 5 evaluates the proposed verification approach. Section 6 concludes the paper.
2. Wireless Sensor Service System
A wireless sensor service system (WSS) is a large-scale distributed environment which consists of multiple wireless sensor nodes, public data resources and security authorities, which is shown in Figure 1. Sensor nodes in WSN can collect these resources, and provide different basic functions, such as data analyzing or processing, which are treated as various services in WSN. There is also a security authority for each data resources for the management of these data security levels which are used for the security verification. The service on each sensor node can be defined as follows.
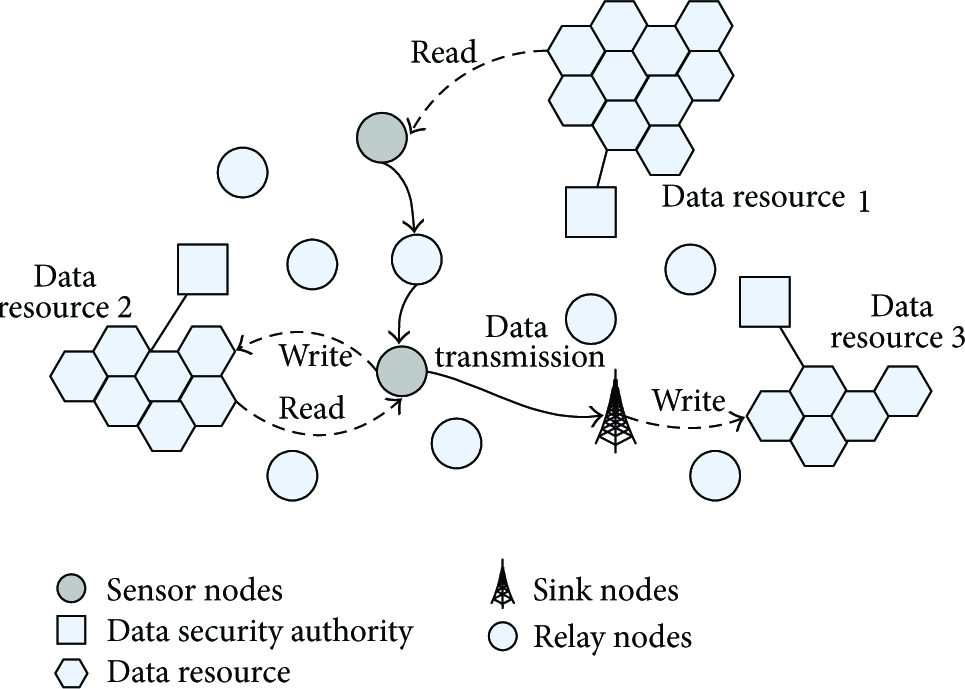
A wireless sensor service system.
Definition 1.
Each service
In WSS system, various services are provided by different sensor nodes. These individual services can also be combined together to generate a more powerful service. During the execution of composite service, each service node collects data from its local storage or the public resources, processes the input data, and finally provides results to the sink nodes. On the other hand, these nodes may also update the local storage or store to the public data resources in WSS. A composite service can be denoted as a directed graph, where the vertex is the service component and the edge represents an composition relationship from one service to another. In this paper, we investigate a simplified composite service, the service chain, which is defined as follows.
Definition 2.
A service chain
In a service chain

A service chain model.
Due to the dynamic and heterogeneous sensor network environment, it is necessary to select appropriate service to satisfy the different requirements including QoS and security. In this paper, we focus on the verification of the information flow security in composite service chain and providing support for the security enforced selection of services in WSN.
3. Secure Information Flow Model
3.1. Security Label Model
For the information with different sensitivities, we use multilevel security labels to describe the security properties of objects o.
Definition 3.
Security label model is defined as a lattice
The lattice model is widely used in government or military systems in which the security classes are determined solely from the four security levels: unclassified, confidential, secret, and top secret [12].
For a clear discussion, in this paper, we define that each object o has a provided and required security level,
3.2. Information Flow in Service Component
In a service chain, the information flow through

Information flow in service component.
For the input information for
For the output information for
In order to validate the information flow in
Definition 4.
Program dependence graphs (PDG) is a directed graph
Once a program dependence graph
Based on the dependency set
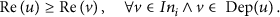
Based on the previous equation, we can obtain the following.
Theorem 5.
For
Each service
Definition 6.
The information flow in service component
The previous condition provides that there are no lower level objects in public resources and local storage storing the data with higher security level during the execution of each service.
3.3. Secure Information Flow in Service Chain
Consider the service chain
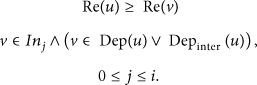
Definition 7.
For objects
For two adjacent services
For two services
For a service chain
Definition 8.
The information flow in service chain
According to the definition of the secure information flow in
Lemma 9.
In a service chain
Proof.
First, let
For
And there is no interservice dependence in
For
Case
1.
Case
2.
Then we suppose that the lemma is true when
Case
1.
Case
2.
Based on (14), (15), and (16), we can get
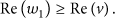
Lemma 10.
If the information flow of each service in first m step of
Proof.
For
Case 1.
Case 2.
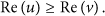
Theorem 11.
For a service chain
Proof.
Let
4. Distributed Information Flow Verification Framework for Wireless Service Composition
4.1. Information Flow Verification Framework
For a service chain

Decentralized information flow verification framework.
In our framework, Service Authorization Centre (SAC) is a trusted third party for service certificate generation before the deployment of the sensor node. There are two phases for the verification of the information flow: service certificate setup and service verification phase. The service certificate that specifies the security properties of the service, that is, the dependence between the service input and output, is first generated and signed by a SAC. During the service composition procedure, the service composer obtains the required service certificates, and verifies the information flow in candidate nodes. These two phases are detailed in the following sections.
4.2. Service Certificate Setup
Service certificate setup is the preparation phase of the verification process, which is shown in Figure 5. In this phase, service developer submits authorization request containing service function code in service node to SAC. And then the generated service certificate

Service certificate setup phase.
Definition 12.
A service certificate
The service certificate
When there is a request for the service, the node needs to send its certificate to the composer for its information flow verification. The provided security levels of the public and local input data and output objects are also required to be sent to the verification node. If the realization of the service is changed, for example, a new version service is published, the service needs to be authorized by SAC again and reinstalled on the sensor node.
4.3. Service Verification
Service verification is a vital phase in which the verification node requires the service certificates and validates the candidate nodes against the information flow control policies. The verification procedure is shown in Figure 6. During the verification process, service composer

Service Verification Phase.
4.3.1. Required Security Level Computation
According to the secure information flow definition in service chain, the required security levels of the data objects need to be computed first. The required security levels of the objects in each service
4.3.2. Service Verification
During the service verification, the information flow control policy (IFCP) specifies how to validate a candidate service
Based on the required security level computation rules and information flow control policies, verification node can validate the candidate sensor node
(17) break; (18) (19) (20) (21) (22) (23) (24) break; (25) (26) (27) (28)
4.4. Decentralized Information Flow Verification Algorithm for the Service Chain
For each step verification, verification node obtains the passed candidate service set
5. Experiments and Evaluations
This paper studies distributed information verification framework for the service composition in WSN. Through the security analysis in Section 3, the information flow security can be ensured by the Theorem 11. In this section, we investigate the impact of distributed service verification on the sensor node's cost including verification time and communication effort. A centralized approach implements the service verification work by a single sensor node. We test both approaches with NS-3 [15] in multiple scenarios. Table 1 shows further details about the simulation configuration.
Simulation Configuration.

Figure 7 shows the computation time on the verification node. In the centralized way, time rises vastly with the increase of the candidate service number. That is because the execution paths that need to be verified are increased at an exponential rate. However, time increases slowly in the distributed way because there is no significant variations on the candidate nodes that each sensor node needs to verify.

Computation time on the verification node(s).
Figure 8 shows the communication effort on the verification node. In Figure 8, the communication effort in the centralized way is evidently higher than that used the distributed way. That is because the single verification node needs to communicate with all other service nodes in centralized way, while it just needs to communicate with the next-step service nodes which can decrease the communication effort and save the energy of the sensor nodes.

Communication effort on the verification node(s).
6. Conclusion
In this paper, we specify the security constraints for each service participant based on the partial order model and propose a decentralized information flow verification approach that cooperates each sensor node to verify the information flow security distributively and builds up secure service chains in wireless sensor environments. Through the simulation on NS-3, the result shows that this approach can decrease the cost of the sensor nodes effectively.
Footnotes
Acknowledgments
This work is supported by Program for the Key Program of NSFC-Guangdong Union Foundation (U1135002), Major National S&T Program (2011ZX03005-002), National Natural Science Foundation of China (60872041, 61072066), and the Fundamental Research Funds for the Central Universities (JY10000903001, JY10000901034, and K5051203010).