Abstract
The key for cooperative collision avoidance (CCA) systems is the real-time and reliable delivery of safety-related messages among vehicles, which include periodical beacons and risk-triggered warning messages. In this paper, we first design a risk-aware dynamic medium-access control (R-MAC) protocol tailored for vehicular CCA applications. In this protocol, each frame is divided into two parts: TDMA segment for transferring beacons and CSMA segment for delivering warning messages. Then, we propose a stochastic model to predict the average total number of potential collisions in a platoon of vehicles, which determines the size of CSMA segment in the R-MAC protocol meticulously. Monte Carlo simulations validate that our model is reliable and practical. The performance of the R-MAC protocol is verified through theoretical analysis and extensive simulations under different traffic scenes. Simulation results show that R-MAC outperforms the traditional IEEE 802.11p protocol in terms of packets delivery rate and transmission delay, as well as the Jain's fairness index of the medium access between beacons and warning messages.
1. Introduction
As a potential technology for intelligent transportation system, vehicular ad hoc network (VANET) has received considerable attention by academic communities and major car manufactures around the world. The Federal Communications Commission (FCC) has allocated a dedicated 75 MHz spectrum for vehicular applications in 1999 [1], and some important projects (e.g., Advanced Driver Assistance Systems (ADASE2) [2], CarTALK2000 [3]) have been launched subsequently. Through wireless vehicle-to-vehicle and vehicle-to-roadside communications, VANET can provide various safety-related services. As a typical representation, cooperative collision avoidance (CCA) systems have greatly evolved in the past years [4, 5], which helps to reduce the probability of vehicular collisions and the corresponding damage significantly. Within a CCA system, when a vehicle in the platoon encounters an obstacle or collision, a warning message will be broadcast backwards to the following vehicles. Upon receiving a warning message, the following drivers will promptly brake instead of reacting to the brake light ahead immediately in tradition, which saves a lot of time before the following drivers are aware of the accidents in the front [6].
In this paper, we study efficient and fair delivery of different messages in the considered scenario of CCA systems, where many vehicles form a platoon (or a chain) moving along the same road toward the same direction. Within this system, there are mainly two kinds of messages: beacons and warning messages. Beacons are disseminated among vehicles periodically to inform neighbors about their movement states, such as speed, acceleration, and direction. Warning messages are triggered by a specific vehicle which experiences a hazard or collisions and are propagated from the source to following vehicles as far as possible to inform them of the accidental situation. As a result, such messages have a higher priority [7] compared with beacons. One key for a CCA system is the real-time and reliable delivery of warning messages as well as beacons. In traditional CCA applications [4, 5], some simple approaches are employed to deliver messages, which may lead to several problems in an emergent situation. First, message collisions are more likely to occur with the increasing number of vehicles in the platoon due to a large number of redundant warning messages pertaining to the same emergent event, which results in a serious message-delivery latency and packets loss. Then, the overemphasis on the higher delivery priority of warning messages makes the beacons lose the chance of medium access, especially in the IEEE 802.11p protocol which is based CSMA/CA mechanism. In addition, vehicles will become blind to others without knowledge of their latest movement states, which, in turn, may cause more accidental collisions among the platoon. To overcome these shortcomings, we design a risk-aware dynamic medium access control (R-MAC) protocol tailored for vehicular CCA systems, which makes a good tradeoff between efficient delivery and fairness of messages with different priorities.
To this end, our protocol is based on traditional TDMA mechanism, in which time is divided into periods called frames and each frame can be subdivided into tiny time slots uniformly. However, each frame in R-MAC includes two parts: CSMA segment for sending warning messages and TDMA segment for beacon transmission. In order to ensure the higher transfer priority of warning messages, we allocate slots to CSMA segment prior to TDMA segment in each frame. The number of slots reserved for CSMA segment is determined by the average total number of potential vehicle collisions among the platoon in the next few frames, which can be computed though a stochastic collision prediction model. After allocation for CSMA segment, the left slots fall into the TDMA segment. In this way, both efficiency and fairness of the medium access between the above two kinds of messages can be achieved in R-MAC. In addition, with the rapid spread of 3G and WIFI in recent years, the V2I communications has been feasible. In this paper, the prediction process of average total number of potential collisions operates on a roadside unit (RSU), such as 3G stations, WIFI hot spots.
The main contributions of the paper are listed below.
Considering the efficiency and fairness of delivering beacons and warning messages on the medium access, we design a risk-aware dynamic (R-MAC) protocol tailored for vehicular CCA systems, which is based on a dynamic TDMA mechanism. Since the size of CSMA segment in each frame is determined by the average total number of potential collisions among the platoon in the next few frames, a stochastic collision prediction model is presented, which is based on minimum safety distance and a homogeneous Markov chain. Moreover, extensive simulations under various traffic loads show that R-MAC outperforms the traditional IEEE 802.11p protocol in terms of packet delivery rate and transmission delay, as well as the Jain's fairness index of the medium access between beacons and warning messages.
The remainder of this paper is organized as follows. In Section 2, we briefly review the related work on MAC protocols and vehicle collision models in VANET. Section 3 delineates the operation of the R-MAC protocol in detail. In order to compute the average total number of potential collisions used in R-MAC, the derivation of a stochastic collisions prediction model is introduced in Section 4. The performance of R-MAC is evaluated in different setups in Section 5, which also provides an in-depth analysis of the simulation results. We conclude the paper in Section 6.
2. Related Work
In recent years, various MAC protocols have been proposed to guarantee the real-time and reliable communications in VANET. These protocols are mainly based on two approaches: Carrier Sense Multiple Access (CSMA) and time division multiple access (TDMA). However, most of them cannot be applicable well to the vehicular scenarios with high mobility and fast changing topology.
The TDMA approach operates in a time slotted structure, where time slots are grouped into frames. Due to the collision-free nature of TDMA, it has been widely adopted and become the foundation of several TDMA based protocols [8, 9] in vehicular network. R-ALOHA [10] is the earliest dynamic channel reservation scheme, which enables nodes to reserve a time slot for transmission in a fixed period. RR-ALOHA [11] and ADHOC-MAC [12] are completely distributed TDMA schemes, but both of them are based on the assumption that the network topology stays static. Simulation results show that the throughput reduction of ADHOC MAC protocol can reach up to 30% for an average vehicle speed of 50 km/h [13]. Lam and Kumar designed a DCR protocol with the help of GPS in [14]. However, his work is not suitable for heavy traffic situations. Omar et al. [15] proposed a TDMA-based MAC protocol for reliable broadcast in VANET. This scheme reduces transmission collisions caused by vehicle mobility, but it assumed that there were two transceivers on each vehicle, one used for control channel and the other for service channel.
In CSMA-like random schemes, the prime example is IEEE 802.11 [16], which is a simple, flexible, and contention-based medium access control protocol. In the protocol, when a vehicle wants to transmit messages, it first listens to the desired channel. If the channel is free (not occupied by other vehicles), the vehicle is allowed to transmit. Otherwise, the vehicle has to defer its transmission to the next contention period. Although the approach is simple and flexible, the data delivery delay will increase significantly if the vehicles density is high, especially when an exponential back-off mechanism is employed to resolve the robust contention issues among different vehicles [16]. In order to be delivered timely, warning (emergency) message is assigned a higher priority to contend for the wireless channel with a small contention window size in the IEEE 802.11 p EDCA [17]. Although the small contention window size allows the warning message to be transmitted with a small delay, it introduces the unfairness between warning messages and beacons (with a lower priority than warning message) on the medium access and the delivery delay of beacons is increased greatly. Another limitation for CSMA schemes is that no RTS/CTS exchange is used, which results in a serious hidden terminal problem and reduces packets delivery rate. Consequently, the effectiveness of CCA applications decreases substantially.
However, to the best of our knowledge, little effort has been devoted to design risk-aware MAC protocol by exploiting reliable and practical vehicle collision models. Detailed models of vehicle motion and collision dynamics were given in [18, 19], but they are completely based on deterministic equations for the occurrence of collisions, whereas in fact, randomness is always present introduced by high mobility and driver behavior. In [20], the authors explored the necessary conditions for chain collisions. However, it is assumed that all the vehicles have the same initial speeds and intervehicle distance. A more recent work [21] derived a stochastic model for the number of accidents in the platoon of vehicles equipped with a warning messages communication system. Nevertheless, all the parameters in the model were described by random variables, which cannot give a reliable collision prediction for the real-time traffic scenario. Thus, based on the analysis method in [21], we derive a more reliable and practical stochastic collision prediction model, which takes full advantage of the beacons and warning messages.
In this paper, by combing vehicle collisions model with TDMA-based mechanism, we design a risk-aware and dynamic MAC protocol for the considered CCA application. Besides the reliable and real-time delivery of messages, the fairness between beacons and warning messages on the wireless medium access are also achieved.
3. Details of Risk-Aware Dynamic MAC Protocol
This section mainly presents the detailed description of the dynamic and risk-aware MAC protocol, including the considered traffic scenario, specification of frame structure, and slots allocation algorithm for CSMA and TDMA segments. The number of slots in the CSMA segment is determined by the average total number of potential collisions among the platoon and the corresponding computing method based on a stochastic collision prediction model is given in Section 4.
3.1. The Traffic Scenario
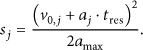
Prior to the detailed description of the proposed protocol, it is essential to give an overview of the considered traffic scenario in which our R-MAC operates. As shown in Figure 1, each RSU and all vehicles under its coverage form a vehicular Ad hoc subnet, which is similar to the model proposed in our previous work [22]. For sake of simplicity, we only consider a platoon of vehicles on highway, which travel along the same road towards the similar direction. However, with vehicles moving on roads at high speeds, the number of vehicles N and the corresponding vehicle density
Traffic scenario under consideration.
3.2. R-MAC Frame Structure
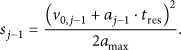
Now, we give the detailed specification of frame in R-MAC, which is a dynamic TDMA protocol. In R-MAC, we divide the time into periods called frames and then each of them is subdivided into tiny time slots uniformly. Every frame is divided into RSU segment and vehicle segment (see Figure 2). The RSU segment is reserved for RSU to disseminate control message and the latter is used for vehicles to transmit beacons and warning messages. In our protocol, the RSU segment always begins from the head of a frame and its size is a constant denoted by α, which means that the length of the vehicle segment is also determined. Based on the different priorities between beacons and warning messages, the vehicle segment is divided into two parts: CSMA segment which is responsible for transmitting warning message in emergency situations and TDMA segment which is in charge of delivering beacons. Without any loss of generality, we introduce β and γ to indicate the corresponding size of CSMA and TDMA segment, respectively.
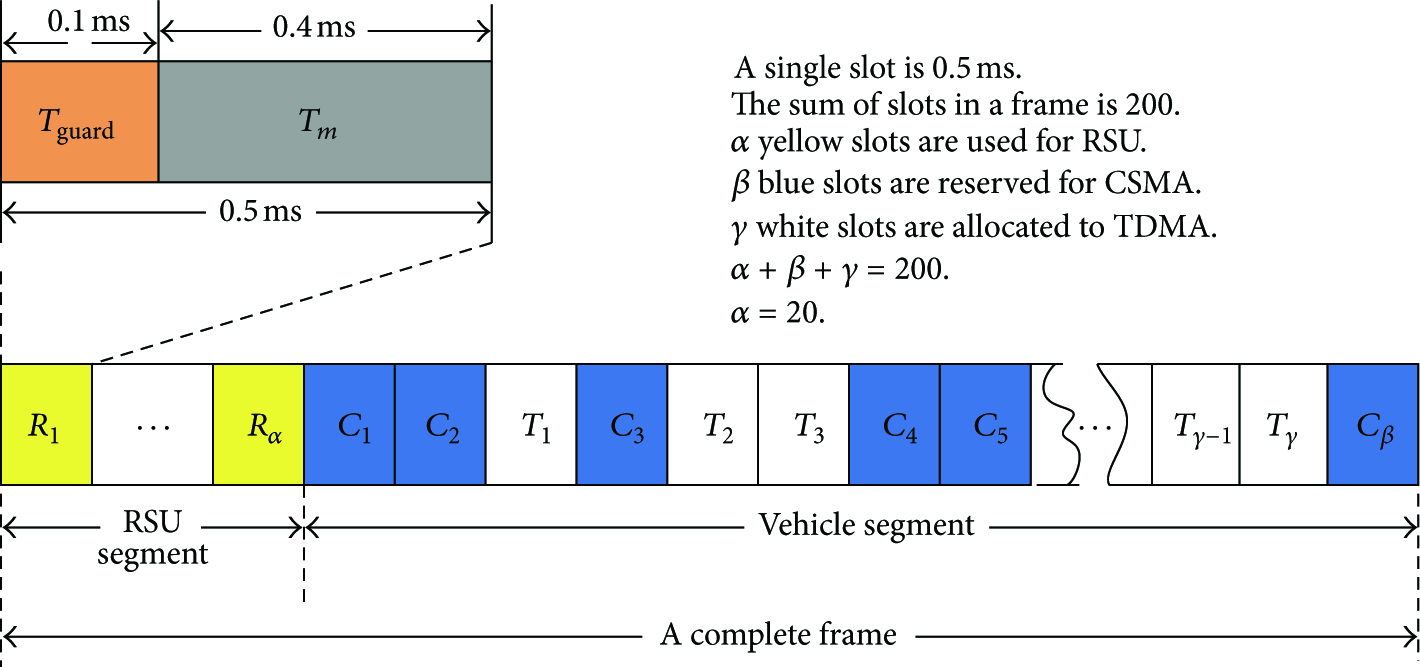
R-MAC frame structure.
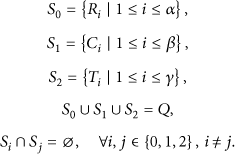
Based on the above description, we define three sets
Then, we define the time duration parameters according to the US standards within IEEE. The update frequency is
In the following, we give more detailed specifications for RSU and vehicle segments, separately.
3.2.1. Specification of RSU Segment
As shown in Figure 2, the number of slots reserved for an RSU is fixed and the size of set
3.2.2. Specification of Vehicle Segment
In contrast to the RSU segment, the vehicle segment of a frame is further divided into CSMA segment and TDMA segment. For the TDMA segment, a vehicle with a chosen slot will send beacon which contains safety-related information to vehicles around it and the corresponding RSU. However, for the CSMA slots, only delivery of warning (emergency) messages is allowed to contend the medium access in CSMA mode. When a vehicle desires to send a warning message, it first listens to the channel and waits for the CSMA slots. If the medium is idle, the vehicle is allowed to transmit. If the medium is busy, the vehicle will defer its transmission to the next CSMA slot, which is different from the exponential back-off mechanism executed in IEEE 802.11 MAC protocol [16]. In order to ensure sufficient slots for vehicles to sending warning messages, the size of CSMA segment is set as the average total number of potential collisions among the platoon in the next several frames. In our protocol, TDMA and CSMA segments coexist in each frame dynamically, which helps to achieve the delivery fairness between beacons and warning messages. In the worst case, all the slots of a frame are allocated for CSMA segment to transmit the massive amounts of warning messages and no slots are left for beacons, in which our protocol operates as a traditional CSMA-based MAC protocol just like IEEE 802.11p. Indeed, once the case above appears, the traffic accident must be disastrous and the whole network has to be flooded by massive of emergency messages. However, the probability of this case is little and both of beacons and warning messages have corresponding slots reserved to be transmitted for most case.
3.3. Slot Allocation Algorithm for CSMA and TDMA (SACT)
In this section, we describe how to allocate slots for CSMA and TDMA segments. The whole slot allocation algorithm abbreviated as
3.3.1. Slot Allocation for CSMA
The slot set of CAMS segment
3.3.2. Slot Allocation for TDMA
Once the slot set
In fact, the slot allocation procedure, including CSMA segment selection and TDMA slot allocation, is conducted on a particular RSU. Then, the RSU broadcasts the final slot allocation map to all vehicles moving under its coverage. Based on the above description, the integrated
Compute the average total number collisions among the vehicles platoon by Algorithm 2; Select Push the slots whose id equals to the above selected For
For each vehicle in the coverage of a RSU If the RSU received a beacon in the last three Frame Then select a slot s from set remove s from Else remove the vehicle from the vehicle list under its coverage; The RSU broadcast the vector vehicles
4. Computation of the Size of CSMA Segment
As described in the SACT algorithm in Section 3, the corresponding size of CSMA segment in a frame is determined by the average total number of potential collisions
4.1. Stochastic Collision Prediction Model
Prior to a detailed description of the envisioned stochastic collision prediction model, we point out a number of assumptions regarding the considered traffic scenario in this paper, which are listed as follows.
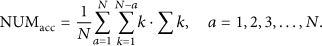
The distance between two neighboring vehicles, named intervehicle space, is a random variable. Moreover, it is an exponentially distributed random variable with parameter λ, which represents the density of vehicles on the road and equals to Each vehicle is capable of estimating its motion state accurately, including velocity, regular acceleration.
The first assumption is based on the fact that inter-space calculated by real-time coordinates on map benefit from GPS and GIS is not accurate and reliable, because the positioning precision of GPS hardly meets the need of the considered scenario. In the worse case, a vehicle is evolving into more critical areas; there may be certain undesired problems in the availability of GPS in certain scenarios where GPS signals may not be detected (e.g., such as inside tunnels and underground parking). Moreover, it has been shown that exponential distribution describes well the intervehicles space when traffic densities are small [24]. In addition, it is easy to get accurate velocity and acceleration of a vehicle, via adequately deployed sensor monitoring the motion state of a vehicle in real-time.
The collision scenario considered in our paper is a platoon (or a chain) of N vehicles traveling along the same road toward the same direction. As a vehicle

Collision model under consideration.
Within this model, the accidental vehicle

Probability graph defined in the collision model.
The transition probability between two nodes in the graph is the corresponding collision probability between adjacent vehicles in the chain
To compute the probabilities of the final outcomes, we can construct a Markov chain whose state diagram is based on the previously discussed probability graph. If the following accidental collisions are caused by the vehicle

Probability graph and corresponding transition matrix for scenario where the collision is caused by vehicle
Then, we compute the probabilities of paths which start from state node
4.2. Compution of the Adjacent Vehicles Collison Probability
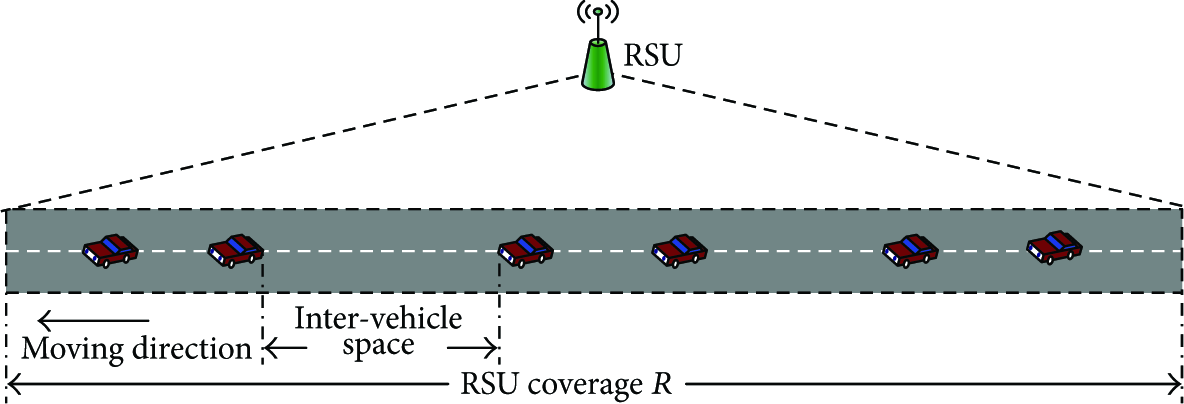
In this section, we come to the problem of computing the collision probabilities
Based on the analysis of the vehicular moving procedure for vehicle in [20, 25], a complete braking procedure is divided into three different stages where acceleration a of a vehicle varies along with time as shown in Figure 6. As mentioned above in the collision prediction model, we still let
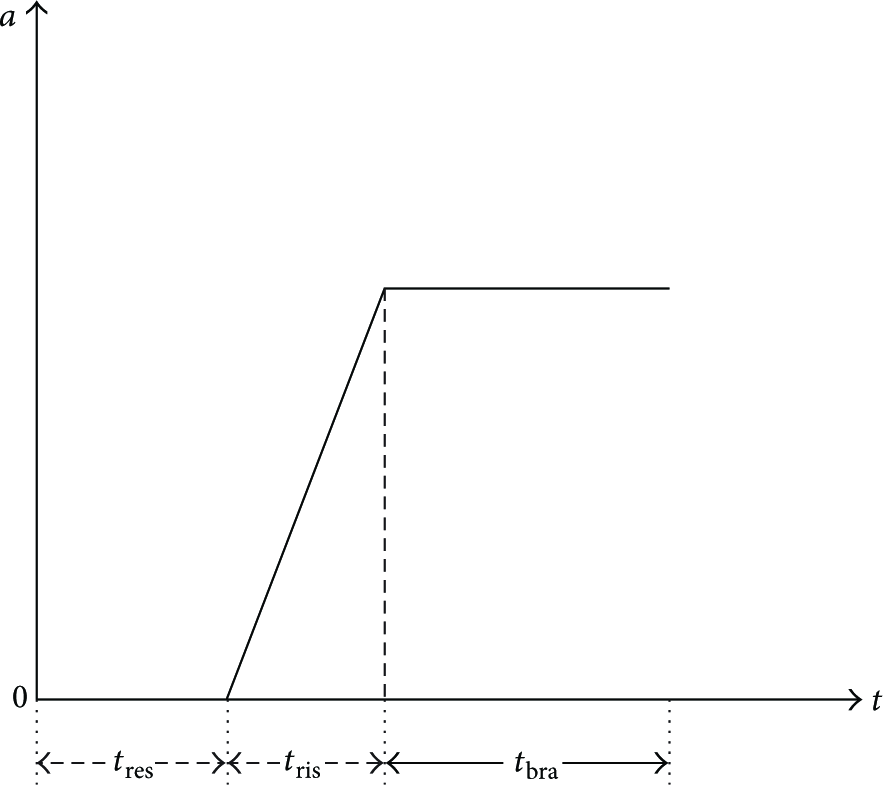
A complete vehicle braking process.
In order to compute the collision probabilities
Definition 1.
Minimum safety distance in our work is defined as the needed minimum distance between two adjacent vehicles to avoid collision based on V2V communications, both of which receive a warning message and start to brake hard at the same time.
For simplicity, we assume that all the vehicles have the same mechanical brake performance with a common maximum deceleration value

MSD model for vehicles
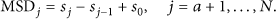
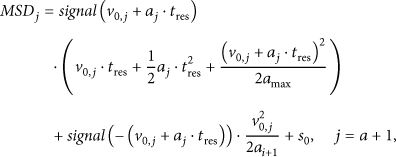
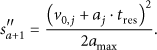
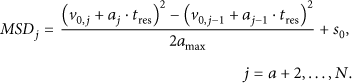
According to the different movement states, we further divide the computation of MSD into three cases as follows. In case 1, the vehicle
Corollary 2.
If the vehicle
Proof.
Noting that the accidental vehicle
If
Corollary 3.
If the vehicle
Proof.
Based on the assumption that
Obviously, the displacement for vehicle
Corollary 4.
In this situation, the velocity of
Proof.
In contrary to case 2, the distance between
4.3. Validation of Stochastic Collision Prediction Model
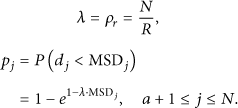
Based on the above detailed description in Sections 4.1 and 4.2, the integrated computation method of the total average number of potential accidents in the platoon (CMAA) is formally described in Algorithm 2. In order to verify the effectiveness of stochastic collision prediction model, we conduct a Monte Carlo simulation and compare the simulation results with that of CMAA algorithm. In the simulation, the initial speed
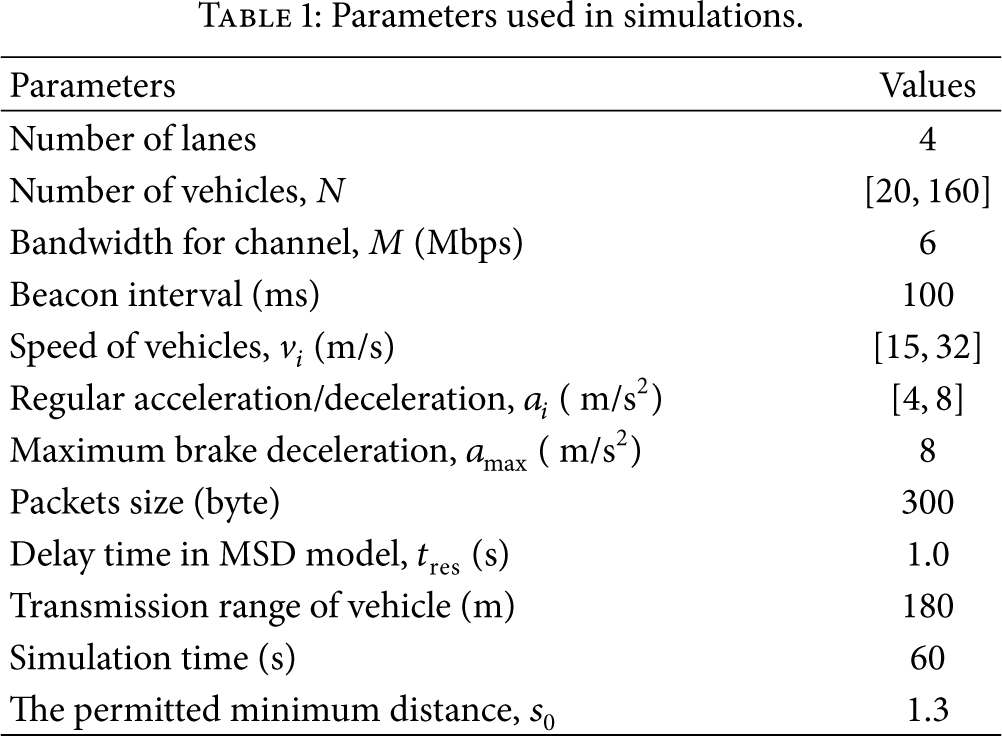
Parameters used in simulations.
For If Then Else if Then Else End for
For End for
Compute the matrix For End for

Average total number of collisions in the platoon versus average intervehicle distance.
5. Performance Evaluation
In this section, we describe the simulation results to demonstrate the efficiency of the proposed R-MAC protocol. In our simulation, we implement our R-MAC protocol on the NS-2 simulator and evaluate its performance fairly against the IEEE 802.11p, which is the standardized MAC protocol for VANET. The objective is two-fold: (1) evaluate the fairness of the medium access between beacons and warning message and (2) compare the performance of R-MAC and IEEE 802.11p on the packet loss rate and transmission delay.
5.1. Simulation Settings
The R-MAC protocol is implemented on the network simulator (NS-2.33). In order to conform to the realistic traffic scenario, a 1000 m × 300 m rectangle road network with a straight 4-lane highway is created, where a 3G station is introduced to act as a RSU. Different traffic loads of the road are considered by setting various vehicle numbers. All the traffic scenario and vehicle mobility patters are generated from the VanetMobiSim engine [27]. For each traffic loads, the simulation are conducted ten times to take the average result.
During our simulation, each vehicle broadcasts a beacon packet of 300 bytes every 100 ms. When a vehicle encounters an obstacle or collision with its preceding vehicle, a packet of 300 bytes is sent immediately backwards to simulate a warning message. For simplicity, we assume that a collision will happen when the intervehicle space is less than the permitted minimum distance
5.2. Evaluation Metrics
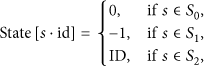
The performance of the R-MAC protocol is evaluated in terms of average packet delivery rate, delay and fairness. The particular evaluation metrics are defined as follows.
5.2.1. Packet Delivery Rate
Packet delivery rate is defined as the rate of the total number of data packets transmitted successfully to the total number of data packets sent from source vehicles to the destination vehicles in the whole simulation.
5.2.2. Delay Metric
In our simulations, we just consider the delay caused in the MAC layer, which is defined as the total time elapsed since the message's (beacon or warning) generation till it accesses the medium and is sent out successfully by a vehicle. And we count the average delays of beacons and warning messages together.
5.2.3. Fairness of the Medium Access
In order to quantitatively evaluate the fairness of the medium access between beacons and warning messages, we adopt the Jain's fairness index in [28]. Prior to the particular definition of Jain's fairness index in this paper, we first introduce the medium utilization for both beacons and warning messages, denoted by 

5.3. Simulation Results
The first set of experiment mainly investigates the performance of R-MAC on the average packets delivery rate, where beacons and warning messages are counted together. We vary the number of vehicles from 20 to 160 with an interval of 20 to simulate various traffic loads. As the number of vehicles increases, more packet collisions will occur, which leads to the decrease of the average packets delivery rate. Figure 9 shows that the average packet delivery of 802.11p experiences an abrupt fall from 75% to 60%. While in our R-MAC protocol, the average packets delivery rate is kept above 85% before the number of vehicles reaches 100. Even in a heavy traffic scenario where the number of vehicles is up to 160, the average packet delivery rate is still around 75%, which guarantees the Qos in safety-related applications greatly.

The packets delivery versus number of vehicles.
The second experiment mainly observes the performance of the R-MAC protocol on the average delay of the medium access. Similar with the first experiment, we count the delay of beacons and warning messages together. Figure 10 shows that the average delay of the medium access increases with the increase of the vehicle number. In addition, the delay gap between R-MAC and 802.11p becomes larger and larger (better) with the increase of the vehicle number, which verifies a good performance of average delay in our R-MAC. Nevertheless, as seen from Figure 10, R-MAC and 802.11p reach nearly the same delay performance (reaching up to 115 ms) when the number of vehicles increases to 140. Obviously, neither the R-MAC nor 802.11p protocol can work well in the heavy traffic situations. So, we will study the traffic overload tolerant R-MAC in the future.
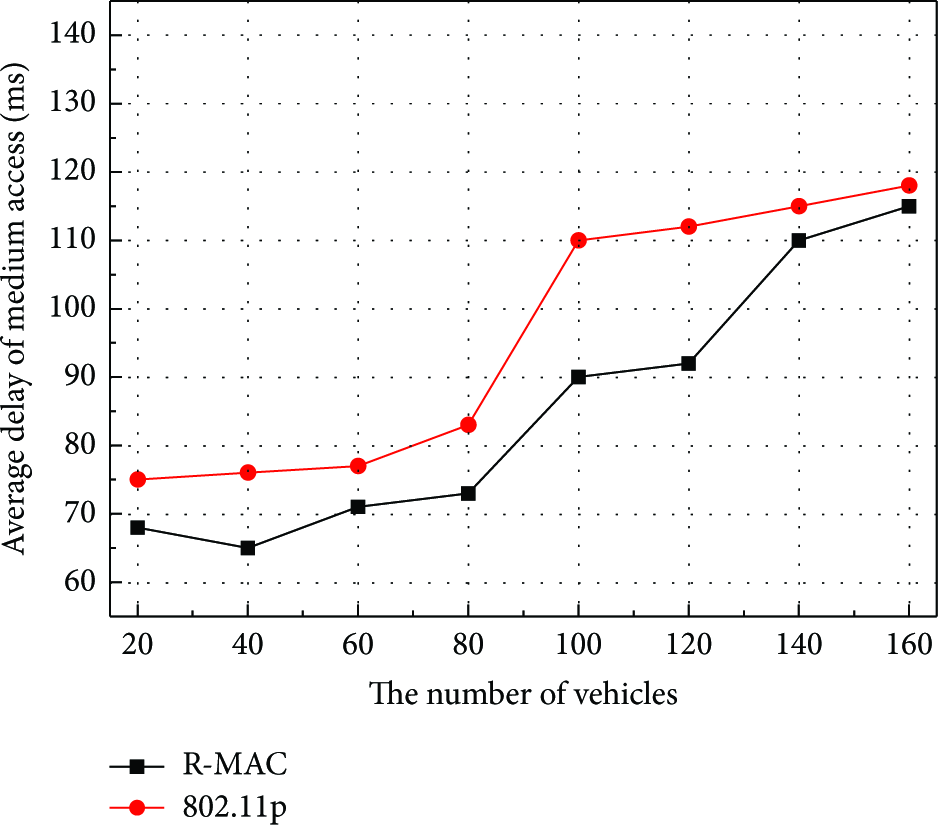
Average delay of the medium access versus number of vehicles.
In the third set of experiments, we mainly investigate the performance of R-MAC on the medium utilizations between beacons and warning messages. Various traffic loads are configured the same as the first experiment. As seen from Figure 11, when the number of vehicles on the road is small (less than 40), the medium utilizations of warning messages approach 100% in both R-MAC and 802.11p. That is because there are few warning messages generated when the traffic is light, and there are enough slots and chance for them to be transmitted. With the increase of vehicles, particularly from 60, the medium utilizations of warning messages and beacons decrease dramatically in 802.11p, which is caused by the more and more collisions among messages. However, even in a heavy traffic (number of vehicles more than 140), Figure 11 shows that the medium utilizations of beacons and warning messages are greater than 82% and 40% in our R-MAC, respectively.
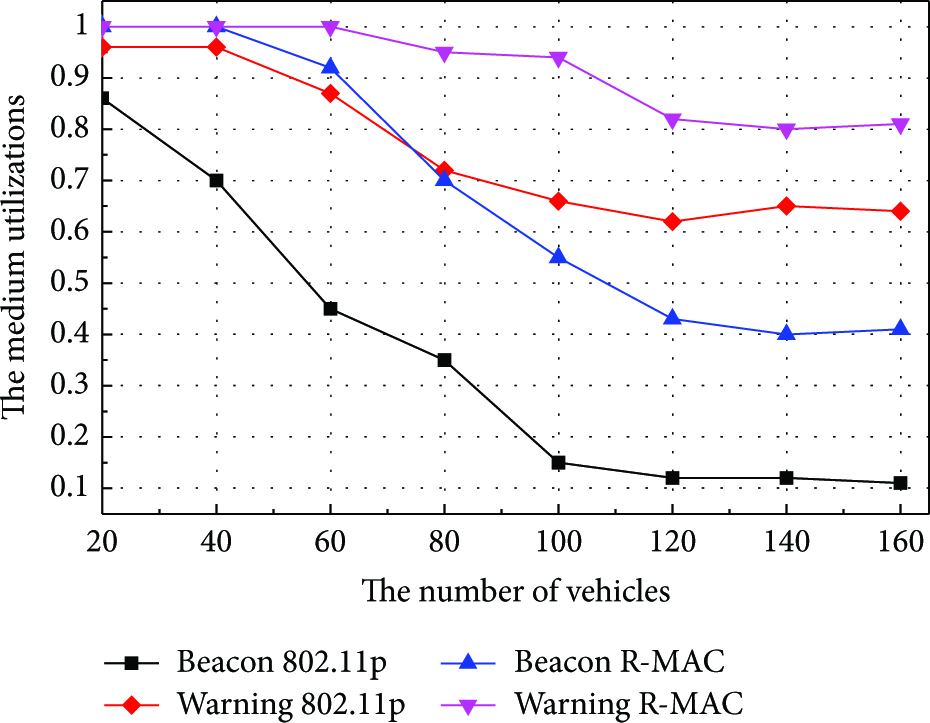
The medium utilization versus number of vehicles.
In order to demonstrate the fairness of the medium access between beacons and warning messages, the final experiment is conducted with the same settings as the third one. The Jain's fairness index is computed and plotted in Figure 12. As shown in Figure 12, the Jain's fairness index decreases dramatically with the increase of vehicles in 802.11p, which is caused by inherent attribute of contest in CSMA and different priorities of messages. When the number of vehicles reaches up to 140, the Jain's fairness index in 802.11p even drops to 0.65, which almost indicates the worst case. However, the Jain's fairness index in R-MAC always floats between 0.9 and 1.0, which means that a good fairness between beacons and warning messages is achieved. Compared with 802.11p, our proposed R-MAC protocol can improve the Jain's fairness index by about 39% even in heavy traffic scenarios.
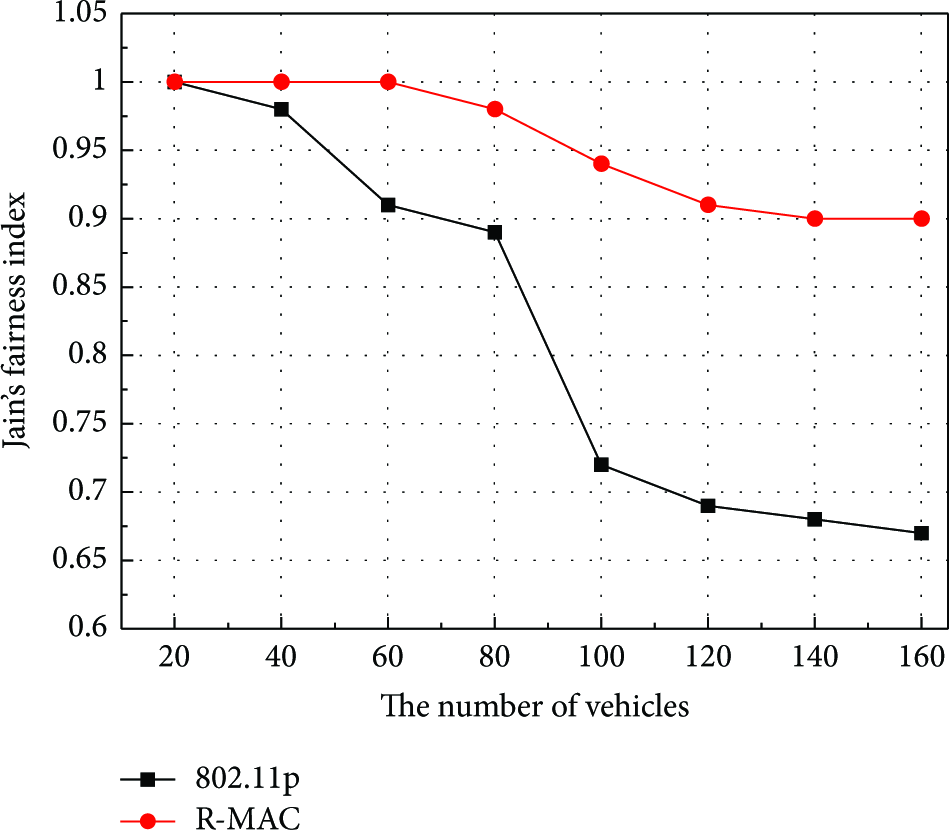
Jain's fairness index versus number of vehicles.
6. Conclusions
This paper has studied the dynamic MAC protocol problem to satisfy real-time and reliable delivery of messages while achieving the fairness of the medium access between different kinds of messages in cooperative collision avoidance (CCA) systems. We have designed a risk-aware dynamic medium-access control (R-MAC) protocol for this problem. In order to ensure the accuracy of risk-aware in R-MAC, a stochastic prediction model of the average total number of potential collisions in the platoon is presented. Extensive Monte Carlo simulations verify that our model is reliable and practical enough. Efficiency and fairness of R-MAC are verified by simulations against the standardized MAC 802.11p protocol of VANET. The simulation results show that R-MAC can improve the Jain's fairness index by about 39% compared with 802.11p. Even in heavy traffic scenarios, the packet delivery rate is still above 80% in R-MAC and the average delay is reduced significantly, which meets the communication requirements in CCA systems adequately in general scenarios. From the simulations, we have found that the transmission delay is relatively lager in overload traffic scenario. As a future work, we will study the traffic overload tolerant R-MAC protocol for CCA applications.
Footnotes
Acknowledgments
This paper is supported by the National Grand Fundamental Research 973 Program of China under Grant No. 2011CB302905, the National Science Foundation of China under Grant No. 61170058, 61272133 and 61228207, National Science and Technology Major Project under Grant No. 2011ZX03005-004-04 and 2012ZX03005009, Special Project on Industry Technology of Suzhou (No. ZXG201041), and China Postdoctoral Science Foundation under Grant No. 20110490821.