Abstract
Security and privacy have been important issues in VANETs. Anonymity is an effective way to achieve privacy protection, and it sometimes requires to be disclosed for determining traffic liability. In most pseudonym schemes, an authority is aware of a vehicle's secret, and its compromise will result in the leakage of a large amount of privacy information. So, we propose a distributed traceable pseudonym management scheme in VANETs. In the scheme, a blind signature method is adopted to achieve strict separation of issuance and tracking. The distributed tracking protocol is proposed to enhance the robustness for tracking, which is based on the improved scheme for shared generation of RSA keys. An efficient pseudonymous authentication mechanism is proposed to reduce the communication overhead. Compared with other related proposals, our scheme is unforgeability, especially against authority forge attacks, and has better robustness. Moreover, the performance analysis shows that it is efficient in VANETs.
1. Introduction
Vehicle-to-vehicle and vehicle-to-infrastructure communications improve vehicle's perception from the surrounding environment. Vehicular ad hoc networks (VANETs) will be used widely in collision avoidance, road-hazard notification, and coordinated driving systems [1]. Nonetheless, there are many security threats in VANETs [2–4]. For example, an attacker might tamper with messages to evade accident liability or forge information to meet specific needs. The attacker also might eavesdrop on broadcast messages, analyze data, and track a vehicle. So, security and privacy have been important issues in VANETs.
A number of studies have been made on the issues of security and privacy preservation. Raya and Hubaux [5, 6] pointed out that anonymity is conditional for liability purposes and that authority can disclose the pseudonym. In [5, 6], a security protocol was introduced. Although this protocol can effectively meet the conditional privacy requirement, it is far from efficient and can hardly become a scalable and reliable approach, because the authority has to keep all the anonymous certificates for each vehicle. Lin et al. [7] proposed a security and privacy preserving protocol. With group signature, security, privacy, and traceability can be achieved without inducing the overhead of managing a huge number of stored certificates at the authorities' sides. Calandriello et al. [8, 9] proposed on-the-fly pseudonym generation and self-certification, which alleviates the overhead of managing certificates. Group signature method is adopted to ensure that legitimate nodes can generate their pseudonyms anonymously. Lu et al. [10] presented a conditional privacy preservation protocol, which improves efficiency in terms of the minimized anonymous keys storage at each vehicle. Performance evaluation shows that the protocol can achieve much better efficiency than Raya and Hubaux's [5, 6] and Lin et al.'s [7] when vehicles are revoked. Zhang et al. [11] proposed a scalable robust authentication protocol. In [11], some roadside units (RSUs) serve as the issuer of vehicles' private key, and a signcryption method is employed to distribute the keys securely. Hao et al. [12] proposed a distributed key management framework, which has advantages in the revocation of malicious vehicles and system maintenance. An efficient cooperative message authentication protocol is developed to reduce the computation and communication overhead in the group signature.
The above reported schemes [7–12] are based on group signature. In Boneh et al.'s group signature scheme [13], each user's private key is generated by the private-key issuer, which is a hidden security threat. In [7–9], each vehicle's group private key is computed by a member manager. In [10], a trusted authority is required; the authority generates valid private keys for on-board unit and RSU. In [11], RSU generates and sends the group private key to the vehicle. In [12], some measures are adopted to prevent RSU from misbehaving, but authorities cannot decide which is the malicious, RSU or the vehicle or both, when they find a mismatch. Therefore, these schemes [7–12] suffered from private key revealing attacks, in which the private-key issuer knows each user's private key.
Schaub et al. [14] adopted blind signature technology to achieve the separation of issuing and tracking. But the disadvantages of the scheme are that V-token (
To solve the above problems, this paper presents a distributed pseudonym management scheme in secure VANETs. The main contributions of the scheme are as follows. (1) Pseudonym is coproduced by the issuer and the vehicle. Either party attempting to deceive can be detected. It can resist authority forge attacks. (2) An efficient pseudonym authentication mechanism is proposed by finding the optimal number of messages with the pseudonym certificate, which not only reduces the communication overhead but also ensures the message authentication probability
The remainder of this paper is organized as follows. The pseudonym management model is given in Section 2. The pseudonym issuance protocol, the pseudonymous authentication protocol, and the distributed tracking protocol are presented in Sections 3, 4, and 5, respectively. Section 6 analyzes and compares the security and the performance of our scheme with other related schemes. Finally, the conclusion of this paper is given in Section 7.
2. Pseudonym Management Model
There are three types of entities: (1) a vehicle (V). Its identity is
The security and privacy requirements in the model are as follows.
Anonymity. For other entities (such as PCA, attackers) except TAs, it is computationally infeasible to disclose the identity from a pseudonym.
Traceability. If the members in TAs implement the protocol honestly, at least m members can disclose collaboratively the identity from a pseudonym.
Unforgeability. For any entity, it is computationally infeasible to forge a false signature or impersonate another entity.
Robustness. If any authority compromises, the implementation of pseudonym issuance, pseudonymous authentication, and tracking are not affected.
The process of pseudonym management is shown in Figure 1. (1) The vehicle V gets an identity certification from CA. (2) V applies for pseudonym certificates. (3) PCA issues some pseudonym certificates to V. (4) V communicates with other vehicles and RSU with the pseudonym certificates. (5) Once other vehicles find suspicious vehicles, they submit a tracking request to TAs. (6) TAs disclose the identity from the pseudonym.

Pseudonym management framework.
The model consists of three protocols: a pseudonym issuance protocol, a pseudonymous authentication protocol, and a distributed tracking protocol. TAs' public key
3. Pseudonym Issuance Protocol
Chaum [16] first proposed the concept of a blind signature, which allows users to get a message signature without leaking any contents. The pseudonym certificate issuance protocol adopts the blind signature method.
V sends PCA verifies V extracts V extends them to V sends PCA the blind alternative commitments PCA randomly generates verification set I, V shows PCA computes V removes the blind factors
The prerequisite of implementing the protocol is that during the initialization stage, V has got TAs' public key
In Schaub et al.'s issuance protocol [14], CA signs V-tokens for a vehicle. Pseudonym provider (PP) checks the validity of V-tokens; if valid, PP issues a pseudonym certificate. Four rounds of interaction are required. If CA wants to cheat, it will not interact with a vehicle. And it will obtain a fake pseudonym certificate and impersonate a vehicle, so will PP.
In our issuance protocol, PCA issues directly a pseudonym certificate to a vehicle, and three rounds of interaction are required. A pseudonym is coproduced by V and PCA. PCA cannot provide
As a result, our issuance protocol maintains good property of vehicular privacy in the presence of an authority and provides security against authority forge attack. Moreover, the communication overhead is reduced from four rounds to three rounds.
4. Pseudonymous Authentication Protocol
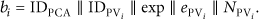
A complete authentication message consists of six fields: messageID
If each message carries a certificate of 796 bytes during the same pseudonym period, the communication overhead is high. If only the first message carries the certificate, the message length is reduced from 1031 bytes to 235 bytes. However, if the first message with the certificate does not arrive at the receiver, other received messages which do not contain the certificate cannot be verified.
Some researchers proposed a mechanism to reduce the communication overhead of secure messages by omitting the inclusion of certificates in messages. Concrete methods such as the periodic omission of certificates, neighbor-based certificate omission, and congestion-based certificate omission were proposed in [9], [18], and [19], respectively. In these schemes, the optimal parameter was obtained by means of simulation. In contrast to the earlier proposals, we found the optimal parameter by means of probability analysis.
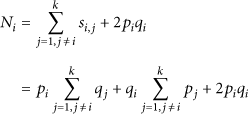
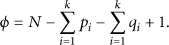
Define that α is the number of messages and λ is the number of messages with pseudonym certificate during one pseudonym period. If at least one message with certificate is accepted by the receiver, other arrived messages with the same pseudonym can be authenticated. Define the message authentication probability
Figure 2 shows the relationship among the message authentication probability
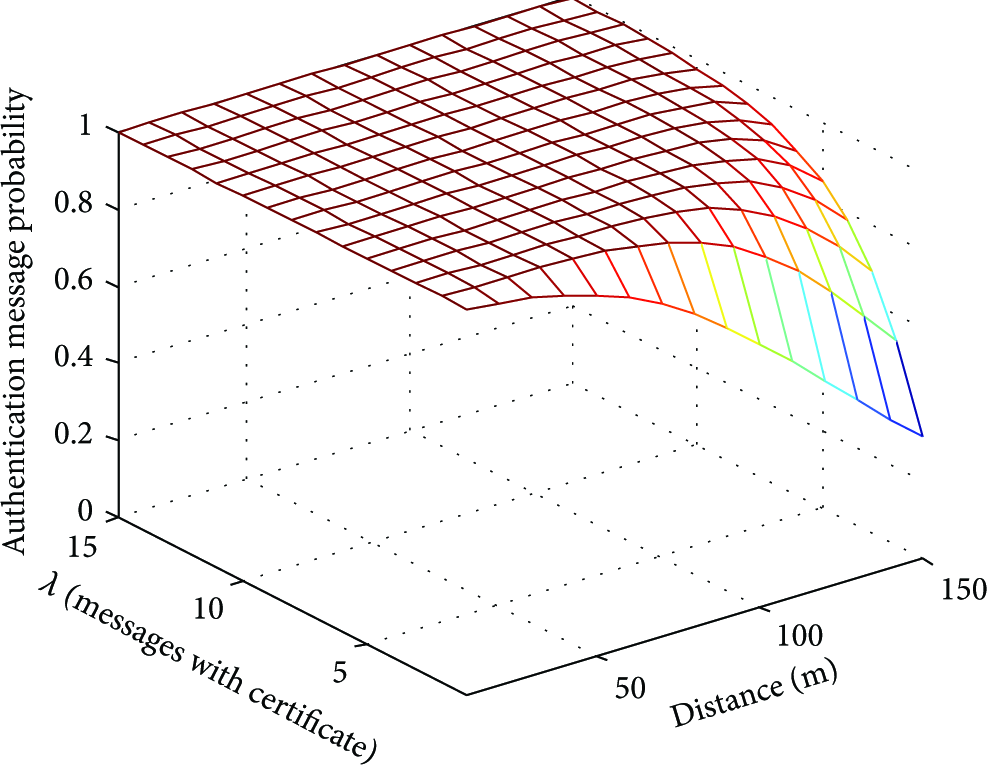
Impact of different d and λ on pseudonymous authentication.
We define

Relationship between average message length and the number of messages during a pseudonym period.
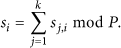
5. Distributed Tracking Protocol
Based on the secret sharing scheme [20], TAs' private key d is assigned to the k authorities, and any one subset of at least m of them can disclose the secret. Generally, there is a trusted center during the initialization stage of the secret sharing scheme. Once the center compromises, the privacy will be leaked. Boneh and Franklin [21] discussed the generation of RSA keys without a dealer, but the protocol required the help of a third party. Cocks [22] presented another protocol to generate shared RSA keys without the help of a third party. There exists a large number of modular exponentiation operations to generate the modulus, and thus the efficiency of the protocol is poor. Malkin et al. [23] extended two parties [21] to k parties.
Instead of time-consuming modular exponentiation, we use modular multiplication to generate N, where N is the modulus of RSA. And furthermore, we extend the
5.1. Distributed Generation of Modulus N
Each member and broadcasts All members compute Any member in TAs picks an integer TA1 computes and broadcasts If the verification fails, all members execute steps (1)–(6) again. Otherwise, success is returned.
5.2. Distributed Generation of Private Key and Secret Share
TA1 computes
After implementing the protocol, each member obtains the private key
5.3. Collaborative Tracking
The vehicle If passed, TA1 extracts IDPV from CertPV and sends IDPV to other members. If Participants TA1 tries all possible u and x (
It extracts
Then TA1 submits
In Lin et al.'s protocol [7], a centralized method for tracking is adopted. A trace manager (TM) computes a vehicle's private key from a signed message in order to disclose the vehicle's identity. Once TM is compromised, a large amount of privacy information is leaked.
In Schaub et al.'s protocol [14], the secret sharing method for tracking is adopted to prevent misuse and abuse of a system. The method is distributed, but it generally requires a trusted center to distribute secret share in the initialization phase. Therefore, the trusted center will be a secure bottleneck.
In our tracking protocol, all the processes in the secret sharing method adopt a fully distributed structure, such as generation of private key and secret share, generation of modulus N and collaborative tracking. As a result, our tracking protocol avoids a single point of failure.
6. Analysis
6.1. Security Analysis
Proposition 1.
Neither issuing authorities nor other vehicles can determine the relationship between a pseudonym and an identity in the protocol family, so the scheme achieves anonymity.
Proof.
(1) During the issuance stage, PCA gets
(2) Other vehicles get the signed messages and extract
Proposition 2.
The m authorities in TAs can disclose the identity
Proof.
Let
Since
Construct a degree
Taking the formula (10) into the formula (9), we can obtain the following formula:
Consider the issuance protocol and obtain
Compute
Proposition 3.
Regardless of the PCA, the vehicles and the outside attacker, forging the pseudonym certificate is as difficult as solving a large integer factorization problem.
Proof.
A pseudonym PCA cannot provide V cannot provide An external attacker without V's and PCA's private keys cannot pass the authentication, because the issuance protocol is with two-way authentication. Therefore, the attacker neither obtains the blind signature nor personates PCA to sign the pseudonym certificate.
In short, forging an RSA signature or cracking an RSA cipher is as difficult as factorizing a large integer, so the scheme achieves unforgeability.
Proposition 4.
The scheme is robust.
Proof.
(1) The separation of pseudonym issuance authorities and tracking authorities, to some extent, reduces the risk.
(2) Some PCAs are deployed in the model. Once a PCA fails, other PCAs can still provide pseudonym issuance service.
(3) In the pseudonymous authentication protocol, the optimal number of messages with the pseudonym certificates is suggested. It ensures the message authentication probability
(4) During the TAs initialization stage, the generation of modulus N and the generation of the private key and the secret share are distributed fully. So, the scheme does not require a trusted center, and it avoids any single point of failure.
(5) During the TAs operation stage, as long as the number of compromised members is not more than
We further compared our scheme with similar works that are intended to ensure conditional privacy preserving communication [7, 14]. The results of comparisons of security features among our scheme, Lin et al.'s scheme [7], and Schaub et al.'s scheme[14] are shown in Table 1. All the three schemes provide anonymity, traceability, and authentication.
Security features comparisons.

Lin et al.'s scheme is based on a group signature method, in which a member manager (MM) generates member private keys and sends them privately; MM knows all private keys, and it can forge a valid group signature on an arbitrary message. Schaub et al.'s scheme adopts a blind signature method to issue certificates, and thus CA or PP does not know the relationship of an identity and a pseudonym; unfortunately, CA or PP can forge a pseudonym certificate for itself. Therefore, Lin et al. and Schaub et al.'s schemes are not secure against authority forge attacks. In our scheme, a pseudonym is coproduced by a manager and a vehicle; neither PCA nor V is capable of providing complete data to forge a pseudonym; our scheme is unforgeability, especially against authority forge attacks.
As mentioned in Section 5, the tracking methods for Lin et al., Schaub et al. and ours are centralized, distributed, and fully distributed, respectively. Our scheme has better robustness.
6.2. Performance Analysis
6.2.1. Computation Overhead
For convenience to evaluate the computation cost of the protocol, we ignored the computation cost of some operations such as a hash function and a multiplication operation, since they are quite light in terms of load. We focused on some time-consuming operations defined in the following notations.
In order to provide the precise comparisons of computation cost, we use the experiment data in [24–26] to evaluate them. The experiment environment is operated on a standard PC, whose processor is Pentium IV with the maximum clock speed of 3 GHz. The pairing system is considered the Tate pairing system. The order of a nonsupersingular curve over a finite field
The results of comparisons of computation cost are shown in Table 2, where n is the number of pseudonym certificates obtained at one time and k is the number of tracking authorities. Some common parameters and secret keys are generated in the system initialization, and for convenience we did not evaluate the computation cost of the initialization in all the three schemes. In Schaub et al.'s scheme and ours, the average computation costs for issuance and tracking are considered.
Computation cost comparisons.

Compared with Lin et al.'s scheme, ours and Schaub et al.'s scheme require less computation for signature and verification and more computation for issuance and track. Compared with Schaub et al.'s, our scheme requires less computation for issuance if
6.2.2. Communication Overhead
In Table 3, α is the number of signed messages and λ is the number of signed messages with pseudonym certificate during one pseudonym period in the authentication protocol; m is the threshold value in the distributed tracking protocol. The communication cost of Lin et al.'s scheme is the lowest, but their scheme suffered from the private key revealing attacks, in which MM knows the private key of each member. Schaub et al.'s scheme and ours rely on the blind signature method and achieve vehicular privacy protection in the presence of the authority. Compared with Schaub et al.'s scheme, our scheme is efficient in terms of the communication overhead.
Communication cost comparisons.

6.2.3. Storage Overhead
In Schaub et al.'s scheme and ours, the storage cost of the vehicle is high because some pseudonym certificates need to be stored; the storage cost of the manager for tracking is very little because an identity can be obtained directly from the pseudonym certificate. On the contrary, the storage cost of the manager in Lin et al.'s scheme is high because the record set
7. Conclusions
In this paper, a secure and efficient pseudonym management scheme for vehicular ad hoc networks is proposed. The scheme not only maintains the property of conditional privacy preservation but also provides the advantages in security against authority forge attacks and better robustness. In the scheme, a pseudonym is coproduced by V and PCA to avoid the deception of either party. A blind signature method is used to achieve the separation of issuance and tracking. Based on the improved share generation scheme of the RSA keys, the distributed tracking protocol is proposed to avoid a single point of failure. By searching for the optimal number of messages with a pseudonym certificate, the efficient pseudonym authentication mechanism is given to reduce communication overhead. By uniting the pseudonym issuance protocol and the tracking protocol, malicious vehicles are revoked easily. Moreover, compared with Schaub et al.'s scheme, the communication cost and computation cost in our scheme are lower. As a result, our proposed scheme is suitable for anonymous communication with tracking requirements in VANETs, since it provides security, robustness, and efficiency.
For future research, we will discuss interdependencies of various factors, establish systematic evaluation mechanism of the overall performance, and further enhance the performance.
Footnotes
Acknowledgments
The authors acknowledge the financial support of the National Natural Science Foundation of China (no. 60873195), the National High Technology Research and Development Program (“863” Program) of China (no. 2011AA060406), and the Natural Science Foundation of Anhui Province (no. 090412051). The authors are grateful for the anonymous referee for the careful checking and helpful comments that improved this paper.