Abstract
We propose a secure and lightweight key distribution mechanism using ZigBee Pro for ubiquitous sensor networks. ZigBee consumes low power and provides security in wireless sensor networks. ZigBee Pro provides more security than ZigBee and offers two security modes, standard security mode and high security mode. Despite high security mode, ZigBee Pro has weakness of key distribution. We use enhanced ECDH for secure key distribution in high security mode. Our simulation results show that the energy consumption of our approach decreases and the average run time is decreased by 39%. Moreover, the proposed scheme enhances security, that is, confidentiality, message authentication, and integrity. We also prove that the proposed key distribution can resist man-in-the-middle attack and replay attack.
1. Introduction
Various sensors in a sensor network technology are located within wired/wireless network infrastructures. Spatially distributed autonomous sensors monitor physical or environmental conditions such as temperature, humidity, sound, vibration, pressure, and motion and pass their data through the wired/wireless network to a base station. Sensor network technology has been utilized in monitoring military, home automation, and health care systems, as well as agriculture and weather conditions.
Sensors have limited memory and throughput capacity for wireless sensor networks. Therefore, limitations of the sensor itself and the underlying vulnerability of wireless communication with the sensors must be considered. In addition, sensed and transmitted data in each field are usually private information or important authentication information. Thus, security is to be applied in most cases. For this, ZigBee [1] provides a low power consumption and security standard-based protocol for applications on wireless sensor networks. ZigBee was developed to address the following needs: low cost, security, reliablility and self-healing, flexibility and extendibility, low power consumption, being easy and inexpensive to deploy, being global with use of unlicensed radio bands, integrating intelligence for network setup and message routing.
ZigBee Pro [2] (the latest specification for ZigBee, is termed ZigBee-2007) revolves around mesh networking, enhancing security. ZigBee Pro [3] also supports a large number of interoperable standards, including ZigBee health care, ZigBee home automation, ZigBee remote control, ZigBee smart energy, ZigBee telecom services, ZigBee building automation, ZigBee input device, ZigBee light link, ZigBee network devices, and ZigBee retail services. The ZigBee home automation profile [4] for a smart home allows consumers to save money, be more environmentally aware, feel more secure, and enjoy a variety of conveniences that make homes easier and less expensive to maintain.
However, the enhanced key management mechanism still has vulnerabilities in key distribution. The ZigBee home automation profile has just been applied at the network level. An enhanced mechanism is needed for this.
CertiCom [5] issues ZigBee Smart Energy certificates to manufactures whose products are certified by the ZigBee Alliance. The ZigBee Smart Energy PKI uses Elliptic Curve Qu Vanstone (ECQV) implicit certificates, which serve as an identity certificate for each ZigBee Smart Energy device. However, it does not improve ZigBee Pro itself but uses PKI separately.
In this paper, we apply the ECDH (Elliptic Curve Diffie-Hellman) [6] key distribution mechanism for ZigBee Pro vulnerabilities and propose a more efficient ECDH using sub-MAC [7] that has message authentication and prevents man-in-the-middle attack and replay attack. Our research exhibits an enhanced key mechanism and message authentication in ZigBee Pro for ubiquitous sensor networks.
The rest of this paper is organized as follows. Section 2 presents related works. Section 3 presents the proposed enhanced key distribution mechanisms. Section 4 illustrates simulation environments and analyzes the simulation to evaluate the effectiveness of our scheme. In Section 5, we analyze our approach from the view point of security. Finally, we conclude this paper in Section 6.
2. Related Work
2.1. ZigBee Pro
ZigBee Pro is a standard specified in ZigBee-2007. ZigBee Pro improves the security of the ZigBee 2006 version with two new security modes: standard security mode compatible with the residential security of ZigBee-2006- and high security mode compatible with the commercial security of ZigBee 2006.
ZigBee security, which is based on a 128 bit AES (Advanced Encryption Standard) [8] algorithm, adds to the security model provided by IEEE 802.15.4. The security services of ZigBee include methods for key establishment and transport, device management, and frame protections. ZigBee uses three types of keys to manage security: Master, Network, and Link.
Master Keys are used as an initial shared secret between two devices, when they perform the key establishment procedure (SKKE) to generate Link Keys. Keys that originate from the Trust Center are termed Trust Center Master Keys, while all other keys are termed Application Layer Master Keys. Network Keys perform security for the Network Layer on a ZigBee network. All devices on a ZigBee network share the same key. High Security Network Keys must always be sent encrypted over the air, while Standard Security Network Keys can be sent either encrypted or unencrypted. Link Keys as an optional key secure unicast messages between two devices at the Application Layer. Keys that originate from the Trust Center are termed Trust Center Link Keys, while all other keys are termed Application Layer Link Keys. Table 1 summarizes the security keys.
Security keys.

ZigBee Pro offers two different security modes (i.e., Standard and High) and features as shown in Table 2 [9].
Security modes.
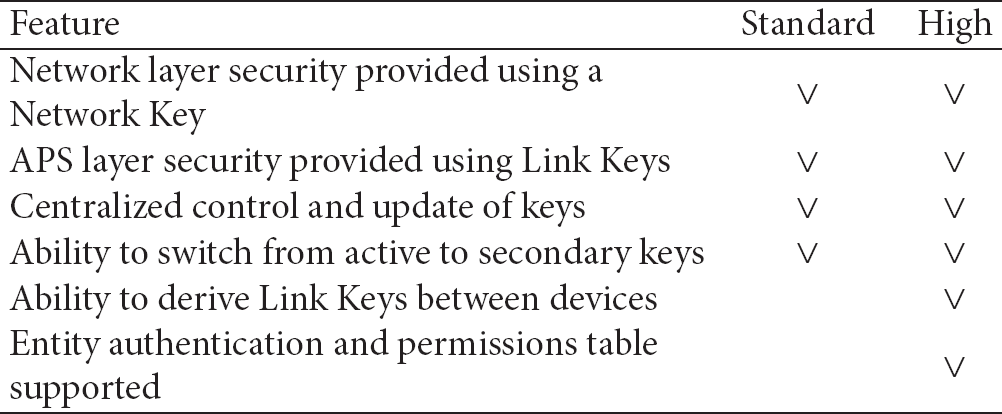
In the standard security mode, the list of devices, Master Keys, Link Keys, and Network Keys, can be maintained either by the Trust Center or by the devices themselves. The Trust Center is still responsible for maintaining a Standard Network Key; it controls policies of network admittance. In the high security mode, the Trust Center maintains a list of devices, Master Keys, Link Keys, and Network Keys that it needs to control and enforce the policies of Network Key updates and network admittance.
Unlike standard security mode, high security mode supports the ability to derive Link Keys between devices and entity authentication and permissions table supported. The Master Keys and Network Keys are preinstalled or transported; Link Keys are used in key-establishment based on a Master Key. Unencrypted key transport will give rise to serious security vulnerability [10].
2.2. ECDH
ECDH [6] is a key exchange algorithm, the well-known Diffie Hellman [11] key agreement based on ECC (Elliptic Curve Cryptography) [12]. ECDH is important in modern protocols as a key exchange and can be adopted for ECC. Figure 1 shows the key exchange process.
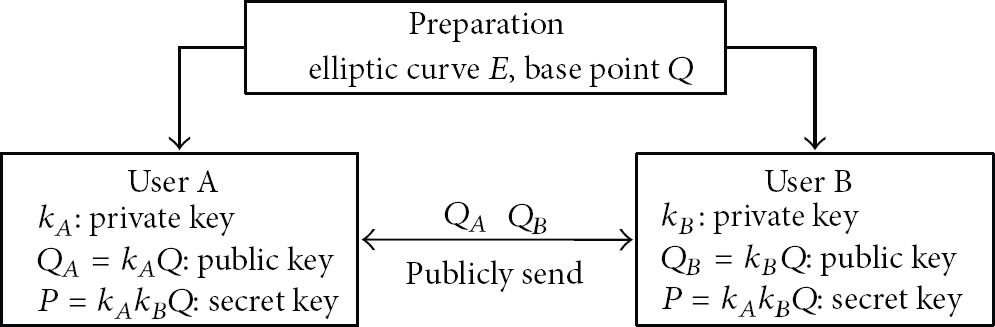
ECDH.
Consider two parties, A and B, willing to exchange a common secret key. Both have agreed to a common and publicly known curve E over a finite field, as well as to a base point Q. User A randomly chooses
3. Proposed ZigBee Key Distribution
3.1. Standard Security Mode
The transport-key command sent from the Router to the Joiner shall not be secured in standard security mode. For this, we apply ECDH for secure Network key generation and transmission and sub-MAC mechanism for message authentication and integrity. We proved that our scheme could provide efficiency by achieving a similar run time and similar energy consumed in standard security mode [16].
3.2. High Security Mode
If the Trust Center does not already share a Master or Link Key with the newly joined device, Figure 2 shows the high security mode authentication procedure of ZigBee Pro.

High security mode authentication procedure.
The Symmetric-Key Key Establishment (SKKE) protocol is a process in which an initiator device (Trust Center) establishes a Link Key with a responder device (Joiner) using a Master Key. The next step is an entity authentication process between Router and Joiner.
As in standard security mode, Update-Device Command and Secured Transport-Key Command are encrypted with Master key, but Transport-Key Command sent from the Router to the Joiner is not secure. This has a security issue.
The MAC scheme is used for key confirmation in SKKE. The first 128 bits of keying data shall be a Mac Key and the second 128 bits shall be a Link Key during Mac Key generation. After SKKE, the Network Key is securely transmitted using the Master Key.
We propose a procedure to ensure key secure distribution as shown in Figure 3.

Proposed key distribution in high security mode.
Trust Center → Joiner: J, Sub-MAC(
When the Trust Center receives an APSME-UPDATE-DEVICE.request message, the Trust Center generates an
A sub-MAC [7] is constructed by selecting some bits of an HMAC. We reduce the overhead by transmitting only a part of the actual HMAC, rather than the entire HMAC using sub-MAC. Sub-MAC guarantees message integrity and authentication. Our research selects 8-bits of 16 bytes. We assume each node has the same PRNG (Pseudo Random Number Generator) [18].
Joiner → Trust Center: TC, TC: Trust Center's 64-bit address Sub-MAC(Master K): sub-MAC using Master Key.
The Joiner sends
Trust Center → Joiner:
Next, the generated Master Key encrypts
4. Simulation and Results
The Qualnet simulator was used to evaluate the performance of the proposed scheme. Our research uses Qualnet 4.5 [19] with sensor network libraries based on the ZigBee protocol and additional protocols.
We composed one clustering network structures. The clusters were composed of 15 nodes. Node 1 is a Joiner, node 16 is a Router, and node 8 is a Trust Center.
4.1. Efficiency Analysis of Enhanced Key Mechanism
We propose an enhanced key distribution scheme using ECDH for secure and lightweight key distribution and sub-MAC to overcome the vulnerability of ECDH. The simulation was performed ten times in each of the previous four procedures with Trust Center, Router, and Joiner.
First, we performed the key generation in standard security mode and high security mode, proposed key distribution in standard mode (Standard_ECDH), and proposed key distribution in high security mode (High_ECDH). Figure 4 shows the total run time measurements.
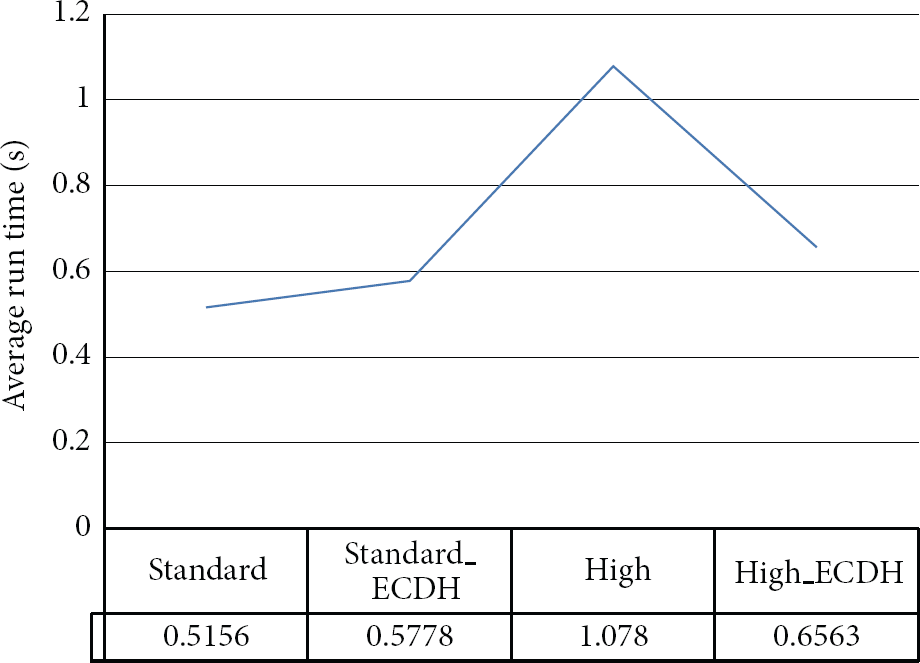
Simulation result-run time.
The average run time of the standard security mode is 0.5156 seconds, and for proposed key distribution in standard mode (Standard_ECDH) it is 0.5778 seconds; the difference is 0.0622 seconds. When this value is compared to the average run time of standard security mode, it adds 12%. However, the difference, 0.0622, is slight in terms of the figure and compared to the enhanced security.
The average run time of high security mode is 1.078; the average run time of proposed key distribution in high security mode (High_ECDH) is 0.6563; it decreases 0.4217. When this value is compared to the average run time of high security mode, it is decreased by 39%. It also provides enhanced security.
Next, we measured energy consumption in Joiner (Node 1), Router (Node 16), and Trust Center (Node 18). Figure 5 shows average energy consumption in transmit mode. Figure 6 shows average energy consumption in receive mode. The average energy consumption of each node for transmit mode and receive mode is similar.

Energy consumed in transmit mode.
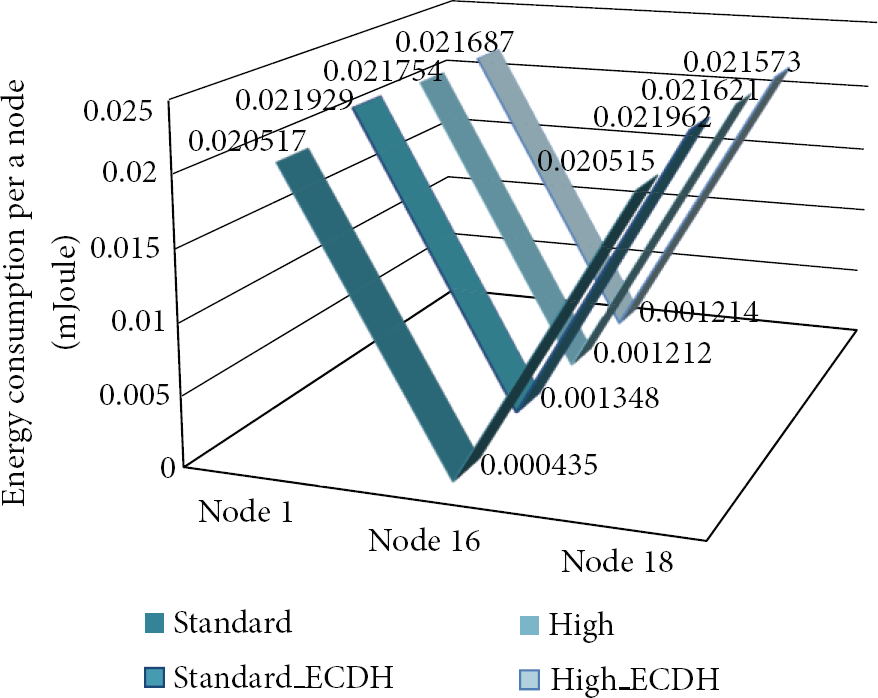
Energy consumed in receive mode.
Table 3 details the values. When the proposed key distribution in security mode is compared to the standard security mode, it consumes more energy. Especially, the receive mode of the Trust Center (N18-R) shows the maximum difference, 0.001447 mJoule. However, the Trust Center has sufficient capacity and energy, so this difference is negligible. The second difference is 0.001412 mJoule in the receive mode of the Joiner (N1-R). The sensor node uses two AA alkaloid batteries. An AA alkaloid battery contains a maximum of 3000 mAh, so the total energy is 6000 mAh. The formal voltage of an AA battery assumes 1.5 volts. The amount of eletric power is 9 Wh, products of 6 Ah and 1.5 V, and this is converted into 32,400 J, 3600 X 9 (J) [20]. The difference is slight compared to 32,400 J.
Energy consumption.

The energy consumption of the high security mode and proposed key distribution in high security mode (High_ECDH) is similar. The energy consumption of proposed key distribution in high security mode (High_ECDH) decreases, except for the transmit mode of the Joiner (N1-T) and the receive mode of the Router (N16-R). Moreover, the proposed scheme enhances security.
5. Security Analysis
In this section, we analyze our enhanced key distribution for ZigBee Pro that provides security properties and resists some general attacks. ZigBee Pro is vulnerable in the case of key distribution in two security modes. ECDH cannot prevent man-in-the-middle attack and does not provide authentication. However, our proposed scheme overcomes these vulnerabilities and enhances security. Our scheme could resist man-in-the-middle attack, replay attack, and ensure confidentiality of keys, message authentication, and message integrity [16].
We assume that an attacker does not know the sub-MAC method. Therefore, even if the attacker knows the Joiner's private key b, he/she cannot make the sub-MAC message. If the attacker tries to make the sub-MAC message, the probability of failure enhances because the attacker does not know how to create a sub-MAC message using Master Key. Additionally, there is a public key infrastructure (PKI) system. The Trust Center assures the private key b using the received public key
The security of a MAC scheme can be quantified in terms of the success probability achievable as a function of total number of queries to forge the MAC [21]. The security of a i-byte MAC is quantified as
5.1. BAN Analysis
BAN logic (the Logic of Authentication of Burrows, Abadi and Needham) [23] is widely used and studied in formal analysis due to its simplicity and efficiency. The BAN logic is a model logic based on belief and can be used in the analysis and design of a cryptographic protocol. The use of a formal language in the analysis and design process can exclude faults and improve the security of the protocol.
5.1.1. Basic Notations
The symbols A, B, P, and Q are principals involved in this sort of key agreement protocol: P◁X: P sees X. A principal has sent P a message containing X.
5.1.2. Inference Rules
Message Meaning Rules for shared keys:

If principal P believes that key K is shared only with principal Q and sees a message X encrypted under a key K, it believes only with principal Q. P may conclude that it was originally created by Q who once said its contents.
Jurisdiction Rule is as Follows

If P believes that Q believes X and also believes that Q has jurisdiction over X, then P should believe X too.
Nonce Verification Rule is as Follows
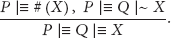
If P believes that X is fresh and that Q once said X, then P believes that Q has said X during the current run of protocol and hence that Q believes X at present. In order to apply this rule, X should not contain any encrypted text. The nonce verification rule is the only way of “promoting” once said assertion to actual belief.
5.2. BAN Analysis of the Proposed Key Distribution
Initialization Hypothesis is as Follows
Trust Center ∣≡ TC. Trust Center ∣≡ Joiner ∣≡J. Trust Center ∣≡ Joiner ⇒ Trust Center ∣≡ sub-MAC. Joiner ∣≡ J. Joiner ∣≡ Trust Center ∣≡ TC. Joiner ∣≡ Trust Center ⇒ Joiner ∣≡ sub-MAC.
Proposed Key Distribution Idealization
Trust Center → Joiner: J, Joiner → Trust Center: TC, Trust Center → Joiner:
Goal
Trust Center ∣≡ Trust Center Joiner ∣≡ Trust Center Trust Center ∣≡ Joiner ∣≡ Trust Center Joiner ∣≡ Trust Center ∣≡ Trust Center
Analysis. Through the proposed key distribution idealization (1), we can get
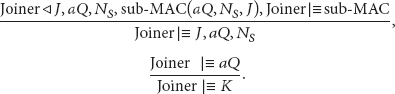
Through the proposed key distribution idealization (2), we can get

The Trust Center computes K and then sub-MAC(K) as follows:

And then, Trust Center ∣≡ Joiner ∣≡ Trust Center
Through the proposed key distribution idealization (3), we can get

And then, Joiner ∣≡ Trust Center ∣≡ Trust Center
According to the formalization analysis, we can get the conclusion that the proposed key distribution can resist man-in-the-middle-attack and replay attack.
6. Conclusion
This work proposed an enhanced key distribution scheme using ECDH and sub-MAC for efficiency and security. We have applied ECDH for secure key distribution and improved vulnerability of ECDH, using sub-MAC and nonce for message freshness and integrity.
We compared ZigBee Pro to the proposed scheme. We proved that our scheme could provide efficiency by achieving a shorter run time and lower energy consuming in high security mode. Security analysis proved our scheme could resist man-in-the-middle attack, replay attack, and provide confidentiality, message authentication, and integrity. Consequenly, the proposed scheme provides lightweight and secure key distribution compared to ZigBee Pro. We are going to experiment our proposed scheme with ZigBee devices in future work.
Footnotes
Acknowledgments
The work was supported by Ewha Global Top 5 Grant 2011 of Ewha Womans University and World Class University Program (R33-10085) through National Research Foundation of Korea funded by the Ministry of Education, Science and Technology. It was also in part supported by Basic Science Research Program through the National Research Foundation of Korea (NRF) funded by the Ministry of Education, Science and Technology (2011-0014020).
