Abstract
Intrusion detection is a challenging problem in wireless networks due to the broadcast nature of the wireless medium. Physical layer information is increasingly used to protect these vulnerable networks. Meanwhile, reconfigurable antennas are gradually finding their way into wireless devices due to their ability to improve data throughput. In this paper, the capabilities of reconfigurable antennas are used to devise an intrusion detection scheme that operates at the physical layer. The detection problem is posed as a GLRT problem that operates on the channels corresponding to the different modes of a reconfigurable antenna. The performance of the scheme is quantified through field measurements taken in an indoor environment at the 802.11 frequency band. Based on the measured data, we study the achievable performance and the effect of the different control parameters on the performance of the intrusion detection scheme. The effect of pattern correlation between the different modes on the scheme's performance is also analyzed, based on which general guidelines on how to design the different antenna modes are provided. The results show that the proposed scheme can add an additional layer of security that can significantly alleviate many vulnerabilities and threats in current fixed wireless networks.
1. Introduction
Attacks on wireless networks have become increasingly sophisticated with the increasing pervasiveness of these networks. It is challenging to detect and counteract intrusions in wireless networks due to the inherent broadcast nature of the medium. Among many known security risks, man-in-the-middle attacks and spoofing attacks [1] pose a significant intrusion threat to wireless networks since such attacks allow intruders to hijack a connection already established by a legitimate user. Though advanced wireless intrusion protection and detection systems have been developed and deployed to mitigate such threats, it has been repeatedly demonstrated that each method has its point of failure and no single method guarantees protection against all attacks [2, 3].
Such a hostile landscape requires multiple levels of defense for network protection. This requirement has gradually led to a more cross-layer approach to wireless security in recent times where security mechanisms are being deployed at different layers of the network. Particularly channel information available at the physical layer is being increasingly used to provide an additional degree of protection against intruders. Schemes that employ channel based security techniques can be categorized into encryption and authentication schemes. The former uses the wireless channel as a source for encryption key generation [4–9], while the latter utilizes a metric derived from the channel information as an identifier for authentication [10–16].
Intrusion detection has traditionally been categorized into misuse detection or anomaly detection techniques. While the former uses patterns characteristic of known attacks to detect known intrusions, the latter relies on detecting deviations from the established behavior patterns in the system [17]. In many usage scenarios, where the physical link remains unchanged over a session, the wireless channel response corresponding to the link can be considered to represent the established behavior pattern for that link. Any changes that violate this pattern abruptly beyond a certain limit can be then checked for adversarial behavior. In this paper, we follow this approach where the channel is monitored for any abrupt changes in its statistics through repeated applications of the generalized likelihood ratio test (GLRT) [18]. The scheme is based on the idea that the statistics of the link corresponding to an intruder who is physically located at a different location will be different from that of the legitimate user and when the intruder tries to inject packets over the same connection, it will trigger an abrupt change in the GLR value.
Additionally we utilize a pattern reconfigurable antenna to improve the performance of the intrusion detection scheme. The ability of pattern reconfigurable antennas to enhance system throughput has been well demonstrated [19]. By picking antenna modes that are decorrelated in their radiation patterns, decorrelated channel realizations can be obtained to enhance system performance. Hence channels corresponding to different modes of the antenna can be expected to have different statistics, a property which is exploited to the benefit of the proposed detection scheme. However, the use of reconfigurable antennas (pattern diversity) should be differentiated from schemes that use multiple antennas (spatial diversity) with perfect decorrelation between the elements [11, 14, 16]. We relax any assumptions about channel correlation between the different diversity branches and specifically quantify the effect of correlation on detection performance. Moreover, a reconfigurable antenna provides a more practically viable solution to generate multiple channel realizations than spatially separated multiple antenna elements due to cost and space constraints.
In many public open networks (e.g., coffee shops) higher level authentication solutions are usually not implemented. Freely available software tools such as Firesheep can be used to simply execute session hijacking attacks when users visit insecure websites in such networks [20]. A wireless access point equipped with reconfigurable antennas that can implement the proposed method can be used to provide a layer of security that can significantly alleviate such security threats in these networks. In networks with higher level security mechanisms for encryption, authentication, and integrity, the proposed scheme can complement those mechanisms while they continue to play their part in securing the wireless link.
The rest of the paper is organized as follows. The intrusion detection problem and the threat model are described in Section 2. The detection scheme is described and the GLRT for intrusion detection is developed in Section 3. The channel measurement procedure is described in Section 4. We justify our assumption regarding the probability distribution of the channels in Section 5. The performance of the scheme is analyzed and the results are presented in Section 6. Some practical considerations are discussed in Section 7 before we conclude this paper in Section 8.
2. Problem Definition and Threat Model
The problem that is addressed in this paper is one of detecting an intruder who has gained access into the system by means of hijacking a connection already established by a legitimate user. The problem scenario consists of three players: the receiver

Illustration of the problem. (a)
To gain a practical perspective of the problem,
To achieve his goal,
It should be noted that
Additionally, we assume that only
As stated earlier, the proposed solution exploits the fact that
3. Description of Scheme
With the notable exception of mobile networks, many current and emerging wireless data networks are associated with stationary terminals at both ends of the link. Temporal variations in channels related to such networks arise mainly due to movements of people and objects in the vicinity of the terminals as well as small localized movement of the terminals within a very small area [21–23]. A typical example for such a scenario would be a user seated at a bench in a public place accessing the network from a laptop connected to an access point in the vicinity. This work addresses intrusion problems that pertain to such wireless network usage scenarios and does not address large-scale terminal mobility.
The amplitude of the estimated complex channel coefficient, corresponding to a single frequency carrier g, is denoted by h. The probability distribution of h follows a Ricean or Rayleigh distribution. We choose the latter distribution with parameter σ to describe h for reasons that will be discussed in Section 5:
Let
The use of multiple antenna modes will result in M different channel realizations at each time instant. The environment “seen” by the different modes of the antennas will be different due to the differences in their radiation patterns and therefore the distribution for each of these M channel realizations will be characterized by different σ's. Assuming that the channel realizations yielded by the different antenna modes are independent, we can now write
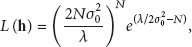
The control parameters that can be used to tune the performance of this scheme are listed in Table 1.
Control parameters.
A graphical depiction of these parameters are shown with respect to a sample evolution of

Sample evolution of the GLRT.
3.1. Steps of the Detection Scheme
During the outset of the session, Actual transmissions begin from Based on these computed In the event of an alarm, a higher layer reauthentication procedure can be evoked to reverify the identity of the transmitter.
3.2. Threshold Selection
The value of γ will be chosen based on the values observed for
The connection can be vulnerable to an attack during this threshold selection phase as well. Therefore, higher layer authentication protocols (e.g., 802.11i) should be evoked to verify false alarms during this adaptation process to ensure security until the target value of K is reached though this may cause some processing overhead due to frequent reauthentication. Optionally, depending on the level of threat to which the network is exposed to, this reauthentication process can be relaxed during this adaptive threshold determination phase for more efficient operation and all alarms may be treated as false alarms.
4. Channel Measurements
Channel measurements were performed on Drexel University campus using a four-port vector network analyzer. The measurement environment and node locations are shown in Figure 3. The environment is a large laboratory which is 20 m long, 8 m wide, and 4 m high with plaster walls. The room has several cubicles partitioned using metallic walls and laboratory equipment and furniture distributed throughout the room.

Layout of measurement environment. Test locations of
The measurements were performed with
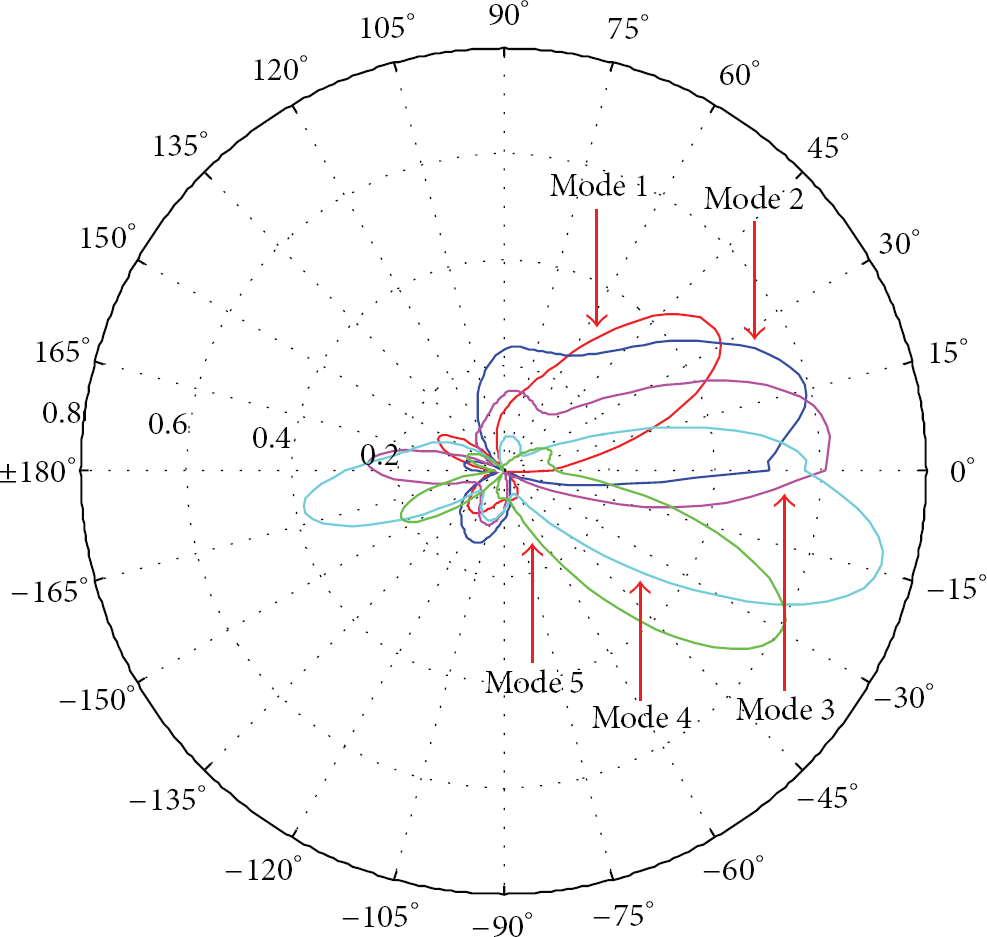
Radiation patterns corresponding to the 5 different antenna modes in the elevation plane. The elevation plane corresponds to the measurement environment plane shown in Figure 3. All patterns are vertically polarized.
5. Why Rayleigh Distribution?
It has been assumed that the channel amplitudes follow a Rayleigh distribution instead of the more general Ricean distribution for the purposes of this study. In order to justify this assumption, the empirical distribution functions obtained for each link from the measured data was compared to a Rayleigh or Ricean distribution whose parameters were estimated from the measurements. The similarity between the empirical distribution
The total support S is defined as



Difference between empirical and parametric distributions.
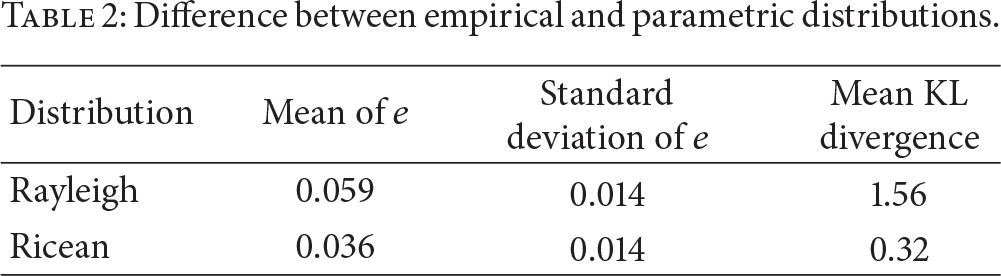
As can be observed, though the channel distributions are not “purely” Rayleigh nor Ricean, which is to be expected, they resemble these distributions sufficiently enough which provides us with the ability to develop an analytical framework for the problem. Moreover, as the values indicate, on average, due to the combination of line-of-sight (LOS) and nonline-of-sight (NLOS) links, modeling the channel as Rayleigh does not lead to a large error compared to modeling it as Ricean in the system, though the observed distributions marginally resemble the Ricean distribution more than the Rayleigh. Nevertheless, Rayleigh distribution was picked over Ricean for three reasons. Closed form MLE estimates do not exist for the parameters that characterize Ricean distributions and it requires recursive methods that are computationally intense [26]. The second reason is that when small values of N are used in the scheme, the recursive scheme does not achieve convergence resulting in very poor estimates that will have a significantly negative effect on the scheme's performance. Finally, a simpler form of GLRT function cannot be formulated due to the Bessel functions that characterize Ricean distributions which will lead to higher computational complexity. Based on these observations and reasons, the channel was modeled as Rayleigh distributed.
6. Analysis and Results
The performance of the intrusion detection scheme was studied in terms of the probability of missed detection For each ( For the The friendly samples were followed by samples from This process was repeated for 100 trials with different subsets of friendly and adversary samples and the average α and β were computed. The overall α and β were computed as the average obtained over all possible (
Unless specifically otherwise stated, the presented results also reflect the average over the different antenna combinations possible for a given M; that is, for a given α, the presented missed detection probabilities are averages obtained over the
6.1. Single Antenna Mode
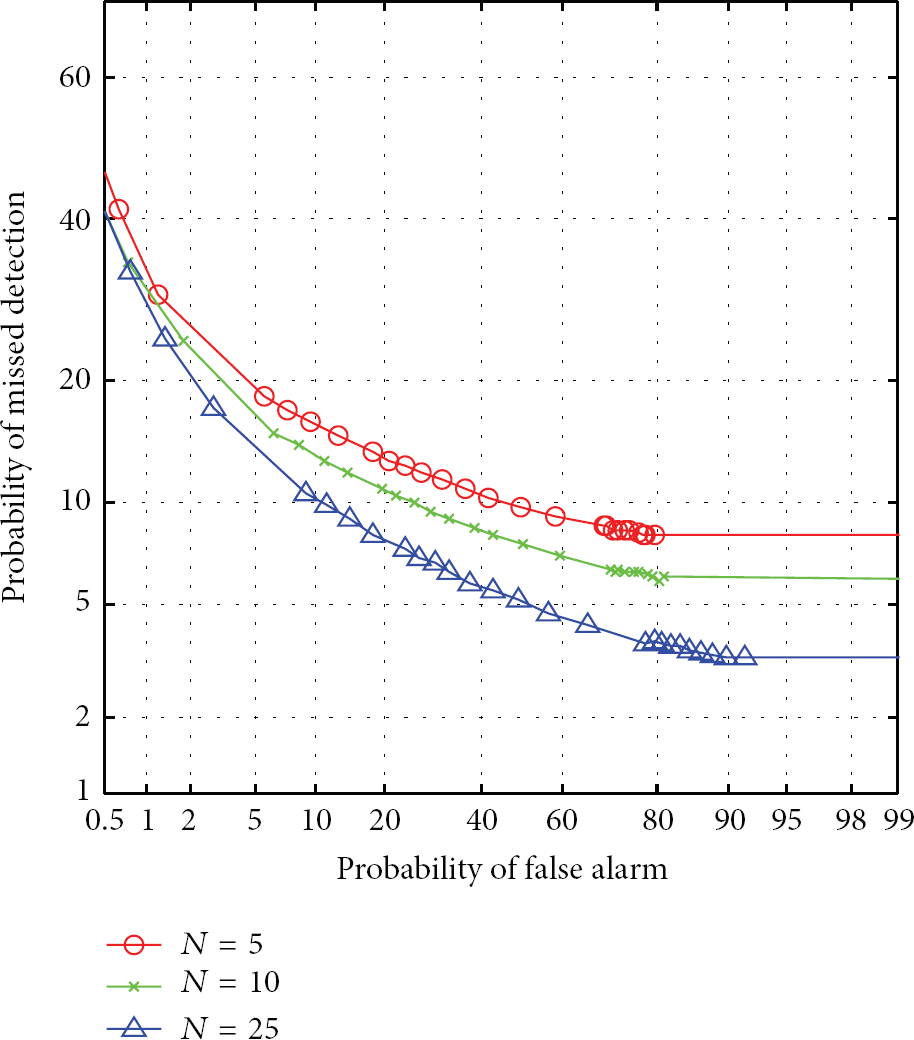
Figure 5 shows the average detection error tradeoff (DET) curves for a single antenna mode for different values of block size N. The nonlinear scaling of the axes in a DET curve is designed to yield a straight line when
Average DET curves for a single antenna
It can be observed that the performance improves with block size. This is due to two reasons. A larger block size gives a better estimate for
Moreover, the values of N used in the computation of
However, with just a single antenna mode, the achievable detection rates are unacceptably low at low α regions. In cases where 
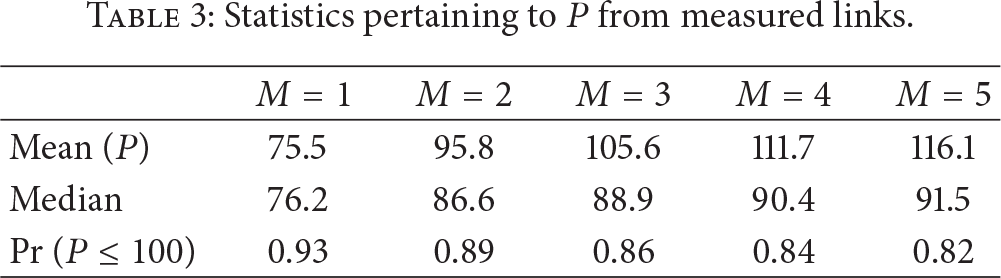
Statistics pertaining to P from measured links.

CDF of P for different values of M. The support and mean shifts toward higher values with increasing M.
Figure 7 shows the variation of probability of detection as a function of detection delay in terms of number of packets. Understandably, detection rate improves with the allowable detection delay. However, it should be noted that timely detection of the intruder is very critical and therefore
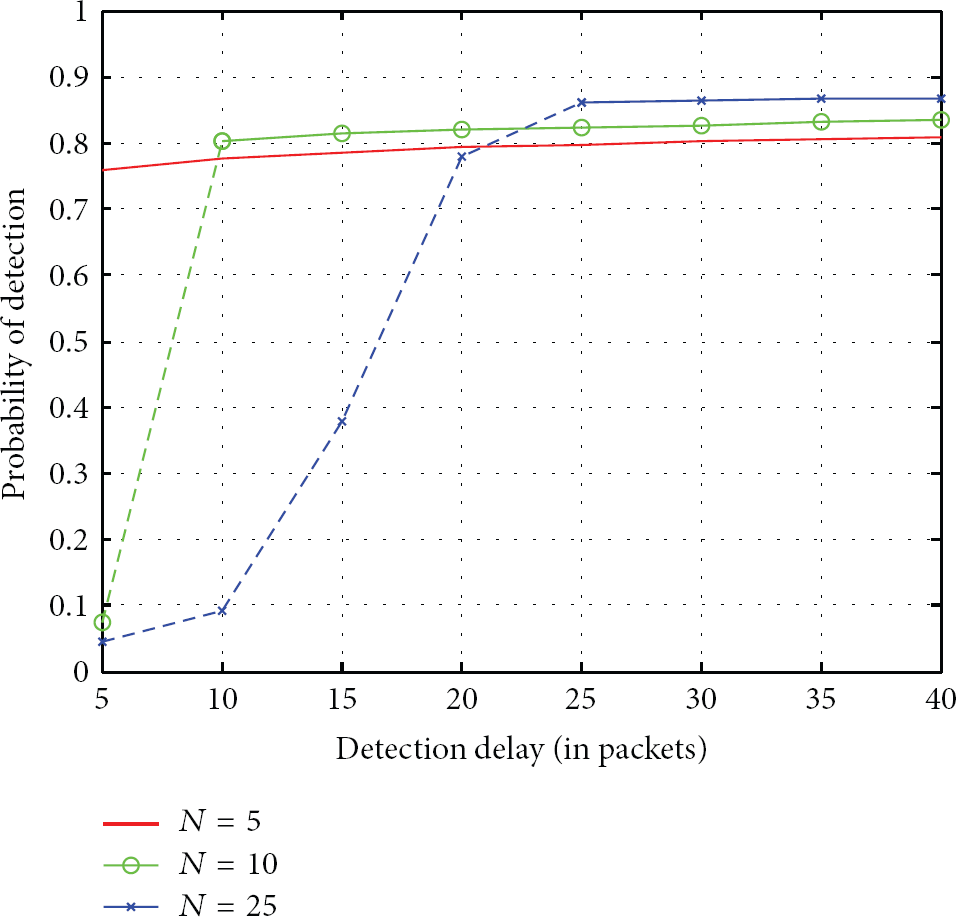
Variation of detection probability with
The false alarm rate, as a function of the number of friendly transmissions from

Variation of α with
To summarize the preceding trends, higher N lowers α while improving detection rates. Though a longer detection delay can help detection rates, in practice it is undesirable to have such long delays. However, due to the marginal difference between the σ values for the
6.2. Multiple Antenna Modes
We begin our analysis of the multiple antenna mode case with Figure 9 which shows the DET curves achievable through the combination of channel information corresponding to multiple antenna modes. For each incoming packet,
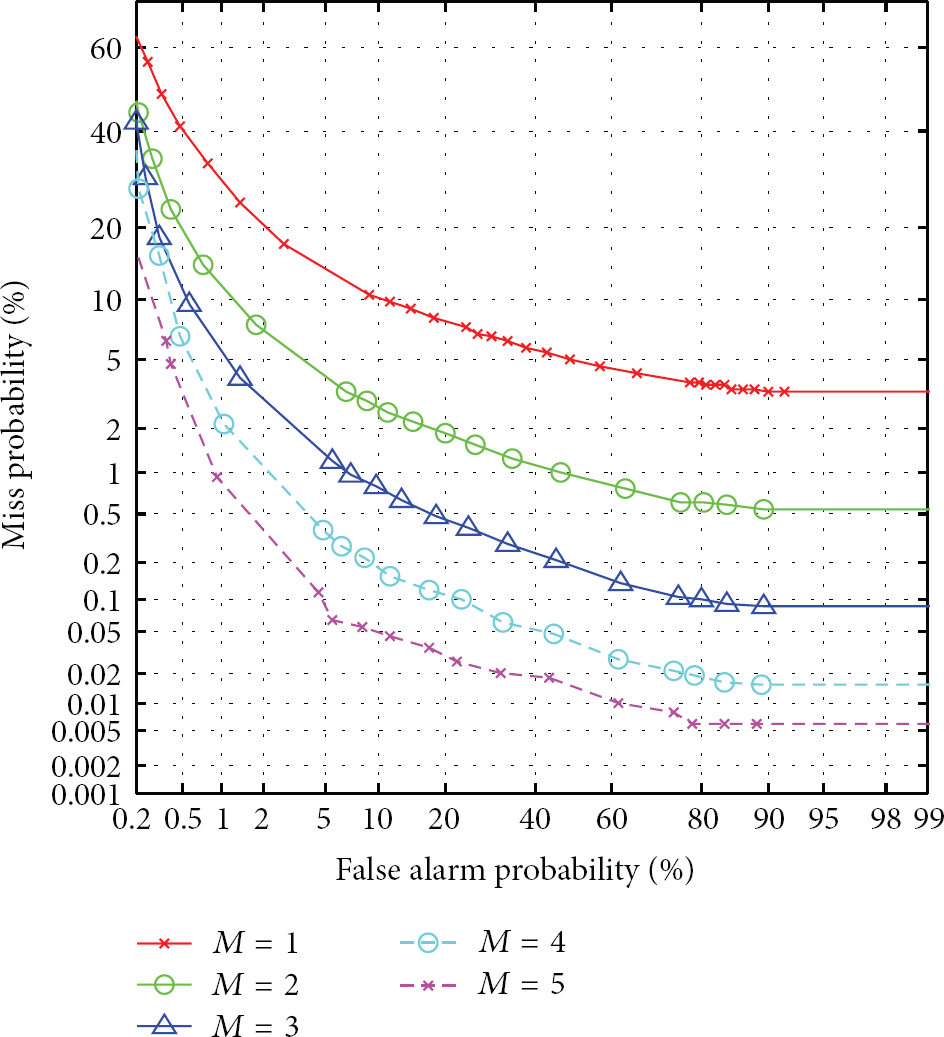
Average DET curves for a multiple antenna modes for
Figure 10 shows the achievable detection rates as function of detection delay for the different M values. Comparing this with Figure 7, it can be seen that the level of improvement achievable in detection rates is quite high with M than N. For example, increasing N from 10 to 25 results in a mere 5% improvement in detection when a single mode is used. Moreover, this improvement comes at the cost of a longer detection delay. By introducing an additional mode, β can be lowered from around 20% to 9% while keeping N and

Variation of detection probability with
Figure 11 shows α as a function of the number of friendly packets. As described in step (2) in Section 6, α is defined as the probability that there will be at least one packet that exceeds the threshold γ during the friendly transmissions. Improvements in α is also observed with increasing M. Naturally false alarms increase with increasing friendly packets regardless of M. For relatively smaller values of N and a single antenna mode, when certain samples in

Variation of α with
We conclude this section by providing a list of key statistical measures for α and β that were observed for various values of K in 100 trials. These measures are shown in Table 4. It can be observed that the standard deviation is limited to 1.5% for false alarm rates and to less than 1% for missed detection rates. The data shows that, for a given set of parameters, false alarm rates and missed detection rates are stable across multiple trials.
Key statistical measures for α and β observed during 100 trials (

6.3. Which Modes to Choose?
From the previous results it is clear that introducing multiple antenna modes improves the system's overall performance. However, these results do not provide insights into how to pick the mode combinations and most importantly if there is any benefit in increasing the number of modes beyond a certain level. Some insights into this problem can be found by analyzing Figure 12 and Table 5. Table 5 lists the spatial pattern correlation that exists between the radiation patterns corresponding to the different antenna modes used in the study. The best, worst, and average detection rates achieved by different individual mode combinations for
Pattern correlation coefficients between different modes of the LWA.

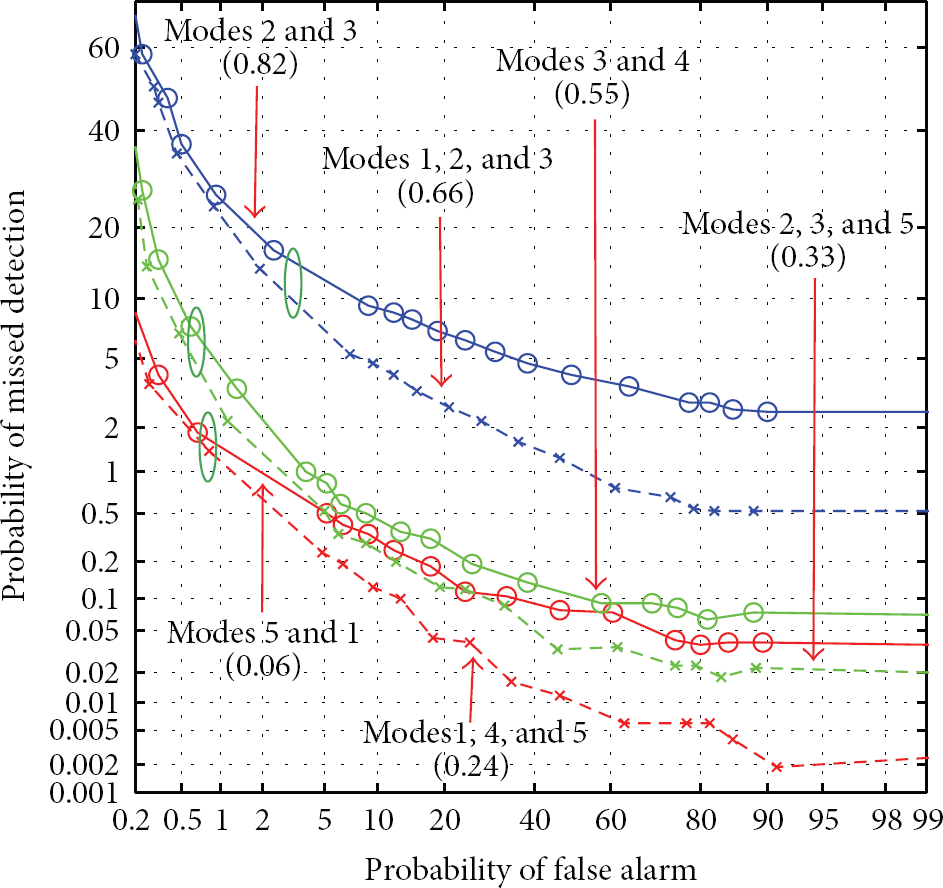
Average DET curves for different antenna mode combinations.
The preceding behavior can attributed to the well-known phenomenon of decorrelated antenna patterns resulting in decorrelated channel realizations [28]. The information provided by more decorrelated channel realizations serves to improve the “quality” of
Based on these trends, two guidelines are suggested for picking the different antenna modes. Antenna modes should be picked such that the pattern correlation coefficient between the different modes should be kept as low as possible. Many reconfigurable antenna architectures exist that can generate patterns with a very low correlation coefficient between their modes [19, 29]. The second is that adding new modes will improve detection rates as long as the newly introduced mode does not diminish the average correlation coefficient among the modes. This can be seen by observing the different circled pairs of DET curves in Figure 12, where adding a new mode improves detection when the addition of the mode lowers the average correlation coefficient among the modes.
6.4. Effect of Training
The quality of training will have a significant effect on the performance of the scheme as the estimated

Average DET curves for
7. Practical Considerations
Some key practical issues need to be considered in order to make this scheme work in practice. The most critical issue is the problem of obtaining channel estimates over all the antenna modes on a packet-by-packet basis. Figure 14 shows the possible candidate for a frame structure at the physical layer that can be used to achieve this operation. An extended payload is interspersed with the necessary training symbols for each mode along with padded intervals to allow for switching the antenna to a new mode and resynchronization. High-speed switches with switching speeds in the order of picoseconds currently exist that can allow the antenna to switch modes at a rate compatible with current high data rate applications.

Extended transmit frame that can be used to obtain channel estimates for multiple antenna modes using a single packet transmission.
As noted previously, this scheme is proposed to complement existing higher level security protocols. Therefore, such protocols should continue to play their role in protecting the wireless link. An adaptive approach can be pursued when the GLRT triggers an alarm at the physical layer. When an alarm is raised by the physical layer scheme, the system can reconfigure the GLRT to operate in a point on the DET curve that prioritizes low missed detection over false alarms. Subsequent alarms should be handled by the upper layer authentication protocols such as 802.11i till it is ensured that the perceived threat does not exist after which point the GLRT can prioritize over false alarms again. Moreover, successfully adapting the alarm threshold will also rely on these reauthentication protocols.
Channel statistics may also gradually change with time which can lead to arbitrarily high false alarm rates. Periodic retraining can be implemented to keep the system performance within acceptable levels. Therefore, this scheme can benefit from more comprehensive training algorithms that continually update
8. Conclusion
An intrusion detection scheme that utilizes physical layer information based on a reconfigurable antenna was proposed. The intrusion detection problem was setup as a generalized likelihood ratio test under the assumption of Rayleigh fading channels for different antenna modes. The assumption was justified based on channel measurements gathered in an indoor environment using a network analyzer. The measurements were then used to study the performance of the scheme as a function of several control parameters available to the user. It was observed that large block sizes lower false alarm rates while yielding high detection rates as well. By utilizing multiple modes in a reconfigurable antenna concurrently in the likelihood function, it was shown that the detection rates can be improved and false alarm rates can be decreased while keeping the block size low. The pattern correlation coefficient that exists between the radiation patterns of the different antenna modes was shown to have a direct correlation with the resulting detection performance, with lower pattern correlation resulting in better performance. In networks with very limited or nonexistent security such as public WiFi spots, the proposed scheme can add a layer of security that can provide improved levels of protection against intrusion. In more secure networks operating in hostile environments, this scheme in conjunction with existing higher layer based security mechanisms can provide a much needed extra layer of security.
Future work to make the scheme more robust includes smart training algorithms that continuously train the system and keep the system up-to-date as well as algorithms that adaptively tweak the different control parameters to keep the system operating at the required performance level.
Footnotes
Acknowledgment
This material is based upon work supported by the National Science Foundation under Grant no. 1028608.