Abstract
Due to the potentials in promoting the driving safety and easing the traffic congestion, vehicular networks, especially vehicle-to-vehicle (V2V) communications, have recently been receiving much attention. The data dissemination protocol for V2V applications should not only provide end-to-end transmissions with low error probability and high throughput but also offer antieavesdropping capabilities. To achieve this goal, we in this paper propose a secrecy-enhanced relaying protocol for vehicular environments. Based on the network topology and the velocity of the moving vehicles, the proposed scheme first generates the relay candidate set, from which a single relay is then selected opportunistically to assist the source. By using the superposition coding strategy, the selected relay jointly sends the source message and the artificial interference to enable secure communications. We derive the tight closed-form expressions for the upper and lower bounds of the secrecy outage probability, based on which we analyze the diversity order of the system. The method to generate the interference signal is introduced, and the choice of superposition weight factor is also given. The analytical and simulation results show that the proposed relay-aided protocol yields a better performance than the competing alternatives in terms of both the secrecy performance and the implementation complexity.
1. Introduction
In the last few years, we have witnessed a large increase in the number of vehicles and critical traffic accidents as well. This calls for the development of Intelligent Transportation Systems (ITS), which integrates communications and information technology (CIT) into the transportation systems to provide a safer and more efficient driving experience. Vehicular network, as an embodiment of ITS, is a promising application-oriented network for enhancing the driving safety, improving the traffic management efficiency, and providing infotainment services [1]. Since the late 1980s, there has been an increasing research interest in the field of vehicular networks, from both the industry and the academia. Several standards have been established, including DSRC (dedicated short range communications), IEEE 802.11 p, IEEE 1609, and so forth. Meanwhile, university research efforts have also been made to characterize and model the wireless vehicular channels [2], develop medium access control (MAC) protocols [3, 4], design routing algorithms [5, 6], and carry out field trials in real-world environments [7].
There are basically two types of data dissemination modes in vehicular networks, namely, V2V (vehicle-to-vehicle) and V2I (vehicle-to-infrastructure). For the former, vehicles communicate with each other directly through a single-hop or a multihop connection, while for the latter, vehicles exchange the information with the fixed infrastructure (called the road-side unit or RSU) that is installed along the roadside. In practice, the data transfer for any source-destination pair can be performed in V2V, V2I, or the hybrid manner. However, in this paper, we only focus on the V2V communications.
Although many communication technologies have been devised so far for wireless networks, it is nontrivial to design a highly efficient data dissemination protocol for V2V communications. The main challenge comes from the unique feature of the vehicular networks. First, due to the fast movement of vehicles, the connectivity among the vehicle nodes may change frequently, and the resulting network topology is highly dynamic. Second, the propagation conditions for vehicular communications are more complicated compared to traditional wireless systems. The existence of the obstacles such as buildings, trees, and traffic lights will lead to poor channel quality. These two factors make the wireless communications for vehicular networks error-prone, which indicates the necessity for developing novel protocols to support the stringent QoS requirements in vehicular environments.
To achieve this goal, more and more efforts have been made to enhance the performance of the physical layer (PHY) of the vehicular networks. Among many candidates of physical layer techniques, cooperative relaying is widely recognized as a powerful tool, which can provide the spatial diversity and multiplexing gain by letting neighboring users cooperate with each other. Since the seminal works of [8, 9], a large body of literature has appeared dealing with the relaying protocol design for various systems, and many cooperative techniques have been proposed, including distributed space-time code (DSTC), relay selection, coded cooperation, collaborative beamforming, and so forth [10–14]. In vehicular communications, the destination node may be outside the transmission range of the source node; however, there are often many intermediate vehicles that can serve as relays. Therefore, the application of cooperative relaying in vehicular communications is an appealing solution to provide reliable end-to-end data delivery. In [4], a relay-aided distributed MAC protocol is proposed to optimize the system throughput and extend the service range of vehicular networks. The key idea is to adaptively select the relay node and the cooperative mode according to the channel quality and the relay positions. In [15], cooperative communication is exploited to improve the performance of routing algorithm, and a path selection criterion is developed to obtain a better tradeoff between the end-to-end reliability and the energy efficiency. The main drawback of the works [4, 15] is that they do not take into account the impact of some network parameters (such as the vehicle density, the road structure, etc.) on the protocol design. Aiming at this problem, [16] investigates the collective impact of the internode distance, the vehicle density, and the transmission range of the vehicles on the access and connectivity probability for vehicular relay networks. In [17], a cooperative data dissemination mechanism is introduced. The authors explore the symbol-level network coding to enhance the reception reliability and the content downloading rate.
Common to the aforementioned works is that they mainly focus on the use of cooperative relaying to enhance the transmission reliability, improve the end-to-end throughput, or extend the service coverage of vehicular networks. However, the openness of the wireless vehicular channels makes the transmitted data available to unauthorized users as well as the intended receiver. For example, Vehicle A wants to transmit a confidential message to Vehicle B via some trusted relays. Meanwhile, there is some malicious entity (called Vehicle E) within the transmission range that attempts to extract this information. Therefore, guaranteeing the secrecy of the data transmission process is also of vital importance. Existing approaches to securing communications rely heavily on the data encryption at the upper layers of the protocol stack. Taking vehicular networks as an example, IEEE 1609.2 specifies the formats for the secure messages and the corresponding encryption/decryption procedure. In contrast with this paradigm, the physical layer (PHY) security exploits the characteristics of the physical channel to guarantee secrecy. Since the pioneering work of [18, 19], more and more attentions have been paid to PHY security from an information-theoretic point of view [20–23]. Recently, the secrecy problem was considered under the framework of cooperative networks. Reference [24] studied the use of decode-and-forward (DF) and amplify-and-forward (AF) relays to enhance the PHY security, and [24–26] discussed the cooperative jamming (CJ) technique with sending artificial noise as its core. To reduce the implementation complexity without sacrificing the achievable secrecy performance, relay selection is introduced as an efficient mechanism to fulfill secure cooperation. In [27], an opportunistic selection technique was reported to minimize the secrecy outage probability. Following the idea of jamming, the authors of [28] proposed several schemes to select two relays to protect the legitimate receiver from being eavesdropped, significantly enhancing the performance. Reference [29] also adopts the relay selection and cooperative jamming to secure communications, but the jamming signal is sent from the destination rather than the selected relay.
Although the developed PHY-security methods in [28, 29] are effective in improving the secrecy performance of relay systems, none of them take the characteristic of the vehicular networks into consideration. Besides that, in these schemes, the channel state information (CSI) regarding the eavesdropping link is assumed to be available, which may not hold for vehicular applications. Unlike the existing works, a secrecy-enhanced data dissemination protocol is proposed in this paper for vehicular networks, using relay transmission and cooperative jamming techniques. The protocol works as follows: first, the relay candidate set is formed, based on the road structure, the vehicle locations, and the velocity of the moving vehicles. Then, a single vehicle is selected opportunistically from the set, which jointly transmits the source message and the intentional interference. By exploiting the CSI of the relaying link (not the eavesdropper link), we make the interference signal completely known at the destination but unknown at the eavesdropper. In this manner, the secrecy outage probability of the system is obviously decreased.
The rest of this paper is organized as follows. Section 2 introduces the system model and notations. In Section 3, the proposed relaying protocol is described. In Section 4, the secrecy outage probability of the proposed protocol is analyzed in details, and a simple power allocation scheme is also given. Simulation results are shown in Section 5, from which the superiority of our protocol can be observed. Finally, we conclude our work and point out some further directions in Section 6.
2. System Model
As is shown in Figure 1, we consider a segment of the road, which consists of M straight lanes with length of L meters each. The width for every lane is W meters. Within the considered
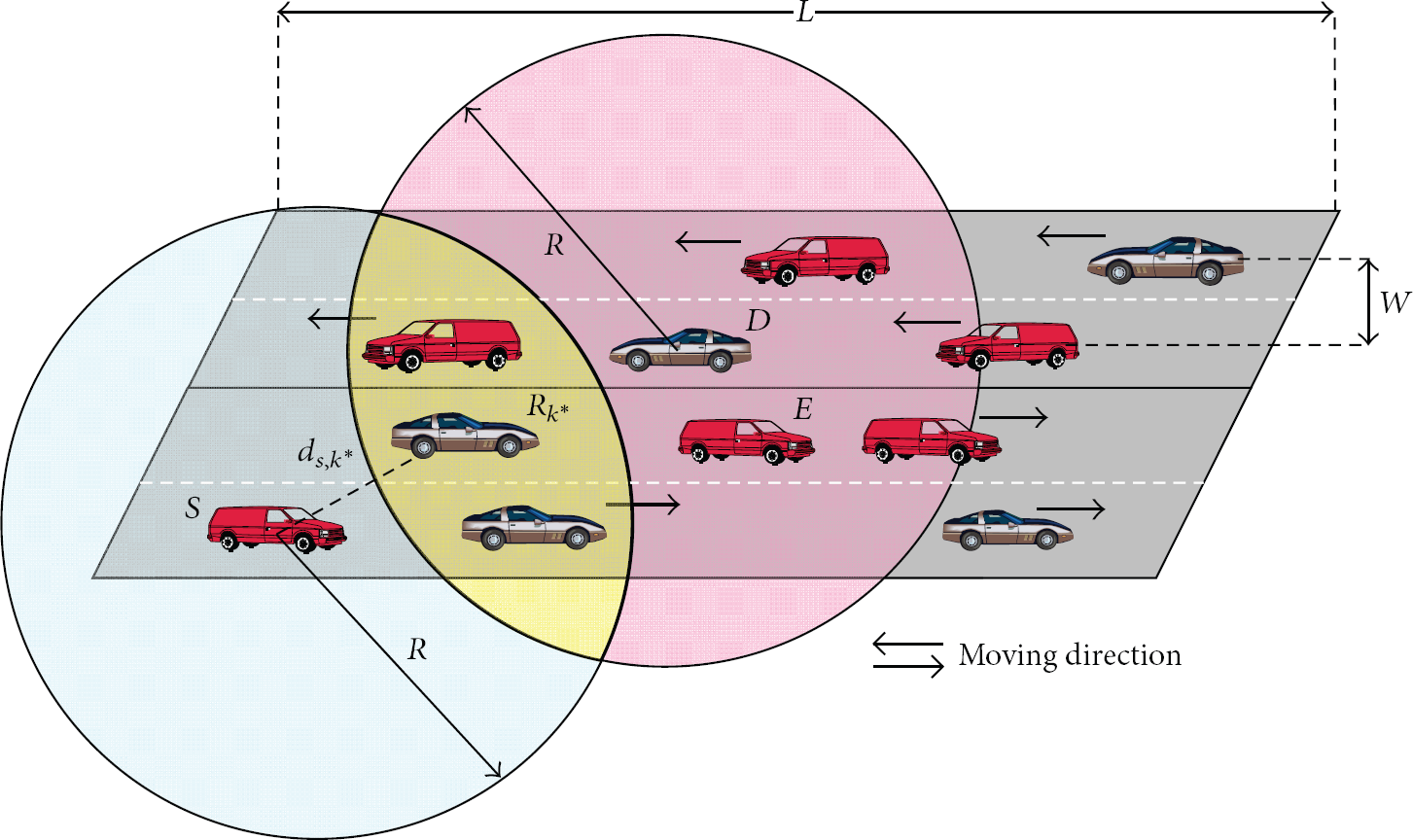
An example of the considered system with
We model the velocity of any vehicle
3. Secrecy-Enhanced Relaying Protocol
The proposed secrecy-enhanced relaying protocol includes four stages: the relay candidate set generation, the data broadcasting, the distributed relay selection, and the secure relaying. In what follows, the design details of these stages will be shown.
3.1. Relay Candidate Set Generation
As we have mentioned before, a TDMA-based scheduler is adopted to decide which source-destination pair can access the channel. Once a specified
If vehicle S and i are moving towards the same direction (see Figure 2(a)), the duration of

The geometry to calculate the links durations. (a) represents the case where S and i are moving towards the same direction, and (b) corresponds to the scenario where S and i are moving towards the opposite direction.
On the other hand, if vehicle S and i are moving towards the opposite direction (see Figure 2(b)), the duration of
Similarly, the duration of the link
Based on the above calculations, the duration of the two-hop link
3.2. Data Broadcasting
After the relay candidate set has been formed, the actual data transmission will start. As previously mentioned, the whole procedure is composed of several frame transmissions, with each consisting of the broadcast phase and the relaying phase. During the broadcast phase, S sends its message and all the relays belonging to the candidate set receive the message. The received signal at
3.3. Distributed Relay Selection
The proposed relay selection scheme aims at maximizing the secrecy rate, which is characterized by the difference in the data rate of the channel between S and D and that between the S and E. In respect of our system model, the secrecy rate is zero if
In the above derivations, a key assumption is that
Prior to any frame transmission, RTS (ready-to-send) and CTS (clear-to-send) packets are sent from S and D, respectively. On receiving the CTS, each relay
3.4. Secure Relaying
In the relaying phase, the selected relay transmits the superposition of the source message and the artificial noise. The legitimate receiver (D) and the eavesdropper (E) try to extract the source information
4. Performance Analysis
4.1. Secrecy Outage Probability
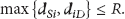
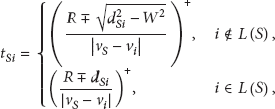
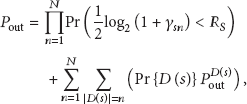
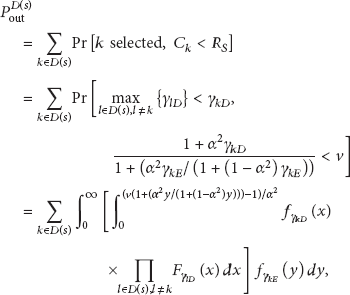
The secrecy outage probability (SOP), which is widely adopted to evaluate the performance of secrecy protocols in fading channels, is defined as the probability that the instantaneous secrecy rate falls below a target secrecy rate
It is extremely difficult, if not impossible, to obtain the exact result of (12). Therefore, we resort to some approximate methodologies to derive its bounds. It can be easily observed that
Applying (13) to (12) and making use of [32, equation (33)], the lower and upper bounds of
Substituting (11), (14), and (15) into (10), the closed-form expressions for the lower and upper bound of the SOP are obtained. However, we omit the results due to space limitation. In the next section, it will be verified through simulations that the derived two bounds are rather tight for all the SNR values.
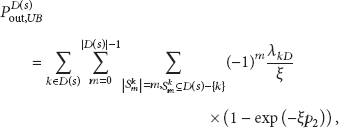
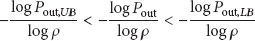
4.2. Diversity Order Analysis
In order to gain some useful insight into the system performance, we proceed to analyze the achievable diversity order, defined as
When
As
Employing the limit operation that
Following similar steps, it can be proven that
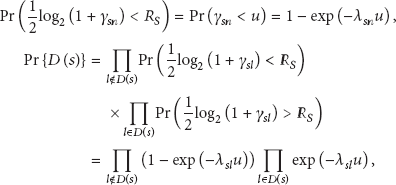
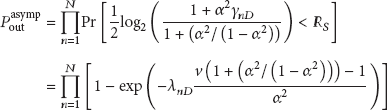
4.3. Choice of the Superposition Weight Factor
By choosing the weight factor optimally, a lower secrecy outage probability can be achieved. Nevertheless, it is not convenient to perform this optimization based on the derived bounds. Instead, we focus on the asymptotic behavior of the system and try to find a suboptimal one.
For sufficiently large SNR, it is reasonable to assume that all the relays are capable of successful decoding [27, 28]. Furthermore, the approximation in (8) holds with a high probability. Motivated by these, we formulate the asymptotic expression of the secrecy outage probability as
5. Simulation Results and Discussions
This section presents the simulation results to validate the proposed protocol. In Figures 3–6, we simply assume that a group of N relay candidates already exists, and only focus on the performance of the relay selection criterion and the secure relaying scheme. The impact of the network topology and the mobility of the vehicles on the relay candidate generation will be investigated in Figures 7-8. In the following simulations, the direct links of

The simulated secrecy outage probability and the theoretical bounds.

Simulation results of the secrecy outage probability for CS, OS, OSCJ, DACJ, and the proposed scheme.

Simulation results of the secrecy outage probability for different values of
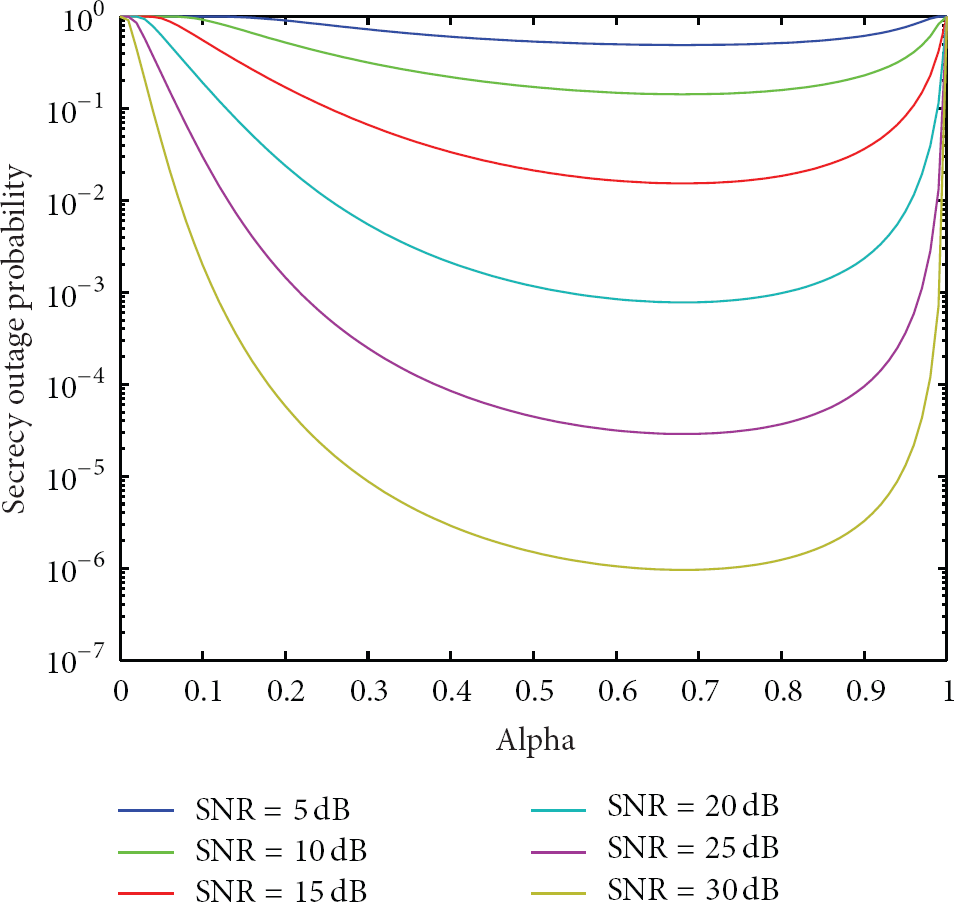
The secrecy outage probability versus the superposition weight factor for various SNR values.

The relationship between the number of vehicles and the number of available relays.
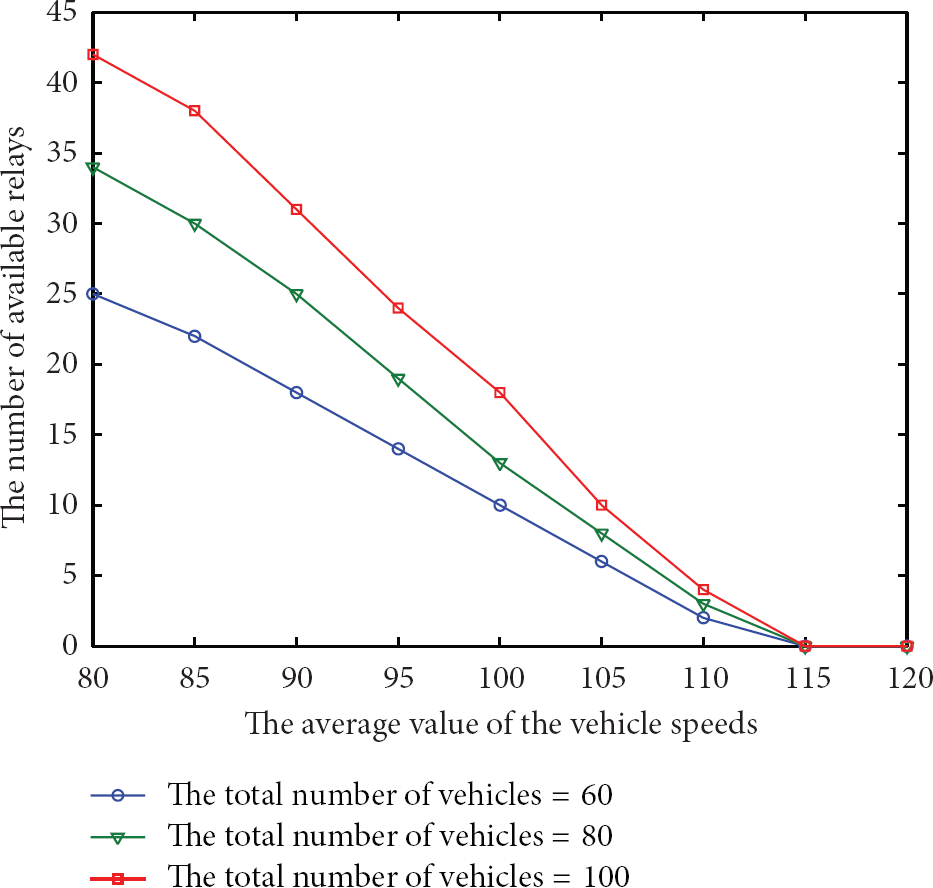
The relationship between the number of available relays and the average vehicle speed.
In Figures 3–6, the source node, the destination node, and the eavesdropper are located at (0, 0), (1, 0), and (1, 1), respectively. N relay nodes are uniformly distributed in the first quadrant of the
The correctness of the theoretical analysis for the secrecy outage probability is verified in Figure 3, from which it can be seen that the derived bounds are accurate for all the SNR values, and the tightness does not change significantly when the number of relays varies. In particular, there is an excellent match between the upper bound and the simulated result. Additionally, the slopes of the curves illustrate that the diversity order of N, that is, full diversity, is achieved by our protocol.
Figure 4 compares the secrecy outage probability of the proposed scheme to that of some representative counterparts, including the conventional opportunistic selection (CS) [11], the optimal selection without jamming (OS) [27], the optimal selection with controlled jamming (OSCJ) [28], and the destination-assisted cooperative jamming (DACJ) [29]. It should be pointed out that the considered system model in [29] is not the same as ours; therefore, some revisions to the DACJ scheme are performed to make it applicable to our system. Specifically, since the direct links of
It is evident from Figure 4 that both CS and OS exhibit a significant error floor, which is due to high eavesdropper SNR as the total power increases. By introducing the controlled artificial noise, OSCJ can obtain a remarkable performance gain compared to CS and OS, indicating the effectiveness of jamming technique in supporting secrecy. In contrast with these alternatives, our scheme brings a nonnegligible enhancement in medium to high SNR regimes. For example, at the secrecy outage probability of
Figure 5 plots the curve of the system secrecy outage probability and exhibits how it varies with the target secrecy rate
In Figure 6, we examine the effect of the weight factor (α) on the system performance. For a set of SNR values, the curves of the secrecy outage probability are plotted as a function of α. An important observation from Figure 6 is that the system performance is not very sensitive to
Finally, Figures 7-8 study the effect of the network topology and the mobility of the vehicles on the relay candidate set generation. In these simulations, the length of the road (L) is set to be 400 m. The number of lanes is 4 and the width of each lane (W) is 4 m. As described in Section 2, the velocity of all vehicles follows a truncated Gaussian distribution over the interval (60 kmph, 180 kmph), with standard variance 5 kmph. The source and the destination are located at
Figure 7 shows the relationship between the number of vehicles and the number of available relays, with R taking three different values. The mean value of the vehicle speeds is 100 kmph. From this figure we can see that the highly dynamic characteristic of the vehicular networks and the limited transmission power of the vehicles contribute to the phenomenon that the number of available relays is much less than the total number of existing vehicles. Therefore, it is necessary to take both the large-scale effect and the small-scale fading into consideration when we design the data dissemination protocol.
In Figure 8, we fix the transmission range of the vehicles to be 300 m and present the number of available relays as a function of the average vehicle speed. As expected, the number of potential relays decreases as the vehicle velocity increases. This is because the fast movement of the nodes will yield a rapid change in the network topology. As a result, the durations of the links will become shorter.
6. Concluding Remarks and Future Works
In this paper, a relay-aided data dissemination protocol is presented for vehicular networks with secrecy constraints. Based on the idea of jamming, we propose to use the superposition coding and the opportunistic relaying techniques to achieve secure communications. The relay selection policy is given, and the details involved in the design of the protocol are also discussed. We evaluate the system performance via both theoretical analysis and numerical simulations.
Developing relay transmission approaches for vehicular networks under the PHY-security framework is a brand new research topic, and there are a lot of issues worthy of investigation. First, in this paper, we only focus on the information-theoretic analysis, yet how to make the proposed idea work in realistic systems is still open. For example, the protocol design based on imperfect channel estimation and (or) practical coding/modulation strategies is needed. Second, it would be of interest to generalize the proposed method to more complicated network environments, such as the scenarios where there are multiple eavesdroppers and (or) the broadcast phase is not secure. Moreover, the combination of our scheme with other techniques, for example, MIMO and adaptive transmission, may also be valuable directions for further study.
Footnotes
Acknowledgments
This work was supported in part by the National Natural Science Foundation of China (no. 61201207), the National Science and Technology Major Project of China (no. 2013ZX03003001-002), the Open Research Fund of State Key Laboratory of Integrated Services Networks, Xidian University (no. ISN12-12), the Research Fund for the Specialized Doctoral Program of Higher Education of China (no. 20120201110066), and the Fundamental Research Funds for the Central Universities of China.