Abstract
Smart grid is a network of computers and power infrastructures that monitor and control energy usage by collecting data from the power grid. It can gather and distribute information about the behavior of all consumers in order to improve the efficiency, reliability, economics, safety, and sustainability of electricity services. In this paper, we propose a self-certified PKC-based privacy-preserving data aggregation scheme in smart grid to increase computation efficiency and achieve privacy protection of end users. To realize the anonymous aggregation of multidimensional data, we adopt the Chinese Remainder Theorem and homomorphic property of Paillier cryptosystem to achieve it. Comparing our scheme with Lu et al.'s scheme, the result shows that our scheme has more advantages over Lu et al.'s scheme in terms of computational costs of the user, GW, and OA. After adopting batch verification technique, the computational cost of GW is constant in our scheme, however, that of GW is linear with the number of the users in Lu et al.'s scheme. Furthermore, our scheme also supports the anonymity of the user's identity. It indicates that the local gateway GW does not know the real identity of the resident user such that the privacy of the user is better protected.
1. Introduction
Power electric systems in most countries have became old and inefficient. It might result in potential safety hazards. The Northeast blackout of 2003 was worth to be pondered. In this accident, about 200,000 people were affected, and 265 power plants were shut down during the outage. Investigations report found that the reason of blackout was due to human error and equipment failures. And this report indicated that this blackout could have been prevented and that immediate actions must be taken in both the United States and Canada to ensure that our electric system was more reliable. It puts forth a challenge for us. When a problem appears, how should we find it and solve it in time?
To overcome the problems caused by aging power grids, smart grid is developed. The earlier emerging smart grid technologies are electronic control, metering, and monitoring. The term smart grid has been used since at least 2005, when it appeared in [1]. There are many smart grid definitions in the recent literature in different flavors. However, a common factor in these definitions is the application of digital processing and communications to the power grid, making data flow and information management central to the smart grid.
The objective of smart grid is to provide end users or consumers with power in a more flexible, stable, and reliable manner. It makes end users know real-time electricity usage so as to actively adjust use of electricity. Therefore, the smart grid is characterized by a two-way flow of electricity and information between the provider and consumer of electric power. It achieves an automated, distributed energy delivery network and helps end users to balance power supply and demand by distributed computing and communications to deliver real-time information. Meanwhile, it also can detect and respond to weaknesses or failures in the power system in real time such that potential dangers are prevented.
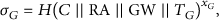
Communication framework in smart grid is shown in Figure 1, where power transmission and distribution systems are separated from the communication system. In the communication system in smart grid, smart meter is an important component in smart grid it can record consumption of electric energy in a time interval and communicate the information back to the utility for monitoring and billing purposes. However, current smart metering technologies which are applied in smart meters may result in privacy leak issues because they depend upon centralizing personal consumption information of the consumers at their smart meters. In 2009, The Netherlands enacted relevant laws to force to consider privacy issues in case of using smart meters [2]. Similarly, in the United States, NIST dictated that there privacy issues be taken into account in the design of smart grid communications [3]. These privacy concerns may be addressed by adequately authenticating the smart meters. However, smart meter is a rather limited resources device with low memory and computational capacity. Thus, we cannot put too much burden on the constrained smart metering resources in the time of designing an authentication mechanism for smart grid communication.
The conceptual architecture of smart grid.
Because communication in smart grid is based on the public data communication networks such as Internet. there exist a wide variety of malicious attacks, such as replay, eavesdropper, tamper of data, traffic analysis, tracing of the locations, and denial of service (DOS) attacks. Thus, before putting the application of smart grid into practice, the corresponding security and privacy issues must be resolved. For example, without the security and privacy guarantees, an adversary in smart grid can forge a fraudulent electricity usage data or breakdown information to mislead operation center. In terms of end users, privacy is a most concerned problem. It includes privacy of identity and privacy of data. Power-consuming data may reveal family income and physical activities. For example, power consumption of a household in a certain time is very low or zero; it implies that no one is at home. The user's identity is sensitive information. If it is leaked, it may result in potential unsafe factor. Then home address and the number of apartments of the user are known. Thus, this privacy-sensitive information must be anonymous.
To achieve data privacy, encryption algorithm is used to ensure the safety of data. However, it may result in data expansion. How do we resist data expansion in the case of keeping data privacy? It brings a challenge to the smart meter with constraint resource. To solve this issue, we adopt homomorphic encryption technique [4] since it can achieve data aggregation under the condition that the data is encrypted. In other words, data can be aggregated in the ciphertext form. In 2005, Castelluccia et al. [5] adopted homomorphic encryption techniques to realize the aggregation of encrypted data without decryption at intermediate nodes. Subsequently, Westhoff et al. showed that the scheme [6] may result in an increased message overhead in per monitoring node since the ID list of the encrypting nodes must be transmitted when every node used different keys. Thus, a symmetric homomorphic encryption technique was applied to increase the efficiency in [6]. In [7], Shi et al. was based on Castelluccia's scheme to put forth a privacy-preserving data aggregation scheme to preserve user privacy. Most of the previous works mainly focus on one-dimensional data. Recently, Lu et al. proposed a multidimensional data aggregation approach based on the homomorphic Paillier cryptosystem by using superincreasing sequence [8]. However, the computation overhead of local gateway is rather high. And the identity of end user is revealed in the communication between user and local gateway. According to [9], the memory size of the local GW is up to 128 KB random access memory (RAM), 1 MB flash memory, and 160 MHz CPU. Thus, the computational cost of the local gateway should be low as soon as possible.
Since the communication between the end user and the local gateway (GW) usually adopts wireless technology, it makes the end user suffer from the different attacks due to the open wireless network. Privacy protection of the end user's identity is particularly important. To guarantee end user's privacy, two important approaches are pseudonym mechanisms and group signature technique. The pseudonymity-based approach needs to periodically change a pseudonym. The group signature-based approach results in longer length of a signature than that of original signature, and computation cost of verifying a signature is very large. These approaches are suitable for smart metering with limited resource.
Self-certified public key cryptosystem was introduced by Marc [10]. In the self-certified public key system, verification and management of certificates are not required, and the key escrow problem can also be eliminated. The main idea is that certificate of public key is replaced by a witness, and the public key is implicitly embedded in it. Anyone who holds a witness along with an attributive identity can recover the corresponding public key to verify a signature. Thus, it leads to the reduction of communication, computation, and storage amount.
Our Contributions. To construct a scheme which is suitable for the device with low communication and computation resources in smart grid and achieve privacy protection of the end user's identity, in this paper, we propose a novel self-certified PKC privacy-preserving data aggregation (SP2DA) scheme. This scheme supports the aggregation of multidimensional power usage data by converting multidimensional data into a single-dimensional data. The main works of this paper are three-fold.
To support aggregation of multidimensional data, we adopt the Chinese Remainder Theorem to achieve the conversion of multidimensional data to single-dimensional data. To support privacy of identity, the scheme adopts self-certified public key cryptography to achieve it. It makes the scheme have the following advantages: short length of the signature and low computation. In the scheme, we realize that the computational cost of the local gateway is constant. It makes our scheme have more advantage over Lu et al.'s scheme [8] in terms of computational cost.
2. Communication System Model in Smart Grid
In the following, we give formal communication system model, security requirements, and our design goals.
2.1. Communication Model
The communication model, it mainly consists of operation center and local area network (LAN). Operation center is responsible for dynamically balancing power supply. In general, a trusted operation authority (OA) manages it at operation center. All residential users in a special residential area (RA) and the local gateway (GW) form an LAN. Smart appliances and smart meters form a home area network (HAN). The communication between the user and the local gateway is achieved by the communication between smart meters in an HAN and the local gateway. Smart meters transmit the collected real-time electricity usage data to the local gateway. After aggregating all electricity usage data, the local gateway reports the result to operation authority. On receiving the reports from the local gateway in the residential area RA, the OA analyzes the received reports and sends the corresponding to feedback information to the local gateway in the residential area. Then the local gateway broadcasts the feedback information to all users in the residential area. Finally, the users dynamically adjusts power consumption of smart appliance.
2.2. Security Requirements
Security protection is essential in smart grid communication. It is an important condition before deploying smart grid. In the security model, the main aim is to ensure integrity and validity of the transmitted data and the privacy of user's identity.
Here, we assume that the OA is trustable and the local gateway GW is semitrustable, and the users Authentication: it includes authentication of the user identity and message integrity. The user identity authentication means that the encrypted report is from a legal user. Message integrity authentication means that the transmitted data has not been altered. Any tempered data can be detected. Private: it also includes two points. The first point indicates that the data which is sent by the residential user is private since it is encrypted and the final data is aggregated. Only the operation authority OA can recover it. The other point indicates that the identity of the residential user is privacy for the local gateway. Any one cannot obtain the relevant information to the identity of the user from the transmitted data. Even the OA cannot also obtain any relevant information to the user from the aggregated data.
2.3. Design Goal
Based on the previous communication model and security requirements, our design goal is to construct an efficient data aggregation protocol to achieve the following three objectives.
Multidimensional data aggregation: in smart grid, the data which smart meters collect includes various types, such as the amount of the consumed power, and temperature and so on. The data in each dimension do not reflect the use of the global situation; thus, we must take into account all the dimensions in order to realize finer-grained control and optimization. At the same time, smart meters of hundred and thousand residential users periodically send the multidimensional data. To efficiently deal with the huge communication cost and multidimensional data, we need to construct an efficient aggregation scheme to support multidata aggregation. Global security. The smart meter-generated data should be authenticated to guarantee that they are from real sources and have not been tampered with during transmission. A tampered fraudulent data must be caught by the OA. Privacy of the residential user: if a residential user behaves honestly and follows the protocol, its identity privacy should be guaranteed against attackers who can eavesdrop communication in smart grid. It means that the identities of the residential users were not revealed during the transmission of the data. However the OA cannot also obtain the identity information of the residential users from the transmitted real-time reports.
3. Preliminaries
In the following, we first review the bilinear pairing technique [11] and the Paillier Cryptosystem [9] as well as some mathematics problems. They are the basis of the proposed SP2DA scheme. Then some security assumptions which are the basis of security proof are given.
3.1. Bilinear Map and Paillier Cryptosystem
In this subsection, we briefly review the properties of the bilinear pairings.
Let bilinear: if nondegenerate: there exists a computable: if
The modified Weil pairing and the Tate pairing are admissible maps of this kind. Please the interested readers refer to [12] for the details.
The Paillier Cryptosystem [9] is a classic homomorphic encryption. Its homomorphic property takes advantage of the homomorphic property of the exponentiation function and makes an encryption of message Key generation phase: let Encryption phase: let m be an encrypted message and Decryption phase: given a ciphertext
3.2. Security Assumption
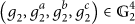
Decisional Bilinear Diffie-Hellman Problem (DBDH). The DBDH problem in
The Weak Computational Diffie-Hellman Problem (WCDH). Let
The k-wCDH problem is
The k-wCDH problem is a new hard problem. The hardness of the problem is based on the difficulty of solving Collusion Attack Algorithm with k traitors.
The
The
The hardness of
The Extended
The extended
4. Our Anonymous Self-Certified Signature Scheme
In this section, we will give a novel self-certified anonymous signature scheme which is the basis to achieve the anonymity of the residential user's identity in our SP2DA scheme.
4.1. System Setup
Let
4.2. KeyGen
For a user with identity ID, it first randomly selects
4.3. WitReg
When a user with identity ID wants to register, it computes a proof of zero-knowledge π of its private key
The TTP first checks whether
4.4. Anonymous Signing
To produce a signature on message m, the user with identity ID computes as follows.
First, it randomly chooses a number Then randomly choose Finally, the resultant anonymous signature on message m is
4.5. Verifying
After receiving a signature σ on message m, a verifier can execute the following process for each signature.
Firstly, the verifier parses σ into Then it checks
4.6. Security Analysis
In the following, we show that the previously mentioned anonymous self-certified signature scheme is secure against existential universal forgery under adaptive chosen message attack.
Lemma 1.
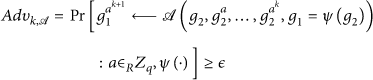
If there exists an adversary 𝒜 can forge the previous anonymous signature on a message m, then the
Proof.
Here, we will show that if an adversary 𝒜 could forge a valid message signature in our scheme, then there exists another adversary ℬ that can solve the
To answer the different queries from the adversary 𝒜, we need to run ℬ to set up the system parameters. Let
If If
Finally, ℬ returns
Corruption Oracle. When 𝒜 makes a corruption query with identity
WitReg Oracle. 𝒜 issues a witness register query on input
Anonymous signing oracle. When the adversary 𝒜 issues an anonymous signature query with ℬ firstly retrieves Then, ℬ randomly picks And ℬ randomly selects ℬ picks at random to compute ℬ checks whether string Finally, the resultant signature
Forgery. Eventually, 𝒜 outputs a forgery The corresponding The corresponding
According to the forking lemma [14], ℬ makes a replay with the same random tap but different choice of
Thus, we have
Lemma 2.
Our signature satisfies anonymity of signer's identity.
Proof.
Given a signature
5. Our Privacy-Preserving Data Aggregation Scheme
In the following, we will put forth a novel privacy-presrving aggregation scheme in smart by utilizing the proposed self-certified anonymous signature scheme. Three types of entities, That is, the trusted operation authority (OA), a local gateway (GW), and the residential users (U), are involved in the scheme. It mainly consists of the following six phases: system initialization, GW register, user register, user report generation phase, privacy-preserving report aggregation phase, secure report reading, and response phase.
5.1. System Initialization
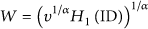
The trusted operation authority (OA) set up the system as follows. Let
In addition, OA initializes Paillier cryptosystem. Therefore, it chooses two large primes
Finally, OA publishes the system parameters
5.2. GW Registration
When a local gateway (GW) of the residential area wants to register itself in the system, it randomly chooses a number
5.3. User Registration
When a user The user Then it computes a zero-knowledge proof The OA verifies the validity of Upon receiving
5.4. User Report Generation
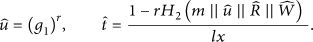
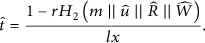
To periodically report electricity usage data of the residential user, each user Randomly choose Then, it randomly chooses And randomly choose The resultant anonymous signature on message m is Finally, the encrypted electricity usage data
5.5. Privacy-Preserving Report Verification and Aggregation of GW
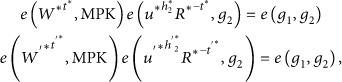
After receiving all electricity usage data Firstly, GW parses Then check
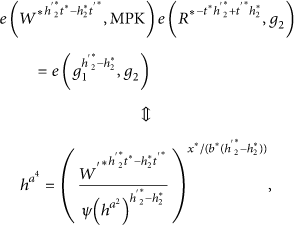
To increase efficiency of verifying signatures, the local gateway GW can make use of the following batch verification:
We can find that the computation overhead in the batch verification is approximate to that in the verification of a signature. It only needs three pairing operations which are the most time-consuming operators.
After all previously mentioned verifying is valid, the gateway GW performs the following aggregation process to aggregate all electricity usage reports.
It aggregates all encrypted data Then, it produces a BLS signature Finally, send the aggregated data
5.6. Secure Report Reading and Response
After receiving an aggregated σ on message C, the authority operation OA first checks whether the signature
Since
then the recovered message is
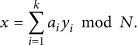
By the Chinese Remainder Theorem, we can obtain the electricity usage data as follows:
for
compute
All derived electricity usage data
It randomly chooses And it computes The resultant cipher is Then the OA produces a BLS signature Upon receiving the transmitted After receiving the broadcasted It computes
Then it recovers the message m as
With the recovered electricity usage feedback report m, the user
6. Security Analysis
In this section, we show that our scheme satisfies the previous security requirements.
Global security requirement: obviously, this security requirement is satisfied since each user's report is signed by our anonymous signature algorithm and the aggregated report is signed by BLS signature algorithm in our scheme. Furthermore, Lemma 1 shows that our anonymous signature is secure against adaptive chosen message attack, and the BLS short signature is provably secure under the CDH problem. Thus, we can efficiently identify the identity of the resident user, and it is impossible that exists a valid signature on a tempered data. Multidimensional data aggregation: in our SP2DA scheme, we adopt the Chinese Remainder Theorem and Paillier Cryptosystem. It can achieve multidimensional data aggregation in the ciphertext form. For a user's transmitted data Privacy of the residential user: Because the transmitted report of the residential user is signed by adopting our anonymous signing algorithm in our SP2DA scheme, each residential user's identity is protected. Furthermore, the transmitted report is encrypted by Paillier Encryption algorithm, it means even if the attacker 𝒜 eavesdrops the transmitted report, it still cannot obtain the individual user's data. For a feedback message m of the OA, OA sends the ciphertext
Lemma 3.
The broadcast encryption scheme in our SP2A scheme is semantic secure against chosen-plaintext attack under the DBDH problem.
Proof.
Suppose that there exists an adversary 𝒜 that can break the broadcast encryption in SP2DA scheme; then we can construct an algorithm ℬ that can solve the DBDH problem with advantage ϵ by using 𝒜 as a subroutine.
Let ℬ be given a DBDH problem instance
ℬ sets
In the challenge phase, the adversary 𝒜 chooses two messages
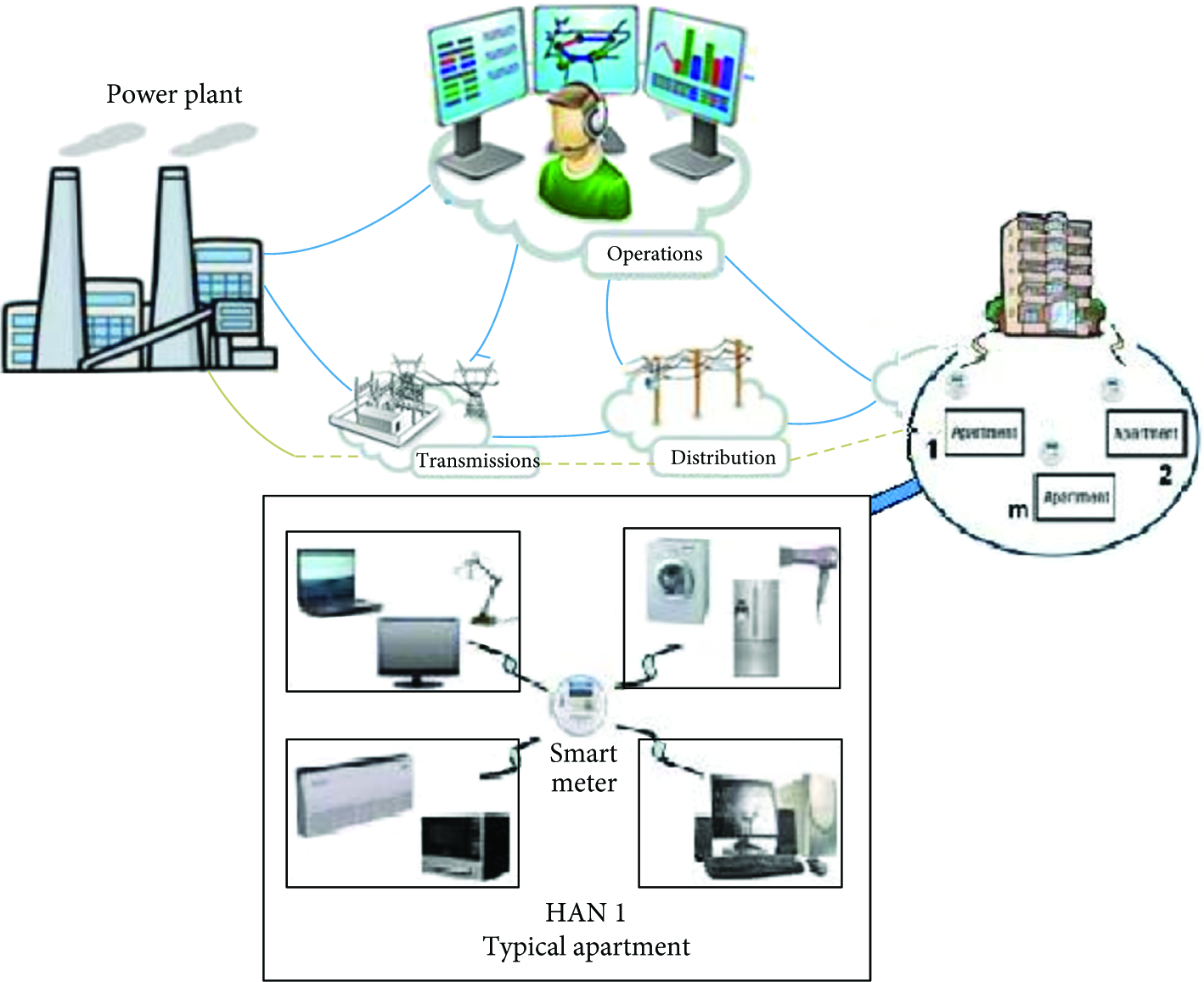
6.1. Efficiency Analysis
Until now, Lu et al.'s scheme [8] is only a privacy-preserving aggregation scheme (EPPA) in smart grid which supports multidimensional data aggregation. In the following table, we give a comparison of our scheme with Lu et al.'s scheme. Let
Comparison of Lu et al.'s scheme [8] with our scheme.
If experiments were performed on a Pentium IV personal computer with 3.0 GHz CPU, 512 MB RAM, and window XP operating system, and based on PBC cryptography libraries [12] and MIRACL libraries [15]. The experimental results show that to compute a single exponentiation operation in

Computational costs of users and GW.
6.2. Communication Overhead
According to the afarementioned communication construction, the whole communication is divided into user-to-GW communication, GW-to-OA communication, and OA-to-GW communication. In the user-to-GW communication, the reported data is the form of
7. Conclusion
In this paper, we have proposed an efficient self-certified PKC-based privacy-preserving data aggregation scheme to satisfy the requirement of efficiency in smart grid communication. By adopting the Chinese Remainder Theorem technique and homomorphic property of Paillier cryptosystem, it achieves a multidimensional data aggregation approach under the ciphertext form. And it applies our proposed anonymous signature scheme to achieve anonymity of the real identities of end users in end-user-to-GW communication. It efficiently resists the end user's identity leakage problem which is not considered in other literatures. Compared with Lu et al.'s multidimensional data aggregation scheme, our scheme can significantly reduce computational cost of the local gateway GW. And we have also provided security analysis to demonstrate that the proposed scheme can satisfy the desirable security requirements. It is a future work to trace the malicious behavior of a dishonest residential user (end user) in a residential area.
Footnotes
Acknowledgments
This work was supported partly by Beijing Natural Science Foundation (no. 4122024 and 4132056), the Importation and Development of High-Caliber Talents Project of Beijing Municipal Institutions, and the New Star Plan Project of Beijing Science and Technology (no. 2007B001).