Abstract
Key management in a large portion of ubiquitous sensor networks has been a challenge due to the limited capabilities of their wireless communicating and battery-powered sensors. Moreover, an attacker physically capturing even a few nodes hampers the entire network security by impersonating nodes to inject false data in an undetected manner. To efficiently protect from such impersonating by node capture, we propose a new dynamic key management framework particularly for large-scale clustered sensor networks. In the framework, different keying mechanisms, respectively, secure in-cluster, intercluster, and individual communication by refreshing keys on demand, while adaptively handling node addition and capture. Theoretic analysis and simulation results show that our proposed framework provides higher connectivity and security against impersonating than other existing studies do, for better trade-off with resource overheads.
1. Introduction
Wireless sensor networks (WSNs) of wireless communicating and battery-powered sensors have attracted attention from ubiquitous networking due to such sensors' cheapness and handy installation. In particular, for unmanned monitoring, these networks are often deployed in unattended and adversarial environments [1]. Here rises providing security against security attacks, which are more likely to incur in such WSNs due to the sensors' limited capabilities on communication, computation, and storage, as a key issue. Among varied security attacks introduced in [2], we particularly target impersonating by physical node capture because such an attack enables attackers to compromise all the secrets, such as cryptographic keys, of captured nodes and spread malicious data out over the entire network with impersonating the captured nodes by the obtained keys. Thus, as several studies [2–5] have already noted, any security strategies to be proposed should be highly resource-efficient as well as provide the basic security requirements: confidentiality, protection of the content of a packet; authentication, corroboration of the source of a packet; and integrity, ensuring that the content of a packet is unchanged during transmission.
To achieve all of them, a lot of security schemes have been proposed based on symmetric or asymmetric cryptography. Simply speaking, the difference between them is if the same key is employed both by a sender for encryption and by its receiver for decryption or not [4, 6]. Although asymmetric schemes generally provide stronger authentication [2, 4], symmetric key algorithms have been superior in WSNs for their light complexity [5, 7, 8]. For instance, one of typical sensors Tmote has 10 kb RAM, 48 kb flash memory, 1 mb storage, and 250 kbps communication bandwidth, which is insufficient to enable traditional asymmetric cryptography to work [9].
In the paper, we propose a new symmetric key-based security framework for efficiently secure communication in WSNs. To suggest an efficient data aggregation model for large-scale WSNs, we first assume that a WSN consists of a single very powerful base station (BS) and a number of clusters of regular sensors as in [10, 11]. Accordingly, as in Figure 1, our framework supports three different communication patterns invoked by the following three types of keys: a static individual key shared with BS; a one-time in-cluster key shared within a cluster; and a static intercluster key between two neighbouring nodes across different clusters. We demonstrate how different keying mechanisms for these keys work to cope with impersonating by node capture in the following organisation. Section 2 describes what assumptions we take first and introduces our proposed security framework in cluster-based WSNs of our interest. In Section 3, with designing the impersonating attack model, we provide theoretic analysis of our framework in several performance metrics. Section 4 compares the performances of ours with those of selected conventional key schemes. Finally, we conclude the paper in Section 5.

Three different communication patterns. Whereas the single-line arrows represent pairwise in-cluster communication, the double-line ones correspond to intercluster communication across two different clusters. The base station (BS) individually communicates with a node apart by starting with accessing to the closest node as the dotted-line arrow.
2. Our Proposed Security Framework
Our framework provides multiple keying mechanisms to support the three communication patterns, while giving confidentiality, authentication, and integrity. We first give several assumptions regarding WSNs of our interest; present the keying schemes to establish and manage each of individual, in-cluster, and intercluster keys with secure transmission employing the keys; and discuss how to handle node addition and eviction.
2.1. Network and Security Assumptions
In the paper, a WSN consists of a single BS and a number of static wireless sensors that are deployed as in [12]. Every time a helicopter stays in a different deployment point, it scatters a sensor subset, called a cluster. In such a cluster, every node knows all of its cluster members' IDs and directly or indirectly interacts with others in a hop-by-hop manner. One of them is safely announced as the cluster head, a local controller, to the other members. When a node newly joins one cluster after the initial deployment, the head is informed of its ID by BS and lets all the members know the ID as well before it is actually placed. Since any sensor does not know its immediate neighbours in advance, it attempts to find its neighbours and establish required keys shortly after its deployment. This keying phase is assumed to be fairly well protected. However, once a security attacker captures a node, it can obtain all of the node's cryptographic information. We also assume that the most feasible path from a source to its destination is selected and notified to all the on-path nodes by the clusterbased back-pressure routing algorithm of [13].
We illustrate our security framework using the next notations that appear in the rest of this discussion.
N is the number of nodes in a WSN. i and j are principals for clusters. u and v are principals for sensor nodes.
2.2. Individual Key
Since individual communication with BS contains highly private information, such as new node's joining announcement by BS or any neighbour's misbehaviour report by a node, which can be detected by any anomaly-based intrusion detection system discussed in [14], one's individual key is only shared with BS to authenticate the source of such notification. These keys are assigned by BS prior to deployment as follows.
Key Predistribution. To assign a unique individual key to each node, BS first builds a symmetric key matrix of
2.3. In-Cluster Key
We note that in-cluster communication most frequently occurs to exchange successive incoming percepts and to efficiently aggregate data. If a single cluster key is shared within a cluster for economical reasons, an adversary easily endangers the entire cluster by capturing only one node. Thus, we propose that a group of nodes sharing a key chain utilises all of the keys as each one's one-time encrypting keys in their own manners. One's current one-time key is derived only by its neighbours in its cluster, called in-neighbours, with its privately known base in advance and the current packet sequence number unless the base is compromised. This idea has, over the conventional key chain studies [1, 15, 16], the following additional advantages: strong key freshness, no need of key disclosure synchronisation, and no message overhead for direct key delivery.
Key Chain Predistribution. Before the initial deployment, BS generates and provides a unique one-way key chain of k keys for every cluster i based on OWF h and key

Different key-use orders of nodes u and v on their shared key chain
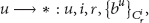
Neighbour Discovery and Base Exchange. After its deployment, every node u first attempts to find its any neighbour v by broadcasting its id, cluster ID i, and random key index r in
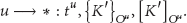
Rechaining and Key Chain Distribution. When member v reports its key reference exhaustion on the currently shared key chain to the head of cluster i or when any member v is perceived as captured, the head u generates key
2.4. Intercluster Key
For packets crossing clusters, every pair of border nodes in two adjacent clusters, called interneighbours, should share a distinct pairwise key. So far, every node has been loaded
Key Establishment. Every border node u of cluster i is given a series of pairs
2.5. Secure Transmission
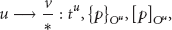
Now, we present how these established keys practically secure in-cluster, intercluster, and individual communication as in (5) to (7), respectively:
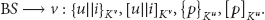
Within a cluster, node u sends another node v or broadcasts packet p by transmitting the p's encryption and MAC by its current Node u of cluster i always uses intercluster key When BS individually informs node u in cluster i of packet p, it transmits p to the first node v on a given path as in (7). Whereas the former two to address the destination are repeatedly decrypted and reencrypted by the on-path nodes including v through a deal of in- and intercluster communication until they reach u, the rest two are just carried during the transmission and only decrypted by u. The opposite case of u to BS reverses the course we have described.
2.6. Handling Node Addition
Before its deployment, new node u is preloaded its individual key
2.7. Handling Node Eviction
A node is regarded to be evicted when its battery seems to be exhausted; when a large portion of its communication links do not work; or when it is detected as captured. Any of its neighbouring nodes perceiving one of the conditions announces it to the entire network. As soon as its uselessness is notified, its cluster members and inter-neighbours discard every related secret from their memory. In particular, if the node is captured as in the last case, the rest of its cluster should update the shared key chain as in the rechaining and key chain distribution. Also, its in-neighbours individually reselect and broadcasts a new base different from the previous one to their in-neighbours as in (1).
3. Analysis of Our Framework
In this section, we, in turn, analyse our framework in the following performance metrics: network connectivity, resiliency against impersonating attacks by node capture, and resource requirements.
3.1. Connectivity
Because of its deterministic nature, our framework achieves perfect connectivity between any two neighbouring nodes for both in-cluster and intercluster communication at the initialisation phase. This also holds for newly added nodes due to the prior node ID announcement by BS as in Section 2.6.
3.2. Resiliency
Since we view that active attacks, such as false data injection, most degrade network performances, we make the following strong attack model by node capture.
The attacker can retrieve all the information stored in a sensor node once it captures the sensor node. The attacker can capture a set of sensor nodes selectively in a WSN. The attacker ultimately aims at impersonating legitimate nodes to inject false data with compromised keys.
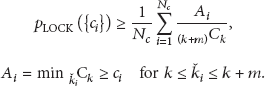
An attacker can purposely locate and capture sensors having more secrets as border nodes in our framework by selectively attacking such nodes. Such an attacker can impersonate only existing nodes whose ids are compromised because a new node with a falsified ID is thoroughly excluded due to the prior node ID announcement by BS. Thus, the resiliency against this attack is measured by estimating the fraction of total sensor nodes that properly impersonate id-known nodes by an attack, modeled as
The overall a completely impersonates every node u of to impersonate each of u's to impersonate each of the rest
The three terms of the numerator of (10), respectively, represent each case given above. For intercluster and individual communication, we can simply count and normalise as in (11) and (12) since one captured node reveals only its individual key and additionally intercluster keys if it is a border node. We simulate our resiliency levels for the different communication patterns with those of alternatives given different key chain lengths in Section 4.2.
3.3. Resource Requirements
Storage. Because the key size is usually larger than any other secret as a node ID or a base, we discuss only the number of retained keys for storage overhead. After the initialisation, every node obtains a single individual key, k, in-cluster keys of its key chain and additionally
Communication. The communication overhead for our security framework occurs between a neighbouring pair during initial keying, rekeying, and keying for a new node. At the initialisation, the pair exchanges only their ids and bases, whereas a seed key for a new key chain and new bases travel for re-keying. For a new node, the pair where one is the new node exchanges at most their ids, bases, a temporal or intercluster key, and the last key of the currently shared key chain as in Section 2.6.
Computation. In the initialisation, every node does
4. Comparison with Previous Studies
In this section, we compare the performances of our proposed framework with those of the following three selected conventional studies.
2KP (see [8]). BS has two key pools of
LOCK (see [19]). This utilises two layers of keys for clustered WSNs. BS communicates only with weakly trusted cluster key servers (KSes) with
LEAP+ (see [1]). Initially, every node u is preloaded the same set of e keys, termed
In the following simulations, we vary only the number of used or stored keys,
4.1. Connectivity
As already stated, the deterministic key establishing methods in ours and LEAP+ guarantee perfect connectivity regardless of the number of keys.
Since 2KP has stably high resiliency with 200 selected keys from 10000 keys [8], we take that
Regarding that
The comparison of direct pairwising connectivity amongst ours, 2KP, LOCK, and LEAP+ has given our setting is resulted as in Figure 3. As illustrated, our framework, LEAP+ and LOCK for

Comparison of direct pairwising connectivity amongst ours, 2KP, LOCK, and LEAP+.
4.2. Resiliency
If c nodes are captured in total, no nodes other than the captured nodes can be impersonated in 2KP and LEAP+. Since they do not keep the keys based on which neighbouring pairs establish their pairwise keys using a PRF, the pairwise keys are hardly discovered by unauthorised parties due to the randomness of PRF. For broadcasting in LEAP+, every node owns its one-way key chain as well as its neighbours' one-time broadcasting keys. Even though the attacker obtains such a broadcasting key, it is hard to derive its future broadcasting keys by the one wayness of OWF [17]. Similarly, our impersonated probability on individual communication is given by
In LOCK, k keys are always kept to establish pairwise keys with new nodes even though the keys are periodically updated. The fraction of total sensor nodes that is impersonated by
Given c total captured nodes in

Comparison of average resiliency against impersonating by node capture amongst ours, 2KP, LOCK, and LEAP+.
4.3. Resource Requirements
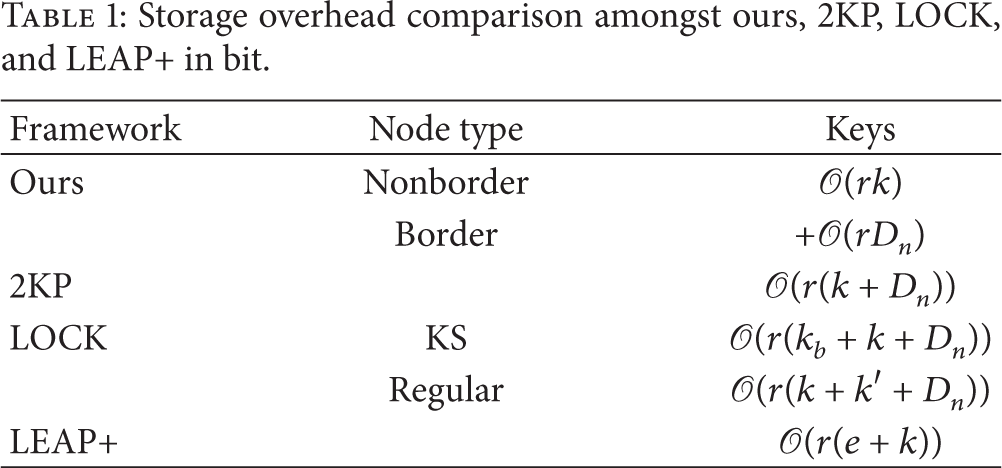
Now, we compare our framework with 2KP, LOCK, and LEAP+ in three resource overhead metrics: storage, communication, and computation. Every analysed overhead is represented by the big O notation to see its maximum complexity even in the worst case.
Storage. Table 1 provides the storage overheads of the selected keying frameworks. Regarding that r stands for the size of key in bit, the different storage requirements to nonborder and to border nodes in our framework are given as stated in Section 3.3. By 2KP, every node is preloaded k keys from the M-pool for new nodes and shares pairwise keys with
Storage overhead comparison amongst ours, 2KP, LOCK, and LEAP+ in bit.
Communication. While assuming that the key size, r, is greater than node ids, key ids, bases, and the MACs of all of these without losing generality, we present the communication overheads required between a neighbouring pair for each of initial keying, rekeying, and keying for a new node by the different studies as in Table 2. For any keying course, our keying framework consumes communication sources with a single key with its MAC, two bases with their MACs, or two node ids as discussed in Section 3.3. Similarly, a neighbouring pair exchanges associated node ids or a broadcasting key with its MAC in LEAP+. By contrast, in 2KP and LOCK, every node broadcasts the sequence of their own key ids as needed to find neighbours having common keys. Since the broadcasting key delivery of LEAP+ more often occurs than our rechaining, our framework reduces the communication overheads of all the keying phases over 2KP, LOCK, and LEAP+.
Communication overhead comparison amongst ours, 2KP, LOCK, and LEAP+ in bit.

Computation. All the complexities required to chain keys by an OWF, to produce an MAC by a hash function, and to generate a pairwise key by a PRF can be regarded to be negligible [1, 8]. Thus, the security frameworks without the key ID comparison, ours and LEAP+, have lower computation overheads than 2KP and LOCK do.
Although our framework does not achieve the least storage overhead, it is fairly competitive because the resource consumption of wireless sensor nodes is usually dominated by communication [20].
5. Conclusion
In the paper, we have proposed a new dynamic keying framework for large-scale clustered WSNs, widely employed to implement ubiquitous sensor networks. In the framework, different keying mechanisms, respectively, not only protect in-cluster, intercluster, and individual communication but also effectively handle node addition and eviction. Our proposed key-use ordering mechanism of a cluster-shared one-way key chain, illustrated in Figure 2, and intercluster key establishment using the preloaded key matrix achieve perfect connectivity as well as well protect wireless sensors from impersonating by node capture with low resource overheads. Such our claims have been discussed by the given theoretic analyses and varied simulations. As one of extensions for this work, we may raise energy efficiency and practicability by utilizing environment energy and considering crosslayer networking as in [21].
Footnotes
Acknowledgments
This work was supported by the Basic Science Research Program through a Grant from the National Research Foundation of Korea (NRF) funded by the Ministry of Education, Science, and Technology (2012-0005793 and 2011-0013776). This work was also supported by the IT R&D program of MKE/KEIT (10039165, development of learner-participatory and interactive 3D virtual learning contents technology).